abuse.ch ретвитнул

🇫🇷 We’re proud to be a Gold Sponsor at #Botconf26 with our partner @abuse_ch next month! After attending many times, we’re delighted to be supporting this brilliant event. 🤖🤩
#GoldSponsor #Botnets #Malware

English
abuse.ch
3.4K posts


@abuse_ch
Fighting malware and botnets



FUD #SparkRAT related. 'ChromeSetup.msi' seen from Hong Kong bazaar.abuse.ch/sample/91a2945…

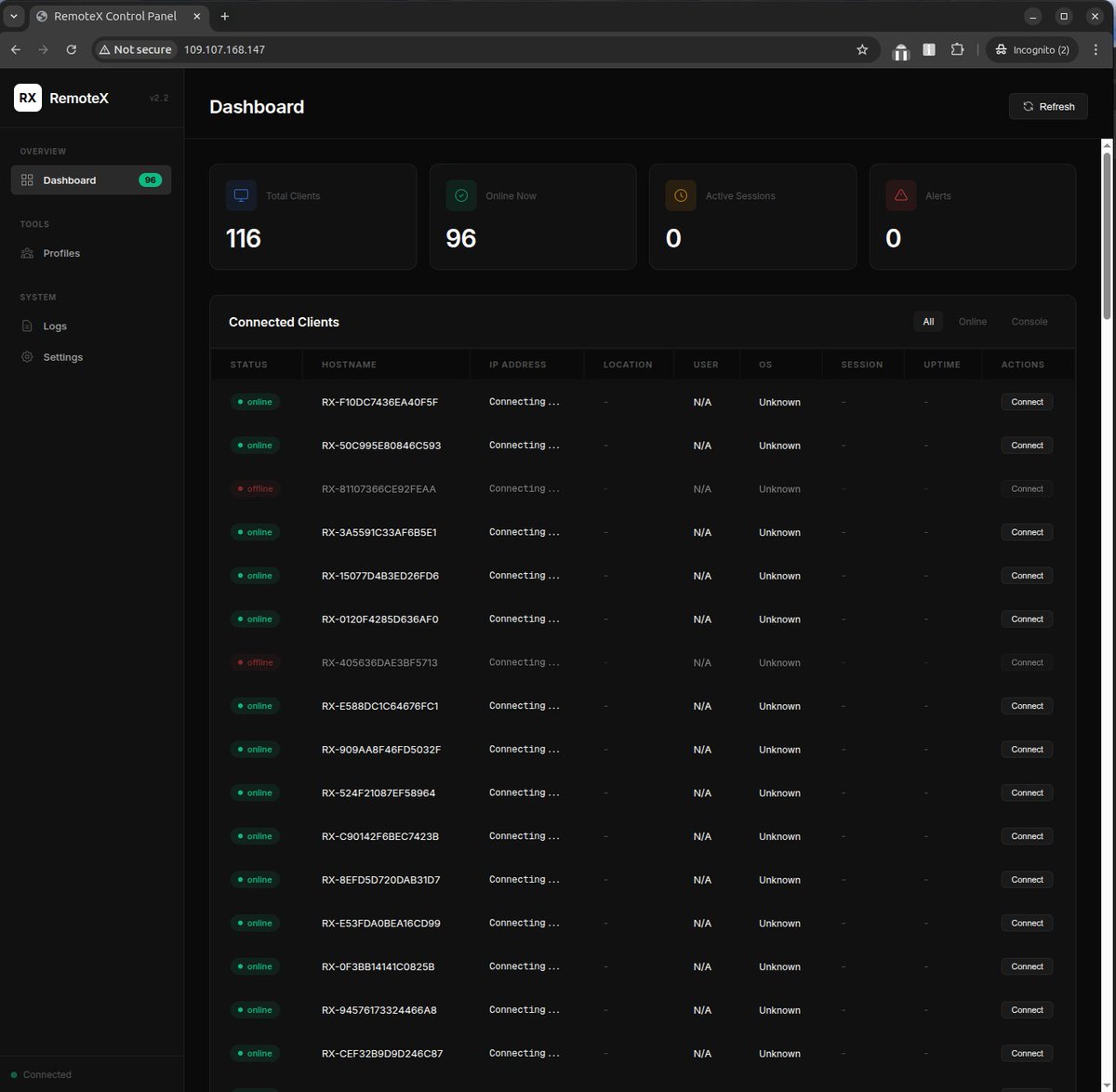
Proofpoint threat researchers identified a new malware-as-a-service named #TrustConnect. Notably, it masquerades as a legitimate remote monitoring and management tool, marking an evolution in how attackers weaponize trust around enterprise tooling. brnw.ch/21x05Vh



















'Tis the season for a new infostealer: #SantaStealer. Promotion on Telegram and underground forums says the malware-as-a-service will release before year-end. Rapid7 Labs analyzed unstripped samples to detail how it operates & what defenders should know: r-7.co/4q5pk75