DinDinDin
83 posts


DinDinDin
@comores_11
Bug Hunter | Never give up ...
Присоединился Eylül 2019
100 Подписки576 Подписчики

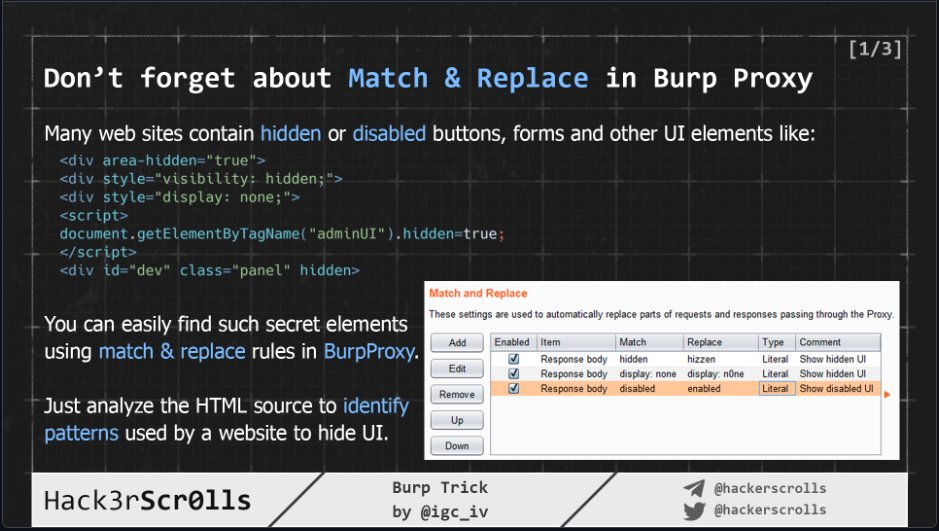
On SPA apps (React/Vue/Angular), use Burp Match & Replace to swap all "false" to "true" in JSON responses.
The result ? Hidden admin panels, debug modes, and restricted UI features can appear. 🔓
Don't just test the API, explore the UI! 🛡️
#Infosec #WebSecurity #BurpSuite #BugBounty #Pentest
English
DinDinDin ретвитнул

How to bypass WAF on HTML tag with attributes. Another great scheme by @hackerscrolls. #infosec #CyberSecurity #bugbountytip #ethicalhacking

English

🔥 XSS Tip: Raw HTML response vs Browser DOM
When a XSS payload is reflected and filtered in a HTML response, always verify it in the DOM as well.
Why? In the raw HTML response, your payload might look safely filtered or encoded. However, once it reaches the DOM, it can still execute due to JavaScript processing (client-side rendering).
Don't just trust the raw bytes in Burp — trust the DOM 🔍!
#BugBounty #XSS #Pentest #Infosec #WebSecurity #BurpSuite
English

🔥 XSS Tip: Unicode Normalization
Don't give up if <, >, " or ' are filtered ! Many apps normalize Unicode after the WAF/security layer.
Some bypass variants (URL-encoded):
🔹 < ➔ %EF%BC%9C
🔹 > ➔ %EF%BC%9E
🔹 " ➔ %EF%BC%A2
🔹 ' ➔ %EF%BC%87
🔹 ` ➔ %EF%BD%80
For example, inject %EF%BC%9Cscript%EF%BC%9E and check if it reflects as