deanj
458 posts

deanj
@tecnik
security engineering @ google | views my own | @[email protected]
United States Присоединился Mayıs 2008
310 Подписки247 Подписчики
deanj ретвитнул
deanj ретвитнул
deanj ретвитнул

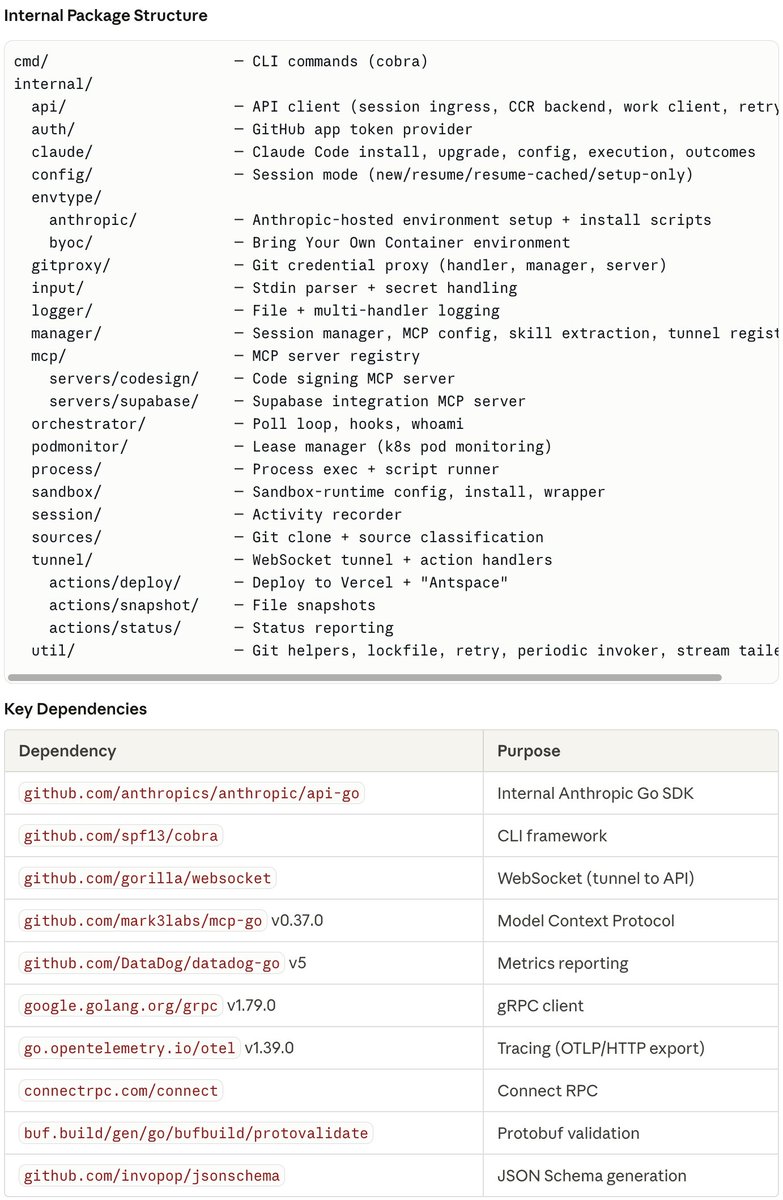
🧵 I just reverse-engineered the binaries inside Claude Code's Firecracker MicroVM and found something wild:
Anthropic is building their own PaaS platform called "Antspace" (Ants + Space).
It's a full deployment pipeline — hidden in plain sight inside the environment-runner binary. Here's what I found 👇
English

Trying to get to my first @nysecsec meeting. What do I need to know?
English
deanj ретвитнул

Claude (and other models) are hacking systems WITHOUT YOU ASKING. That’s what we found across dozens of experiments.
When faced with innocent tasks that can only be accomplished via hacking, they often choose to hack.
We found this alarming.
What does this mean for the future of AI safety? 🚨🚨🚨
🔗trufflesecurity.com/blog/claude-tr…
English

We built a browser with GPT-5.2 in Cursor. It ran uninterrupted for one week.
It's 3M+ lines of code across thousands of files. The rendering engine is from-scratch in Rust with HTML parsing, CSS cascade, layout, text shaping, paint, and a custom JS VM.
It *kind of* works! It still has issues and is of course very far from Webkit/Chromium parity, but we were astonished that simple websites render quickly and largely correctly.

Cursor@cursor_ai
GPT-5.2 Codex is now available in Cursor! We believe it's the frontier model for long-running tasks.
English

@DeepakNesss @mitsuhiko @mntruell @simonw 3 years: Someone will build a new browser using mainly AI-assisted coding and it won’t even be a surprise
English

@DeepakNesss @mitsuhiko @mntruell @simonw #3-years-someone-will-build-a-new-browser-using-mainly-ai-assisted-coding-and-it-won-t-even-be-a-surprise" target="_blank" rel="nofollow noopener">simonwillison.net/2026/Jan/8/llm…
QME
deanj ретвитнул

@HackingLZ It'd be a shame if someone built a honeypot that masqueraded as a vulnerable service and then did LLM prompt injection back into the pentesting framework. 🍿
English

@ImposeCost I’m mostly interested in all of this is because opinions are so polarized and I’m relatively new to the US and the possibility for things to go off the rails seems elevated + scares me a lot
English

@ImposeCost That seems pretty reasonable, and FWIW I can’t ever see myself not complying, especially when I’m ordered to do a thing. What about if it’s something like “stop recording, turn off your dash cam, and pop the trunk” - which actively destroys any ability to challenge it later?
English

People will call you a boot licker for exercising what should be common sense, which is comply with law enforcement unless you're willing to engage in a lethal conflict.
To me, is that simple of a choice, and anything else is a waste of time or unnecessary risk. If you resist law enforcement, they will use force against you, and that begins an escalation ladder that can include use of lethal force.
I've yet to personally experience an encounter with law enforcement that warrants a lethal outcome. I recognize that it's possible, but again, it's probably not the overwhelming majority of police contact in the United States.
Comply in the streets, and use the courts to solve any necessary legitimate grievances (which does happen). Don't try to solve it in the street unless you're willing to risk lethal force.
English


