wrongbaud
3.2K posts

wrongbaud
@wrongbaud
Cars, Bikes, Coffee and Embedded Systems Security | Founder @voidstarsec Training and Consulting https://t.co/0ib8fK31Ib https://t.co/YzN9K2LaST
Boston, MA Присоединился Mayıs 2019
1.1K Подписки4.9K Подписчики
Закреплённый твит
Happy Friday! Looking for weekend reading about hardware hacking?
JTAG: wrongbaud.github.io/posts/jtag-hdd/
SWD: wrongbaud.github.io/posts/stm-xbox…
I2C: wrongbaud.github.io/posts/Holiday-…
SPI: wrongbaud.github.io/posts/BasicFUN…
UART: wrongbaud.github.io/posts/router-t…
English
wrongbaud ретвитнул

Hacking Renesas chips for cars: three glitching resources to boost your success. 🚙⚡🫨🔬👨🏻💻
More details on:
LinkedIn: linkedin.com/posts/dlaskov_…
Substack: it4sec.substack.com/p/hacking-rene…

English
wrongbaud ретвитнул

Best damn hacking video in years and it's mah dude, mr @joegrand
SO SO GOOD and check you out, Mr electro magentico
youtube.com/watch?v=MhJoJR…

YouTube
English
wrongbaud ретвитнул
Save the date! 📅
We're happy to announce another session of our asynchronous training: Fundamentals of Browser Exploitation!
📅Start-Date: June 1st, 2026
🌎Location: Remote / Self-Paced
ℹ️Purchasing and full information: ret2.io/trainings
English
wrongbaud ретвитнул

wrongbaud ретвитнул

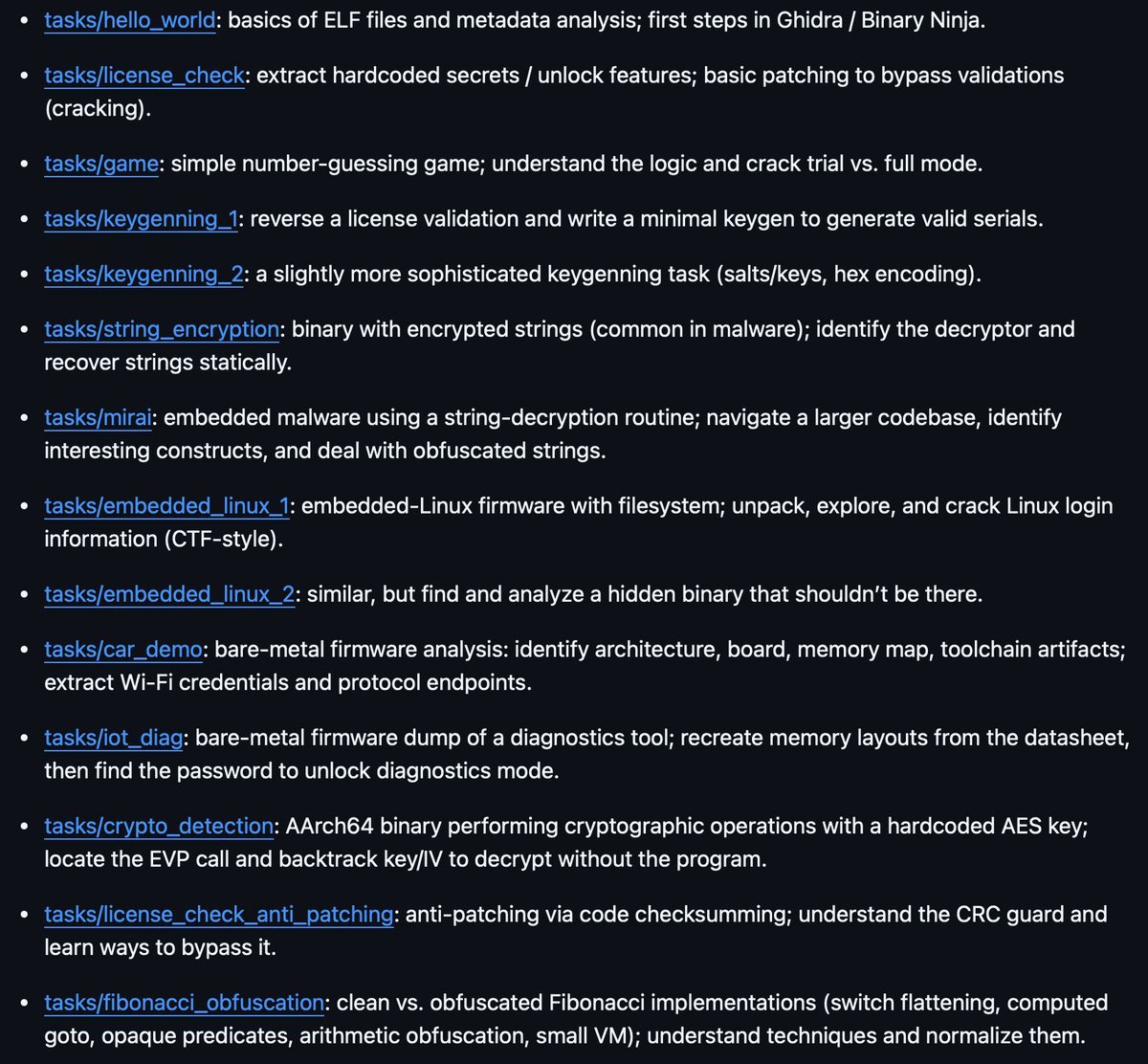
@emproofsecurity's workshop material to get started with embedded firmware reverse engineering
github.com/emproof-com/wo…
#infosec #embedded

English
wrongbaud ретвитнул
wrongbaud ретвитнул

I’ve been selected to play at the Tin Pan South NSAI Best Of Songwriting Seminar round on SAT MARCH 28 in NASHVILLE 🤠 tickets on sale now! ticketweb.com/event/best-of-…

English
wrongbaud ретвитнул

📠 Hardware Hacking Guide: How to Build a Hardware Hacking Lab
Blog: voidstarsec.com/hw-hacking-lab…
author: @wrongbaud
#infosec
GIF
GIF
English
wrongbaud ретвитнул

Yes! I recommend:
@yashiro_ld (Cool RF stuff, DIY MRI machine)
@kuwahara82 (Cool RF Stuff)
@AnalogDevicesJP (somehow better than the USA account 🤣)
@by_kohei (Cool RF stuff and electronics in general)
@0yama (DIY Audio Synth)
@edy555 (NanoVNA dev)
@toragiCQ (publisher)
sam@SamuelBeek
if you're into hardware and not following japanese accounts, you are not doing it right so many gems
English
wrongbaud ретвитнул
wrongbaud ретвитнул

@joegrand en Tropicon 2026. ¡Aprende del mejor! 🌴🛡️
¡Pocas veces tienes a un referente mundial tan cerca! Joe Grand se une a nuestro lineup de speakers para una edición que promete ser histórica.
🔥 Lo que te espera:
Joe mostrará técnicas para recuperar bitcoins de hardware wallets!
El ambiente único de Cozumel. 🏝️
#Tropicon #JoeGrand #Hacker #TechMexico #Cozumel #InfoSecNews
📅 17-18 de Abril, 2026
🌐 Más info: tropicon.org

Español
wrongbaud ретвитнул

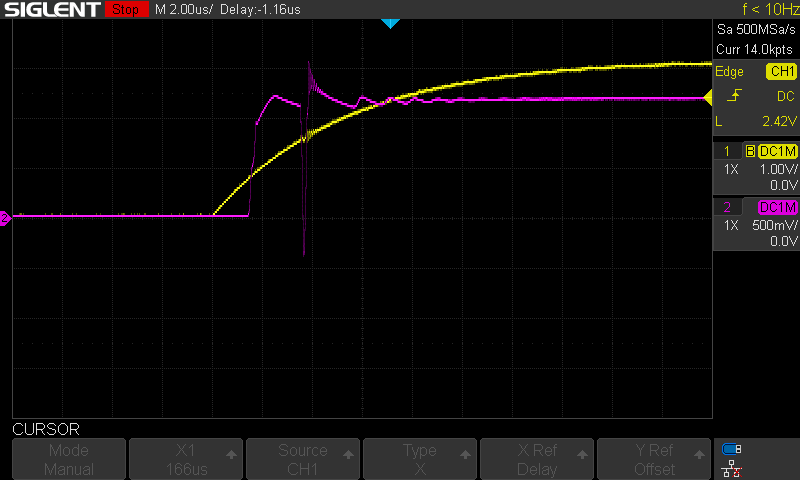
If you glitch one, can you glitch many?
Extracting automotive firmware is a challenge.
@Phil_BARR3TT explains how he bypassed the IDCODE protection in several variants of the RH850 MCU family using both voltage glitching and side-channel analysis ⚡️🚗
blog.quarkslab.com/bypassing-debu…

English
wrongbaud ретвитнул

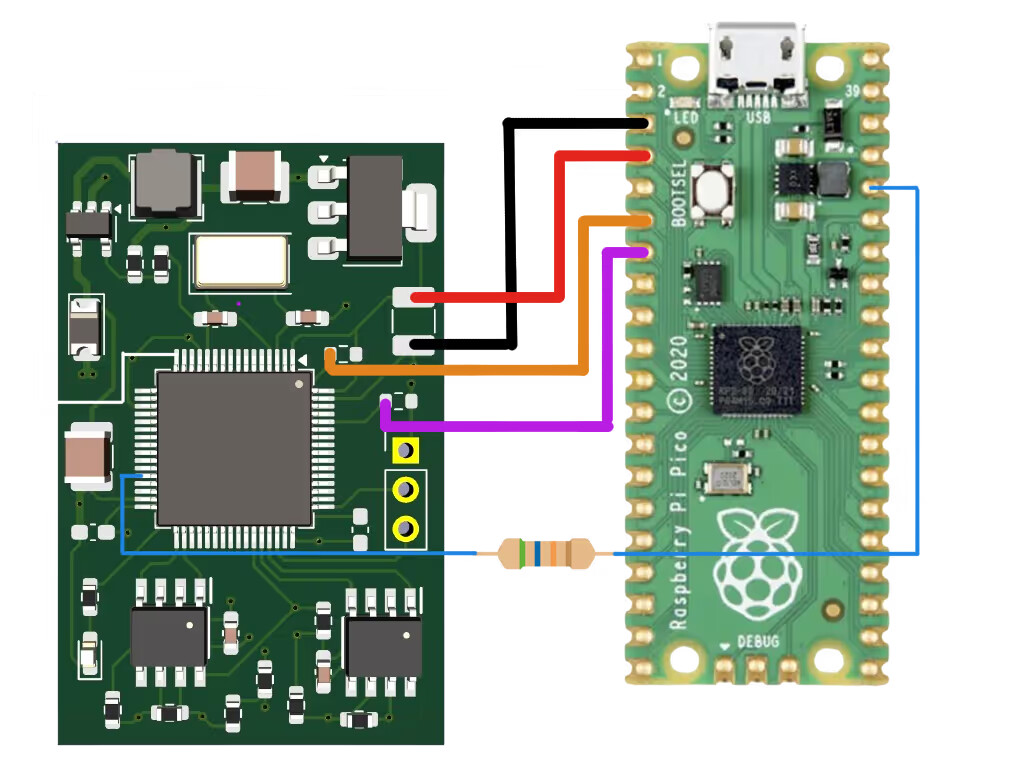
🔓 The rabbit hole goes deeper based on comments :)
Following our thread on STM32 RDP bypass, the community just dropped more clues on how that mystery dongle likely works: open-source refs, attack chain breakdown, and real-world reproductions on Pi Pico, maybe others?
👇 community.penthertz.com/t/breaking-stm…
English
wrongbaud ретвитнул

From UV light to CPU register tracing: 8 years of tackling STM32 readout protection, quickly summarized.
The latest? STM32-TraceRip achieves 100% flash recovery on STM32G0: no glitching, no decapping, just reading processor state during normal execution.
Full state of the art on our community:
👇
community.penthertz.com/t/breaking-stm…
English
wrongbaud ретвитнул
wrongbaud ретвитнул

CVEs reserved for 2 @UnitreeRobotics RCEs 🔥 blog dropping next week. one unauthenticated/unpaired/ota, one paired but scarier. same base vulnerable code, two completely different channel to trigger it in the latest firmware. 31 min read 😬 full journey from RCE A to RCE B
English
So happy that people are finding this guide useful!
Denis Laskov 🇮🇱@it4sec
How to become a hardware 𝗁̶𝖺̶𝖼̶𝗄̶𝖾̶𝗋̶ security researcher: from lab setup to fault injection and glitching.🎓🔬👨🏻🏭🧠👨🏻💻 More details on: LinkedIn: linkedin.com/posts/dlaskov_… Substack: it4sec.substack.com/p/how-to-becom…
English
wrongbaud ретвитнул
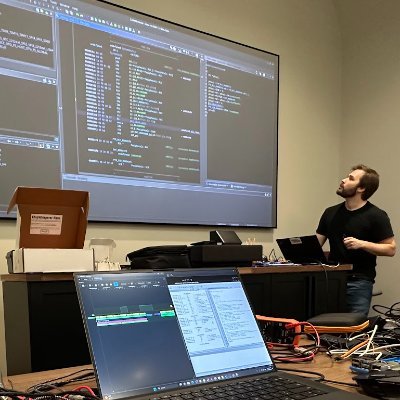
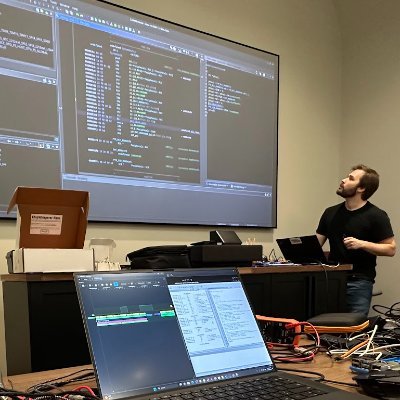
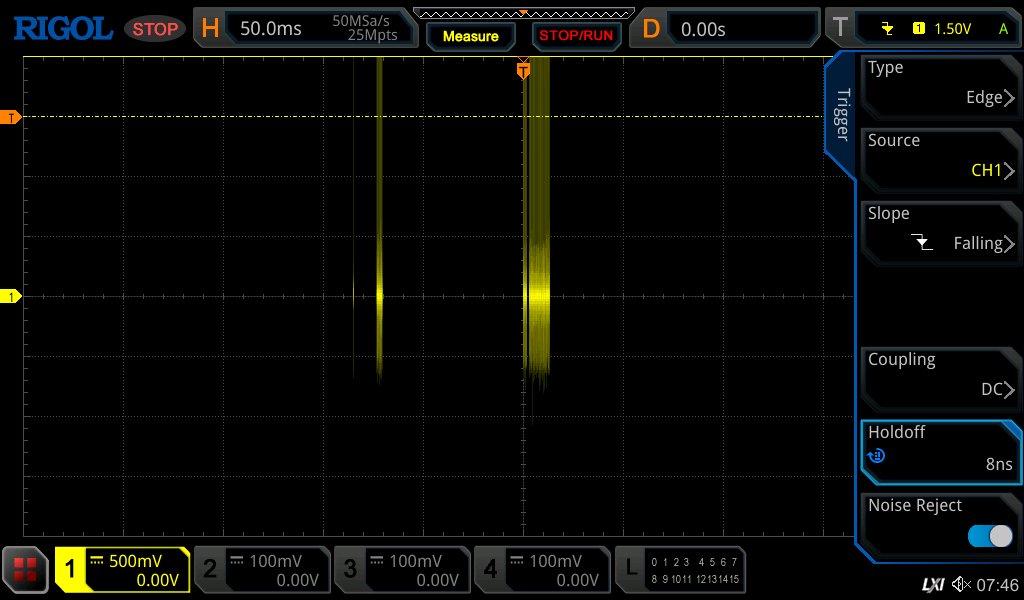
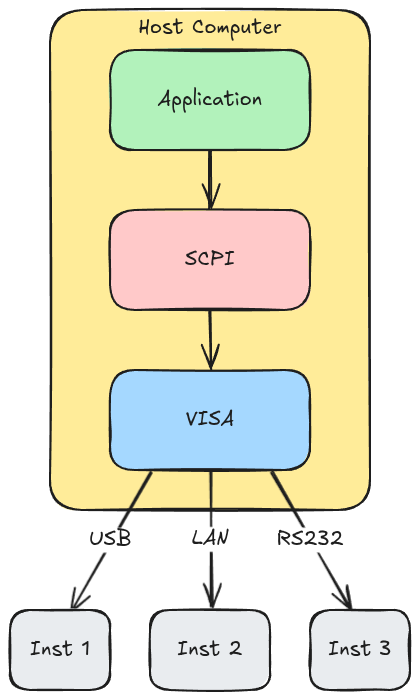
New blog post! SCPI and Hardware Instrumentation for Reverse Engineers - Part 1
Learn how to use SCPI and PyVISA to programmatically control your oscilloscope and power supply for hardware hacking. We walk through automating power cycling, capturing waveforms, and importing traces into PulseView for analysis.
voidstarsec.com/blog/scpi-and-…
English
wrongbaud ретвитнул