Modern attacks rarely stay in one domain. What starts as credential misuse in the cloud can quickly extend to identity systems and endpoints.
This video explains:
🔐 Why correlating cloud, identity, and endpoint telemetry matters
🧭 How a unified attack narrative helps security teams understand scope and respond with clarity
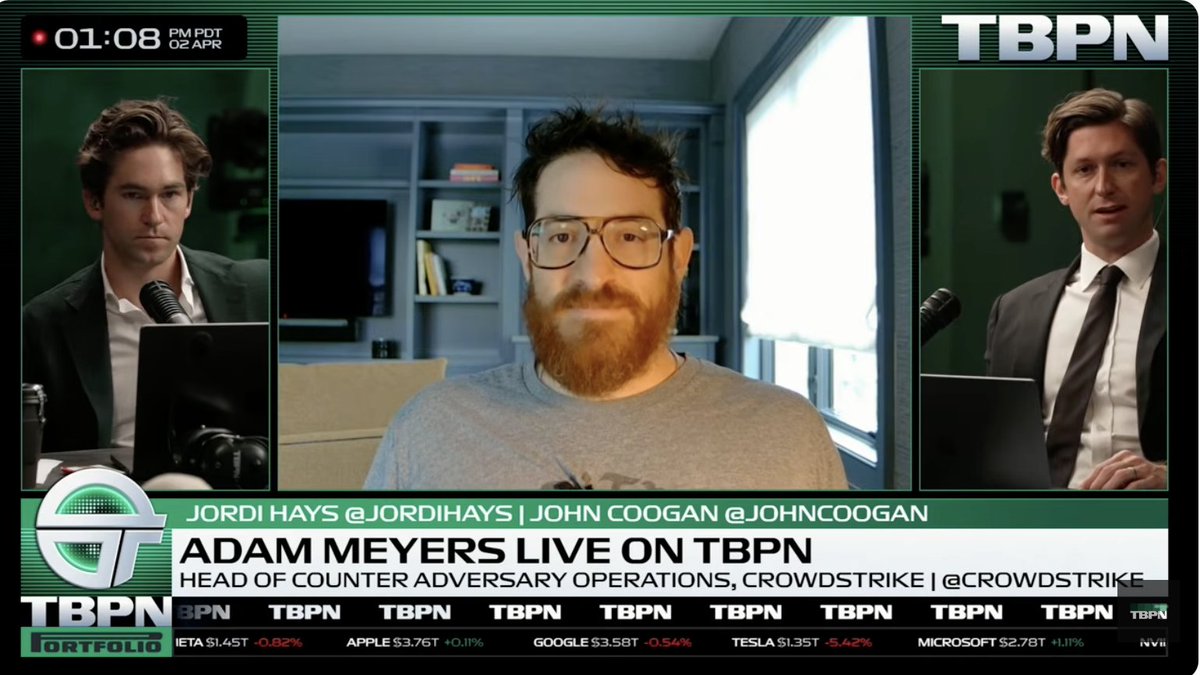
Watch the full video here: crwdstr.ke/6019B6qVEJ
English