Kushagra Sharma รีทวีตแล้ว

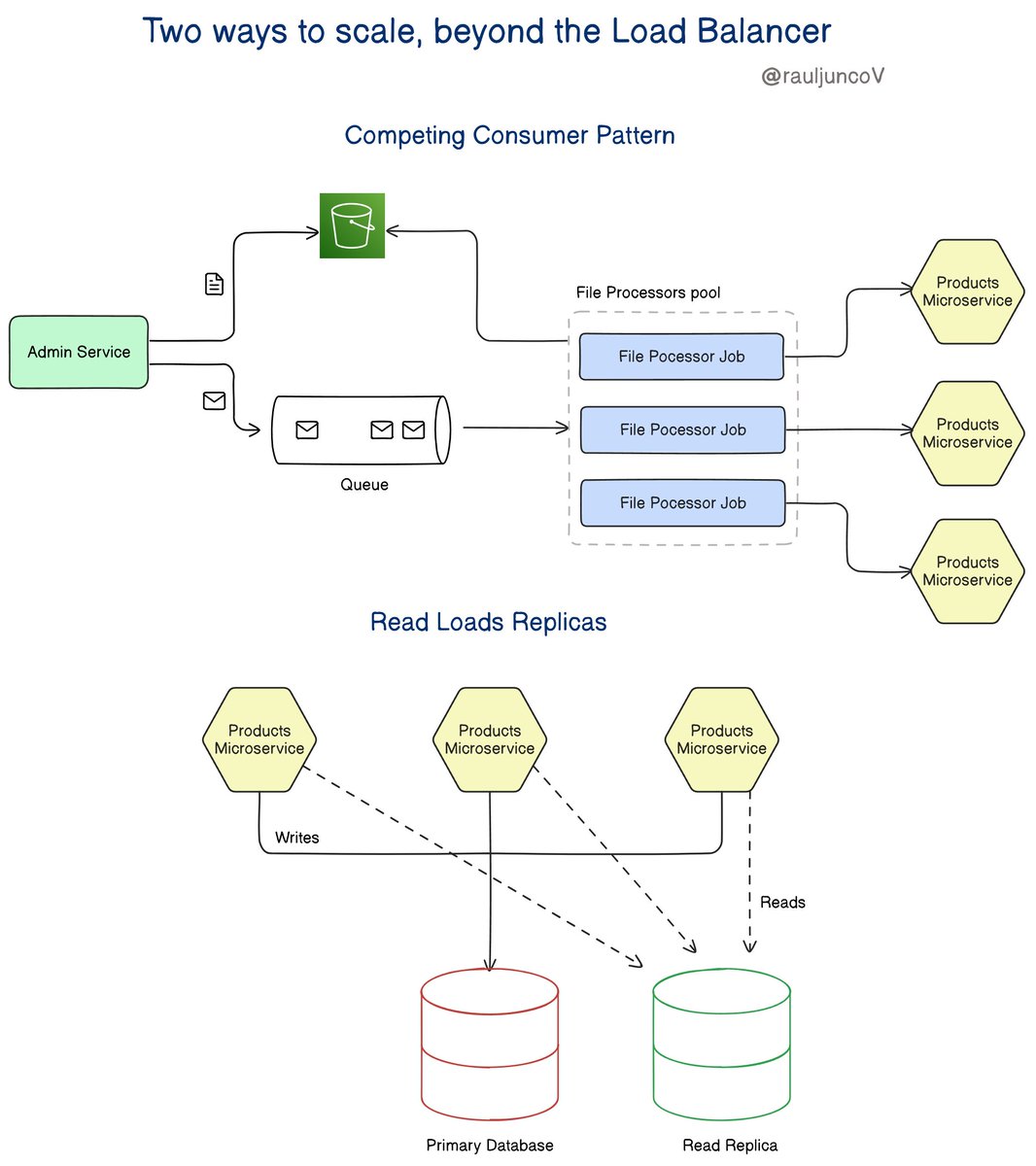
Horizontal scaling is more than a load balancer.
Here are 2 more ways to scale Horizontally.
With horizontal duplication, you duplicate part of your system to handle more workloads and distribute the work between these duplicates.
The most obvious way of horizontal duplication is using a load balancer. They:
• Distribute the work.
• Detect when a node is unavailable and remove it from the load balancer pool.
1. Competing Consumer Pattern
The idea of this pattern is to distribute the load to achieve more throughput.
This is ideal when you have job processors. For example, if your system needs to allow users to import and process large files.
You place each uploaded file in a queue; many consumers would compete to pick up and process them.
2. Read Loads Replicas
To reduce the reads on the primary database, you create a Read Replicas.
This works well if a lot of the load on the main system is read-heavy.
For example, in an e-commerce system.
The primary database handles all write operations, while read replicas handle read-heavy operations, like fetching product details or user order history.
Horizontal duplication is somewhat straightforward.
If vertical scaling isn't available, this form of scaling is typically the next thing I'd look at.
Assuming you can split the work across the duplicates, it's an elegant way of spreading the load and reducing resource contention.
With a caveat that requires more infrastructure, of course, costs more money.
Have you done any of these?
English