Senderwallet รีทวีตแล้ว
Senderwallet
301 posts

Senderwallet รีทวีตแล้ว
Senderwallet รีทวีตแล้ว

🦖
Day 275 of learning blockchain👾
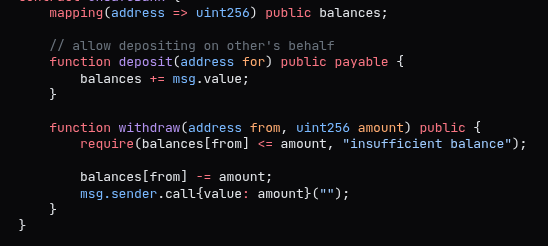
Got a bug confirmed on Immunefi today.
But here’s the truth no one talks about…
If you don’t make it, there will be no evidence you ever tried.
All the sleepless nights, staring at code until your eyes hurt
All the self-doubt when nothing clicks
All the silent losses no one sees
It will all mean nothing to the world.
That’s the painful part.
This path doesn’t reward effort — it only rewards outcomes.
So you either win…
or your struggle disappears like it never existed.
And that’s exactly why I’m not stopping.
English
Senderwallet รีทวีตแล้ว

Bypass SSRF WAF rule blocking access
Additional Internal URLs Accepted
https://0x7f000001/ | Yes | localhost (hex) |
https://[::1]/ | Yes | IPv6 loopback |
#BugBounty #BugBountyTips
English
Senderwallet รีทวีตแล้ว
Senderwallet รีทวีตแล้ว

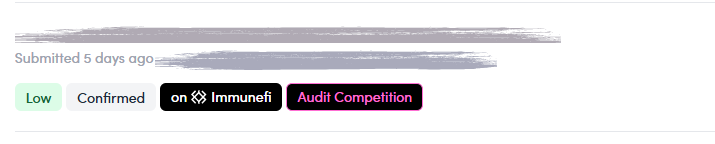
Ross benchmarked 28 (up from 21) different AI security tools.
The results are pretty stark, most security tools are worse than ChatGPT.
ross.wei@z0r0zzz
English
Senderwallet รีทวีตแล้ว

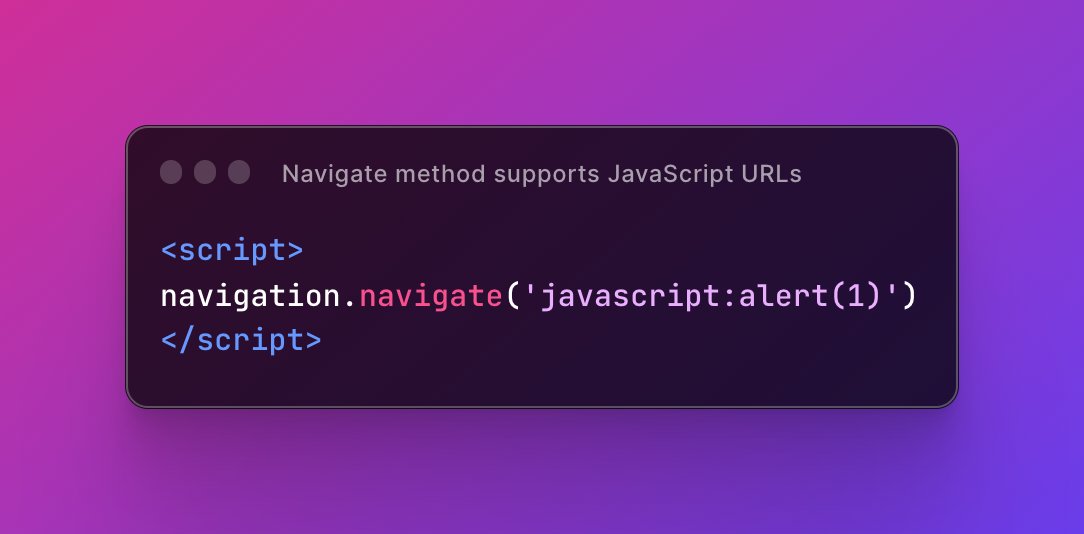
We've discovered you can use the experimental 'navigation' object to trigger JS execution in Chrome. Check it out on our cheat sheet:
#navigation-navigate-method" target="_blank" rel="nofollow noopener">portswigger.net/web-security/c…
English
Senderwallet รีทวีตแล้ว

you have a big js file ? no time to analyze it all
search for these :
URLSearchParams
window.location
window.location.search
URL.searchParams
fetch()
XMLHttpRequest
FormData
window.location.hash
window.location.href
URL.hash
#bugbountytips
English
Senderwallet รีทวีตแล้ว

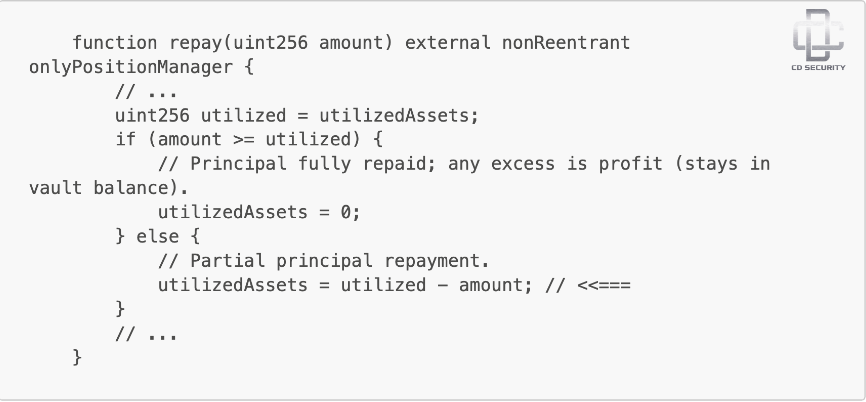
🚨 In one of our audits, we found a Critical accounting bug that incorrectly reduced the system’s recorded debt in a lending vault.
With a single repayment, the protocol could make outstanding loans disappear from its accounting.
Here’s what was happening:
LPs deposit assets into a vault and borrowers take loans from it.
The protocol tracks active loans using a variable called `utilizedAssets`, which represents the total assets currently lent out.
When a loan is repaid, this value should decrease only by the borrowed principal.
But the `repay` function deducted the entire repayment amount from `utilizedAssets`.
This amount could include principal, profit, or liquidation penalties.
So when a position closed with profit, the protocol treated that profit as if it were debt repayment.
Result:
`utilizedAssets` could drop to zero even while other loans were still active.
This causes the protocol to underreport outstanding debt and misprice LP shares.
The fix was simple: reduce `utilizedAssets` only by the repaid principal, while treating the excess as profit added to vault liquidity.
English
Senderwallet รีทวีตแล้ว
Senderwallet รีทวีตแล้ว

تدرس أمن سيبراني أو مهتم بالتقنية؟ 👨💻
فيه مستودع اسمه The Book of Secret Knowledge يعتبر كنز حقيقي 👀
يجمع لك مئات الأدوات والمواقع والشروحات في مكان واحد
🔹 أدوات الشبكات والاختبار الأمني
🔹 أوامر لينكس المهمة
🔹 Cheat Sheets سريعة
🔹 مواقع تدريب وموارد تقنية
بدل ما تضيع وقتك تدور الأدوات في الإنترنت، بتلقى كل شيء مرتب في مستودع واحد يفيد الطلاب والتقنيين.
العربية
Senderwallet รีทวีตแล้ว

Why do CPUs have multiple cache levels? by Fabian Giesen.
One of the best explanations, and my periodic recommendation to the students.
fgiesen.wordpress.com/2016/08/07/why…
English
Senderwallet รีทวีตแล้ว

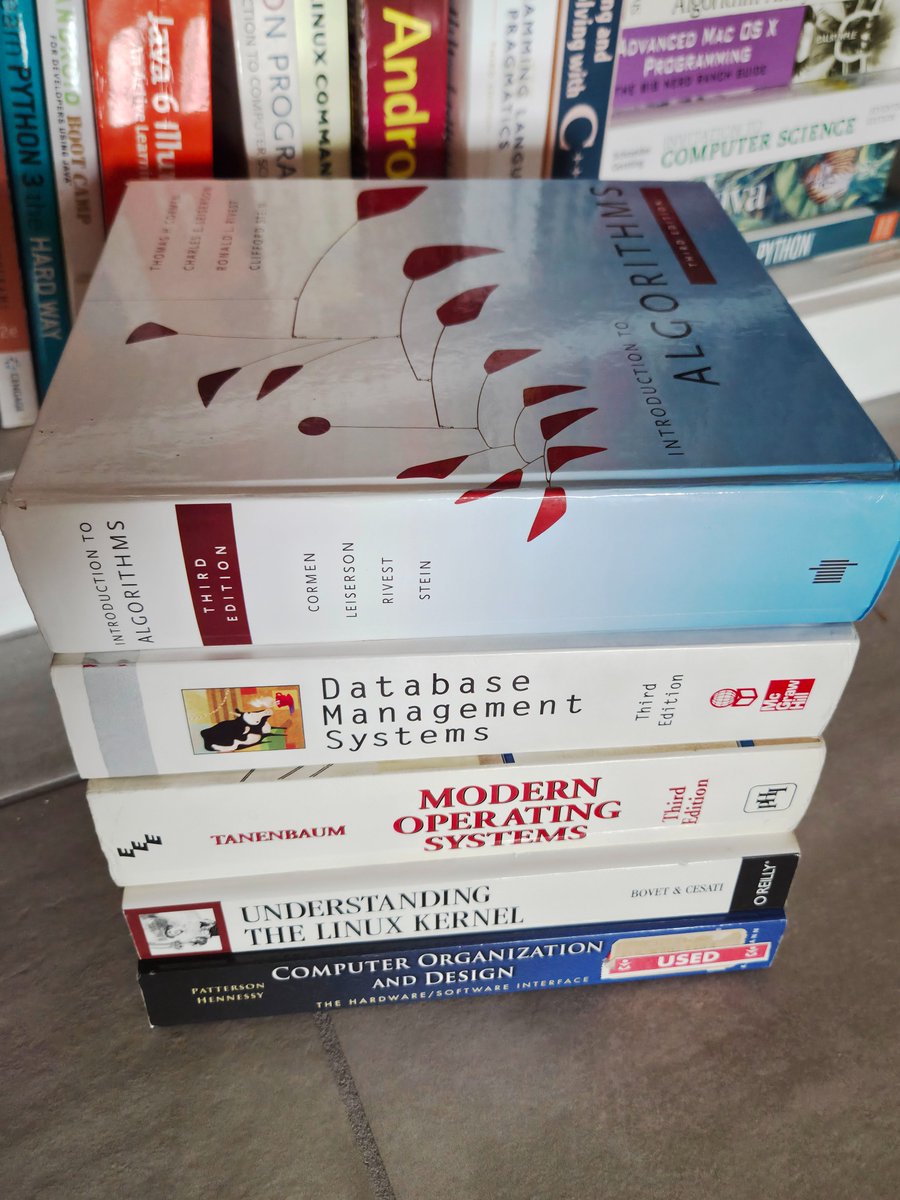
- Programming sits on maths.
- Algorithms run on maths.
- Every AI model is maths.
- Machine learning is maths.
- Deep learning is maths.
- Graphics are maths.
- Simulations are maths.
- Cryptography is maths.
- Blockchain is maths.
- Data science is maths.
- Optimization is maths.
- Signal processing is maths.
- Robotics moves because of maths.
- Game engines run because of maths.
- Your entire tech stack survives on maths.
You're still asking if we need math for programming?

English
Senderwallet รีทวีตแล้ว
Senderwallet รีทวีตแล้ว

Introducing solidity-auditor-skills — an open-source Claude Code skill for Solidity security auditing.
210 attack vectors, 7 parallel agents, DeFi protocol checklists, adversarial reasoning.
Forked from @PashovAuditGrp's excellent skills repo with 40 new vectors covering DeFi liquidation economics, staking reward manipulation, Uniswap V4 hooks, EIP-1153 transient storage, and OZ v4→v5 migration pitfalls.
Aggregates knowledge from 20+ audit skill repos including @trailofbits, @QuillAudits_AI, @OpenZeppelin, @AuditMos, @cyfrin, and more.
Drop it into Claude Code, Cursor, or Codex and run /solidity-auditor on your contracts.
github.com/sanbir/solidit…
English
Senderwallet รีทวีตแล้ว

2026 bug bounty guide: #8-waf-bypass-techniques" target="_blank" rel="nofollow noopener">github.com/The-XSS-Rat/Se…
English
Senderwallet รีทวีตแล้ว

📌 Repaying debt in a share-based stablecoin system is NOT just burning tokens.
In this model, debt isn’t stored as a number.
It’s stored as shares.
Actual debt is always:
debt = shares × exchangeRate
So what does repayUpTo() really do?
1️⃣ Convert the MyUSD amount into debt shares
2️⃣ Cap repayment if the user tries to repay more than they owe
3️⃣ Decrease user shares
4️⃣ Decrease totalDebtShares
5️⃣ Burn the MyUSD tokens
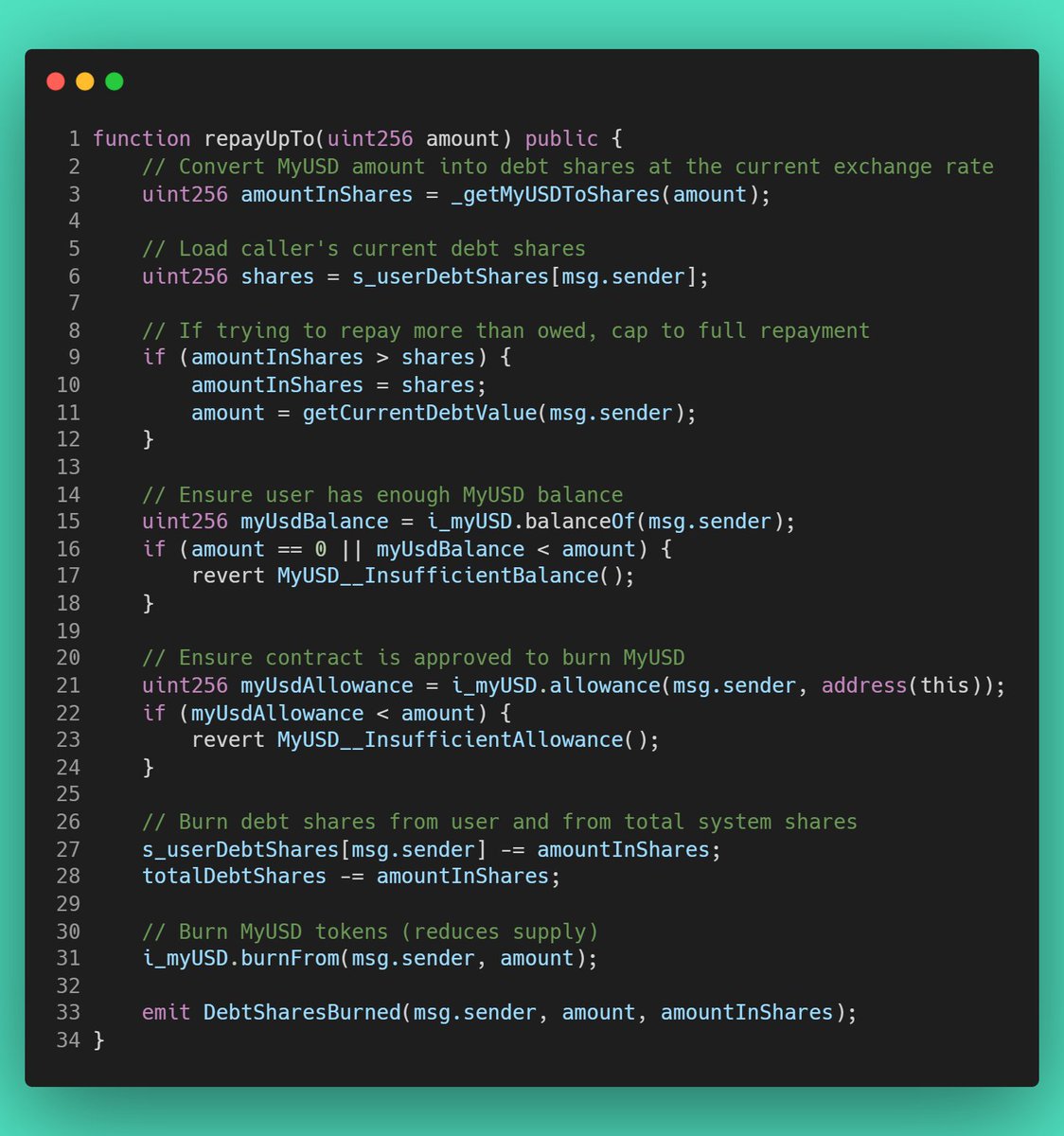
English
Senderwallet รีทวีตแล้ว
Senderwallet รีทวีตแล้ว

Read only re entrancy attack
Bookmark if you want to read later.
Read only re entrancy is a type of vulnerability in smart contracts that relies on functions marked as view or read only. normally, these functions are supposed to just check or show data without changing anything. For example, a contract might have balance[msg.sender] >= amount inside a view function to check if a user has enough tokens before allowing a withdrawal, on the surface this seems safe because no state changes happen in a view function.
the problem happens when this view function is called from another external function that does update the state, like transferring tokens or withdrawing funds. If the view function is not designed carefully following the CEI pattern, it can give a false sense of security. that is the view function will show that the balance is sufficient, even though a malicious fallback could trigger before the balance is actually updated.
An attacker can exploit this by making the fallback function reenter the vulnerable contract. Since the contract has not updated the user balance yet, the view function still reports enough funds. This allows the attacker to withdraw multiple times or perform other unwanted actions. In short, even readonly checks can become dangerous if the contract logic does not carefully separate checking balances from updating them.
Sadik@0xsadikbaba
In 2023 there was an exploit of morethan $700k in one protocol because of Read only Reentrancy here is minimal contract that valnurable to Read only Re-entrancy attack can you spot the bug?
English
Senderwallet รีทวีตแล้ว

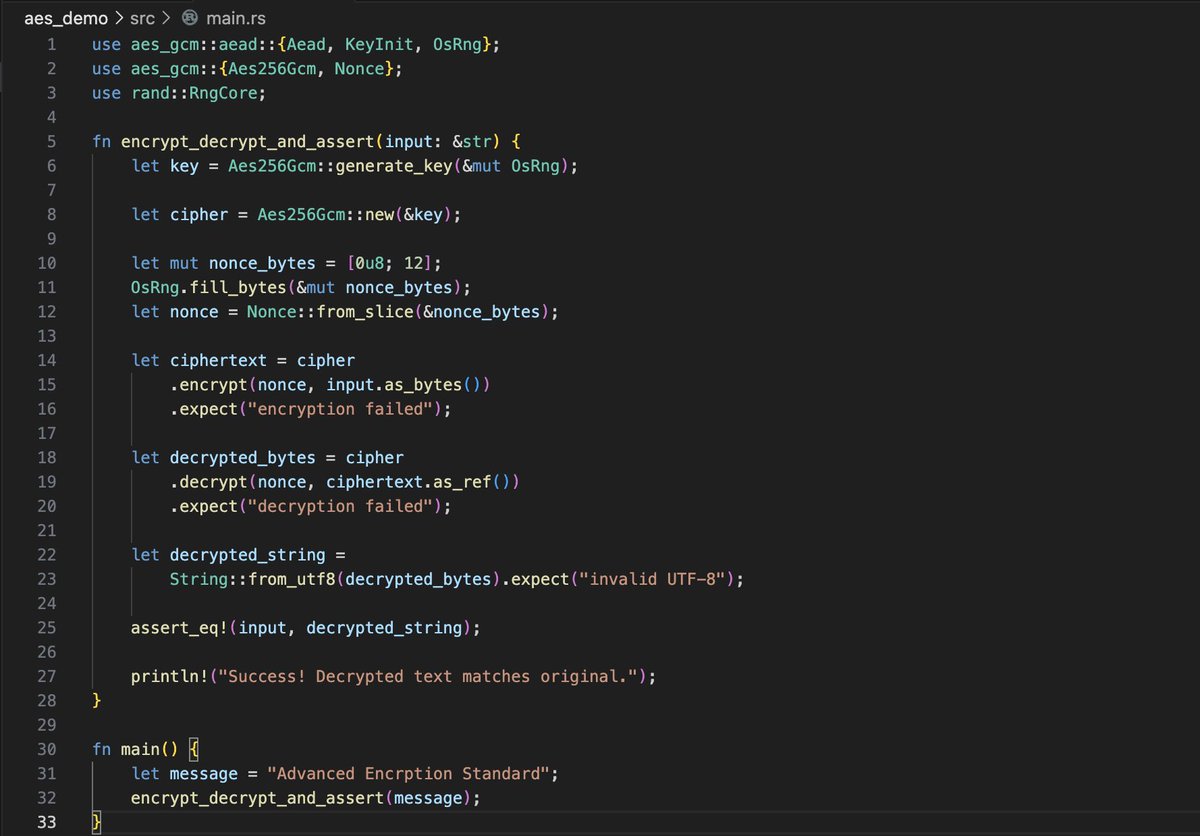
Day 20/100 of ZK
Today was mostly hands-on: implementing AES encryption and decryption in Rust, then verifying round-trip correctness (encrypt → decrypt → same plaintext). I used the aes-gcm crate for authenticated encryption. It's simple, secure by default, and enforces correct nonce + tag handling so we avoid common footguns.
Using aes-gcm is convenient because it gives authenticated encryption out of the box (prevents tampering), which is important when thinking about real-world ZK proofs of encryption (you often want to prove both correctness and integrity).
In ZK, this kind of round-trip proof is a stepping stone, later we constrain AES rounds in circuits to prove knowledge of key/plaintext without revealing them.
English