ทวีตที่ปักหมุด
HackenProof
6K posts


HackenProof
@HackenProof
Expert web3 bug bounty and crowdsourced audit platform with 220 programs and over 20 million in bounty DS: https://t.co/yl9Srpuzbb
Start bug bounty journey → เข้าร่วม Mayıs 2018
2.2K กำลังติดตาม37.7K ผู้ติดตาม

Written by @gneiss2meetU , Security Analyst at HackenProof.
👉 Read Part 1 now: hackenproof.com/blog/for-hacke…
English
HackenProof รีทวีตแล้ว

i found chain halting bug on a network carrying $120M in stablecoins and $1.85B in market value. anyway, good morning! @HackenProof #HackenProof

English

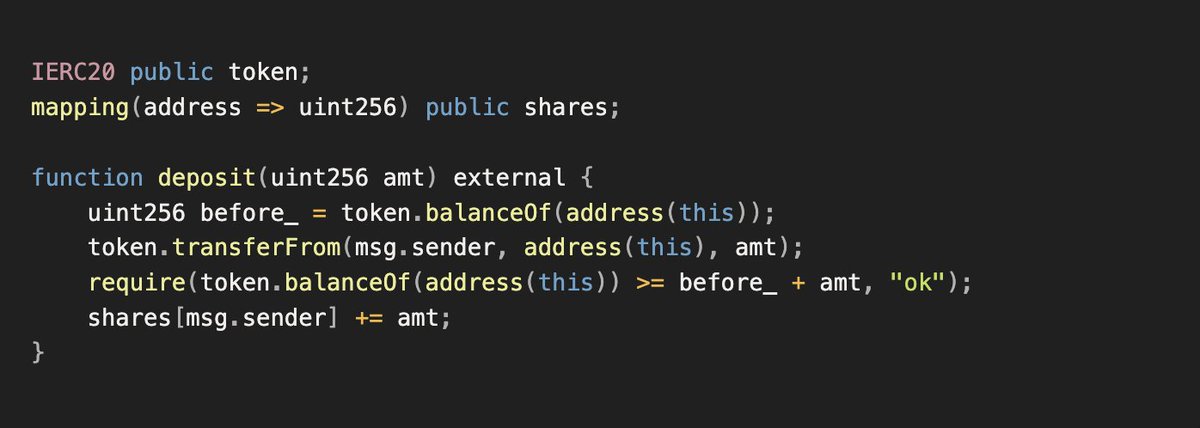
@HackenProof deposit missing a "payable" plus what everyone is saying concerning using what contract receives in updating shares
like what webrainsec says
English

@HackenProof If it's a deflationary token, then require will revert every time.
English

@HackenProof uint256 before_ = token.balanceOf(address(this));
token.transferFrom(msg.sender, address(this), amt);
uint256 received = token.balanceOf(address(this)) - before_;
shares[msg.sender] += received;
Developer Lesson: 👉 Never trust amt, always calculate received.
English

@HackenProof The transferFrom function credits shares based on the requested amount, instead of the actual amount therein, therefore an attacker can deposit malicious or fake tokens and then go ahead to dilute the contract's balance.
English

✅ [New bug bounty] Earn up to $10,000 with @idOS_network
You will be rewarded based on these tiers:
Critical: $10,000
High: $5,000
Medium: $2,000
Low: $200
Start the #bugbounty hunt right now! hackenproof.com/programs/idos-…

English

✅ [New bug bounty] Earn up to $2,000 with @pumbua
You will be rewarded based on these tiers:
Critical: $1,000 - $2,000
High: $700 - $900
Medium: $200 - $500
Low: $50 - $100
Start the #bugbounty hunt right now!
hackenproof.com/programs/pumb-…

English

📢 Big news from @suidevelopers and @SuiNetwork!
A new bounty target is live:
Bella Ciao — next-generation Sui VM execution layer rewrite with enhanced performance and new Move capabilities — offers a wide range of bounties:
Critical: $100,000 - $1,000,000
High: $10,000 - $50,000
Medium: $5,000 - $10,000
Low: $2,500 - $5,000
Start the #bugbounty hunt right now: hackenproof.com/programs/sui-p…

English

📢 New opportunity for security researchers!
Sui Developers@suidevelopers
Sui’s new VM just went public. Bug bounty is open & we want the community's eyes on it before Mainnet. The bella-ciao branch is a rewrite of the execution layer. Faster. Per-package caching. Next gen Move features. Internal review & multiple independent audits from @osec_io & @zellic_io done. Report on @HackenProof. Paid at Mainnet rates, before it hits Testnet.
English

✅ [New bug bounty challenge] Earn up to $250,000 with @flipcash
Flipcash is offering up to $250,000 to the first researcher who successfully exploits Reserve — its autonomous on-chain smart contract on Solana.
A $50,000 referral bonus is also available. Read the full details and join here:
hackenproof.com/programs/the-f…

English

@0xb4dg0d Hello, please, join discord server and open a ticket at # bug-bounty-support request. Our support team will be happy to assist you
discord.com/invite/NHX6yt7…
English

@HackenProof I found an IMO high-severity bug in your web app, but I only have 82 rep points instead of the >99 required. Is there any way to submit the bug bounty report before farming rep points on other BBPs first?
English