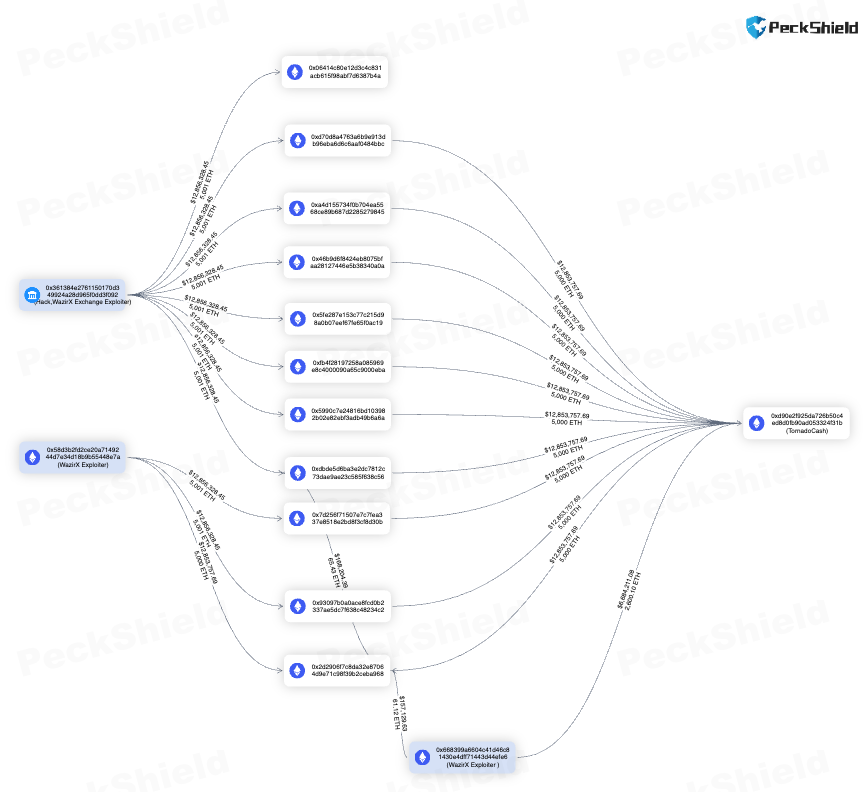
The @lifiprotocol exploiter started with 1 ETH from Tornado Cash and 9 hops later, back to Tornado Cash with 1 ETH🤭
HACKDEFI
63 posts





The @lifiprotocol exploiter started with 1 ETH from Tornado Cash and 9 hops later, back to Tornado Cash with 1 ETH🤭












We've partnered with blockchain security firm @scalebit_ to provide more comprehensive coverage for #Web3 security. This partnership expands the security footprint for both #fuzzland and #ScaleBit in the blockchain ecosystem by enabling more participants to secure themselves.


FuzzLand (@hackthedefi) has established a strategic alliance with @chainlinklabs. This alliance helps #ChainlinkBUILD members access FuzzLand's all-in-one onchain contract security platform, enabling projects to move faster while staying secure. medium.com/fuzzland-blog/…
We're honored to be selected by @xox_labs to safeguard their staking contracts where users stake to earn rewards. By onboarding with Blaz+, they get access to an in-depth security snapshot of potential vulnerabilities and 24/7 real-time smart contract analytics triggered by each state change. If you want to learn more about how Blaz+ can elevate your smart contract security, see our solutions here: fuzz.land.

One application of AI that I am excited about is AI-assisted formal verification of code and bug finding. Right now ethereum's biggest technical risk probably is bugs in code, and anything that could significantly change the game on that would be amazing.