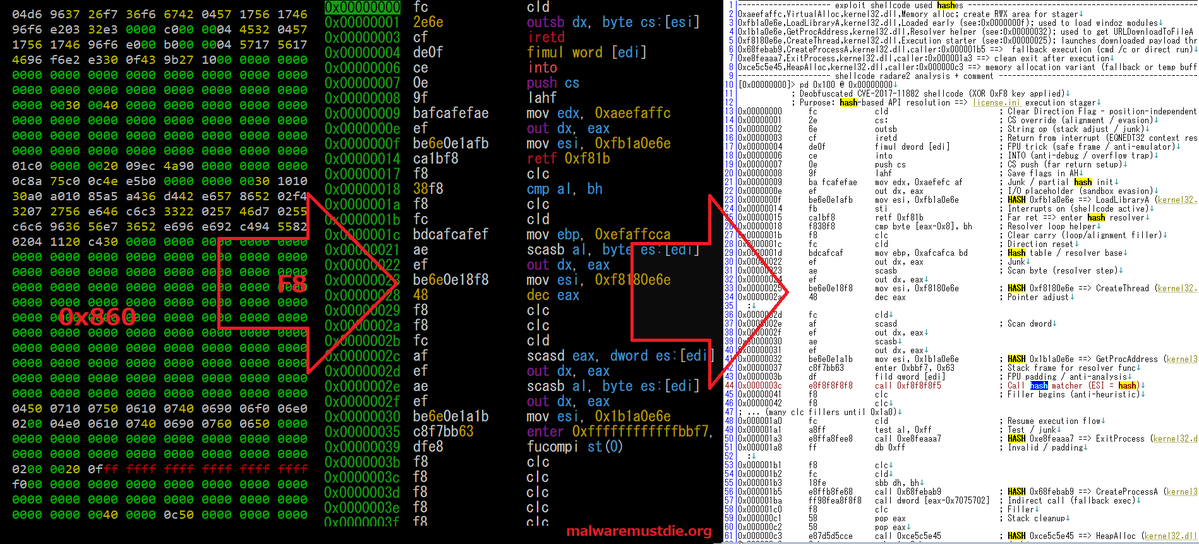
🐚 Custom Windows shellcode is the ultimate way to learn OS internals and sharpen your assembly skills. 🗺️ Video 1: The Game Plan. We start in C to map out the APIs and logic before hitting the ASM. Watch Part 1: 📺 youtu.be/6oeMEzCKXyo ✅ Dev/Debug workflows ✅ Position-Independence (PIC) ✅ Module & API hashing ✅ Stack strings & Endianness ✅ XOR obfuscation & Decryption stubs