
𝓙𝓪𝓬𝓴2
5.8K posts

@2RunJack2
#ThreatIntel Researcher @S2W_Official @TALON_INTEL Main Author of Threat Intel Report 'Campaign DOKKAEBI : Documents of Korean and Evil Binary' / Formerly FSI

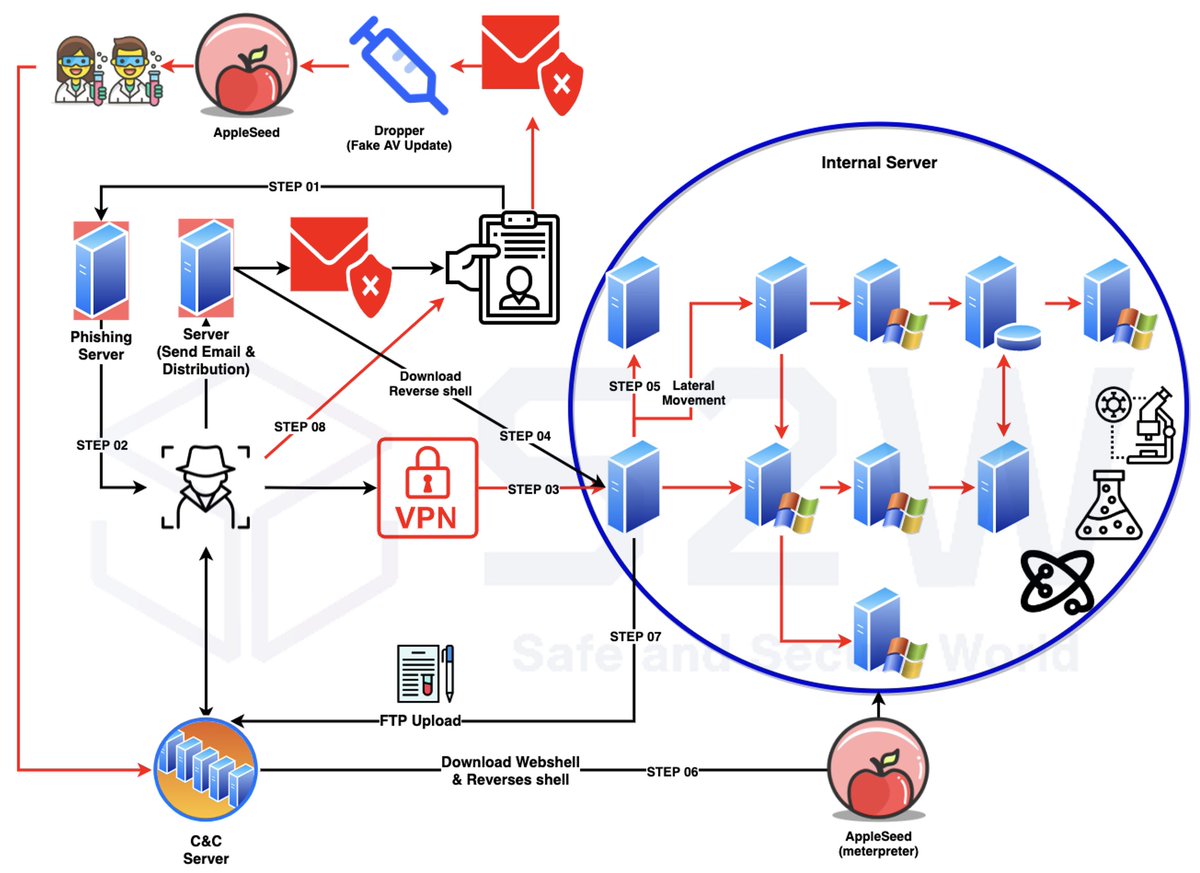



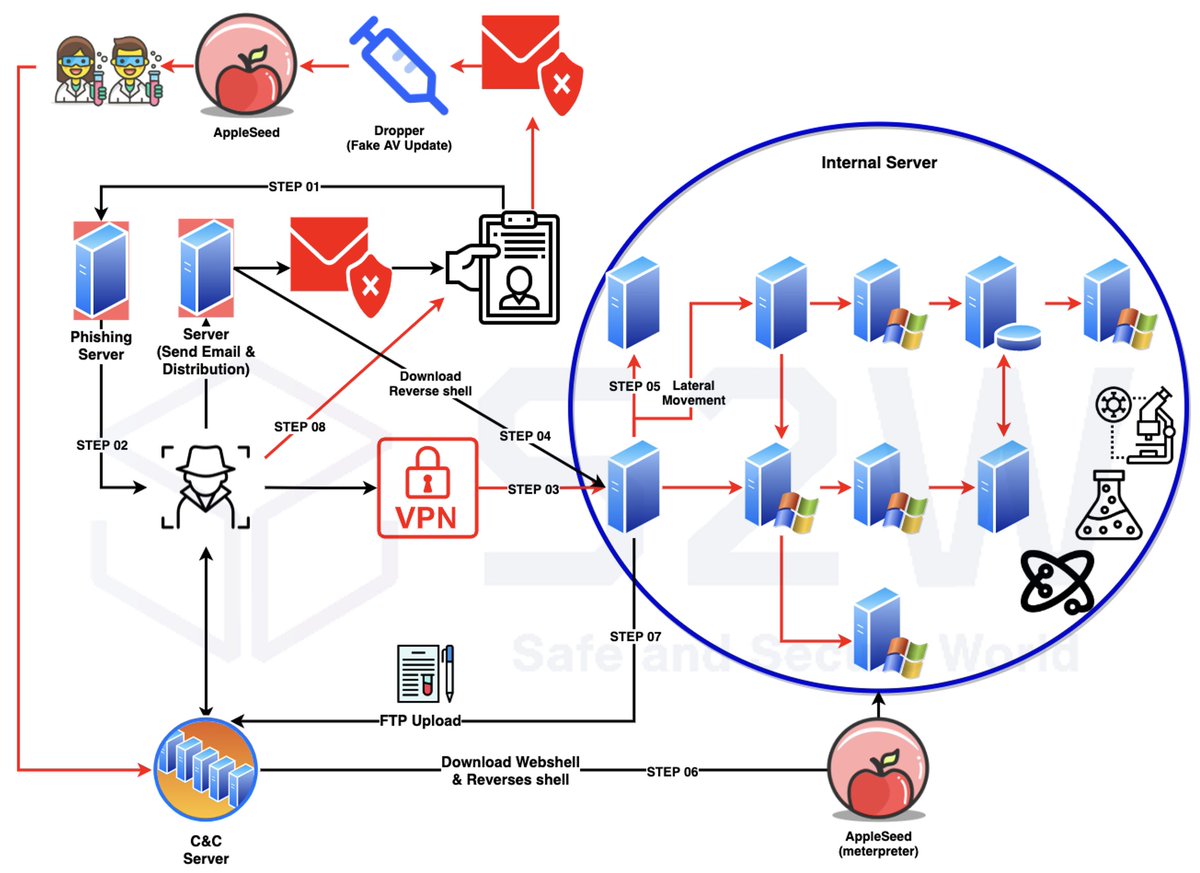
🚨 Unveiling the Full #DocSwap Malware Report S2W analyzed the 'Document Viewing Authentication App' malware, linked to a #NorthKorea-backed APT group. The C2 address showed a Naver favicon & "Million OK !!!!", linking it to #Kimsuky. 👉 Read on Medium: bit.ly/4iuFkMg







S2W's #TALON released a report on #ransomware groups for the first half of 2024. 2,260 companies had their ransomware infection details posted on leak sites, up 445 from last year. Top ransomware groups: #BlackBasta, #BlackSuit, #Qilin, #Ransomhub, #PLAY. bit.ly/3U7puxa

Finally, tomorrow, the S2W Threat Intelligence Center #TALON will deliver an analysis presentation at the #VB2024 conference! Here is the summary analysis of the following presentation topics: 👉 Learn more: - bit.ly/3ZLIPYq - bit.ly/3zHSoNt Stay tuned! 😈






Check out our analysis report on the Lilith RAT #malware distributed by the North Korean-backed attack group #puNK-003. ✍🏻 The report was issued in Korean, but please use a web translator to read it! bit.ly/3yKzuFn