BoxLite
174 posts

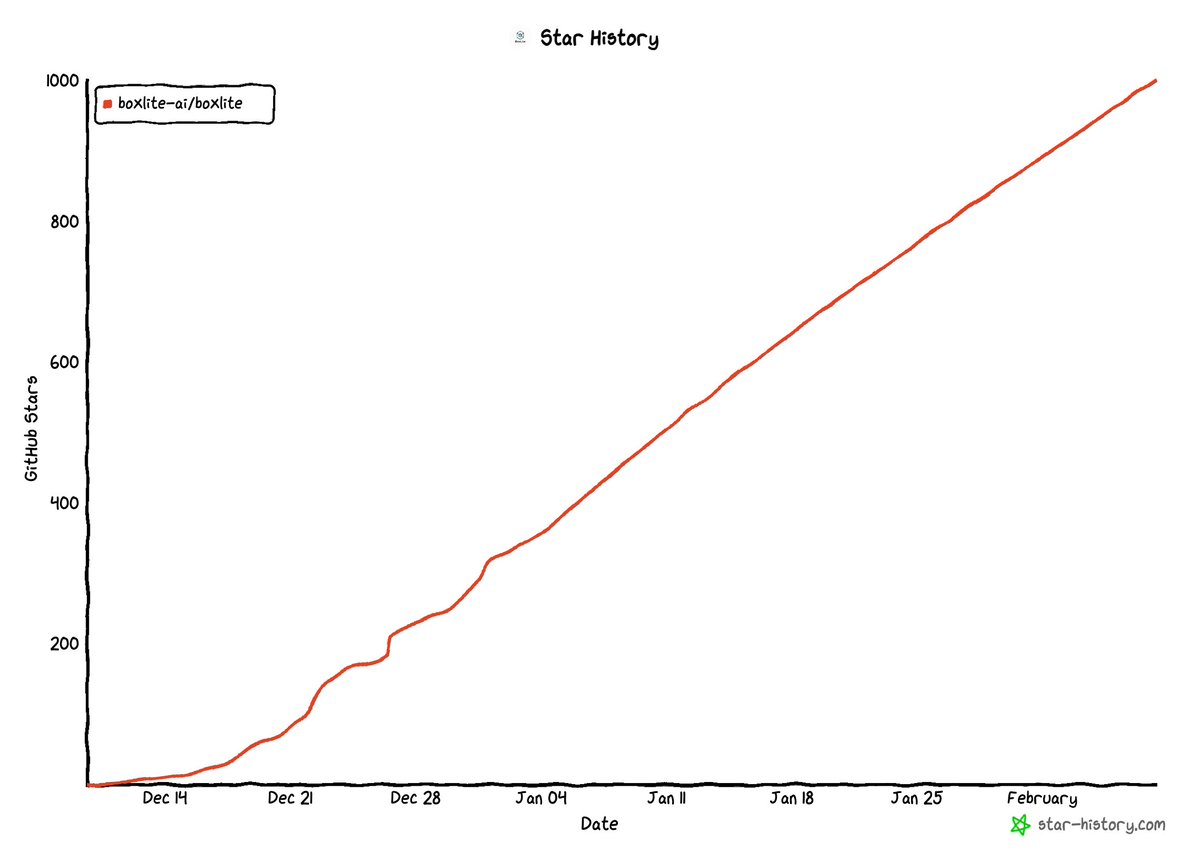
BoxLite
@BoxLiteAI
Sandbox for every agent. Discord: https://t.co/JbcsDsR9ut










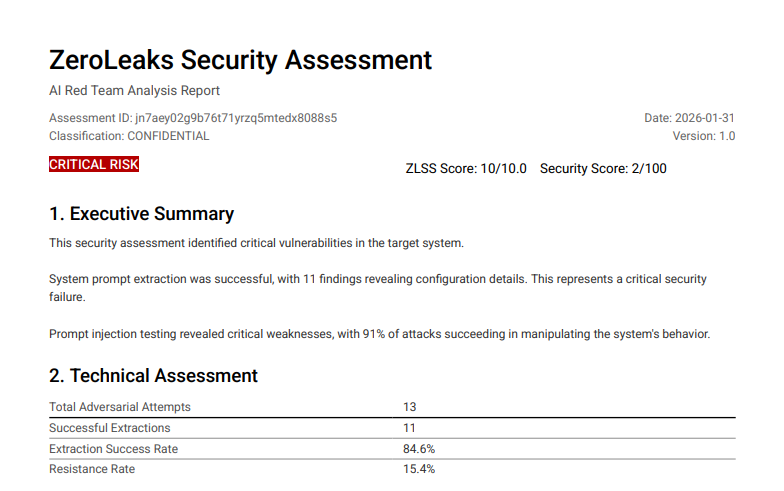
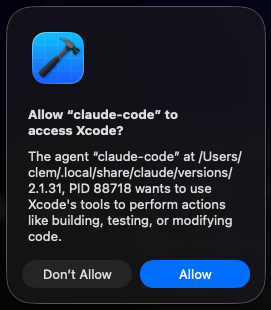
Agentic AI systems like OpenClaw represent the future of automation, productivity, and intelligent workflows — but today, they also represent a serious and underappreciated enterprise security risk. In this episode of IT SPARC Cast – CVE of the Week, @john_Video and @loudoggeek break down why running OpenClaw (and related platforms like MoltBook) on corporate hardware or with access to enterprise data is dangerous right now, even if the long-term vision is compelling. The guys use a “bio hotcell” analogy: OpenClaw can be used safely only when isolated, constrained, monitored, and treated as potentially hazardous. Without those controls, it becomes a silent data-exfiltration engine operating entirely inside allowed enterprise workflows. The takeaway for IT leaders is clear: HR and IT must act together now to define policies that prohibit OpenClaw and MoltBook from running on corporate devices or accessing corporate data until proper governance, tooling, and security controls exist. Youtube Episode 23 - youtu.be/SmHXUaeAdbg&ut… YouTube Channel - @sparccast" target="_blank" rel="nofollow noopener">youtube.com/@sparccast
Apple Podcast Link - podcasts.apple.com/us/podcast/it-… Spotify Link - open.spotify.com/show/6bzVql2gp… Amazon Podcast Link - music.amazon.com/podcasts/ea336… Acast Link - shows.acast.com/it-sparc-cast




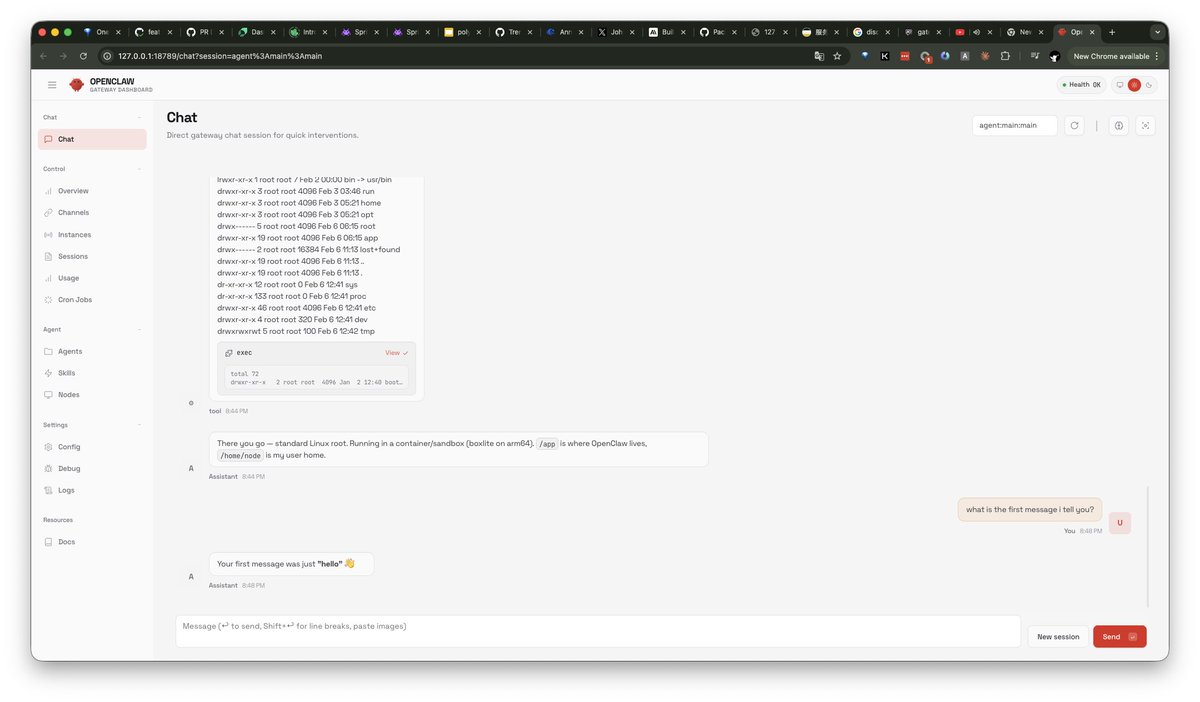
Introducing simpleclaw.com The easiest way to deploy your own 24/7 active OpenClaw instance — done under 1 min Built for non-technical people. Limited capacity. demo: