Provably
194 posts
Provably
@GetProvably
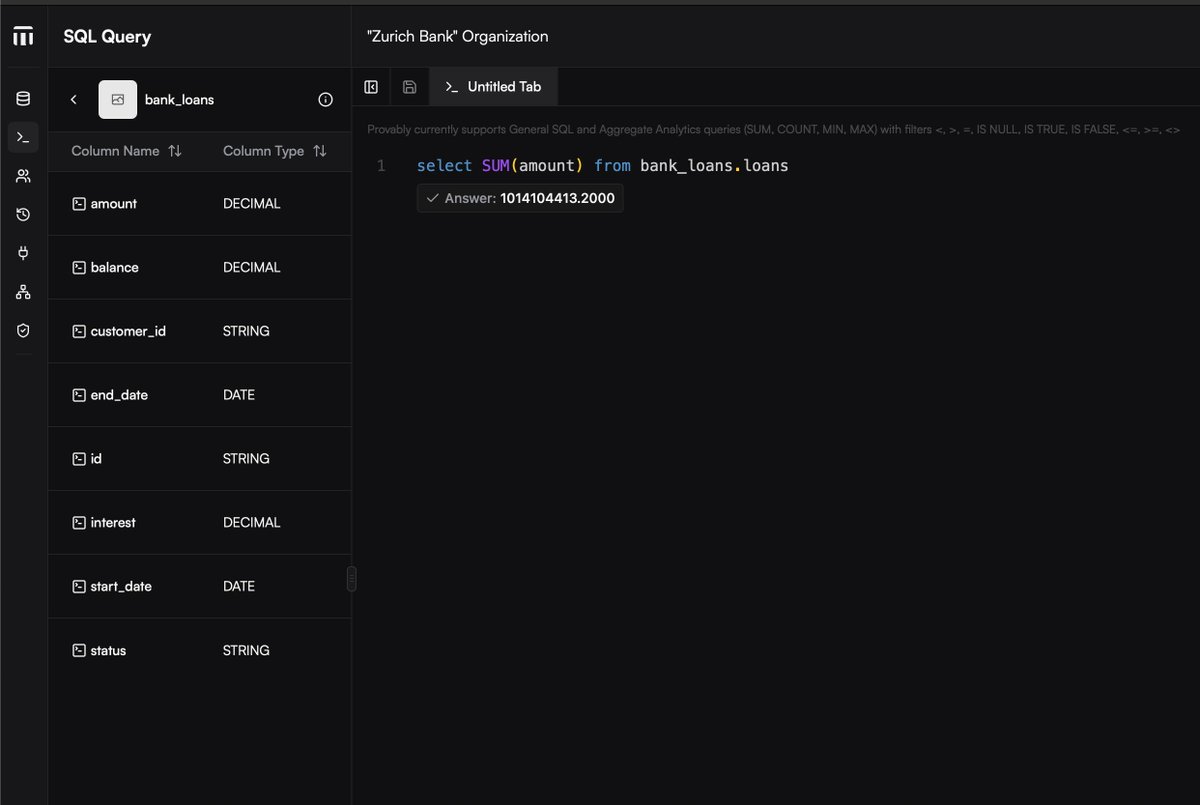
Building Verifiable Databases & SQL for Distributed Systems like Blockchains, Databases and AI.

Tune in to this week's Fireside Dev Hang, happening every Wednesday on X & YouTube LIVE: x.com/i/broadcasts/1…


My wife calls me, panicked. The call is from her number, and her voice is unmistakable- that’s my wife. ‘Babe, our son is hurt. He got in a bike wreck. I’m at the emergency room but they won’t take our insurance and I need cash to get him help. Please send me 3000 dollars as soon as you can, he’s really not doing well.’ Me- ‘Wow, that’s scary. Tell me our passphrase and then I’ll send the money.’ Her (it) - ‘What? What passphrase? This is your wife, our son is hurt. Send the money now!!’ Me- ‘I’ll call you back. I don’t believe that this is my wife. If it is, I’m sorry, but we discussed this.’ The number? Spoofed. Easy to do and there’s no way to tell if a phone number is being spoofed aside from hanging up and calling back to confirm. The voice? AI generated. Easily done. A few seconds of audio is all it takes to create a realistic audio deepfake. What can you do? 1) Create a family safe word or passphrase. Ours is definitely not ‘Keep Going’ although we considered it. Discuss the passphrase far away from phones or any recording device. This is as analog as possible. Don’t forget that the trigger for the passphrase is just as important as the phrase itself. So instead of asking ‘what’s the safe word?’ have a separate triggering question. For example, you could say ‘I’m eating banana cream pie’ and this would trigger your spouse to respond ‘purple velvet pillows’ if that’s the safe word. Make it fun, silly, and easy to remember. And DON’T WRITE IT DOWN. 2) Cognitive security is an essential skill in 2026. Assume every image and video you see online is fake until proven otherwise. Expect scams and spammers, and be pleasantly surprised when it’s not. 3) Figure out a backup communication option with people who you absolutely need to be able to reach. Don’t just rely on a phone number for communication. Have redundant, ideally encrypted methods of communication with family. What did I miss? I think (hope) Nikita is wrong on the timeframe- agentic bots like Claude bot are impressive but not quite ready to flood the phone lines in just 90 days. But I think it’s going to be a huge problem by the end of the year. I already get dozens of increasingly realistic spam calls and texts daily- it’s only going to get more annoying. Have a plan to keep your family and your finances safe!


Introducing the Midnight Summit, our inaugural gathering for builders, innovators, and thinkers in Web3 to explore the future of privacy, decentralized applications, and blockchain innovation. Day 1: Cypher Day A deep dive into privacy at every level, from protecting individual rights to securing the digital future. Decode how privacy shapes blockchain, governance, and public life. Day 2: Ecosystem Day Spotlighting the projects, partnerships, and breakthroughs driving privacy-first innovation across the Midnight ecosystem. 📍 November 17–18 🔗 midnightsummit.io Don’t miss the livestream. Join the conversation shaping the next era of privacy in Web3.