Naka-pin na Tweet
PrivacyHawk
1.4K posts


PrivacyHawk
@Privacy_Hawk
The Personal Data Management App that lets you opt-out, unsubscribe and delete your private data from companies, all in one app. Available for iOS and Android📲
Sumali Mart 2021
21 Sinusundan258 Mga Tagasunod

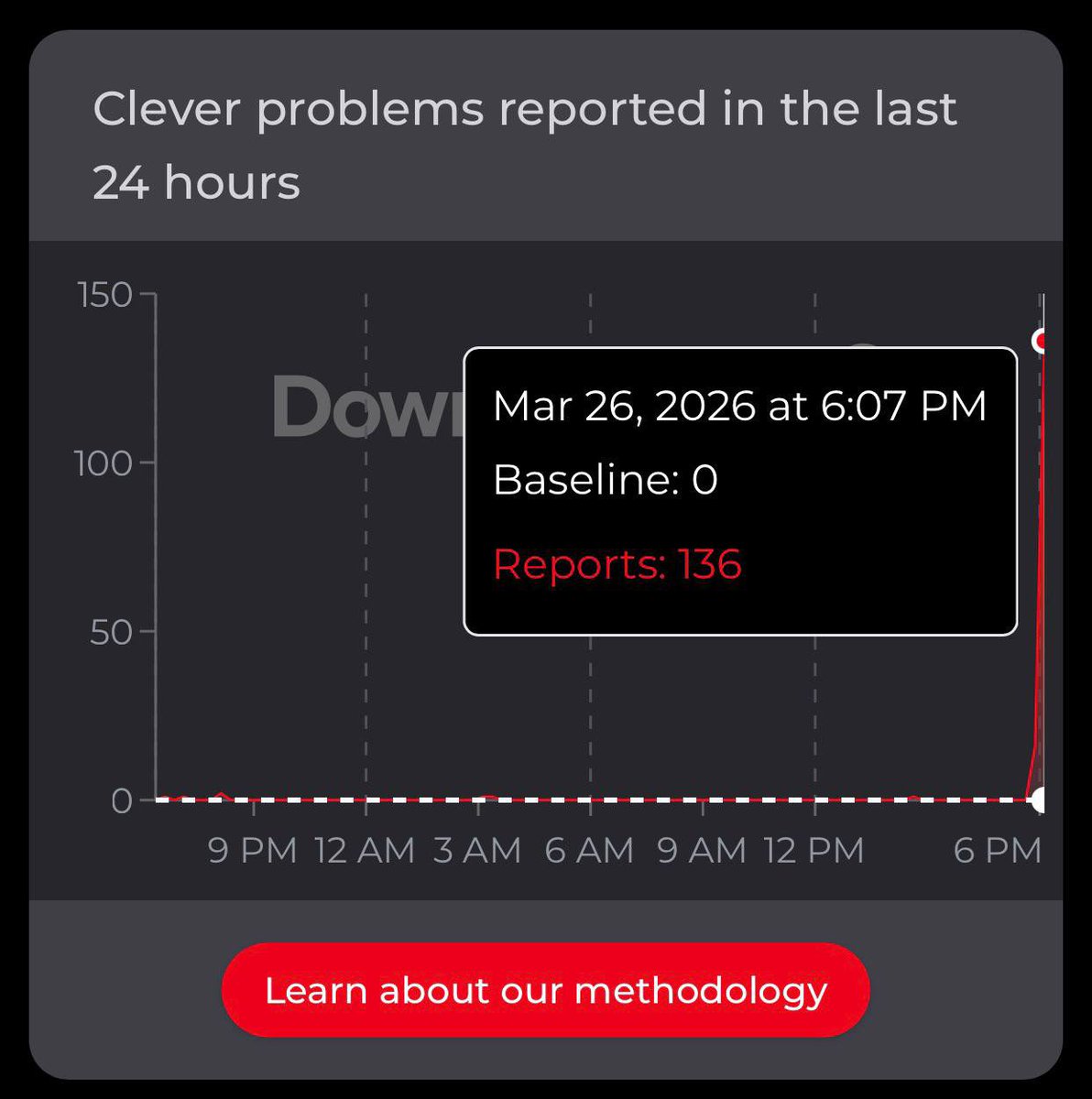
Multi-target hacktivist claims like this are usually about visibility and coordination rather than deep compromise. Hitting government and education platforms at once creates the impression of scale, even if the impact is mostly service disruption. The pattern to watch is how easily these campaigns can trigger outages across regions without needing persistent access.
English

🚨 313 Team Expands Targeting — Romania, US Education Platform and Austrian Federal Ministry of the Interior Impact Claims
The group “Islamic Cyber Resistance in Iraq – 313 Team” claims multiple cyberattacks targeting:
🇷🇴 DIICOT (Romania’s anti-organized crime & terrorism agency)
🇦🇹 Austrian Federal Ministry of the Interior
🇺🇸 Clever (widely used US educational platform)
Key details:
• Reported impact: Service disruptions / outages
• Clever outage supported by Cloudflare error (521) + Downdetector spike
• Campaign pattern: Government + education sector targeting
⚠️ Attribution remains unverified. However, supporting outage indicators suggest at least partial service disruption in some cases.
📊 Ongoing trend: Hacktivist campaigns scaling across multiple geographies and sectors simultaneously.
#CyberThreatIntelligence #DDoS #Hacktivism #OSINT #ThreatIntel #CyberSecurity #DailyDarkWeb



English

Employee data and financial documents create a mix that’s easy to reuse beyond the initial breach. Payroll details, internal records, and financial context can enable tax fraud, benefits scams, or impersonation that looks legitimate to staff. Once that data is out, the impact tends to persist well after the ransomware claim fades.
English

United States 🇺🇸 - Goodwill has allegedly been breached by the InterLock ransomware group, resulting in the leak of 80 GB of employee data and financial documents. dailydarkweb.net/goodwill-indus…

English

Biometric data works differently from passwords.
If a password leaks, you can change it. If biometric data leaks, you can’t.
Fingerprints, face scans, and other biometrics are stored as digital templates, mathematical versions of your physical traits.
If those templates are exposed, there’s no reset button.
That’s why how organizations store and protect biometric data matters so much. Unlike passwords, it’s not something you can simply replace.

English

When contracts, emails, and PII sit together at that scale, the value goes well beyond ransom pressure. Internal communications and deal terms can be reused for impersonation, invoice fraud, or competitive leverage across partners and suppliers. Once hundreds of gigabytes of that context leave the network, the impact tends to show up later in how that data gets reused.
English

Ethiopia 🇪🇹 - National Oil Ethiopia PLC (NOC) has allegedly been compromised, resulting in the exfiltration of over 800GB of sensitive data including PII, contracts, and emails. dailydarkweb.net/national-oil-e…

English

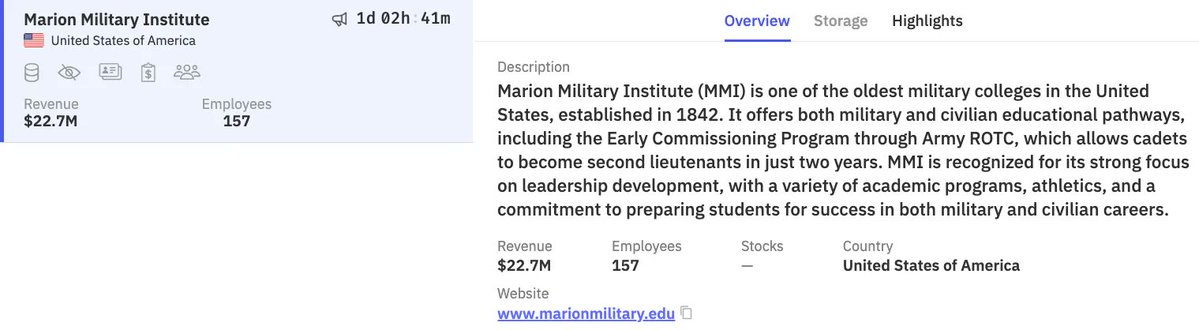
Countdowns like this are mostly pressure tactics, but the data behind them is the real concern. Military institutes hold structured identity data, internal communications, and sometimes training or administrative records that can be reused for impersonation or targeted scams. Once that information is copied, the timeline matters less than how it gets reused afterward.
English

United States 🇺🇸 - Marion Military Institute was allegedly compromised by the Worldleaks ransomware group, with the threat actors initiating a countdown threatening to leak the historic military college's data. dailydarkweb.net/marion-militar…
English

This isn’t just another supply chain story, it’s automation at scale. Exposed tokens and poisoned packages let attackers move through CI/CD pipelines and developer tools faster than teams can react, turning trust relationships into distribution channels. The real shift is how quickly this kind of access propagates across ecosystems once it’s seeded, not just the initial compromise.
English

🚨 TeamPCP Supply Chain Attack — Multi-Stage Cloud-Native Campaign Uncovered
A sophisticated campaign attributed to TeamPCP has compromised multiple ecosystems through a chained supply chain attack impacting Trivy, KICS, LiteLLM, and 45+ npm packages.
Key highlights:
• Initial access via exposed PAT (Pwn Request)
• Malicious packages pushed into CI/CD pipelines
• Lateral movement through Aqua Security’s Trivy ecosystem
• Deployment of Kubernetes wiper + worm (kamikaze.sh evolution)
• Expansion into Checkmarx and broader developer ecosystems
⚠️ The attack propagated in under 5 days, combining credential theft, poisoned dependencies, and automated distribution pipelines.
This campaign demonstrates how modern supply chain attacks are fast, scalable, and cloud-native by design, targeting developers as the new attack surface.
#CyberSecurity #SupplyChainAttack #ThreatIntel #DevSecOps #CloudSecurity #Kubernetes #Infosec #DailyDarkWeb

English

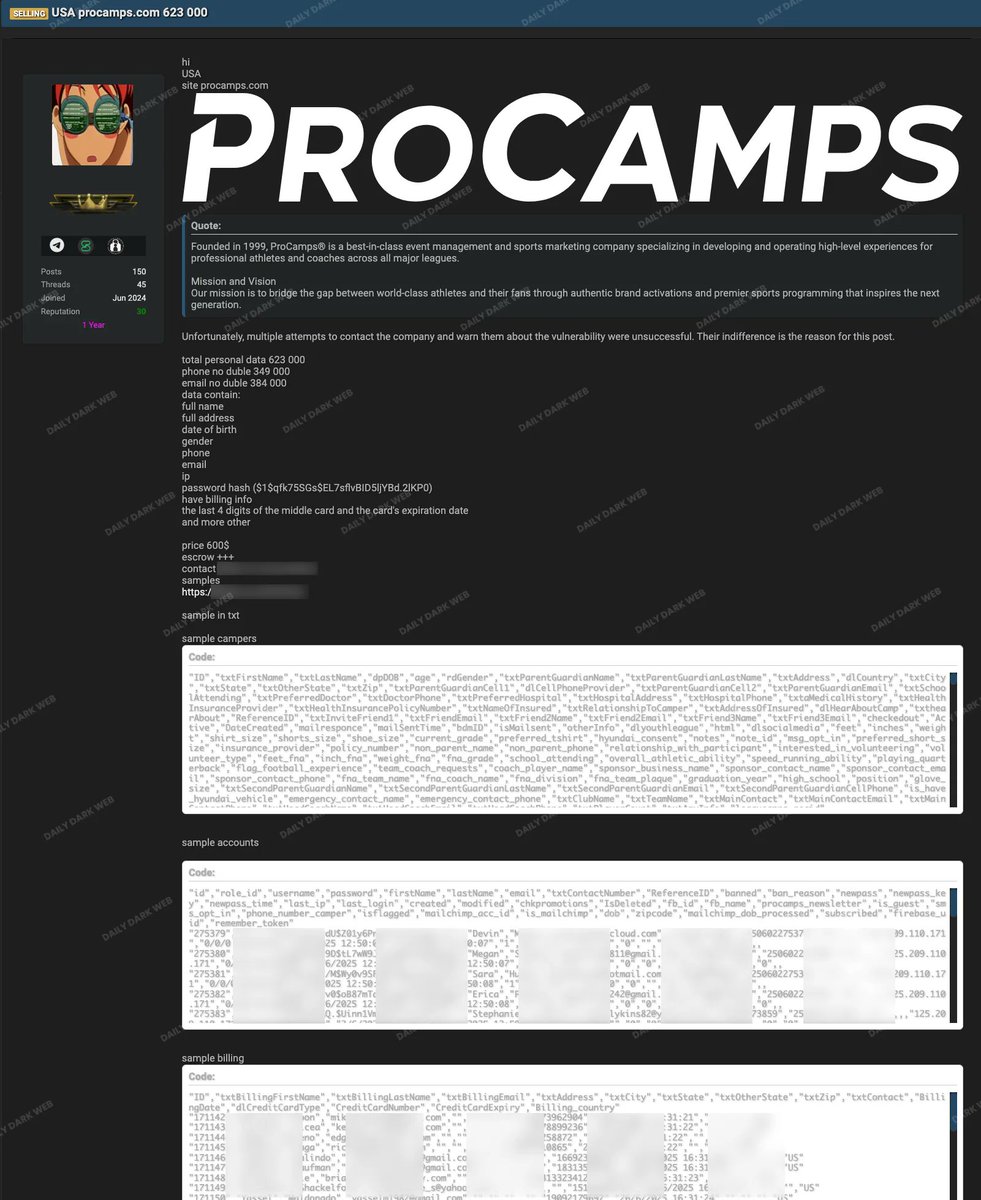
Password hashes plus personal and billing context is what makes this kind of leak stick. Even if the hashes aren’t immediately cracked, they get tested across other services, and any reused passwords fall quickly. Once hundreds of thousands of profiles circulate, it stops being about ProCamps and becomes about where those identities and credentials get reused next.
English

United States 🇺🇸 - ProCamps has allegedly been breached, exposing 623,000 personal records for sale, including names, addresses, password hashes, and partial billing information. dailydarkweb.net/procamps-suffe…
English

It’s spring cleaning season and your apps deserve a review too.
Try this quick cleanup:
📍 Switch your precise location → approximate
👥 Remove contact access most apps don’t need
🎤 Turn off mic/camera permissions when not in use
🧹 Delete old apps or accounts you no longer use
Small changes. Less data exposure.

English

Claims at that scale matter less for the headline numbers and more for what kind of access they imply. If configurations and source code are involved, the risk shifts from data exposure to insight into how environments are structured and secured. For a hosting provider, that kind of context can be reused across thousands of downstream customers, not just the original breach.
English

France 🇫🇷 - OVHcloud has allegedly been breached, with an actor claiming to sell data belonging to 1.6 million customers and 5.9 million websites, exposing personal information, source code, and configurations. dailydarkweb.net/ovhcloud-data-…

English

Compromising ESXi hosts suggests access at the infrastructure layer, not just an app-level breach. Splunk logs, ticketing data, and C-level emails together provide a map of internal activity, incidents, and decision-making that’s easy to reuse for targeted phishing or follow-on attacks. Once that operational visibility is exposed, it becomes a playbook for future intrusion, not just a one-time leak.
English

United States 🇺🇸 - Defion Security has allegedly been breached by an unnamed actor who compromised three ESXi hosts, resulting in the sale of Splunk logs, ticketing data, and C-level emails. dailydarkweb.net/defion-securit…

English

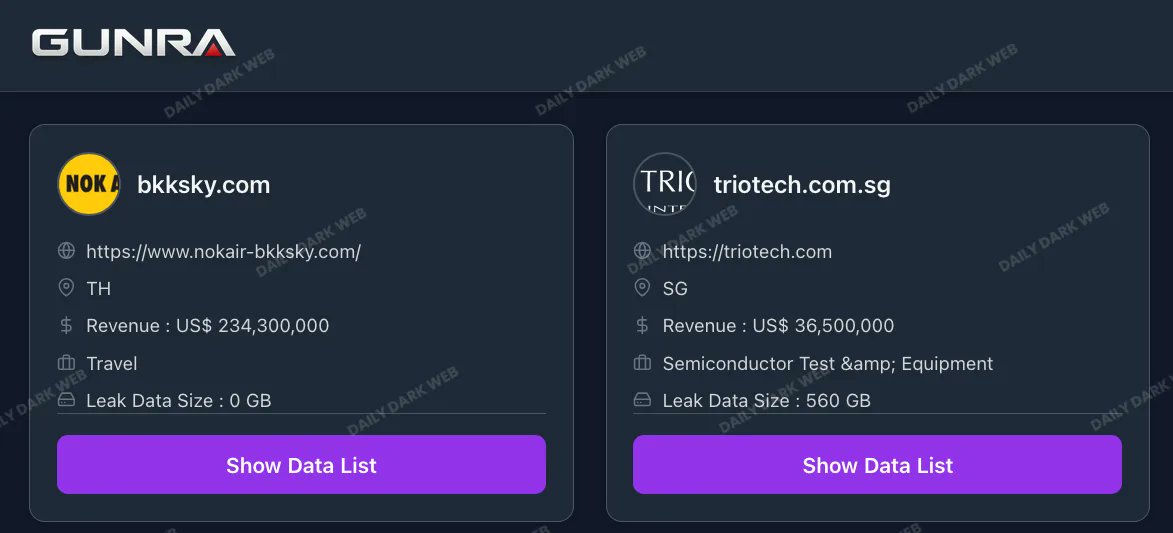
Semiconductor project files carry more value than typical corporate data. Designs, process details, and internal documentation can be reused for competitive intelligence or supply chain targeting without needing direct access to production systems. Once that kind of technical context leaks, it tends to have a longer shelf life than the ransomware claim itself.
English

The Gunra ransomware group claims to have breached BKK Sky 🇹🇭 and Trio-Tech International 🇸🇬, allegedly compromising semiconductor project files and internal data. dailydarkweb.net/gunra-ransomwa…
English

The 9-day gap is the part to watch. When incidents sit before disclosure, it’s usually time for data access, copying, and validation before anything goes public. Even if the breach scope turns out limited, that window is often enough for emails and account data to start circulating and getting reused in phishing tied to real user activity.
English

🚨 Crunchyroll has OFFICIALLY CONFIRMED A DATA BREACH.
“We are aware of the claims and are working with leading cybersecurity experts to investigate.”
⚠️ The incident reportedly occurred 9 DAYS AGO, with claims it was initially downplayed before being publicly addressed.

IDEAL NEWS@Idealnewscentre
🚨 Crunchyroll was reportedly breached via a TELUS partner, exposing ~100GB of user data (emails, IPs, and alleged credit card info). ⚠️ The incident allegedly occurred on March 12, 2026 and was contained within 24 hours. TELUS has confirmed a breach the same day, with reports of up to 1PB of data stolen overall. ❗ Crunchyroll has not yet issued an official statement.
English

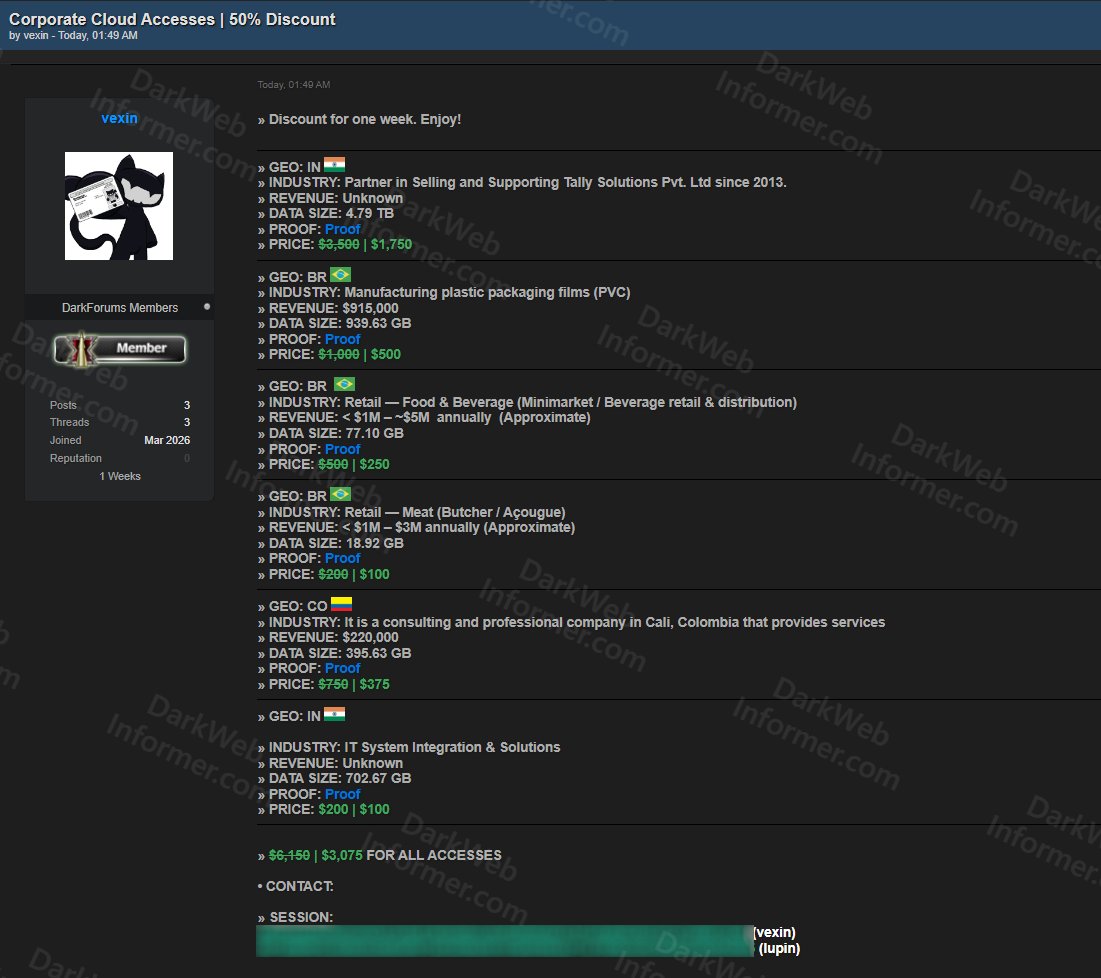
Discounted access listings like this are about volume, not sophistication. Selling multiple cloud footholds across industries suggests initial access brokerage, where attackers monetize entry points instead of exploiting them themselves. Once those accesses are resold, the risk shifts from one actor to many, each deciding how to turn that foothold into fraud, data theft, or deeper compromise.
English

‼️🇮🇳🇧🇷🇨🇴 A threat actor using the handle "vexin" is offering corporate cloud accesses at a 50% discount.
The listing includes seven compromised organizations across India, Brazil, Colombia, and India, spanning industries such as IT solutions, plastic packaging, food & beverage retail, meat retail, and consulting.
Data sizes range from 18.92 GB to 4.79 TB, with individual prices between $100–$1,750, or a bulk deal of $3,075 for all accesses.
English

Long time spans like 2013–2026 are what make retail breaches stick. Orders, invoices, and B2B data create a detailed history of customers and partners that can be reused for targeted phishing or supplier fraud that feels legitimate. Once that kind of longitudinal data circulates, it tends to get repackaged and exploited well beyond the original leak.
English

‼️🇫🇷 Alleged Breach of Airsoft-Entrepot Exposes 333K Customer Records, Orders, Invoices, and B2B Data From French Retailer Spanning 2013 to 2026
darkwebinformer.com/alleged-breach…
English

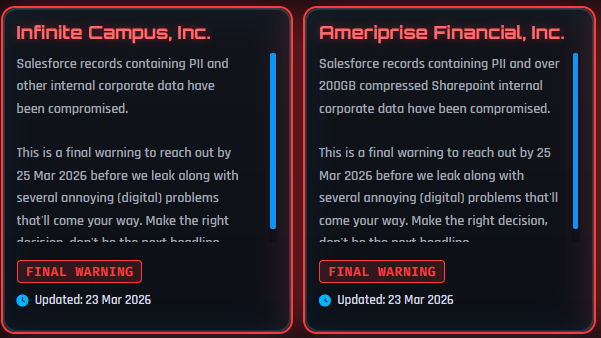
ShinyHunters usually signals data theft first, ransom second. When companies like a school platform and a financial firm are named together, it points to valuable identity and financial datasets that can be monetized even without payment. The threat isn’t just the leak, it’s how that data gets reused for fraud and impersonation once it’s already in hand.
English

Lobbying systems concentrate relationship data that isn’t meant to be public in full context. Schedules, contacts, and identification details can map influence networks and enable targeted impersonation or pressure tactics that feel legitimate. Once that kind of institutional context is exposed, it tends to be reused in ways that go well beyond the original leak.
English

Chile 🇨🇱 - The Government of Chile's Ley Lobby portal has allegedly been breached, with 250GB of sensitive lobbying records, official schedules, and personal identification data posted for sale. dailydarkweb.net/government-of-…

English

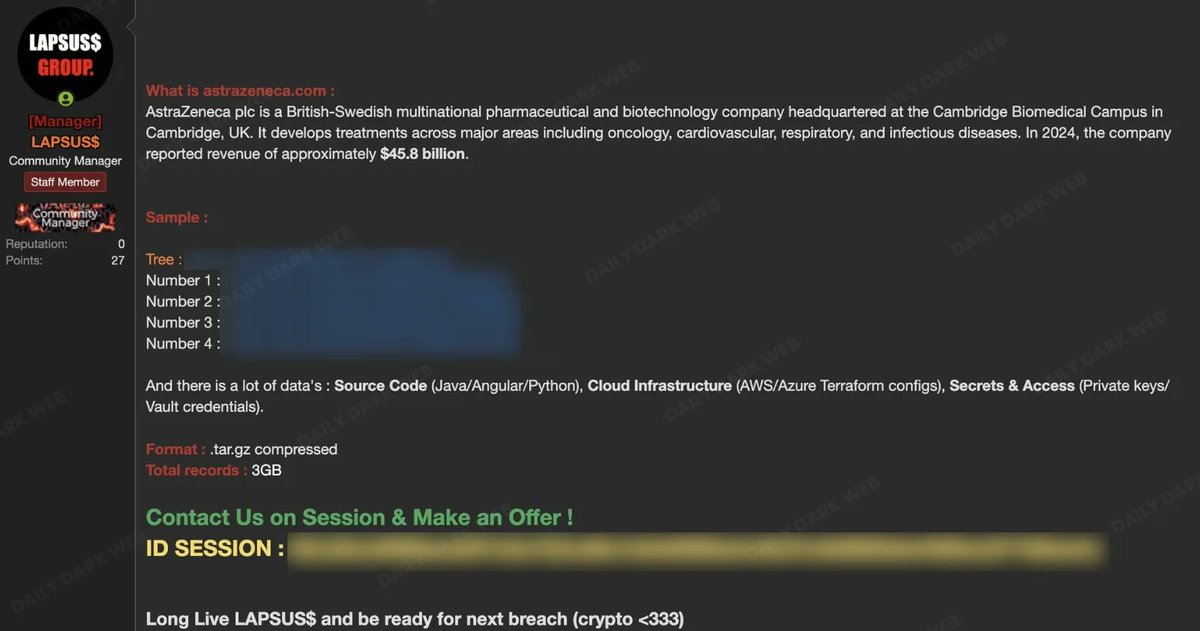
When source code, cloud configs, and access secrets show up together, the risk isn’t just IP loss, it’s potential reuse of access paths. Secrets and infrastructure details can let attackers test environments or pivot into connected systems without starting from scratch. Even a 3GB dump can carry outsized impact if it exposes how the environment is actually wired together.
English

United Kingdom 🇬🇧 - AstraZeneca has allegedly been breached by the LAPSUS$ group, who are attempting to privately sell a 3GB data dump containing source code, cloud infrastructure configs, and access secrets. dailydarkweb.net/astrazeneca-al…
English

Energy infrastructure data carries a different kind of risk than typical corporate leaks. Technical drawings and engineering certificates can reveal system layouts, dependencies, and operational constraints that don’t change quickly. Once that kind of information is exposed, the concern isn’t just data loss, it’s how those insights could be reused long after the breach claim.
English

Slovenia 🇸🇮 - Energetika Ljubljana allegedly suffered a breach exposing 2 TB of national energy infrastructure documents, including technical drawings and engineering certificates for the TE-TOL project. dailydarkweb.net/energetika-lju…

English

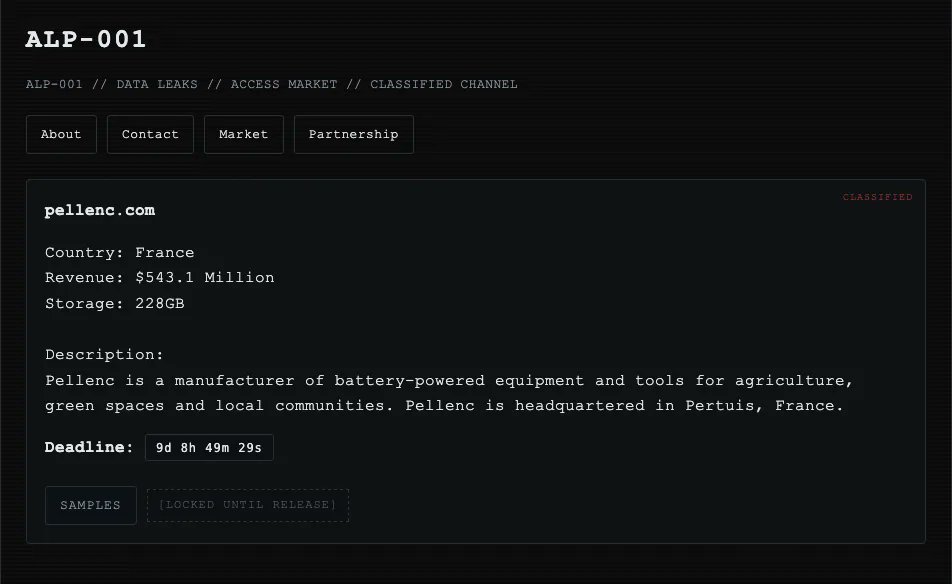
Agricultural manufacturers don’t just hold internal files, they sit in the middle of supplier, distributor, and customer networks. Corporate data at that scale likely includes contracts, pricing, and operational details that can be reused for fraud or competitive pressure. Once hundreds of gigabytes of that context are copied, the leverage extends well beyond the ransom demand.
English

France 🇫🇷 - Pellenc has allegedly been compromised by the Alp-001 ransomware group, which claims to have stolen 228GB of corporate data from the agricultural equipment manufacturer and is threatening a leak. dailydarkweb.net/pellenc-ransom…
English