Naka-pin na Tweet
JohnnyTime 🤓🔥
9.8K posts


JohnnyTime 🤓🔥
@RealJohnnyTime
Founder @ https://t.co/gcgrMm4Njh, JohnnyTime @ Youtube, Securing Web3 @ https://t.co/wJdpJyYcg0 & https://t.co/3d9aL8n5G8
Web3 Sumali Şubat 2012
1.4K Sinusundan12.6K Mga Tagasunod

The scariest part about delegatecall?
It preserves msg.sender and msg.value.
The victim thinks they're interacting with YOU.
But you're running malicious code in THEIR context.
It's identity theft for smart contracts.
smartcontractshacking.com/attacks/call-a…
English

How to steal millions in 4 steps:
1. Flash borrow 100k ETH
2. Dump on a DEX to crash price
3. Exploit a protocol reading that price
4. Repay loan, keep profit
If step 3 fails, the loan never happened. Zero risk.
smartcontractshacking.com/attacks/flash-…
English

This is really sad that @claudeai is taking the "Closed Garden" Apple approach.
GIF
dax@thdxr
opencode 1.3.0 will no longer autoload the claude max plugin we did our best to convince anthropic to support developer choice but they sent lawyers it's your right to access services however you wish but it is also their right to block whoever they want we can't maintain an official plugin so it's been removed from github and marked deprecated on npm appreciate our partners at openai, github and gitlab who are going the other direction and supporting developer freedom
English

paying the checkmark, I have been playing with AI :P
stela-dapp.xyz - starknet banana - best p2p
n4no3d.xyz - me and my wife sometimes like to print 3d shit so its basically for us, test version
apura.xyz - Primavera SQL connector: AI reports.
English

@RealJohnnyTime hehe nope, I tried a lot of them on the kam repo, but nothing :P
English

@RealJohnnyTime ur AI is looping defillama deployed addresses and simulating this for each address till exploited on fork for bounties? :P
English

That lens helps you review like an operator, not a checklist runner.
smartcontractshacking.com/tools/most-exp…
English

Weekend Challenge #8: What issue would you submit if you saw this in an auditing context, Mr. Hacker?
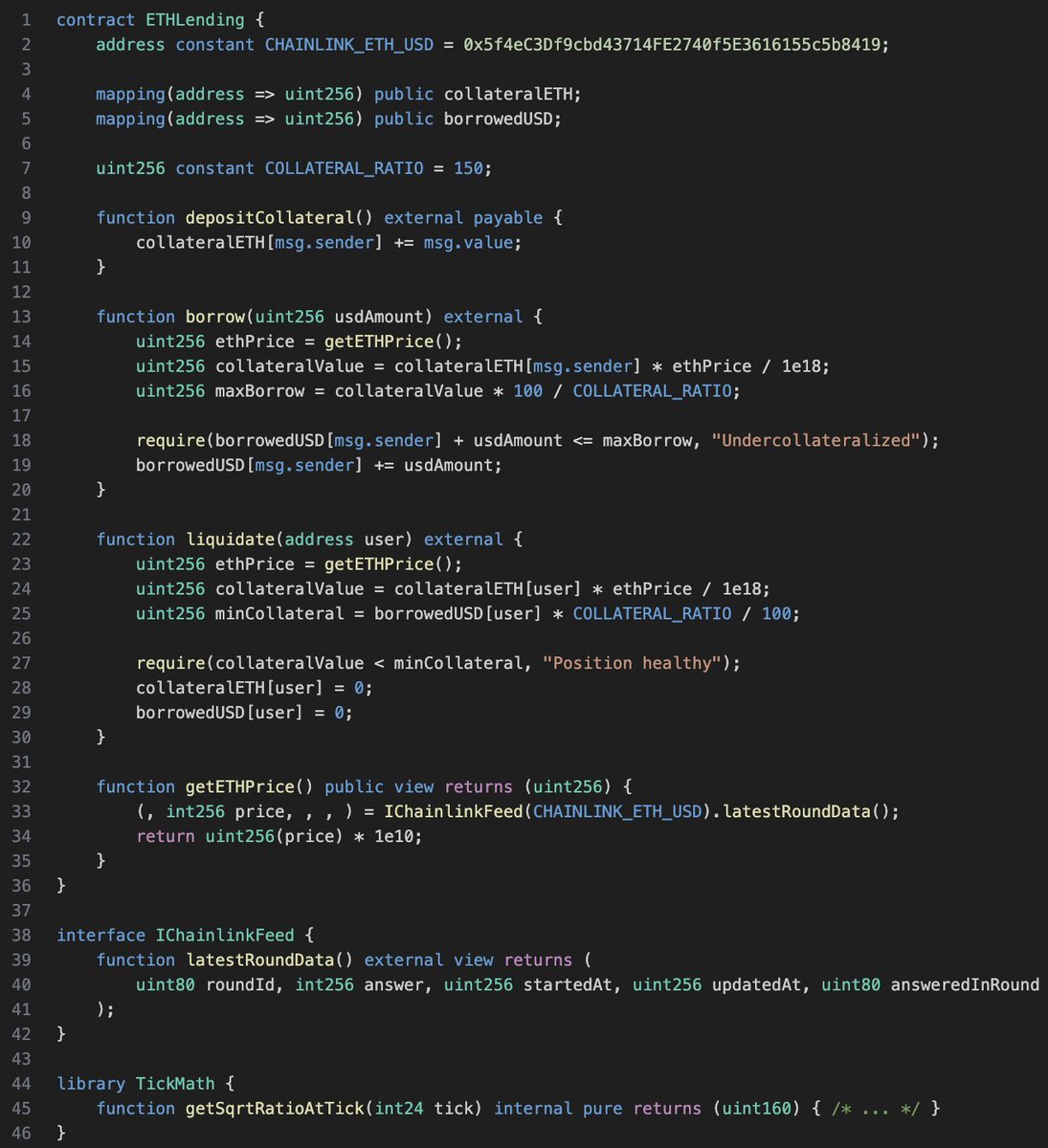
English

If your note can’t name the exact state change, it’s not a finding yet.
smartcontractshacking.com/learn/security…
English

If you’re starting in 2026, this roadmap is one of the few that’s practical and sequenced.
smartcontractshacking.com/learn/security…
English