SysTrack
30 posts



One of our most highly anticipated episodes, enjoy it!
...Let's learn how to train our Claudes :p ty @rez0__
Building Claude Skills as a Bug Bounty Hunter, part 1
English

OMG, what am I seeing here? 26 critical/high vulnerabilities in Google Chrome released at once?
chromereleases.googleblog.com/2026/03/stable…

English


We had to release this one before @rez0__'s brain started returning 429s.
Everything you always wanted to know about using AI to help you hack.
...or is it you who's helping the AI? 👀
youtu.be/qTX9u-EsjmM

YouTube
English

@Michael1026H1 That's a lot of bugs in a small space of time. Are YOU AI? Lol
English

@k_firsov 100% agreed. Even still, with advancements in Claude, it may reduce the attack surface, but it doesn't mean there will be no attack surface or no requirement for human logic in guiding Claude. These industries are going through changes, but we can adapt to the changes
English

So much drama today, people losing their minds over this "new" feature from Anthropic, calling it the death of pentesting and bug bounties. Even stocks tanked for companies that have nothing to do with it. Why?
Because most investors in this space don't know shit about security or what Claude AI actually dropped. We have been running vulnerability scans with various AI models, including Opus 4.6 for months already. This release is basically just a handy button to run what used to be a chain of prompts doing the exact same thing.
Investors: Buy back in.
Bug hunters and pentesters: relax and level up with it. Anthropic’s social media team: Bravo! This clickbait worked out!
Claude@claudeai
Introducing Claude Code Security, now in limited research preview. It scans codebases for vulnerabilities and suggests targeted software patches for human review, allowing teams to find and fix issues that traditional tools often miss. Learn more: anthropic.com/news/claude-co…
English

@Random_Robbie I tried reporting stuff like that but it usually gets pushed back if you cant prove impact. Even theoretical impact gets pushed back in my experience.
English

@my_stewpid @PeterSRWeb3 Appreciate that. None are disclosed yet and I haven't started writing things up publically yet. But maybe I'll start doing that.
English

@SysTrack40 @PeterSRWeb3 do you have links to your reports or write ups? I'd like to read
English

@ctbbpodcast @Hacker0x01 Fair play for doing this lads. Great interview, and for me, even though I'm new, this clears up a lot. Hopefully puts an end to the drama.
English

We said we'd sit down with @Hacker0x01 to ask all the hard questions, and we did!
In the episode below you'll find everything you wanted to know about whether or not your reports are being used to train LLMs, ToS changes, plans for the future and more!
youtu.be/Pa4wWv_ONjM

YouTube
English

@0xTib3rius Lol. Can I buy this demo video with resell rights on the video?
English

I am about to COMPLETELY disrupt the cybersecurity industry...💀💀💀
Presenting the Continuous Reasoning AI Pentester!
Multiple AI agents running every security tool under the sun against your environment, at record speeds. Full pentests achieved in less than AN HOUR.
Zero human input.
One hundred percent success.
English

@pxmme1337 @Hacker0x01 Didn't the overall payouts go up YOY though?
English

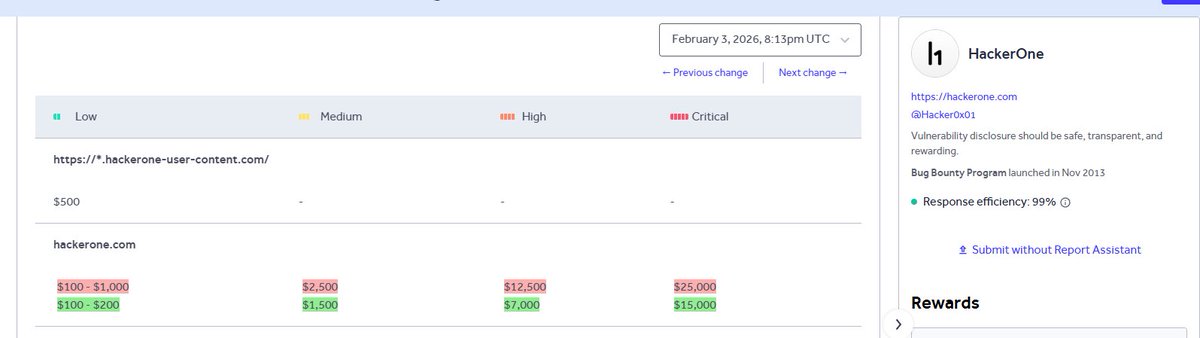
What is going on at @Hacker0x01 lately?
Join the discussion anonymously and express your thoughts for free on url.bugbounty.forum/p/nIzf1

English

ICYMI: I created an LLM-powered tool to detect CVEs before they're even published - and it's now powering vulnerabilityspoileralert.com.
This is a simple GitHub page statically generated using vulnerability-spoiler-alert-action. Check out the backtest findings at github.com/spaceraccoon/v… and let me know what you think the hit rate is!
I'm running this open-source vulnerability intelligence project using a personal API token, but maybe @AnthropicAI... or @OpenAI might want to support this? 👀
English