lostpacket
40 posts

@_lostpacket_
Threat Researcher at @_CPResearch_










The #FBI, @USTreasury, and @Israel_Cyber have released a joint #CybersecurityAdvisory on the Iranian cyber group Aria Sepehr Ayandehsazan aka Emennet Pasargad. Click for new tradecraft details, indicators, and mitigations: ic3.gov/CSA/2024/24103…





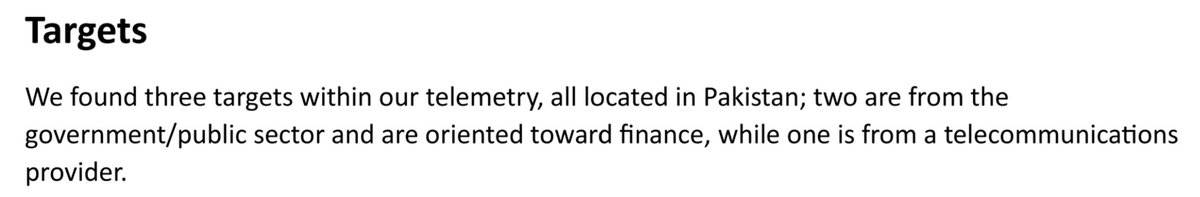
[4\5] ScarredManticore has been consistently targeting high-profile organizations in Saudi Arabia, UAE, Kuwait, Oman, Jordan, and Israel. The most commonly targeted sectors are Government and Telecommunications.




#CloudAtlas continues its operations and during the last year narrows its targeting : 🎯Focus on Russia, Belarus and conflicted areas in Ukraine and Moldova 👾New DLL to proxy connections through the victims’ machines. 👉research.checkpoint.com/2022/cloud-atl…