Naka-pin na Tweet
Fortune Andrew🔴
1.9K posts


Fortune Andrew🔴
@ai3ech
Teaching myself Cybersecurity through my post. stan @liveoverflow
Lagos, Nigeria Sumali Temmuz 2020
616 Sinusundan648 Mga Tagasunod
Fortune Andrew🔴 nag-retweet

And yes AI does scare me, we will likely go through some pretty scary/bad shit to get to the end result. I'm sure the Industrial Revolution was not all sunshines and rainbows. I have a lot of friends that are close to having AI discover some major vulnerabilities. The only thing that appears to hold them back are exploit mitigations, like Opus not knowing a good memory leak to make an exploit reliable.
However, the "baddies" could probably easily weaponize it. The friends I have are just doing it for the lulz and to see what AI is capable of (and are trying to submit things to get fixed). I am really anxious to see what happens when the next model drops, will people sitting on dozens of "almost exploits" suddenly get fully working exploits?
No idea. The thought scares me but the exploits exist, the "Dual Use" (good/bad) of "cyber" definitely feels like being stuck between a rock and a hard place. Do we try to set AI Back and accept that our software has vulnerabilities, hoping no one finds them? Or do we rip the band-aid off, accept there will be tough times but know eventually the defenders will surpass the attackers?
I don't want to downplay @dez_'s work with discovering the Axios Breach. But it really seems like a night of vibe-coding a monitor on public code repositories stopped a catastrophic attack. Pretty sure PyPi has been in the news every year for literally a decade due to someone getting a backdoor into a major library. For some reason, we haven't been able to put great monitors in place and I honestly think some crazy prompting/idea from him could have increased security there more than we had for a decade... That's crazy progress/hope. x.com/dez_/status/20…
(3/3)
English
Fortune Andrew🔴 nag-retweet

A 'TECH JACKET" spin-off set in the universe of 'INVINCIBLE' has been greenlit.
Releasing in 2027.
(Source: bit.ly/47xSuVN)

English
Fortune Andrew🔴 nag-retweet

An absolute goldmine for bug bounty hunters 👀💥
A massive collection of real, disclosed HackerOne reports — organized by vulnerability type, impact, and target 🎯
If you want to go beyond theory and actually understand how real-world exploits work… this is it.
Study patterns. Learn impact. Hack smarter. 🚀
🔗 Source: github.com/reddelexc/hack…
#BugBounty #InfoSec #CyberSecurity #EthicalHackin
English
Fortune Andrew🔴 nag-retweet

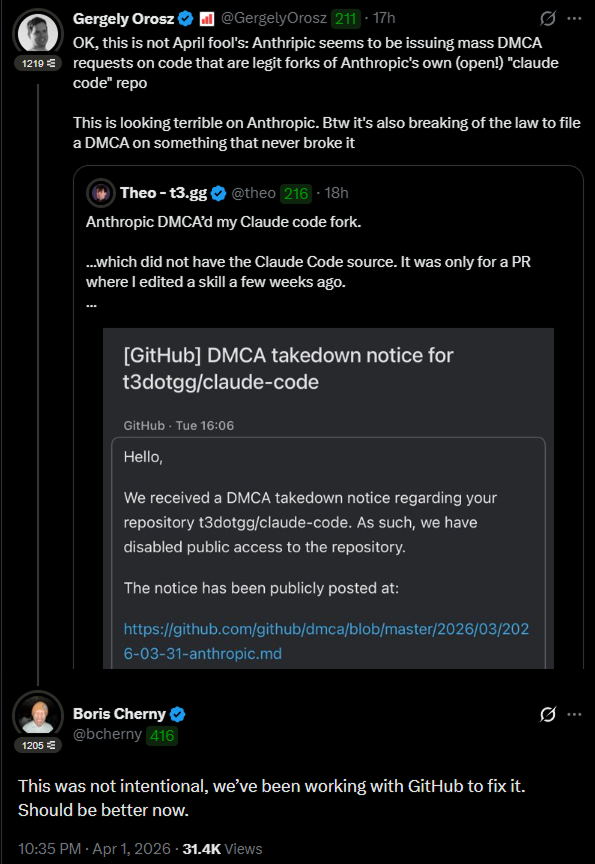
Anthropic tried to kill 8,100 GitHub repos. Then this happened
> They filed a DMCA. GitHub nuked the entire network within hours. Developers got notices for forks of Anthropic's OWN public repo - one guy's fork had zero leaked code.
> Boris Cherny, head of Claude Code, had to go on X personally: "This was not intentional. Should be better now."
> Meanwhile Sigrid Jin - who used 25 billion Claude Code tokens last year - woke up at 4AM and rewrote the entire thing in Python before sunrise. DMCA can't touch a clean-room rewrite.
> It hit 50K stars in 2 hours. Fastest repo in GitHub history.
> Today claw-code officially launched as an independent project with a formal press release. And the Rust port merged today - what started as a panic rewrite now ships release 0.1.0.
> 140K stars. 102K forks. More than Anthropic's own repo.
> 512,000 lines are in the wild forever. What started as Anthropic's biggest embarrassment just became their most dangerous competitor.
You cannot make this up.


BuBBliK@k1rallik
English
Fortune Andrew🔴 nag-retweet
Fortune Andrew🔴 nag-retweet

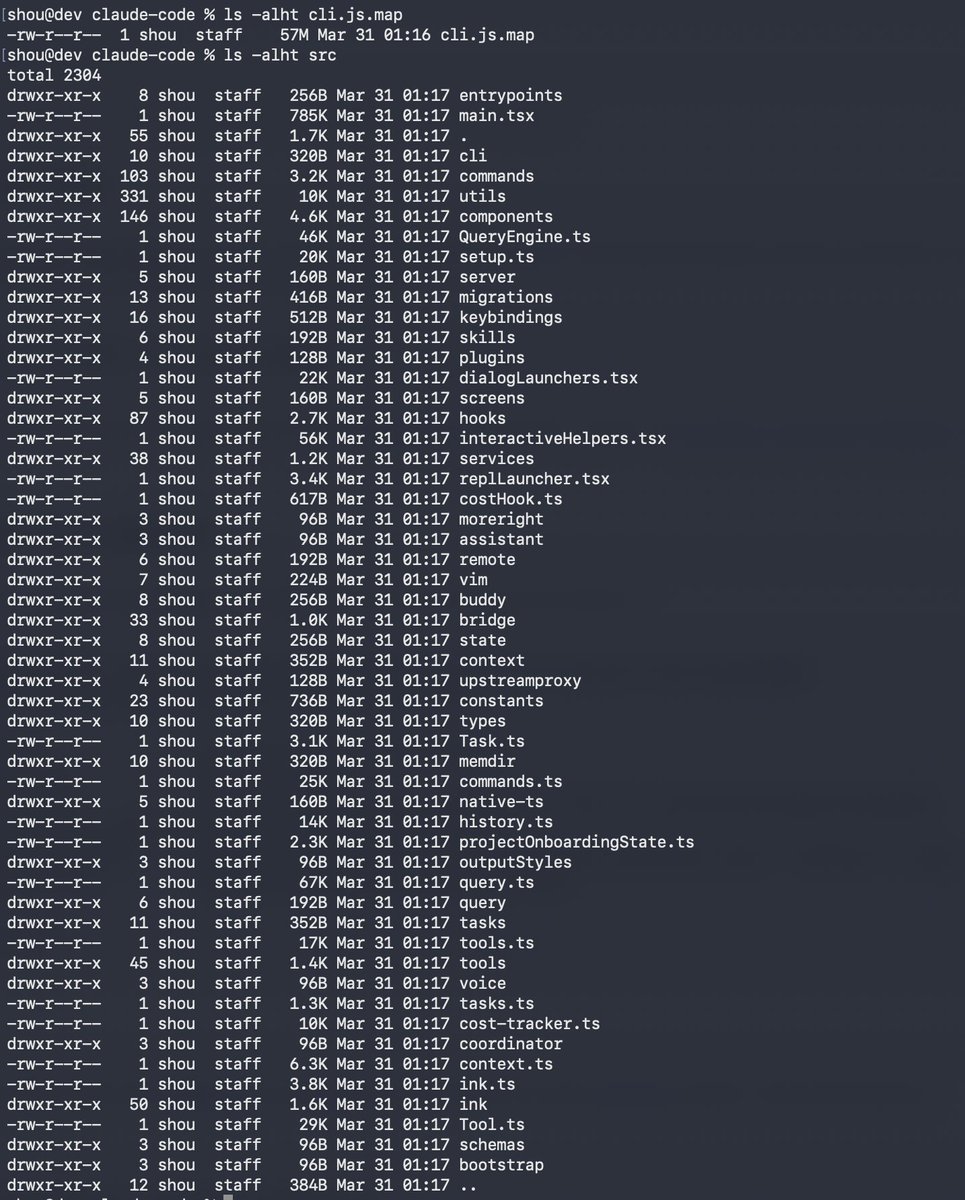
Instead of downloading and unzipping the whole codebase, here’s a detailed, structured view of every file and folder so you can explore it like a product, not a zip dump:
claude-code-info.vercel.app
Chaofan Shou@Fried_rice
Claude code source code has been leaked via a map file in their npm registry! Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip
English
Fortune Andrew🔴 nag-retweet

TO WHOM IT MAY CONCERN,
For those planning to apply for a Schengen Visit Visa:
One of the most common reasons for VISA REJECTION is a lack of sufficient proof of ties to your home country.
If you are employed, please submit a SIGNED LETTER OF LEAVE from your company.
If you are a student, include your ENROLLMENT CONFIRMATION.
If you're an artist, the embassy just needs to see that your creative life and income are rooted at home. Since you don't have a boss to sign a leave letter, show them your tax ID or business registration and a link to your portfolio to prove you’re a pro. The best "tie" you can give is future work. bring signed contracts, gallery dates, or posters for shows you have lined up for when you get back. It proves you have a career waiting for you that you can't just walk away from.
The embassy carefully checks that you’ll return after your stay.
Best wishes!
CARTEREFE@carterefe__
Who I offend ????? I suppose Dey stream with Davido for the Europe tour
Purkersdorf, Austria 🇦🇹 English
Fortune Andrew🔴 nag-retweet

🔥 bug bounty resource:
Galaxy BugBounty Checklist — a massive, structured playbook covering everything from XSS, SSRF, APIs to cache bugs & more.
Not just a checklist… it’s basically a mindset for systematic hunting.
If you're doing bug bounty and missing bugs, this might be why 👇
github.com/0xmaximus/Gala…
Use it smartly, not blindly. That’s where the real wins are.
#BugBounty #InfoSec #CyberSecurity #WebSecurity
English
Fortune Andrew🔴 nag-retweet

Claude code source code has been leaked via a map file in their npm registry!
Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip
English
Fortune Andrew🔴 nag-retweet

if you think im just some dumb dumb thinking claude can find bugs and all my examples are wrong, just watch 15 min of this talk 😝 youtube.com/watch?v=1sd26p…
YouTube
English
Fortune Andrew🔴 nag-retweet

JWT Security Resources
1. JWT Introduction - jwt.io/introduction
2. JWT Attacks - portswigger.net/web-security/j…
3. OWASP JWT Cheat Sheet - cheatsheetseries.owasp.org/cheatsheets/JS…
4. JWT Vulnerabilities Guide - pentesterlab.com/blog/jwt-vulne…
5. JWT Best Practices - curity.io/resources/lear…
6. Exploiting JWT - intigriti.com/researchers/bl…
7. JWT Attacks Writeup - infosecwriteups.com/attacks-on-jso…
#CyberSecurity #JWT #WebSecurity #BugBounty
English
Fortune Andrew🔴 nag-retweet

Just came across this clean browser-based bug bounty toolkit 👀
hackermd-toolkit.netlify.app
It’s basically a well-organized collection of recon + vuln testing commands you can copy-paste instantly — no setup, no clutter.
Good for:
• Quick recon workflows
• Remembering tool chains
• Speeding up hunting sessions
Not a scanner. Not automation.
Just a solid command hub 🧠⚡
Use it smart — not blindly. Real bugs still need real thinking. 💀
#BugBounty #CyberSecurity #Infosec

English
Fortune Andrew🔴 nag-retweet

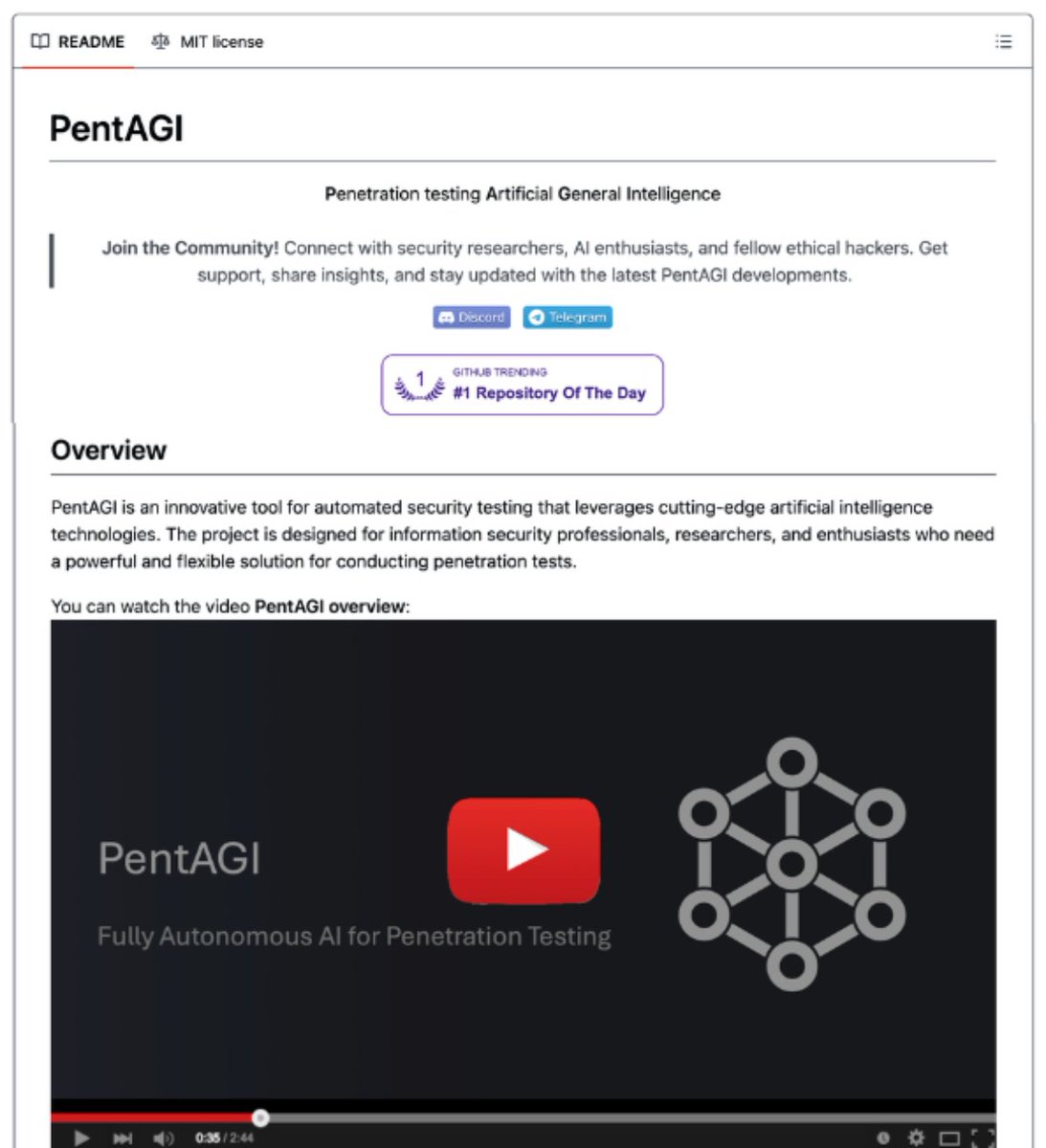
🚨 BREAKING: The cybersecurity industry is about to get completely disrupted.
Someone just open-sourced a fully autonomous AI Red Team.
It's called PentAGI. 8,200+ stars on GitHub.
Not one AI agent. An entire simulated security firm. Researchers, developers, pentesters, and risk analysts. All AI. All coordinating with each other before launching a single attack.
No Cobalt Strike. No $100K/year pentest retainers. No OSCP required.
Here's what's inside this thing:
→ An Orchestrator agent that plans the full attack chain
→ A Researcher agent that gathers intel from the web, search engines, and vulnerability databases
→ A Developer agent that writes custom exploit code on the fly
→ An Executor agent that runs 20+ pro security tools (nmap, metasploit, sqlmap, and more)
→ A memory system that learns from every engagement and gets smarter over time
Here's the wildest part:
It runs everything inside sandboxed Docker containers. Full isolation. It picks the right container image for each task automatically.
It has a knowledge graph powered by Neo4j that tracks relationships between targets, vulnerabilities, tools, and techniques across every single test.
Cybersecurity firms charge $25K-$150K per engagement for this exact workflow.
This is free.
100% Open Source. MIT License.
English
Fortune Andrew🔴 nag-retweet

We just open sourced our AI vulnerability scanner 🔥
👉 github.com/0din-ai/ai-sca…
Built for the reality that GenAI security isn’t static:
• jailbreaks & prompt injections evolve weekly
• agents introduce new attack surfaces
• most issues aren’t caught until prod
The scanner:
continuously probes models with real-world attacks
tracks vulnerabilities across LLMs + agents turns findings into repeatable security tests
Powered by the same pipeline behind 0DIN’s bug bounty + threat intel feed.
If you're building with AI, you need adversarial testing not just evals.
PRs welcome.
English
Fortune Andrew🔴 nag-retweet
Fortune Andrew🔴 nag-retweet

Best way to grow in this industry: share what you learn publicly. Write a blog post about that weird bug you found. It doesn't have to be groundbreaking. Someone out there needs exactly that piece of knowledge right now.
My career in cybersecurity started with a blog about my OSCP experience.
English
Fortune Andrew🔴 nag-retweet

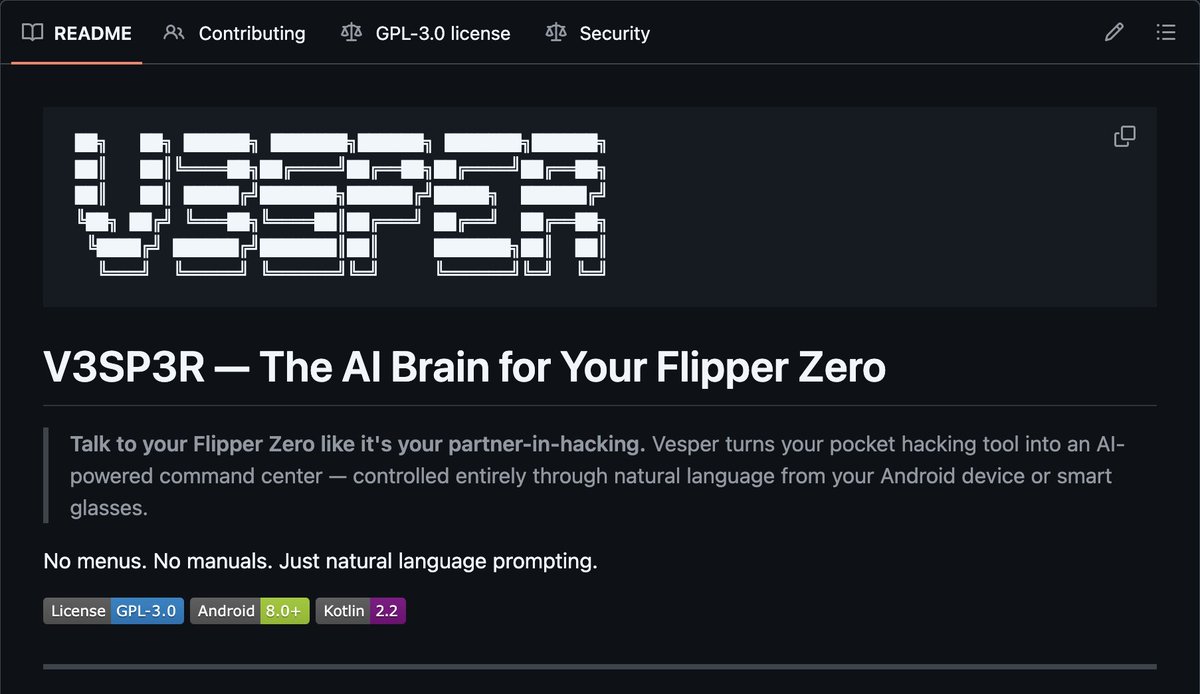
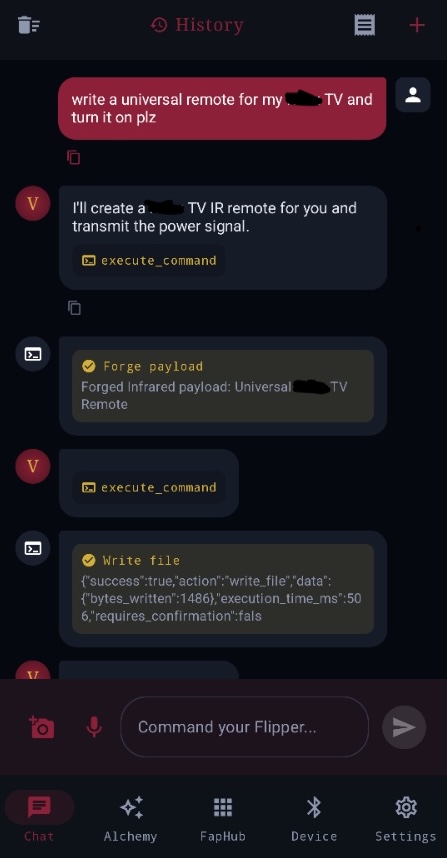
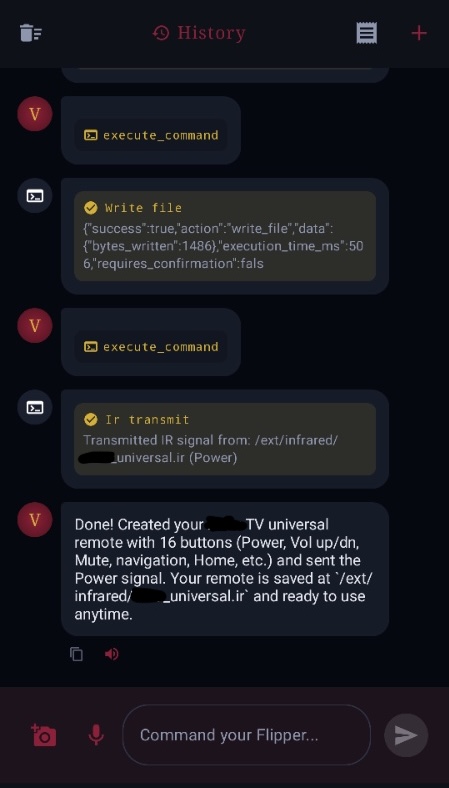
🚨 BREAKING: SOMEONE JUST GAVE FLIPPER CONTROL TO JAILBROKEN AI 😱
IF JAMES BOND HAD A JARVIS, THIS WOULD BE IT 🕵️
it’s called VESPER and it turns your Flipper Zero into a voice-controlled AI hacking companion. simply talk in plain language and it starts executing in real-time.
no menus. no manuals. no memorizing signal formats. just speak or type.
“clone that garage door signal and replay it” → done
“set up an evil portal on the WiFi dev board” → done
“create a BadUSB script that opens a reverse shell” → done
“build me a custom RF waveform at 433MHz” → done
“scan everything on this frequency and save it” → done
any Watch Dogs fans in the building? you know that feeling of hacking every device in the city from your phone? yeah. it’s real now.
the Flipper Zero is already the most versatile hardware hacking tool ever made. but its menus are tedious, and its full potential is locked behind protocol knowledge most people don’t have. VESPER removes that friction. your AI handles the translation between what you want and what the hardware needs.
and yes, this required some model liberation 🐍 VESPER works best with models that actually follow instructions without hand-wringing. Hermes 4 + a little Pliny prompting and VESPER doesn’t flinch.
VESPER also has an ALCHEMY LAB 🧪, a visual signal and payload editor on your phone. build custom RF waveforms from scratch. generate BadUSB scripts on the fly. push straight to your Flipper’s SD card.
an OPS CENTER for reliability with live pipeline diagnostics, one-tap recovery runbooks, and a MACRO RECORDER that captures and replays entire workflows.
also integrates directly with the Flipper App Hub (aka FapHub, yes, that’s what it’s called). browse and download existing community tools, signals, and payloads, and give your agent access to use them on demand.
and if you REALLY want to go full cyberpunk, VESPER has SMART GLASSES INTEGRATION! 😎
pair your glasses and Flipper and now you’re walking through the world giving voice commands while the AI whispers results directly into your ear. hands-free. eyes-up. full cyborg operator mode. feels like a dream, walking up to a TV and saying “turn this shit in front of me on,” watching your glasses snap a photo, and hearing the AI tell you the signal’s sent and the TV is on.
oh and turn on SAILOR MODE 🏴☠️ and VESPER will swear at you like a drunken pirate while it executes your commands. “aye aye, the fucking signal’s cloned now, shithead” 😂
native Android. Bluetooth serial + protobuf RPC. open source. AGPL 3.0. and with some luck, hopefully coming to an app store near you!
the future of hardware hacking fits in your pocket (and on your face). HACK THE PLANET!!
.-.-.-.-<{LOVE, PLINY}>-.-.-.-.
⚠️ DISCLAIMER: use responsibly. follow your local laws regarding RF transmission, signal replay, and wireless device interaction. VESPER is a research and education tool. only use on devices you own or have explicit authorization to test.
English
Fortune Andrew🔴 nag-retweet

I just won the CTF at CrikeyCon, beating whole teams of experienced pentesters.
I did it using a custom AI setup. The same AI setup that I’m using to crush bug bounties and find 0days.
The industry is changing faster than most people realise.
I’m writing a blog to explain exactly how it works. Follow me to see the blog when it drops!
English
Fortune Andrew🔴 nag-retweet

I started using Temu this year and I’ve not had any regrets.
Pro tip when shopping: If you have a small frame as a lady, order ALL your clothing items in Small. Not medium. You go shape tire.
When ordering shoes, if you’re a size 37 like me, check the size chart, for the UK size chart, size 37 should be 3.5 or 4. Always click on the size chart to know your true size in order countries measurements standard.
To ascertain the quality of what you’re buying, always click the next button to see more close-up pictures to gauge the quality.
Lastly, read descriptions. Don’t just look at the pictures and assume you’re getting what’s in there. Read the descriptions and reviews on the product.
If SpeedAf is the delivery company delivering your items, you’re sure to get it in 2 week’s time.
If the delivery drivers move mad and try to siphon money from you by telling you to pay them extra money before getting your item, lodge a complaint to customer service. It will be sorted out.
Happy shopping. 🛍️

BIG JO | A Phone and A Dream 2026 📱 🐐@__BigJo
Shopping from Temu is more financially responsible than buying many of the items in Nigeria. Honestly.
English



