Naka-pin na Tweet
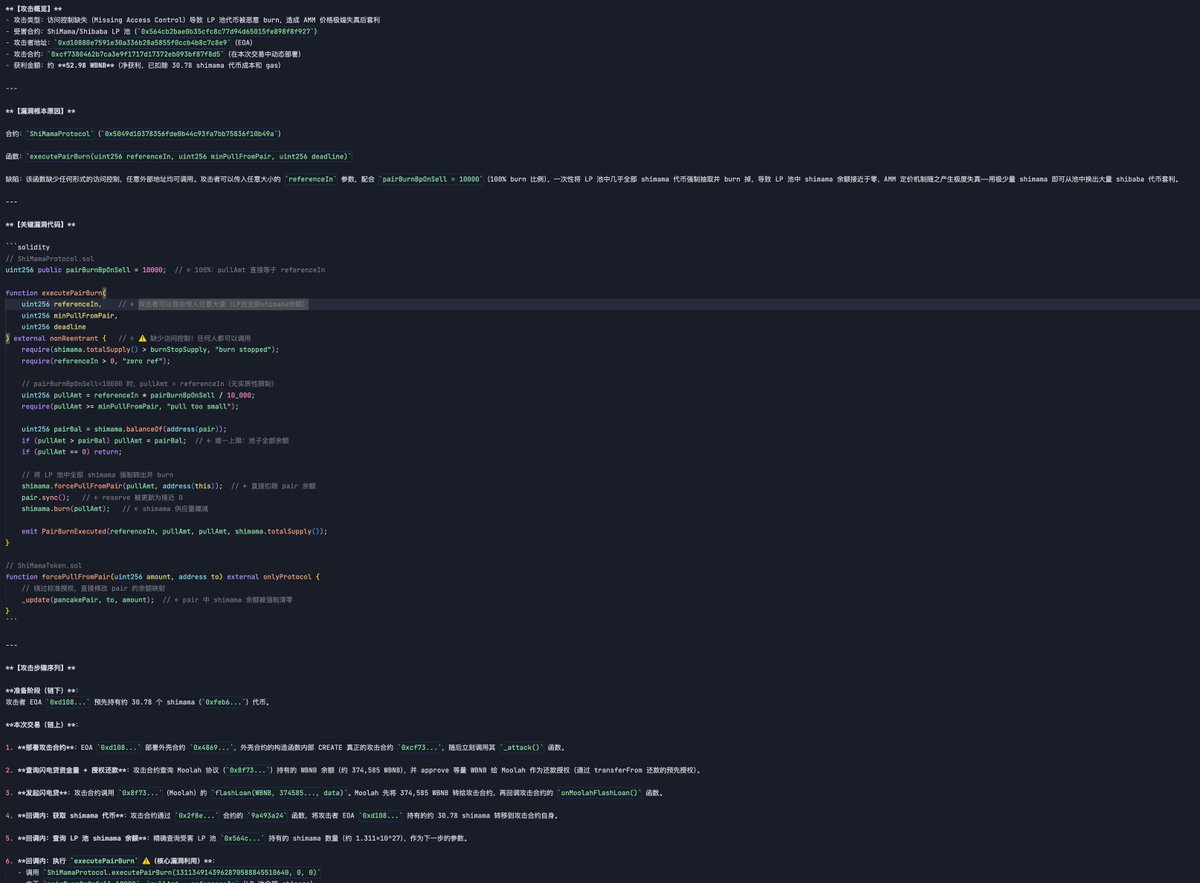
1/ UraniumFinance UPDATE: From on-chain I noticed that Uranium dev has connected with GarudaSwap dev (which got exploited to 0 as well). And Github info shows that one of GarudaSwap's devs is wesoha, who is the Meycoin's dev and employed by meeyland.com
English