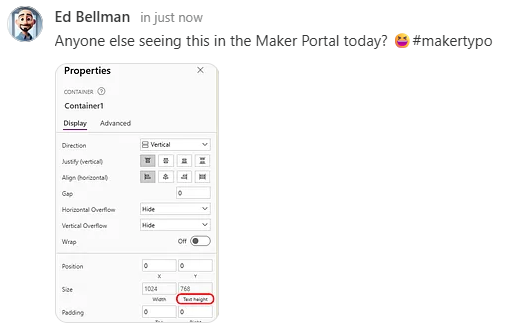
Ed Bellman
2.6K posts


Ed Bellman
@EdBellman
Husband, father, geek, AFOL, former IT guy, M365 & Power Platform. Principle Consultant Power Apps at @P3Adaptive / Opinions are own / Disagreement ≠ hate
Ohio شامل ہوئے Ocak 2010
381 فالونگ127 فالوورز
Ed Bellman ری ٹویٹ کیا

The @Bengals should sign Ja’Marr to a new record deal on Monday, and then on Tuesday announce restructured deals for Burrow and Ja’Marr and a new deal for Higgins to keep them all three together. And then on Wednesday an extension for Trey.
See, that was easy…!
English

Classic Overwatch. Classy rewards.
Enter for a chance to win an Overwatch Collector’s Edition and other prizes 🤩
Now - Nov 30:
🤝 Follow us
❤️ Like this post
💬 Comment your favorite Overwatch: Classic Hero with #Overwatch2Sweepstakes
Official rules: blizz.ly/4i8BqsT

English
Ed Bellman ری ٹویٹ کیا
Ed Bellman ری ٹویٹ کیا

If you ever want to understand the margins of life in the NFL do a study of the Chiefs’ 9-0 versus the #Bengals’ 4-6.
English
Ed Bellman ری ٹویٹ کیا

Forget about sideline scowling. Joe Burrow needs to start getting in the faces of officials who blow calls, like Tom Brady used to do. Because it works. nbcsports.com/nfl/profootbal…
English
Ed Bellman ری ٹویٹ کیا

The exclamation point at the end of a great play ❗️
Barstool Sports@barstoolsports
What if I told you a wide receiver from Incarnate Word changed the touchdown celebration game as we know it
English
Ed Bellman ری ٹویٹ کیا

Any word on the street about @Azure Maps connector support for the Power Platform? Only 8 months until EOS for Basic keys…
@rezadorrani @aprildunnam @MSPowerPlat @AzureMaps
English
Ed Bellman ری ٹویٹ کیا
Ed Bellman ری ٹویٹ کیا
Ed Bellman ری ٹویٹ کیا
Ed Bellman ری ٹویٹ کیا

Please share this far and wide. As far and wide as you can. NIST Password Guidelines for 2024 are in the process of being updated.
This is a HUGE pet-peeve of mine (when vendors in particular are still operating like its 2017 and keep changing passwords every 60 days, STOP DOING THIS, it's outdated and has been shown to put you MORE at risk than less -- NIST explains why it does in this document, meticulously outlining user behavior**) so I'm sharing this in the hopes all of you will pass it along to your bosses.
The Special Publication series governing passwords is SP 800-63 "Digital Identity Guidelines".
The 2024 version is 800-63-4.
Here: pages.nist.gov/800-63-4/
The companion docs are also on that link. They are 800-63A, 800-63B and 800-63C. These are different documents for different scenarios in play at your org.
The previous update was in2020.
The changes in the 2020 version from the 2017 version were numerous but one of them was that the password verification method should NO LONGER require passwords be changed at specific intervals (i.e. every 60 days) but in the following circumstances instead:
1. After a breach/compromise
2. User request
2024 repeats this and adds a bunch more guidlines but here is a screenshot of page 13 of the new 800-63-4 (note the # 4 after it) which outlines how your systems should now and moving forward, be handling passwords.
This goes for Active Directory, too. All your systems which have passwords should align with these guidelines provided there isn't another standard or framework you must adhere to which overrules this.
Most frameworks, however, have moved away from arbitrary password resets and complexity rules.
**We cybersec researchers and hackers use wordlists from breaches in a variety of different ways. Hackers use them in tooling to crack passwords whereas researchers use breach dumps to see the kinds of passwords users are creating and the psychology behind them.
Using complexity rules gets you the user psychology of:
Password1
Password2
and so on
Use phrasing instead and allow for spaces, which is important. Humans type phrases with spaces. They also mention phish-resistant methods and most vendors are on-board with MS going to be turning off all Legacy Auth next month, across all free accounts and tenancies.
I'm so excited for the new changes!
Ok I'm off my soapbox.
Share the love! Thank you!

English
Ed Bellman ری ٹویٹ کیا

Would totally purchase this, if they’d let us…
Willie Lutz@willie_lutz
ESPN proposed individual team packages for $70 that would've allowed you to watch all 17 of your favorite NFL team's games. The league said no.
English
Ed Bellman ری ٹویٹ کیا