پن کیا گیا ٹویٹ
🖤ֆǟʍǟɛʟ🐼
154.7K posts


🖤ֆǟʍǟɛʟ🐼
@FragmentedSoul5
#OreoSec 🎭 the #Truth is well HïÐÐêñ ïñ þlåïñ §ïgh†. #OpSec ł₦₣Ø₴Ɇ₵ It's easier to fool people than to convince them that they have been fooled.#INFP #xuᴎi⅃ 🐧
🕍🦉 ֆօʟօʍօռ'ֆ ₮Ɇ₥₱ⱠɆ 🦉🕍 شامل ہوئے Ocak 2017
722 فالونگ2.7K فالوورز
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا

🚨 Hackers Using Google Cloud Storage to Bypass Email Filters and Deliver Remcos RAT
Source: cybersecuritynews.com/hackers-using-…
Cybercriminals are always looking for smarter ways to bypass security, and their latest method is both simple and effective.
The campaign starts with phishing emails linking to pages hosted on storage.googleapis[.]com, a legitimate Google domain.
These pages mimic Google Drive login screens with branded logos and file icons for PDF, DOC, SHEET, and SLIDE documents.
Victims are prompted to sign in to “view a document in Google Drive,” unaware that the page is built to harvest their email address, password, and one-time passcode. After the fake login, the victim is tricked into downloading a JavaScript file named Bid-P-INV-Document.js.
#cybersecuritynews #cyberattacknews

English
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا

process where event.type == "start" and process.name :"SnippingTool.exe" and process.args: ("ms-screensketch:edit?&filePath=%5C%5C*", "ms-screensketch:edit?&filePath=http*", "ms-screensketch:edit?&filePath=\\\\*")
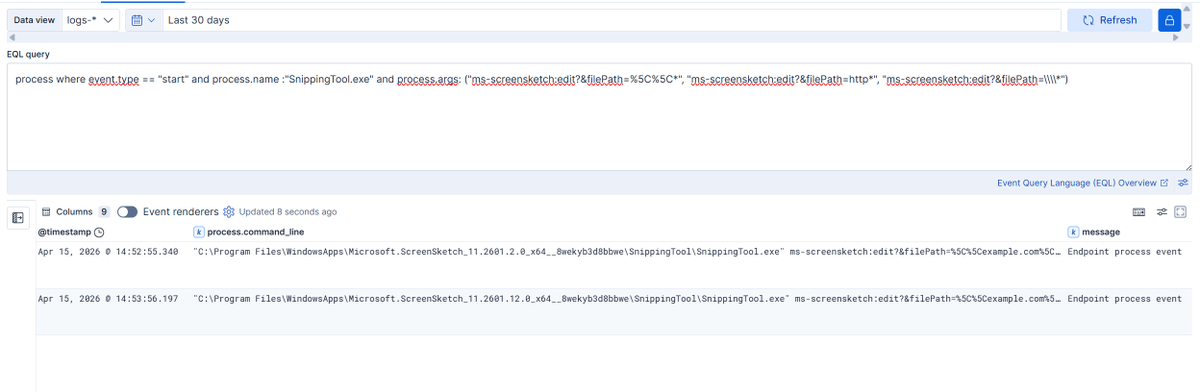
BlackArrow@BlackArrowSec
Microsoft has addressed a one-click NTLM leak vulnerability affecting Windows Snipping Tool (CVE-2026-33829), discovered by our researcher Marcos Díaz (@Calvaruga). ➡️ Read the write-up: github.com/blackarrowsec/… ➡️ Microsoft bulletin: msrc.microsoft.com/update-guide/v…
English
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا

Wars are never about to save or protect the people
Its about Profit, Money and Control.
The rich get richer
The poor gets poorer
Peace is oppression
Freedom is prison.
The world will never know Peace.
#Anonymous for #Justice
English
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا

GitHub - zeroc00I/LLM-anonymization: Reverse proxy for Claude Code that anonymizes sensitive pentest data (IPs, hashes, credentials, hostnames, PII) before it reaches Anthropic. Dual-layer detection: local Ollama LLM + regex safety net, with per-engageme github.com/zeroc00I/LLM-a…
English
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا

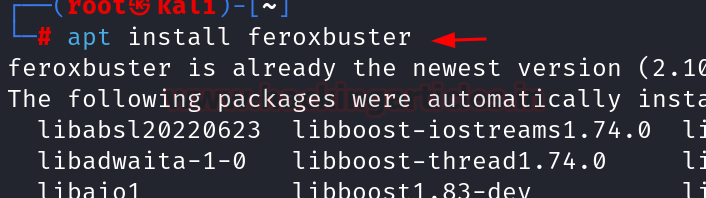
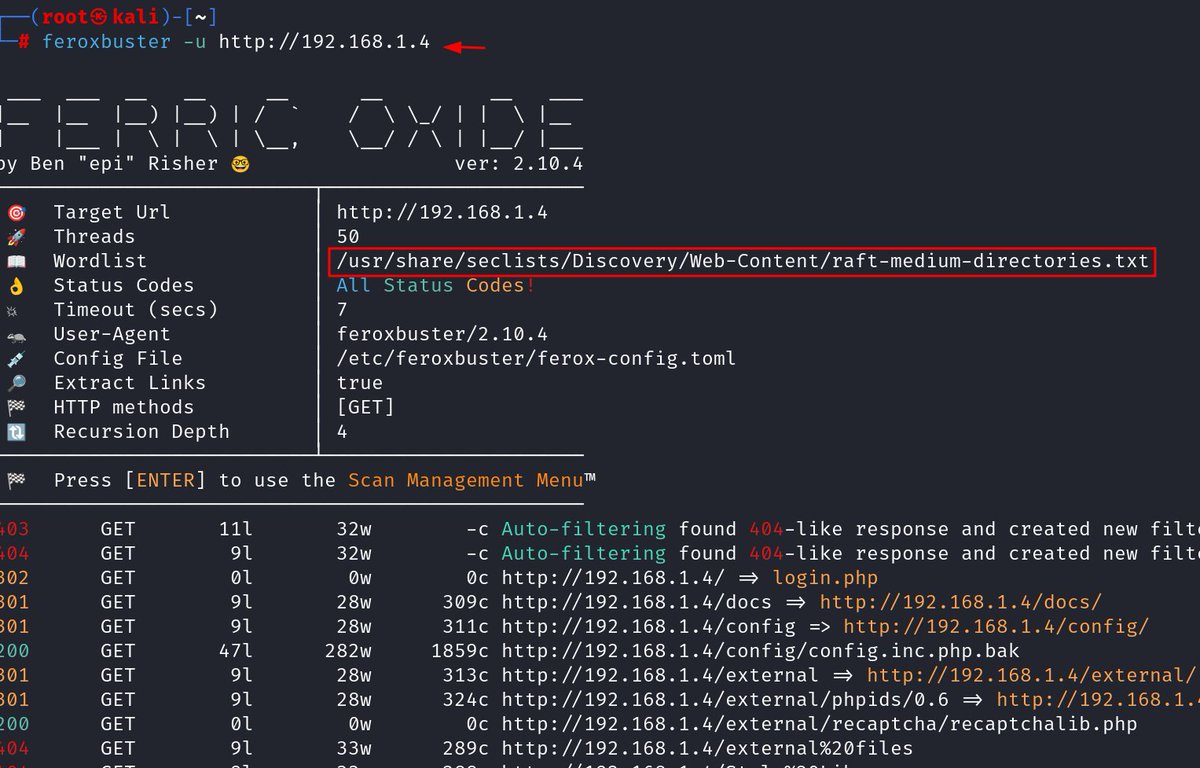
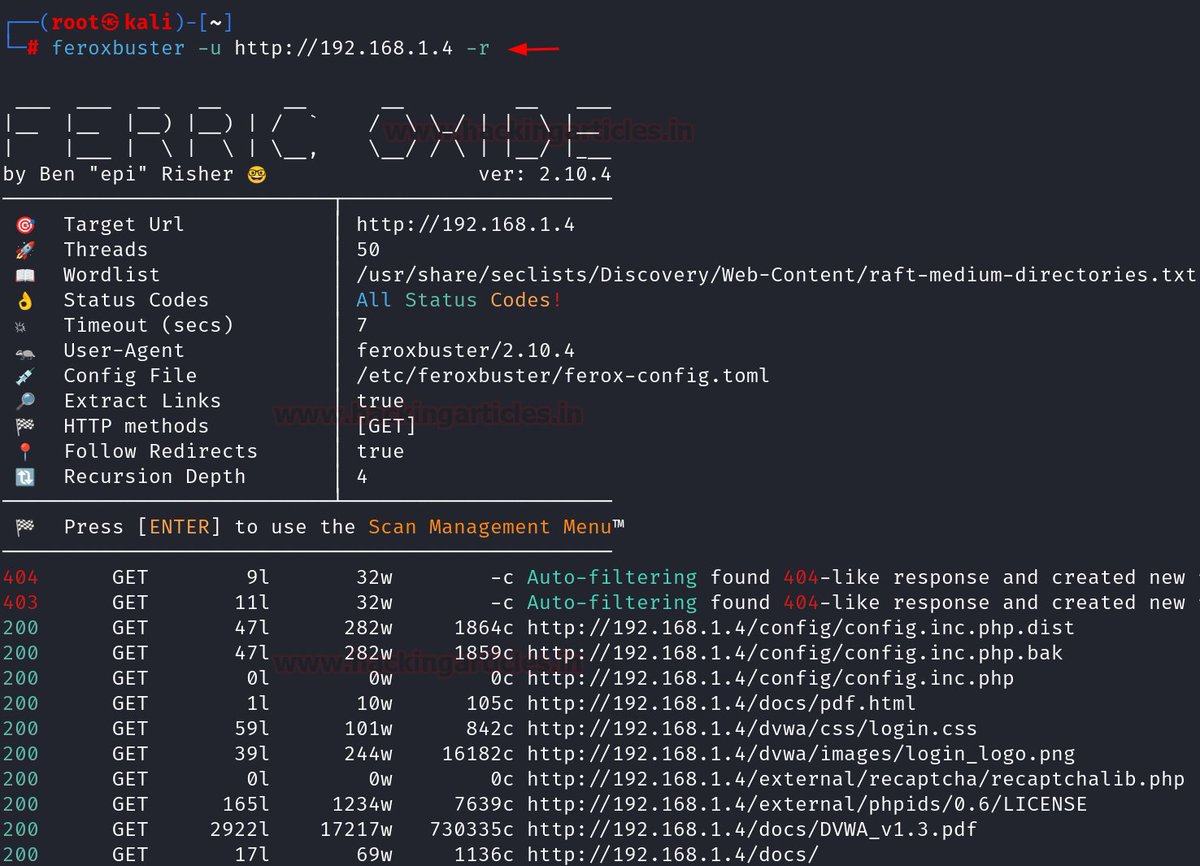
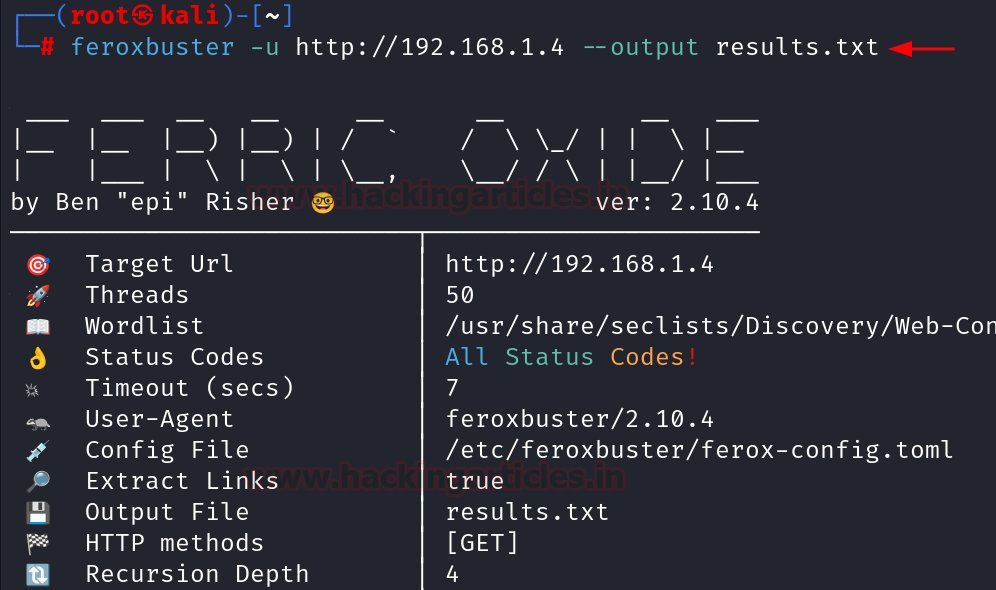
A Detailed Guide on Feroxbuster
🔥 Telegram: t.me/hackinarticles
✴ Twitter: x.com/hackinarticles
Feroxbuster is a high-performance web content discovery tool used by pentesters and bug bounty hunters to find hidden directories, files, and endpoints in web applications through wordlist-based brute forcing. ()
⚡ Key Features of Feroxbuster
🚀 Fast directory & file enumeration
🔁 Recursive scanning of discovered paths
📚 Custom wordlist support
⚙️ Advanced filtering options
🌐 Proxy & custom header support
🛠️ Common Feroxbuster Techniques
📂 Directory brute-forcing
🔎 Hidden file discovery
🧭 Recursive web path scanning
⚡ Filtering responses by status codes
📡 Web application reconnaissance
📖 Article: hackingarticles.in/a-detailed-gui…
#CyberSecurity #EthicalHacking #Pentesting #BugBounty #InfoSec #Recon
English
🖤ֆǟʍǟɛʟ🐼 ری ٹویٹ کیا
Microsoft has addressed a one-click NTLM leak vulnerability affecting Windows Snipping Tool (CVE-2026-33829), discovered by our researcher Marcos Díaz (@Calvaruga).
➡️ Read the write-up: github.com/blackarrowsec/…
➡️ Microsoft bulletin: msrc.microsoft.com/update-guide/v…
English