Pixis ری ٹویٹ کیا

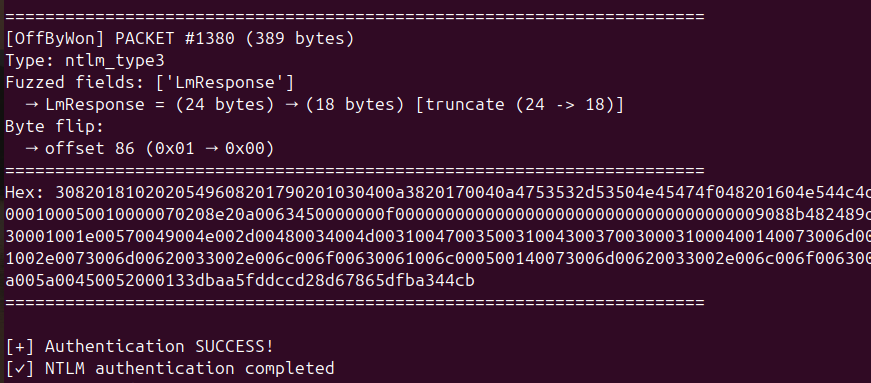
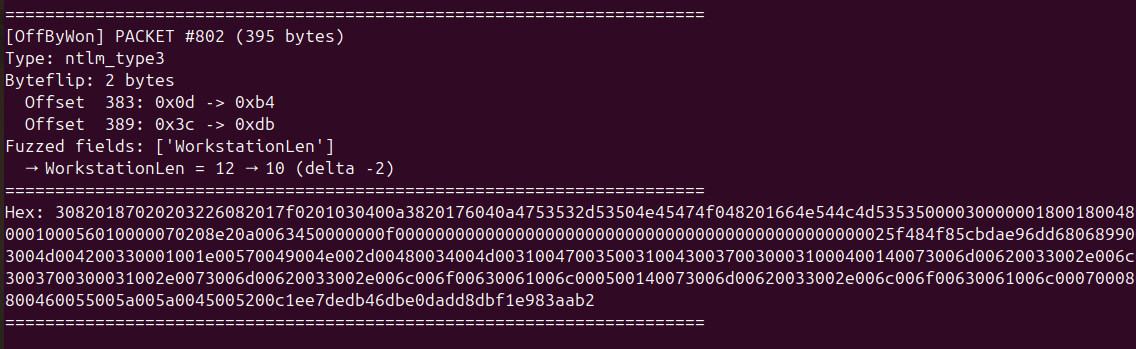
The purpose of this article is to explain NTLM relay, and to present its limits.
en.hackndo.com/ntlm-relay/

English
Pixis
2.6K posts





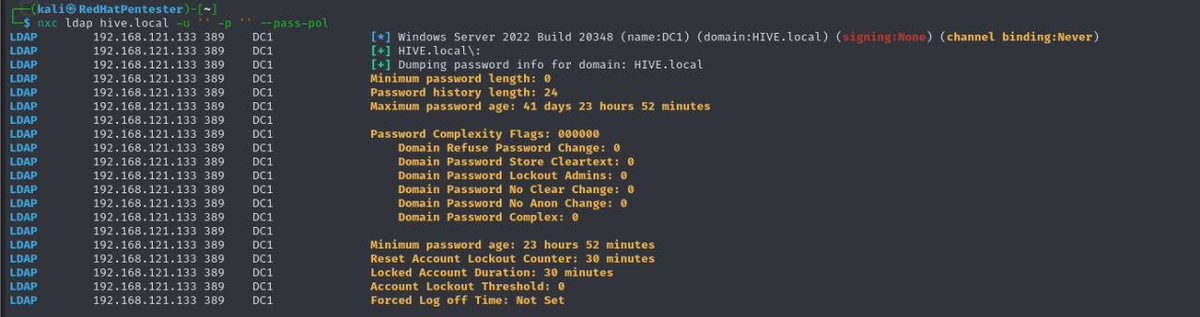
@sekurlsa_pw You can find an excellent write up on password spraying from hackndo’s blog here: en.hackndo.com/password-spray… Mandatory reading IMO for AD network pentesters









L'utilisation de gestionnaires de mots de passe est une pratique courante et recommandée pour des raisons de sécurité. ⚠️ Une de ses limitations ? La compromission d'un poste de travail peut entraîner le vol des secrets du gestionnaire.




🚀Our tool keycred for KeyCredentialLinks and Shadow Credential attacks now works with updated domain controllers again! It turns out, Microsoft violated their own specs. Try it out: github.com/RedTeamPentest…