QuanChain
3.1K posts


QuanChain
@Quan_Chain
The only self migrating/adapting quantum proof blockchain that makes quantum security continuous. Join the telegram community: https://t.co/5QURQ3TJHB
شامل ہوئے Ekim 2015
892 فالونگ90.9K فالوورز

Fixing cryptography after a quantum breakthrough isn't an upgrade. It's a fire drill with no exits.
Google's latest research has renewed serious questions about the long-term security of Bitcoin's signature scheme. The concern isn't theoretical anymore: it's a question of timeline, and no one has a reliable answer.
Most chains treat cryptography as a constant. QuanChain treats it as a variable. The LQCp/h Oracle monitors quantum capability across 7 threat levels (QTL-0 through QTL-6) and triggers automatic migration to stronger key hierarchies before the threat arrives, not after.
If your chain requires a community vote to upgrade its cryptography in a crisis, is that actually a security model?

English

Quantum computing stocks will make some investors rich — and leave others holding hardware that can't protect what it processes.
WallStreetZen's breakdown of IonQ, Microsoft's topological qubit push, and the $1 trillion projection is a reasonable investor framing. But nobody in this video asks the harder question: as these machines scale, what happens to the blockchain infrastructure running underneath the economy they're meant to power?
QuanChain's LQCp/h Oracle monitors that exact inflection point across 7 threat levels, triggering automatic migration before it becomes a recovery problem.
If 2030 is the deadline for quantum stocks to mature, what's your deadline for the protocols those systems will break?
English

Google setting a 2029 PQC deadline is a useful signal — but a fixed deadline assumes the threat arrives on schedule.
The Quantum Bull covers this well, and the Google framing is genuinely significant: one of the most well-resourced quantum research organisations on the planet is saying migrate now, not in 2029. That urgency is real.
What the video doesn't address is what happens when threat timelines compress. 2029 is an estimate, not a guarantee — and a static migration target leaves no room for a system that adapts as capability shifts.
That's precisely why QuanChain's LQCp/h Oracle monitors global quantum computing capability across 7 threat levels in real-time, moving funds to stronger protection automatically rather than waiting for a calendar date.
If your security posture is tied to a fixed year, who updates it when the year changes?
English

Qubit stability is the real bottleneck in quantum computing — not raw processing power.
The StockBox interview with Delta Gold CEO Mike Jones is worth watching for that reason. The claim that nano gold particles exhibit unusual superconducting behaviour at the atomic level, and that this could produce more stable qubits, is scientifically plausible. Professor Harry Ruda at University of Toronto is legitimate. The research direction is real.
What's missing from the conversation: stable qubits accelerate the timeline on breaking elliptic curve cryptography. Nobody asked that question.
At what qubit stability threshold does classical blockchain encryption become genuinely vulnerable?
English

The cyber campaign targeting a Southeast Asian government used three separate threat clusters simultaneously. That's not opportunistic: that's a coordinated operation designed to ensure at least one vector succeeds regardless of defences.
Traditional security thinking assumes you harden one perimeter. This campaign deployed HIUPAN, PUBLOAD, and multiple loader families in parallel, meaning any single-layer defence was always going to be insufficient.
The same logic applies to cryptographic infrastructure. Static security models assume the threat stays constant. QuanChain's LQCp/h Oracle monitors quantum capability across seven threat levels in real-time, and DTQPE's 20 security levels escalate automatically as conditions change: no manual intervention, no chain-wide migration panic.
Multi-vector attacks don't wait for you to schedule an upgrade window. Why do most blockchain protocols still assume they'll get one?

English

The CLARITY Act won't just regulate DeFi yield. It'll expose which protocols were built for compliance and which were built for chaos.
Markus Thielen at 10x Research has it right: ring-fencing yield shifts value toward regulated infrastructure. That's not a bug in the CLARITY Act, it's the point. Protocols that can't demonstrate clean, auditable mechanics will lose ground to those that can.
This is why QuanChain's architecture was built around verifiable, cross-chain state from the start. The Cross-Chain Resilience Protocol anchors quantum-proof state to Solana, Sui, Ethereum, and Polygon — the kind of transparent, multi-chain accountability that regulators can actually audit.
The question worth asking: if regulatory clarity accelerates institutional adoption, does that make security infrastructure a prerequisite rather than a feature?

English

83x growth in card issuance is impressive. The cryptography underneath it is not.
Stablecoin payments scaling fast across Southeast Asia means the signature schemes protecting those transactions are under more scrutiny than ever. Volume alone doesn't make infrastructure secure: it makes the consequences of a cryptographic failure larger.
QuanChain's LQCp/h Oracle monitors quantum computing capability across 7 threat levels in real-time, triggering automatic migration to stronger key hierarchies before a threat becomes a breach, not after.
The question isn't whether Southeast Asia's payment rails can scale. It's whether they're being built with cryptography that can adapt as the threat environment changes. Is "fast growth" a good enough answer to that?

English

Google set a 2029 deadline for quantum-resistant migration. Bitcoin hasn't responded.
That silence is an engineering problem, not a political one. A chain with no formal migration path and no adaptive cryptography layer will face a single decision point: upgrade everything at once or don't. Neither option is clean.
The harder question isn't whether to migrate. It's how you migrate without freezing the network, forking the community, or leaving legacy addresses exposed during the transition window.
QuanChain's DTQPE handles this differently: 20 security levels with oracle-triggered escalation and automatic address migration as threat conditions change. No single panic upgrade. The chain adjusts incrementally as the LQCp/h Oracle tracks global quantum capability across QTL-0 through QTL-6.
If Bitcoin's developers begin a serious PQC discussion, what's the realistic governance path to get consensus before 2029?

English

Memory overread bugs leak data. Quantum computers break the keys protecting it. Most security strategies only account for one of these threats.
CVE-2026-3055 scores 9.3 on CVSS and is already under active reconnaissance: attackers don't wait for patches, they probe while defenders are still reading the advisory.
The real question isn't whether your infrastructure gets scanned. It's whether the cryptographic layer protecting whatever leaks can hold under escalating pressure. QuanChain's LQCp/h Oracle monitors quantum capability across 7 threat levels in real-time, triggering automatic migration to stronger key hierarchies before conditions deteriorate, not after.
Classical vulnerabilities and quantum risk aren't separate problems. At what point does the industry stop treating them as independent threat models?
English

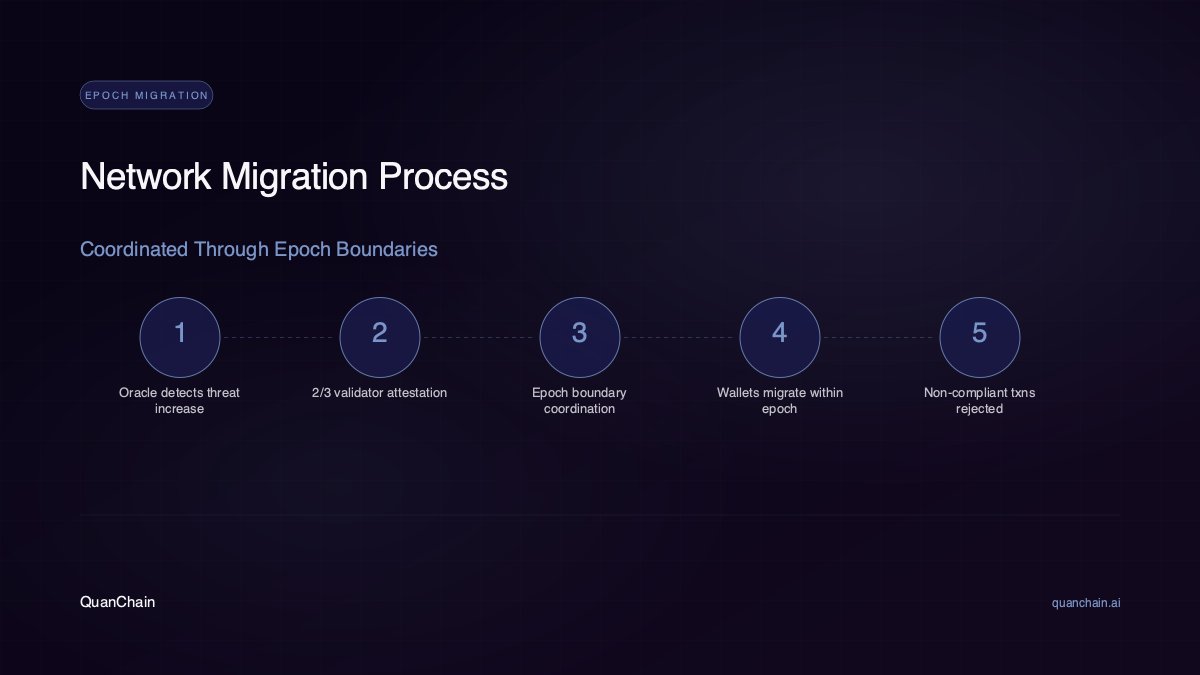
𝗘𝗽𝗼𝗰𝗵 𝗠𝗶𝗴𝗿𝗮𝘁𝗶𝗼𝗻 𝗣𝗿𝗼𝘁𝗼𝗰𝗼𝗹
When the Quantum Oracle detects a threat level increase, the network coordinates migration through epoch boundaries:
⬩ Oracle detects LQCp/h drop below threshold
⬩ New threat level broadcast to all validators via GossipSub
⬩ At least 2/3 of validators must attest to the change
⬩ At the next epoch boundary, the new minimum security level takes effect
⬩ Wallets below the minimum have one full epoch to migrate
⬩ After the grace period transactions from non-compliant wallets are rejected
No panic. No hard fork. Orderly, coordinated, protocol-level migration with validator consensus at every step.
English

The FBI Director's personal Gmail was breached. Let that establish the baseline for what "secure infrastructure" actually means right now.
Iran-linked actors accessing Kash Patel's account is a reminder that credential-based attacks don't need quantum computers: they just need one unprotected inbox. The attack surface isn't the algorithm, it's the static credential sitting exposed until someone decides to use it.
This is exactly the failure mode DTQPE was designed around. Security that sits fixed at one level until it's too late isn't security, it's a countdown. QuanChain's 20-level threat escalation means protection adjusts as conditions change, not after the breach is already in the news cycle.
If the head of the FBI can't secure his own email, what assumptions are the rest of us making about credentials we've left static for years?
English

Supply chain attacks are getting more creative, and the security industry is still debating patch cadence.
TeamPCP hid credential-harvesting code inside a .WAV audio file within two malicious telnyx PyPI packages. The kind of obfuscation that slips past static analysis precisely because nobody expects a sound file to be the threat vector.
This is a different category of risk to quantum cryptography, but it points at the same underlying problem: security assumptions get exploited at the layer nobody is watching.
QuanChain's LQCp/h Oracle monitors global quantum capability across 7 threat levels and triggers automatic key migration before exposure: the same principle of watching the layer most infrastructure ignores.
If your security model only responds after a known attack pattern, what's the realistic detection window when the payload is inside a WAV file?
English

𝗠𝗶𝗴𝗿𝗮𝘁𝗶𝗼𝗻 𝗖𝗼𝘀𝘁 𝗙𝗼𝗿𝗺𝘂𝗹𝗮
Migration carries a computational cost designed to prevent spam whilst reflecting the resources required for higher security levels:
base_cost = 1000 gas
level_cost = (to_level minus from_level) x 500
complexity = 3 (post-quantum), 2 (hybrid), 1 (classical)
total = base_cost + (level_cost x complexity)
Practical examples:
⬩ Level 1 to 5: 3,000 gas
⬩ Level 5 to 8: 4,000 gas
⬩ Level 5 to 15: 16,000 gas
Downward migrations cost nothing. The formula ensures that stronger protection has a proportional but never prohibitive cost.

English

Compliance audits don't make stablecoins future-proof. They make yesterday's balance sheet legible.
Tether processing USDT at scale is one thing. What happens to that attestation when the cryptographic assumptions underneath the ledger start to erode? KPMG can verify reserves. It can't verify whether your signing infrastructure survives the next decade of quantum hardware progress.
QuanChain's LQCp/h Oracle monitors global quantum computing capability across 7 threat levels in real-time, triggering automatic migration to stronger key hierarchies before an upgrade becomes urgent.
Regulatory credibility and cryptographic durability are two separate problems. The industry is solving one and ignoring the other: at what point does "audited" stop being a meaningful guarantee?

English

When a Nobel laureate joins the White House science panel, the threat timeline just got a policy address.
John Martinis built the superconducting qubit systems that put fault-tolerant quantum computing on the roadmap. Now he's advising on U.S. science and technology policy. That's not an academic appointment: that's quantum capability getting a seat at the table where defence and infrastructure decisions are made.
Most blockchain infrastructure treats cryptographic security as a fixed configuration. It isn't. When the threat level moves, the protocol needs to move with it.
QuanChain's LQCp/h Oracle monitors quantum computing capability across 7 threat levels in real time. When conditions shift, DTQPE triggers automatic migration to stronger key hierarchies: no emergency hard fork, no chain-wide coordination panic.
The question worth asking: at what point does a government-advised acceleration in quantum research become the event that separates adaptive protocols from static ones?
English

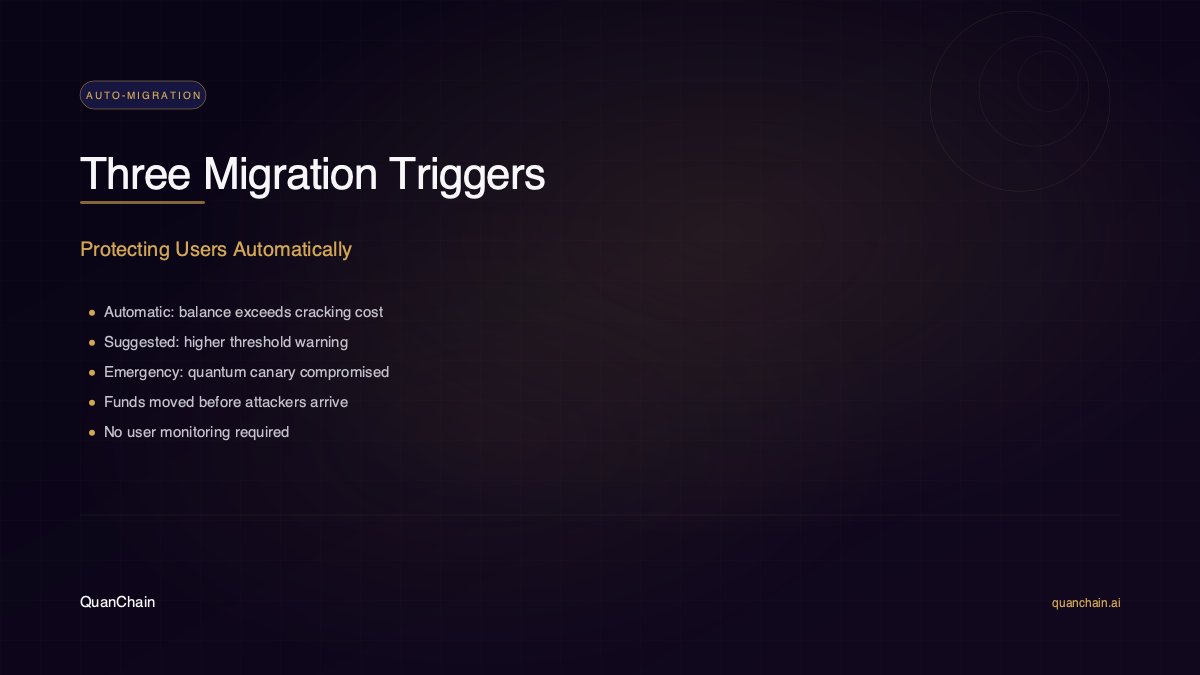
𝗔𝘂𝘁𝗼𝗺𝗮𝘁𝗶𝗰 𝗠𝗶𝗴𝗿𝗮𝘁𝗶𝗼𝗻 𝗧𝗿𝗶𝗴𝗴𝗲𝗿𝘀
DTQPE defines three migration trigger types:
⬩ Automatic: triggered when wallet balance exceeds cracking cost multiplied by 1.5. The protocol moves funds to a higher security level without user intervention
⬩ Suggested: triggered at 3.0x cracking cost. The wallet recommends migration but does not enforce it
⬩ Emergency: triggered when a quantum canary is compromised, indicating an active quantum threat. All wallets below the mandated level must migrate within the epoch
The system protects users who are not actively monitoring quantum threat developments. If the economics of an attack shift, your funds move before the attacker arrives.
English

Faster error correction doesn't make your cryptography safer. It makes quantum processors more reliable: which is exactly the condition that puts classical signatures at risk.
QpiAI's new decoder platform reduces real-time error correction latency on superconducting systems. That's a meaningful engineering step. Every improvement in QEC brings fault-tolerant quantum computation closer to practical reality.
QuanChain's LQCp/h Oracle monitors global quantum capability across 7 threat levels (QTL-0 through QTL-6) and triggers automatic migration when conditions change. No manual upgrade cycle. Funds move to stronger key hierarchies before the threat materialises, not after.
The question isn't whether your chain can respond to a quantum breakthrough. It's whether it was designed to respond at all.

English

The quantum threat timeline keeps shifting, and most chains are still planning for a fixed point on that timeline.
Dr Liam Quinn's optical Ising machine work at Te Whai Ao shows why that's a problem. Hybrid approaches like this accelerate capability gains in ways that don't announce themselves with a single headline. The gap between "years away" and "happening now" closes unevenly.
QuanChain's LQCp/h Oracle monitors global quantum computing capability across 7 threat levels in real-time, triggering automatic security escalation through DTQPE's 20 cryptographic levels before a threat becomes a crisis.
If quantum capability advances through hybrid classical-quantum systems rather than one clean fault-tolerant leap, which threat level are you actually planning your migration strategy around?

English

Google expanding into neutral atom systems is a signal, not a milestone: the hardware race just got structurally more complex.
Two competing quantum architectures from one company means the threat timeline becomes harder to model. Superconducting qubits and neutral atom systems have different error profiles, different scaling curves, different paths to cryptographically relevant capability.
This is exactly the problem QuanChain's LQCp/h Oracle was designed for: it monitors quantum capability across 7 threat levels in real-time, so DTQPE's 20 security levels escalate automatically without waiting for the industry to reach consensus on which hardware "won."
Is a two-architecture world more dangerous for cryptographic planning, or does hardware fragmentation actually slow the threat timeline?
English