پن کیا گیا ٹویٹ

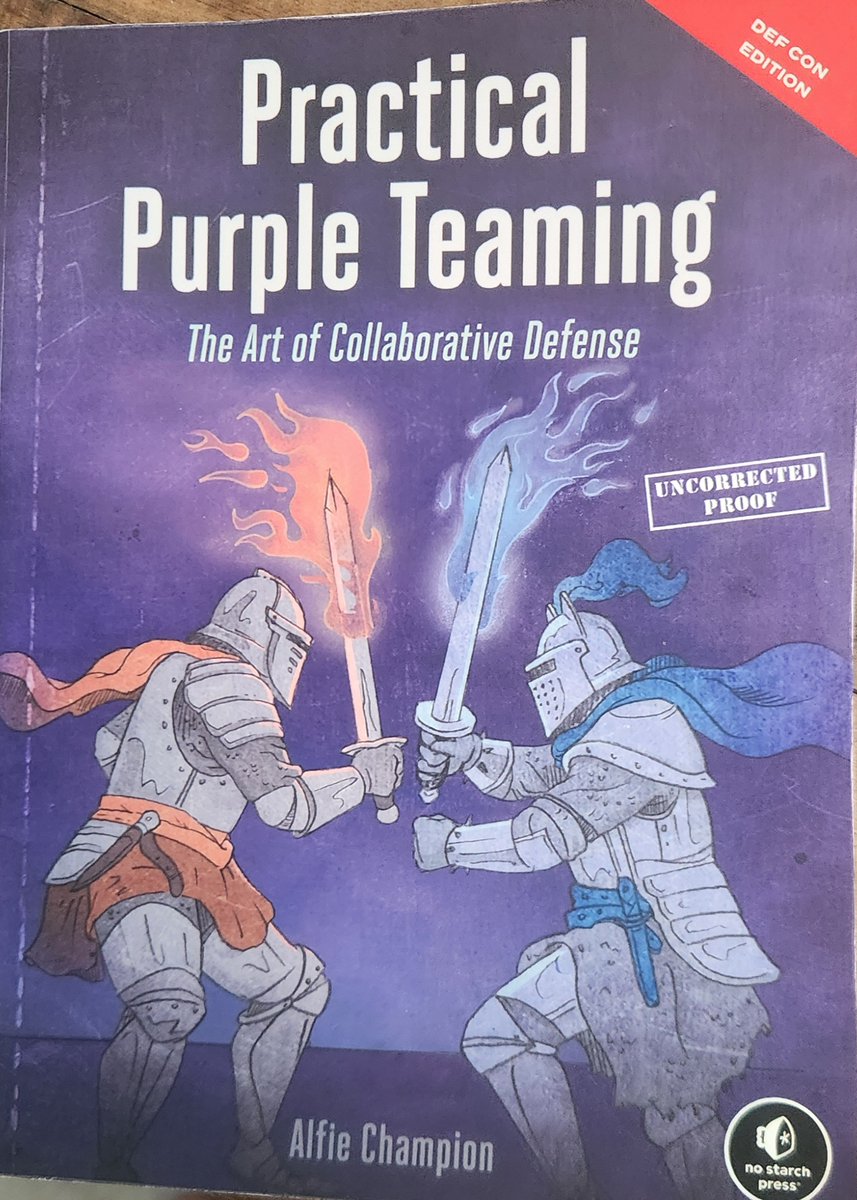
With a process that began two and a half years ago, I'm very excited to announce that I've written a book with @nostarch! 🎉
"Practical Purple Teaming" tells you all you need to know to get started with collaborative offensive testing.
nostarch.com/purple-teaming
English