پن کیا گیا ٹویٹ

The Big Archive for System Design - 2023 Edition (PDF) is available now. And it's completely FREE.
The PDF contains 𝐚𝐥𝐥 𝐦𝐲 𝐭𝐞𝐜𝐡𝐧𝐢𝐜𝐚𝐥 𝐩𝐨𝐬𝐭𝐬 published in 2023.
What’s included in the PDF?
🔹 Netflix's Tech Stack
🔹 Top 5 common ways to improve API performance
🔹 Linux boot Process Explained
🔹 CAP, BASE, SOLID, KISS, What do these acronyms mean?
🔹 Explaining JSON Web Token (JWT) to a 10 year old Kid
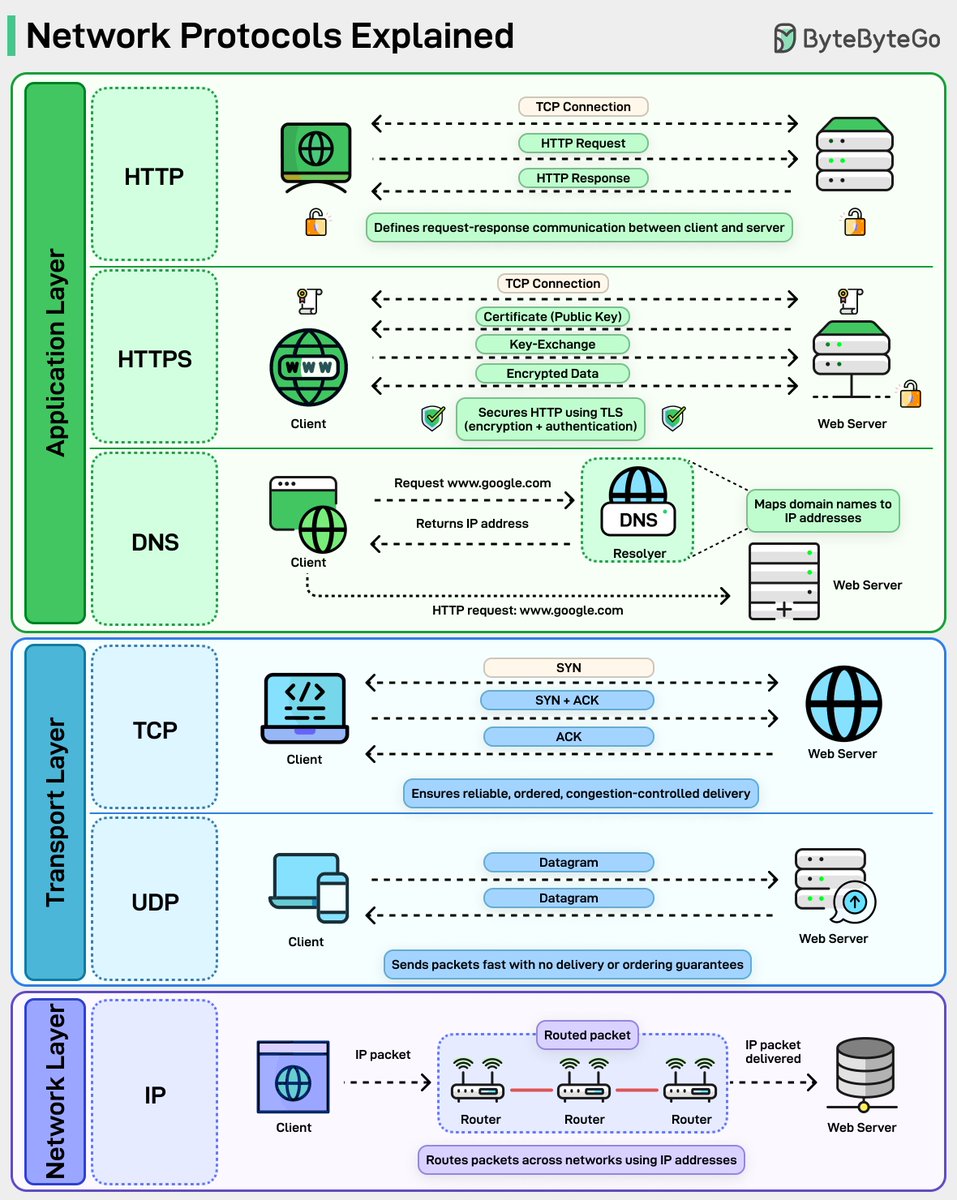
🔹 Explaining 8 Popular Network Protocols in 1 Diagram
🔹 Top 5 Software Architectural Patterns
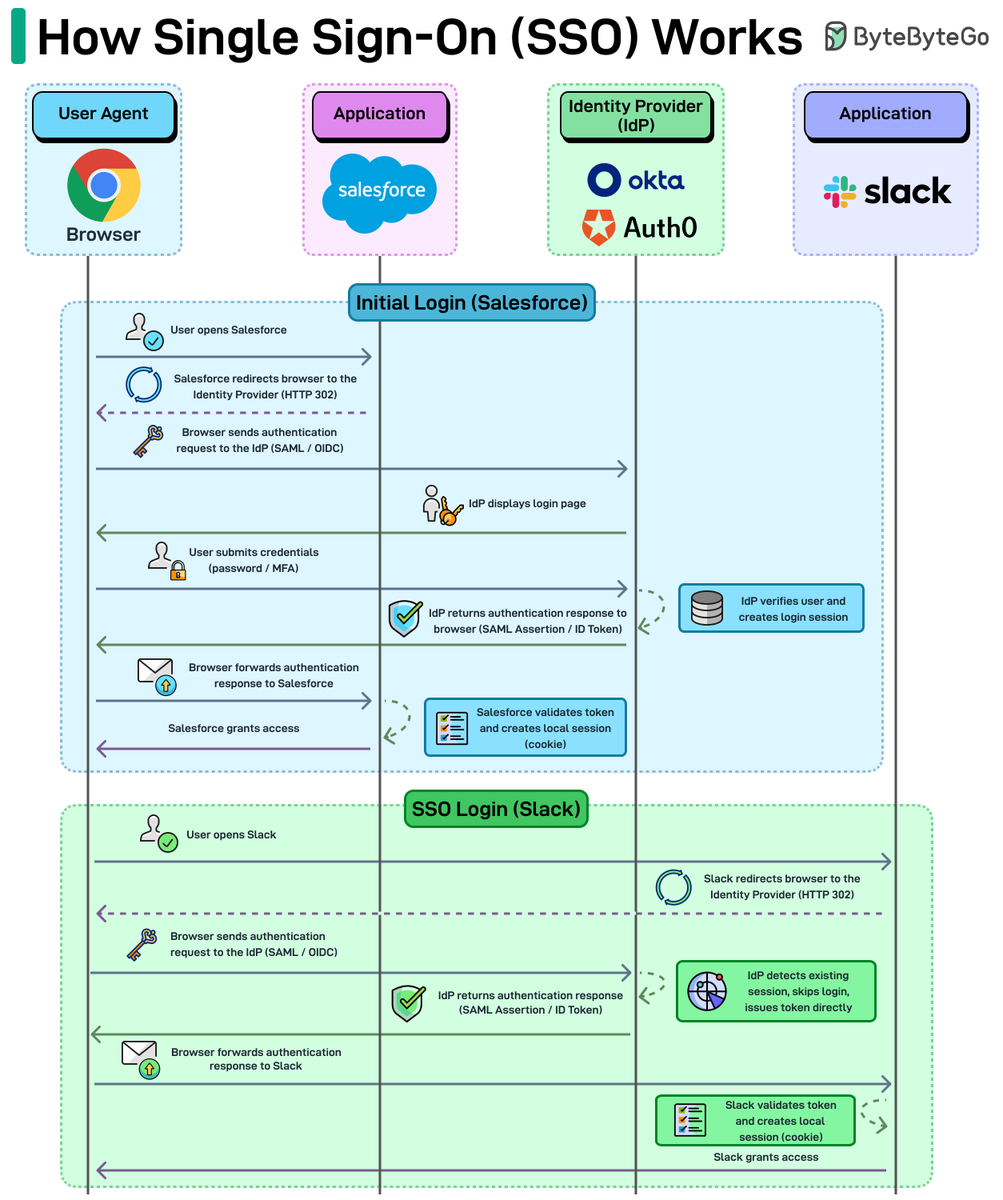
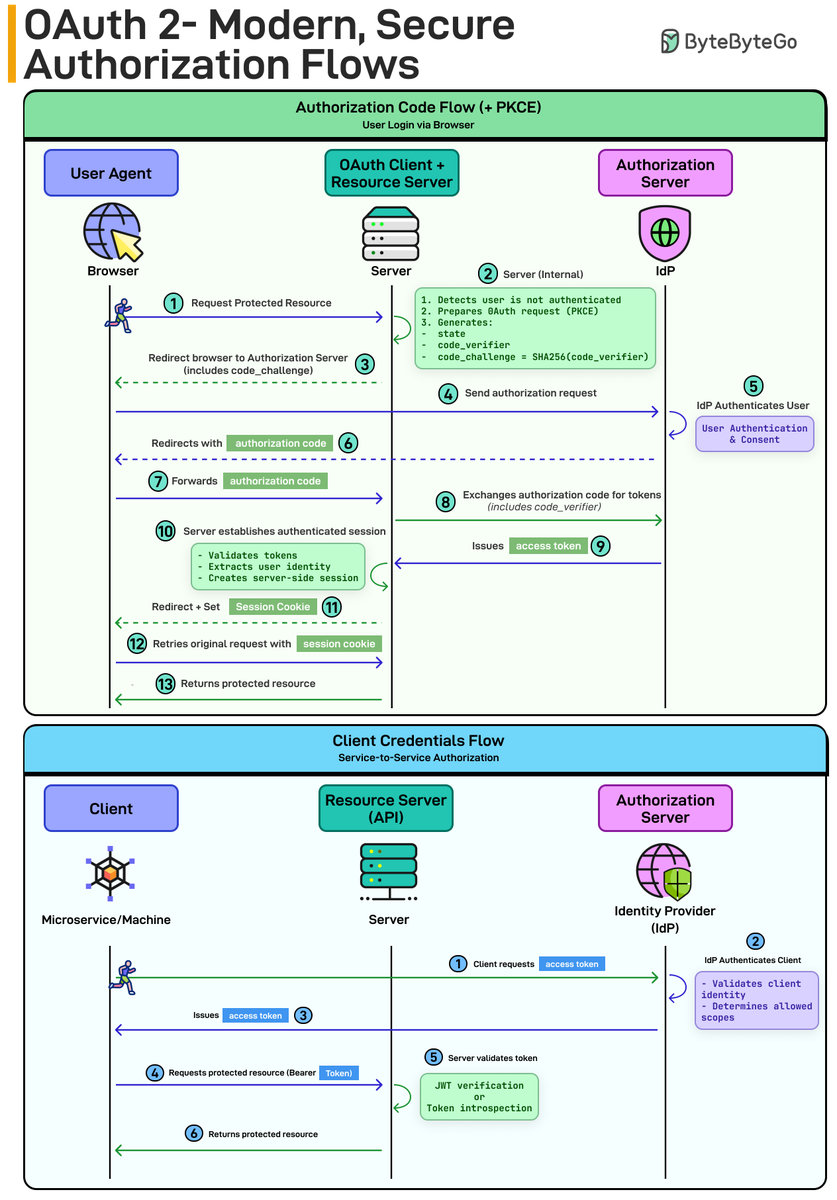
🔹 OAuth 2.0 Flows
🔹 What does API gateway do?
🔹 Linux file system explained
🔹 18 Key Design Patterns Every Developer Should Know
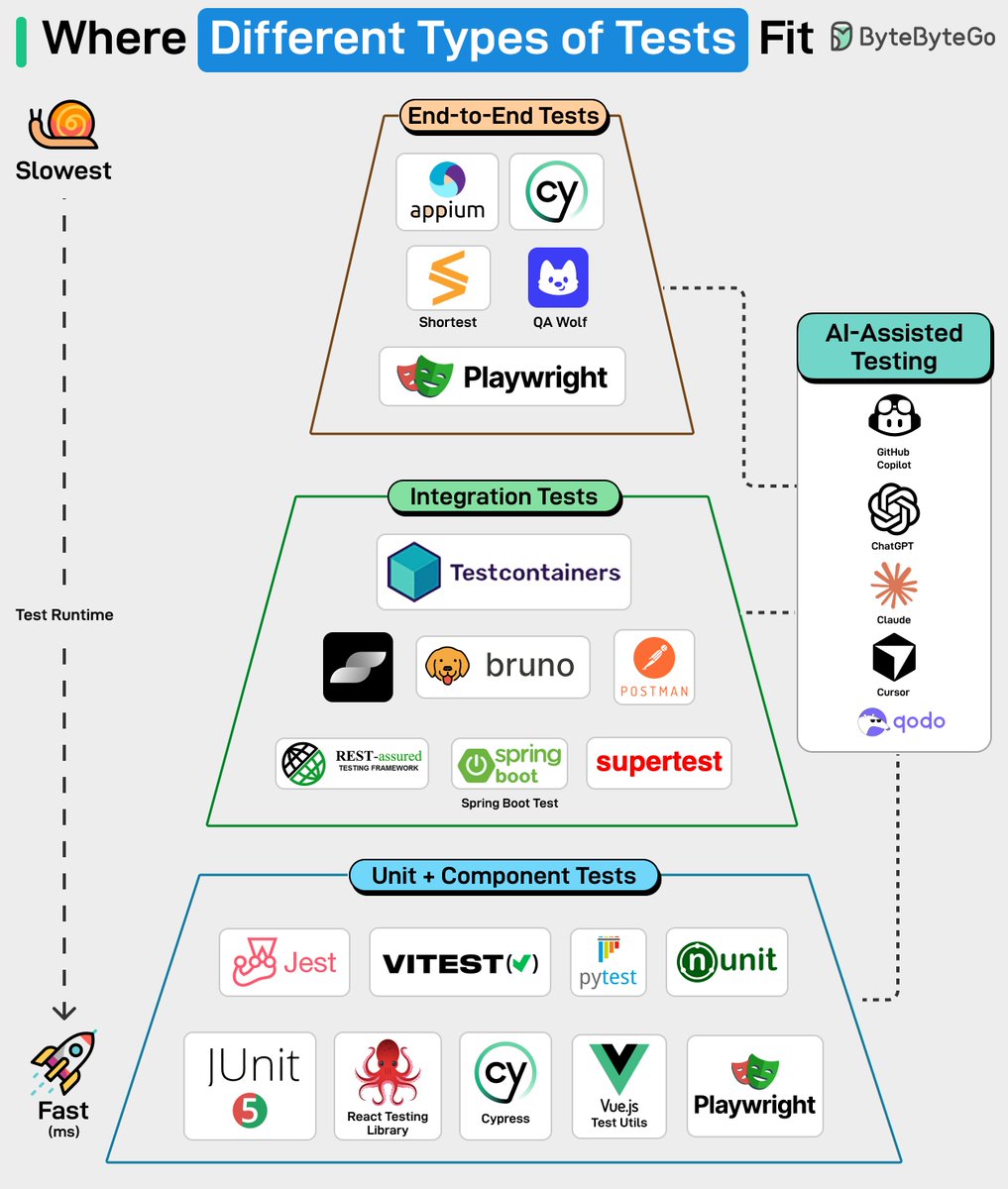
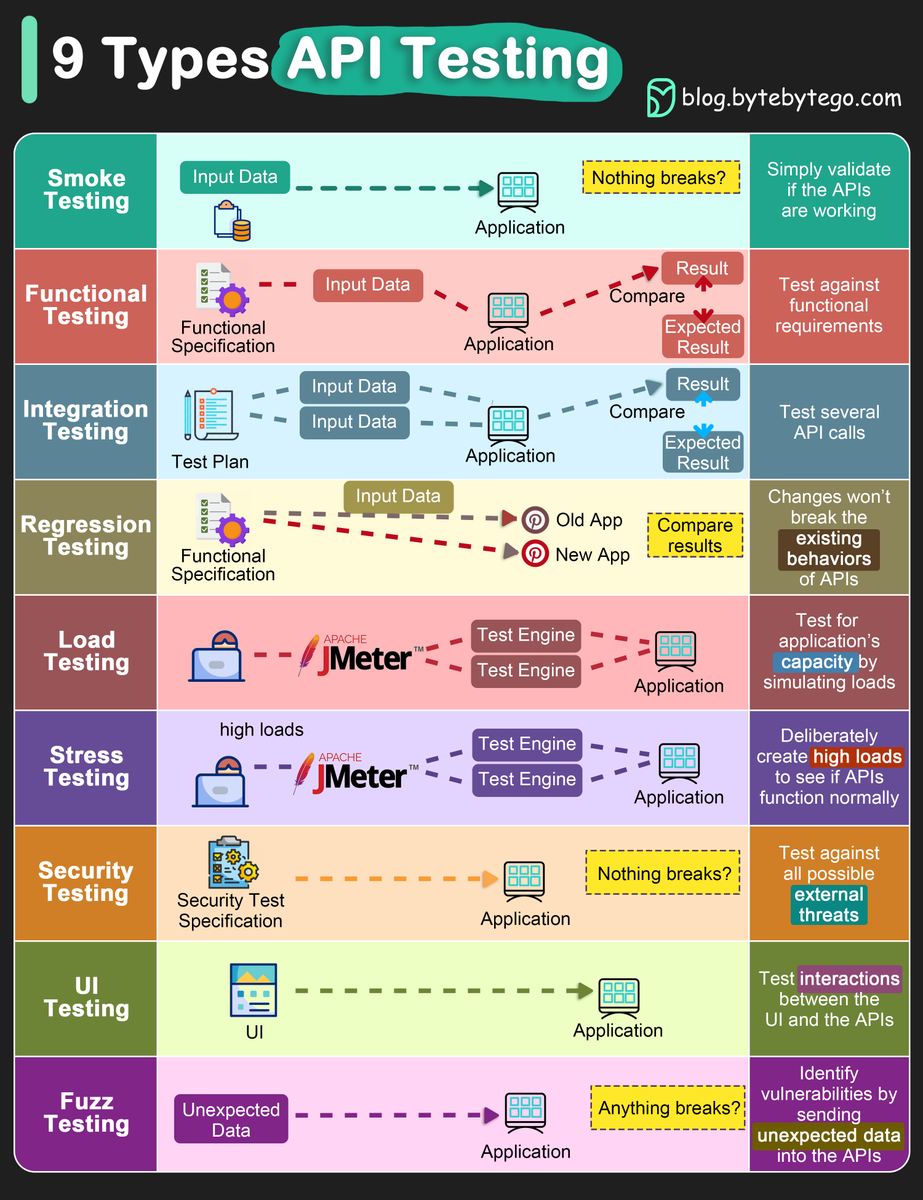
🔹 Best ways to test system functionality
🔹 Top 6 Load Balancing Algorithms
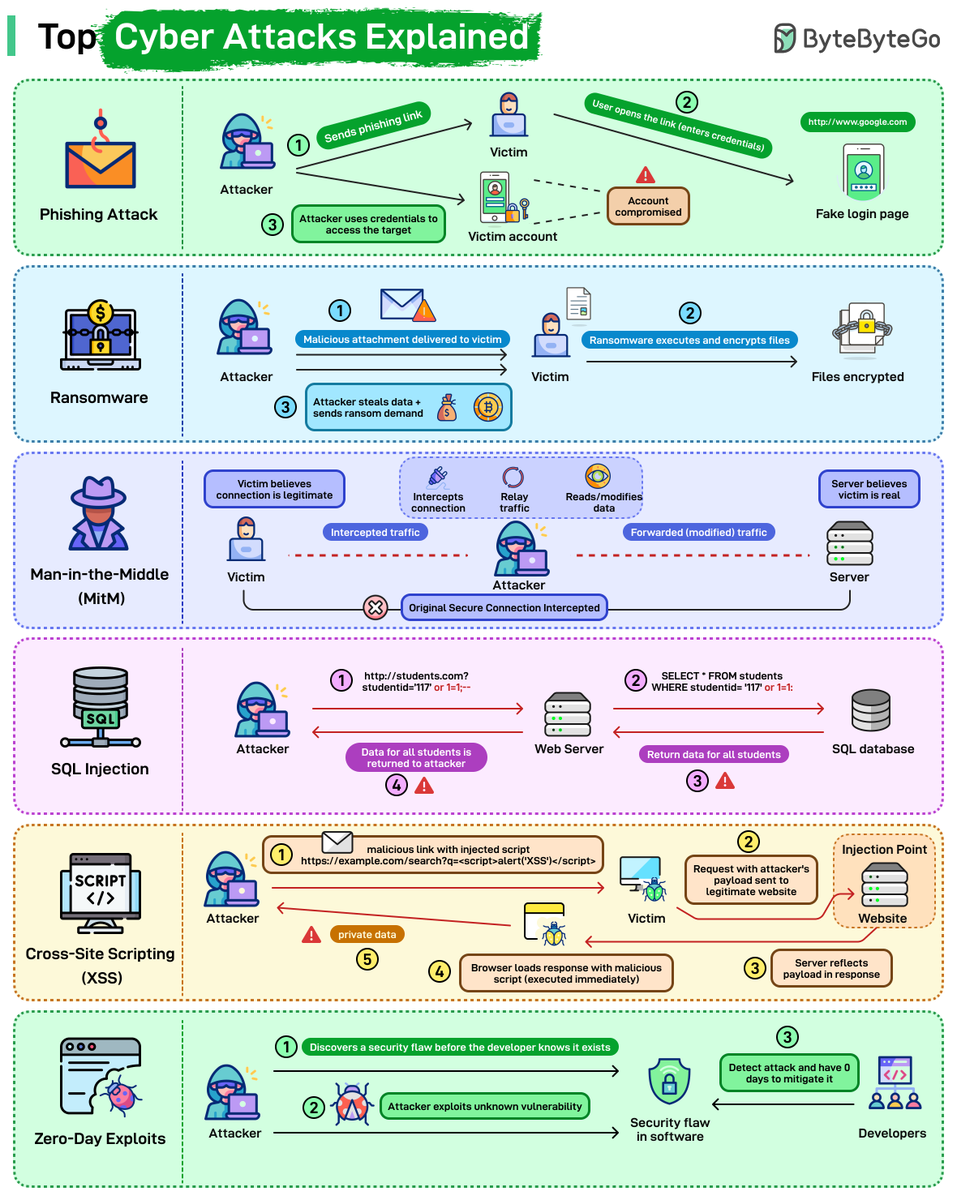
🔹 Top 12 Tips for API Security
🔹 𝐀𝐧𝐝 100+ 𝐦𝐨𝐫𝐞
–
Like, follow and subscribe to our newsletter to receive the PDF download link: bit.ly/3KCnWXq

English