Intricate Security
105 posts


Intricate Security
@intsecllc
With expertise in penetration testing, blue team, and Active Security Operations Center (SOC), we focus on providing specialized services in these areas
Alpena, MI شامل ہوئے Mayıs 2023
56 فالونگ5 فالوورز

This is exactly why we emphasize strong application security, continuous monitoring, and disciplined change management. intricatesecurity.com/r/HRm
English

Check your logs for suspicious VPN login activity. intricatesecurity.com/r/aHH
English

The State of Nevada has been hit with a breach that has brought down a lot of offices. intricatesecurity.com/r/Ya4
English

Massive SharePoint zero-day (CVE‑2025‑53770) exploited in the wild, on-prem servers hit hard. Different orgs hit. Data stolen, keys hijacked, records wiped. Patch now. Respond fast.
intricatesecurity.com/r/sL2
English

Subdomain hijacking is back on the menu
Read the full article: intricatesecurity.com/r/oC8
English
Intricate Security ری ٹویٹ کیا

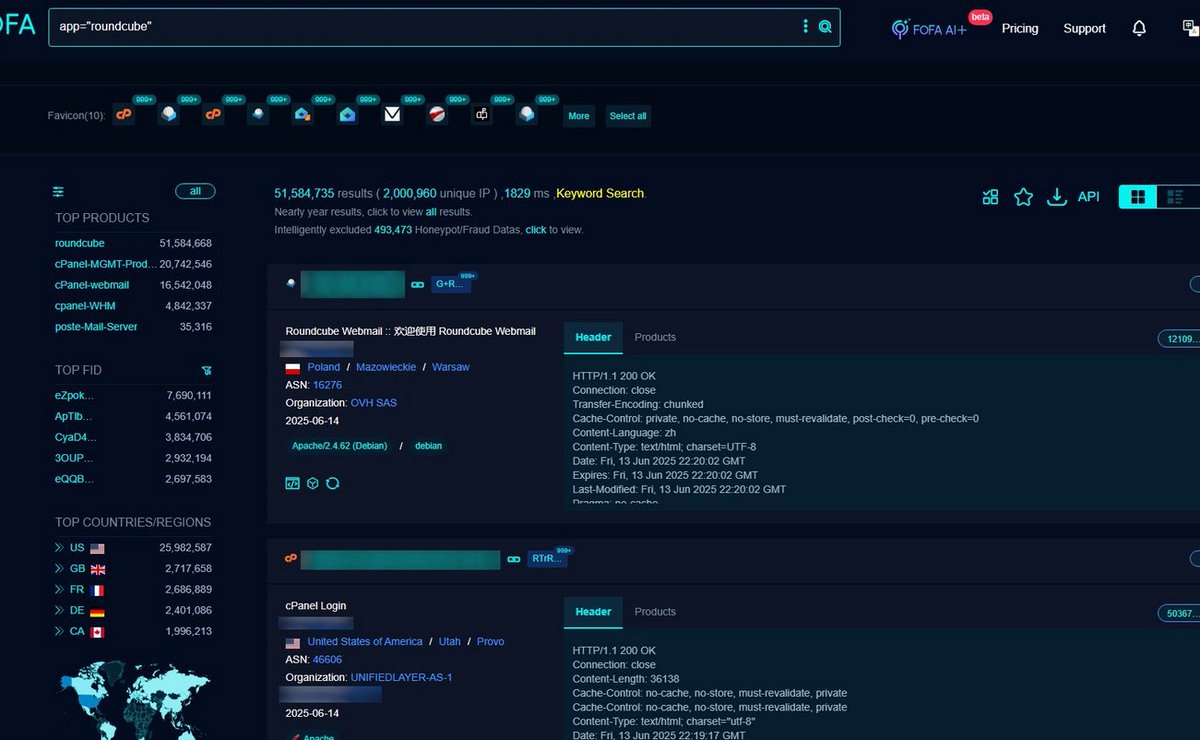
🤬CVE-2025-49113: Post‑Auth Remote Code Execution in Roundcube via PHP Object Deserialization
FOFA Link: en.fofa.info/result?qbase64…
FOFA Query: app="roundcube"
Results: 51,584,735
Advisory:nvd.nist.gov/vuln/detail/CV… CVSS: 9.9
English

Disable PSTN dial‑in for any CUI‑related meetings and enforce Teams client‑only voice. These steps directly support both encryption (SC.L2‑3.13.11) and VoIP governance (SC.L2‑3.13.14). #Cybersecurity #CMMC #Teams #CUI

English

Hackers exploit HTTP/2 to inject harmful code by faking trusted sites. Disable server push/SXG if unused, validate origins, update libraries, avoid shared certs, and use strong CSP to stay safe. intricate-security-llc.odoo.com/r/8UJ
English

