Mɪᴄʜᴀᴇʟ Tᴏᴇᴄᴋᴇʀ
21.9K posts


Mɪᴄʜᴀᴇʟ Tᴏᴇᴄᴋᴇʀ
@mtoecker
Electric Power Geek, Hardhat Hacker, Control System Security Engineer, & .... Opinions are my own. (ಠ_ಠ) c[_] KC3GST





You can send a single smartphone to any point in human history. No instructions. Winner is whoever advances human progress the most. When + where do you send it?




Lindsey Kurowski helps a property owner rediscover his passion for his struggling motel in the charming city of Tombstone, Arizona. Watch a new episode of #MotelRescue tonight at 8/7c on #MagnoliaNetwork on TV, @streamonmax, and @discoveryplus.

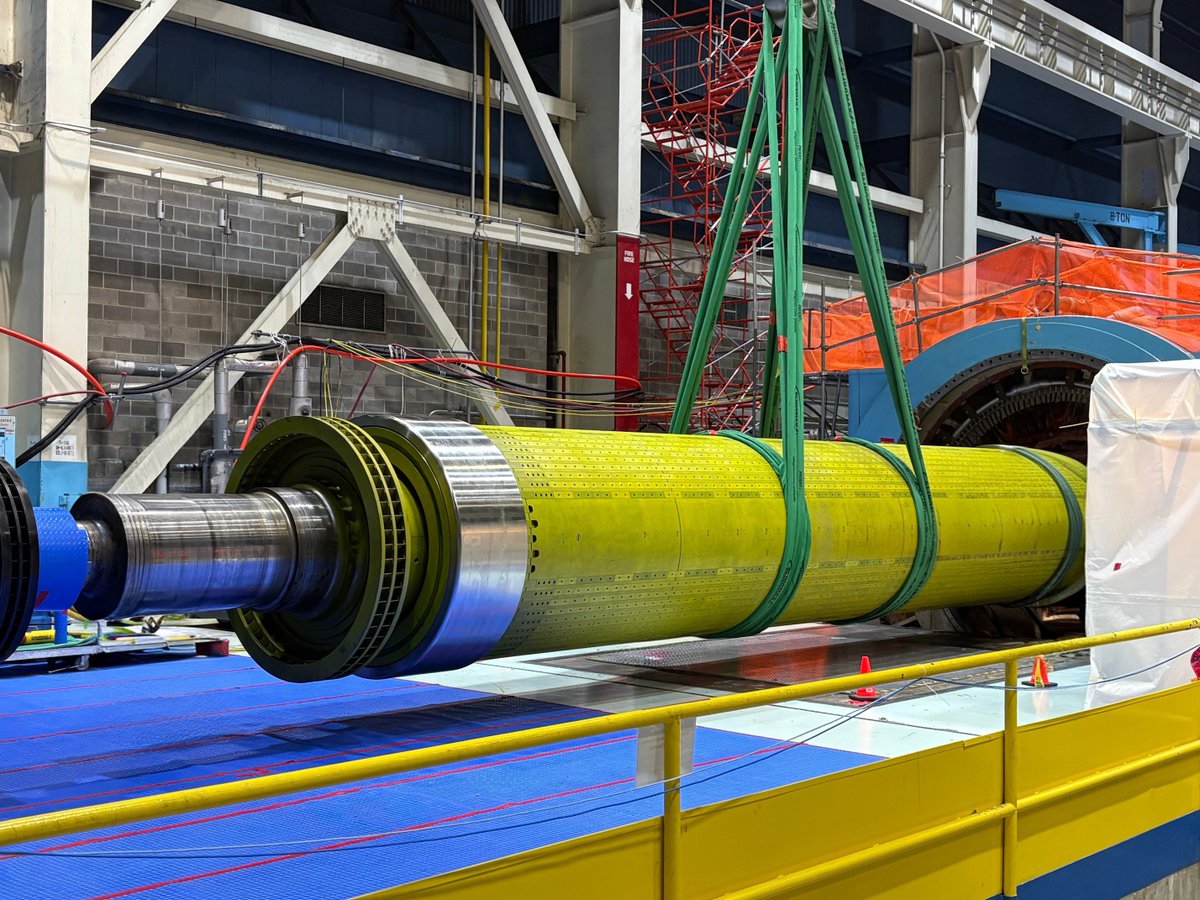
first pole-mounted energy storage system in the US interesting...


i will make a pcb for this lol



The Cloudflare CEO @eastdakota sees 3 possible outcomes from where we are right now: 1. The open web dies. It's all recycled content. 2. AI companies end up employing the content creators. 3. Content creators successfully protect their content and AI companies become resellers.