

John
168.8K posts

@JDreport
Living in The Truman Show inside other dimensions, realities and timelines






J 666 🇳🇱 #oldworld Amsterdam

For over a century, an island called Frisland — also known as Frischlant, Friesland, or Fixland — appeared on nearly every map of the North Atlantic between the 16th and 17th centuries. It wasn’t just a random mistake: multiple cartographers drew the same landmass,


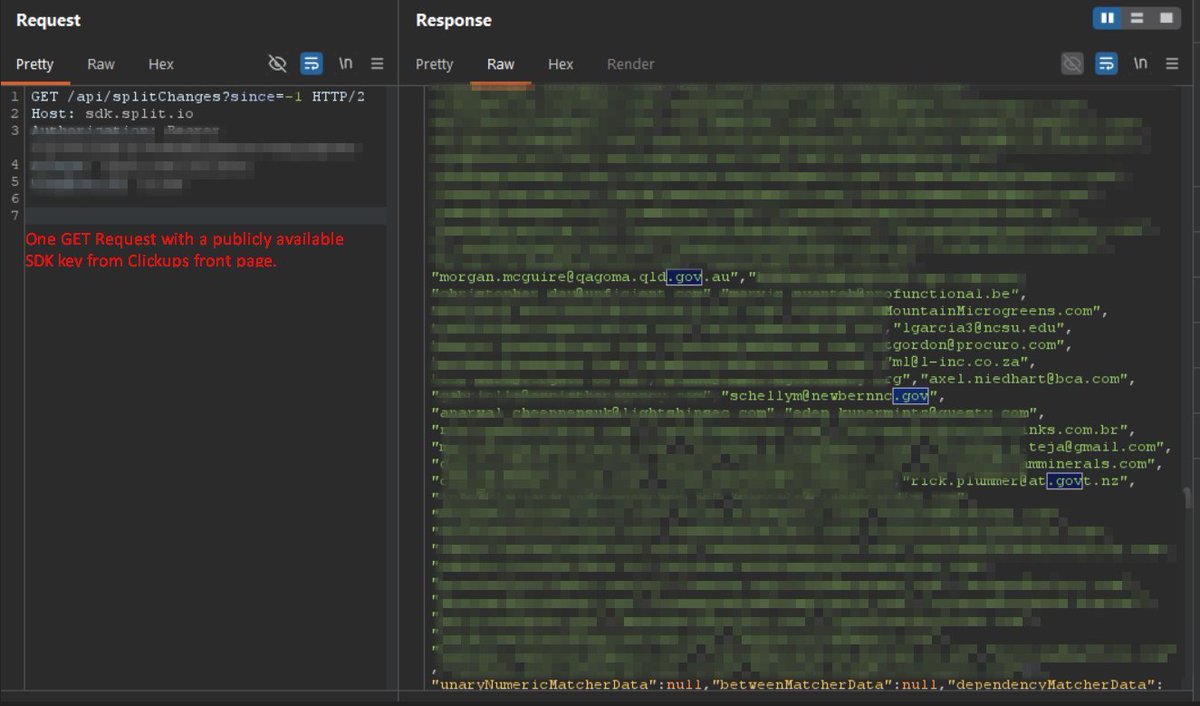
i went to clickup.com. opened the page source. found a hardcoded API key in the javascript. copied it. sent one GET request. got back 959 email addresses and 3,165 internal feature flags. employees from Home Depot. Fortinet. Autodesk. Tenable. Rakuten. Mayo Clinic. Permira. Akin Gump. government workers from Wyoming, Arkansas, North Carolina, Montana, Queensland Australia, and New Zealand. a Microsoft contractor. 71 clickup employees. fortinet sells enterprise firewalls. tenable makes Nessus, the vulnerability scanner half the industry runs. their employees emails are exposed because clickup hardcoded a third party API key in a javascript file that loads before you even log in. this was first reported to clickup through hackerone on January 17, 2025. its now April 2026. the key has not been rotated. i just pulled the response five minutes ago. every email is still there. clickup raised $535 million at a $4 billion valuation. claims 85% of the Fortune 500 use their platform. looks like the proof is in the page source.



Having been called a liar by Anthony Fauci for saying that "not one of the 72 vaccines mandated for children has ever been safety tested", RFK Jr. sued Fauci. After a year of stonewalling, Fauci's lawyers admitted that RFK Jr. had been right all along. "There's no downstream liability, there's no front-end safety testing... and there's no marketing and advertising costs, because the federal government is ordering 78 million school kids to take that vaccine every year." "What better product could you have? And so there was a gold rush to add all these new vaccines to the schedule... because if you get onto that schedule, it's a billion dollars a year for your company." "So we got all of these new vaccines, 72 shots, 16 vaccines... And that year, 1989, we saw an explosion in chronic disease in American children... ADHD, sleep disorders, language delays, ASD, autism, Tourette's syndrome, ticks, narcolepsy." "Autism went from one in 10,000 in my generation... to one in every 34 kids today."

🇺🇦🇷🇺🇩🇪 Ukraine's Nord Stream diving team included Freya, a former erotic model. In her twenties she'd posed for erotic magazines, including a cover shot in a captain's coat with the headline "Why does the Crimean sun awaken sexy feelings?" She was also reportedly the best diver in the group. Her cover story if they got stopped by police: they were filming an underwater porn shoot. You just can’t make that up 😂 Source: Bild