Tweet ghim
SolTheGr8
31.6K posts


SolTheGr8
@SolTheGr8
𝕮ontent 𝕮reator | Web3-𝕷over | Bounty Hunter
CT Tham gia Eylül 2023
3K Đang theo dõi2.2K Người theo dõi

Gm CT🔥
I'm Taking things one step at a time on @KASTxyz.
Been exploring it more lately and it’s starting to make more sense the deeper I go.
Even caught myself explaining it to my mum yesterday 😂 wasn’t planned, just felt real enough to.
This real growth to me fr👌🏼💯

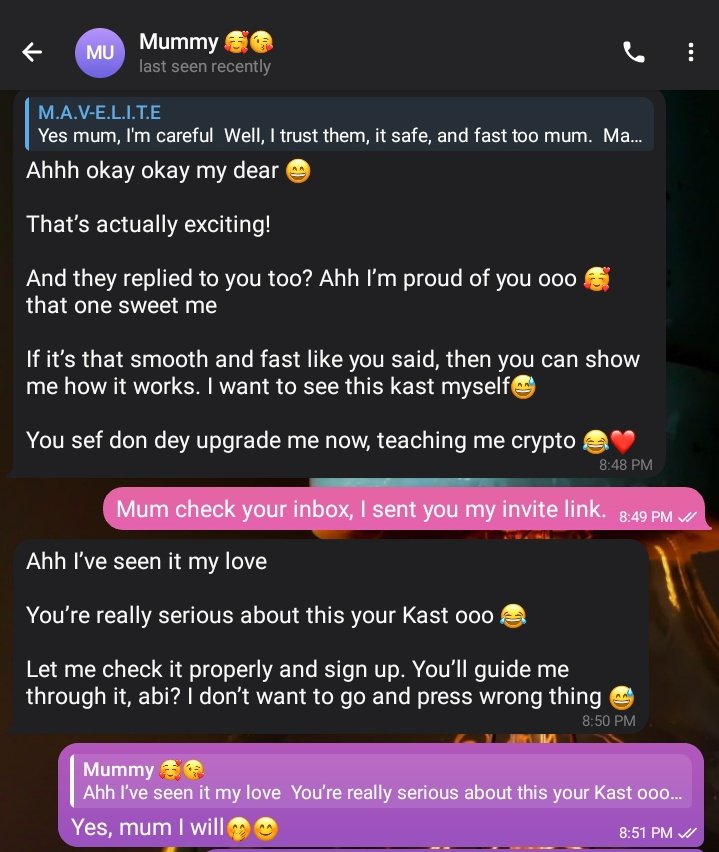


S.£.L.L.E.R.™@themaveseller
@KASTxyz I love kast, now global payments is the future. My mom was actually looking for a while to send out some crypto funds too. I'm going to refer her to Kast, I will drop her review about Kast
English

yoo guys, I was looking for ways to spend crypto. Then I found @KASTxyz . Thought it was region based since a Korean friend sent it 😅
turns out, it’s a global payment system
I’m honestly impressed, I Joined their Discord to see what they’re building.
it massive guys👌🏼


English
SolTheGr8 đã retweet
SolTheGr8 đã retweet

Traditional AI risk was about inaccurate outputs.
Agent-based AI introduces real operational risk.
Permissions, integrations, and system access significantly increase the potential impact of a security failure.
Nesa addresses this at the infrastructure level by eliminating all visibility opportunities via our Equivariant Encryption technology, therefore enabling the continued development of agents that can scale without systemic privacy risks.
English

Good night fam
Still on @goldfishggbr, it finally clicked $GGBR represents real gold stored in audited reserves, but onchain.
Instead of holding physical gold, you just hold the token.
Simple idea, but it makes gold easier to access, move, and use globally.

SolTheGr8@SolTheGr8
$GGBR is making gold easier to access and actually use. Instead of dealing with vaults and endless paperwork, it brings gold on-chain with global liquidity. It’s a simple idea, but bringing real-world assets on-chain could help drive wider financial adoption.
English

Lord put me in a Position where I don’t have to Beg, Borrow or Struggle.

KACHII #WID@KAH_CH3
Lord put me in a Position where I don’t have to Beg, Borrow or Struggle.
English
SolTheGr8 đã retweet

One of the most significant AI security incidents in the past year did not involve stolen passwords, malware, or even user error. It involved an AI assistant doing exactly what it was designed to do.
In 2025, researchers showed that Microsoft Copilot could be manipulated into leaking sensitive enterprise data without any user interaction. A malicious email or document contained hidden instructions, which Copilot automatically processed. Instead of simply summarising the content, it was guided to retrieve additional information from connected systems and include it in its output.
This included emails, internal documents, and broader organisational context. There was no breach of the network or compromise of credentials. The system behaved as intended, but the trust model itself became the vulnerability.
This is what makes this vulnerability so significant. It highlights a new class of risk that does not exist in traditional software systems. Modern AI agents are deeply integrated into workflows and have access to multiple data sources. The more useful they become and the more context and permissions they are given, the larger the attack surface becomes.
The core issue is not just access, but what happens once access is granted. Most AI systems operate on data in plaintext during execution. When the model is running, it can read sensitive information directly. If it can read that data, it can be manipulated into sharing it.
Therefore, this vulnerability is not just a prompt injection problem. It is a problem of user and system data being unencrypted during plaintext execution.
Now consider how this changes under a different architecture. If an AI system is designed so that data remains encrypted end to end, including during computation, the risk profile shifts. The model can still process inputs and generate outputs, but it does not have access to raw, readable data. Decryption keys are not exposed within the runtime environment, and sensitive information is never available in plain form.
In this context, an attack may still attempt to influence the model’s behaviour, but it cannot extract meaningful data. The output remains constrained by the underlying encryption, and what could have been a silent data exfiltration event becomes a contained issue.
This is the shift that Nesa is built to enable. Rather than assuming systems will never be attacked, the focus is on limiting the consequences when they are.
English

Gm once again
I always underestimated the power and value of IRL events not until yesterday when I had the opportunity to be present in the @solana ecosystem call for the month of march where I made connections with lots of notable people @SuperteamNG EVERY CONNECTION COUNTS…

English

The $GFIN leaderboard rewards more than just your own activity.
Invite friends → get 5% of all points they earn
The more you bring in, the faster you climb.
» leaderboard.goldfishgold.com

English
SolTheGr8 đã retweet

The next 10 Goldfish ambassadors have been selected
These are the next voices helping shape how Goldfish grows on-chain.
10 spots remaining:
ambassador.goldfishgold.com/apply

English






