

Hash
2.1K posts







Mr. Titus Tech is correct. cpuid-dot-com is indeed delivering malware right now. As I began poking this with I stick I discovered this is not your typical run-of-the-mill malware. This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs file masquerading, is multi-staged, operates (almost) entirely in-memory, and uses some interesting methods to evade EDRs and/or AVs such as proxying NTDLL functionality from a .NET assembly. The C2 domain present in one of the binaries is a clear IoC. This is the same Threat Group who was masquerading FileZilla in early March, 2026. They've been busy.

WhatsApp’s “encryption” may be the biggest consumer fraud in history — deceiving billions of users. Despite its claims, it reads users’ messages and shares them with third parties. Telegram has never done this — and never will 🤝





How Axios was compromised 🤯

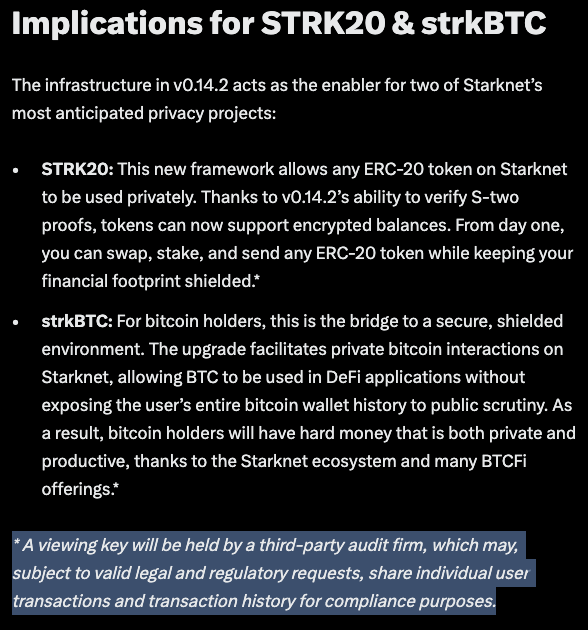
This is my last public swap. Here's my wallet: as.near Open it. Everything I've ever done is right there. Every token I hold, every swap, every address I've ever sent to. My entire financial history, sitting in the open for anyone to read.

Google bumps up Q Day estimate to 2029, far sooner than previously thought arstechnica.com/security/2026/…