Privacy Trash Panda
801 posts


Privacy Trash Panda
@TrashcanPrivacy
Digging through trash to protect your treasure


"Age-verification for social media puts kids at risk" "Online age verification.... puts minors – a population 35 to 51 times more likely than adults to fall victim to identity theft – at risk." spectator.com/article/age-ve…



Between this kind of thing and my recent experience renting a Ford Escape, I fear for Detroit.


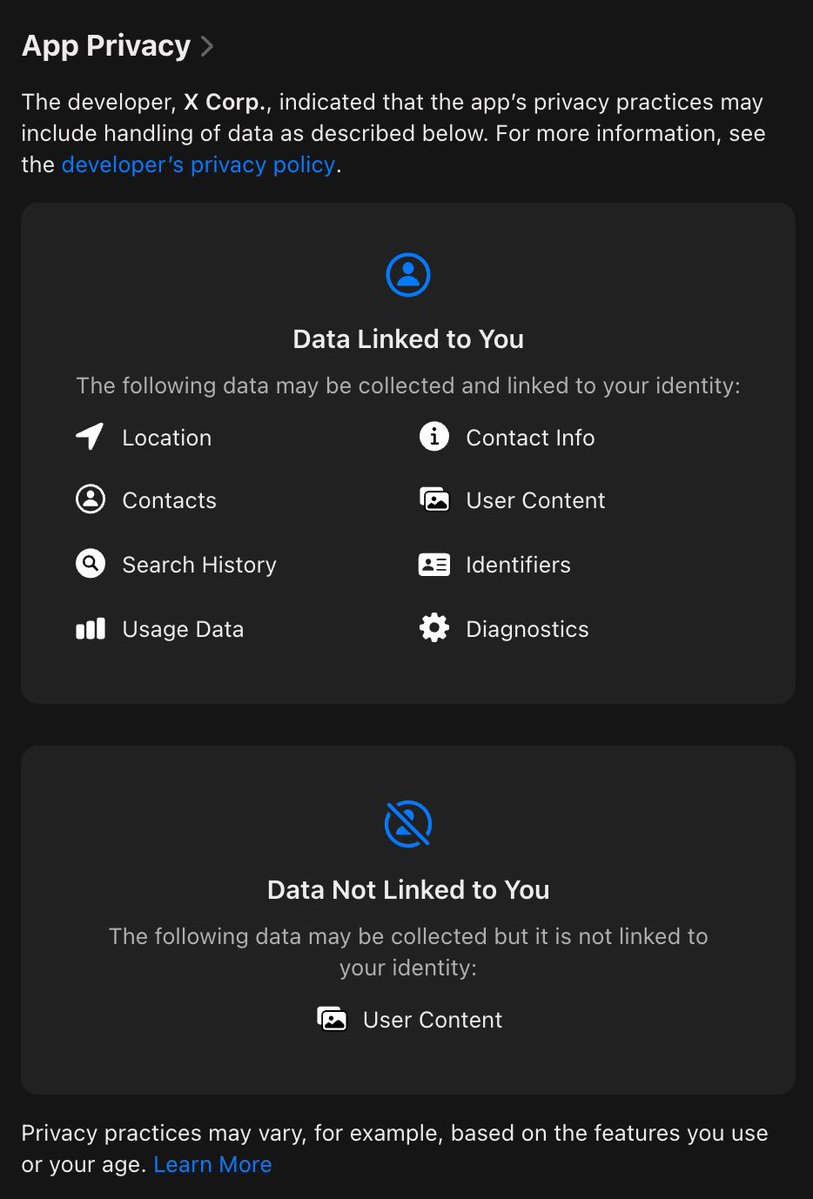
If you want unrestricted access to your own iPhone in the UK, you have to hand over your ID or go through other age checks. Even if you do that, you STILL have to go through further "online safety" age checks to see some Reddit posts or X threads. This is madness.



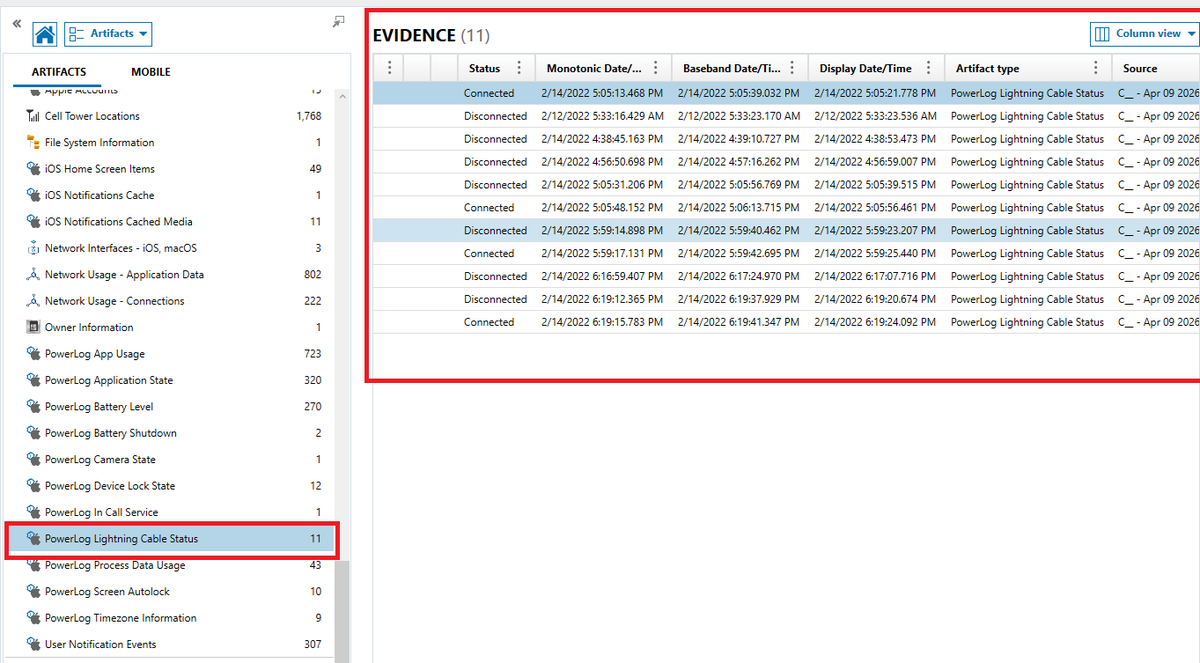
CELL TOWER TRIANGULATIONS Cell tower artifacts provide a passive yet powerful layer of location intelligence. As a mobile device moves, it continuously connects to nearby cell towers; each interaction is logged with associated latitude, longitude, and timestamp data. This means every movement, whether intentional or not, can leave a trail of tower associations. Forensic analysis of these records enables investigators to approximate a device’s path, identify location patterns, and correlate presence within specific geographic areas over time. FUN FACT: A mobile device does not need active user interaction to generate location evidence; simply being powered on causes it to continuously register with nearby cell towers, automatically logging movement over time. Cell tower data is critical for investigators because it provides an independent, system-generated record of a device’s movement, allowing them to place a suspect within a geographic area at a specific time, even when GPS, apps, or user-controlled data have been deleted or manipulated.


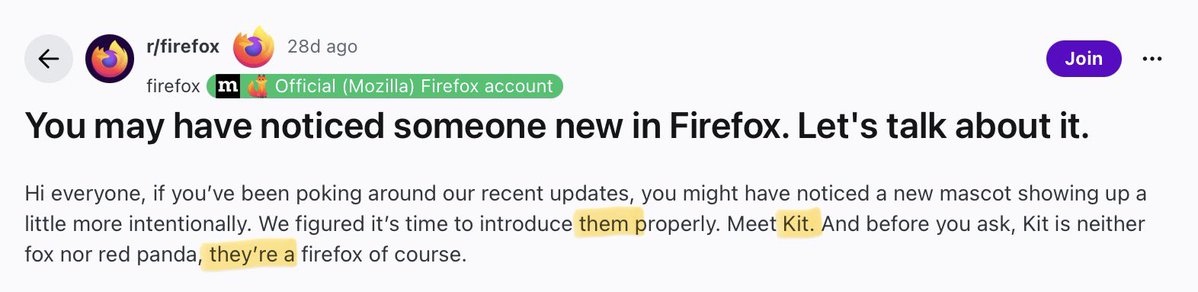
Meet “Kit”. The Firefox Web browser’s new, non-binary mascot. Yes. You read that right. Non-binary. With “They/Them” pronouns. Because, of course @Mozilla had to inject “pronouns”, and “gender identity” politics into a web browser.