
@oriSomething @eytanlevit אפשר המלצות לחשבונות איכותיים לעקוב אחריהם?
עברית
Asi Greenholts
45 posts

@TupleType
Concentrated AppSec juice • Security Researcher @PaloAltoNtwks




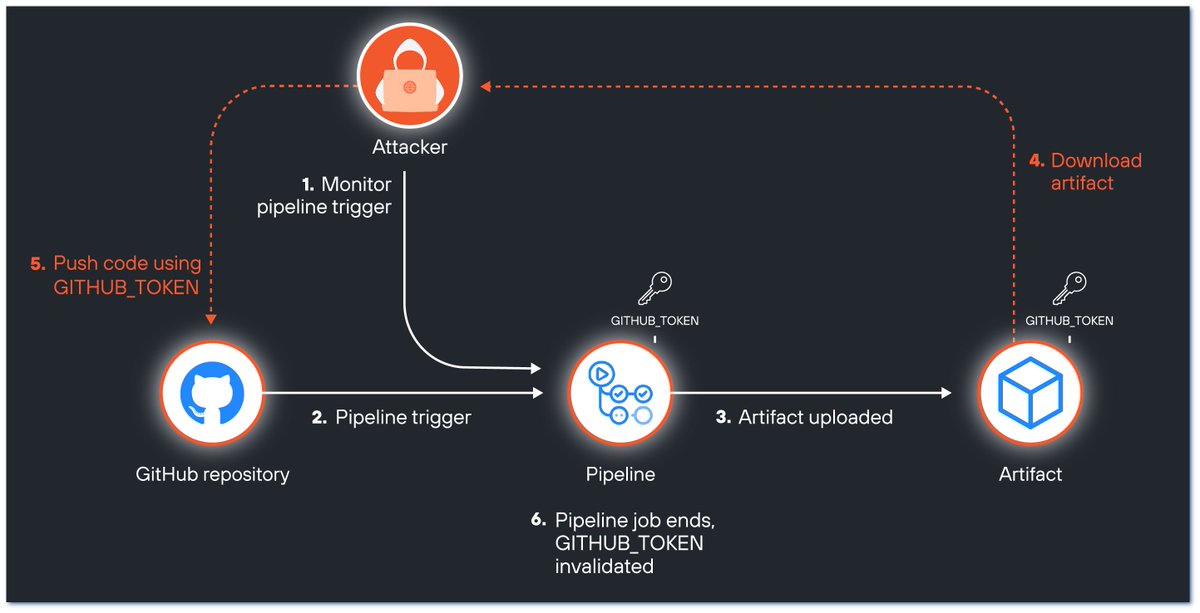















How a worm 🪱 can be used to compromise @github repositories at scale through the Actions dependency tree🌲? The blog details a public disclosure out of many reported to #bugbounty programs This was first reveled at @defcon 31 and @BSidesLV paloaltonetworks.com/blog/prisma-cl…




Keep malicious actors out of your pipeline! Follow the NSA and CISA recommended guidance to defend against CI/CD pipeline compromise. nsa.gov/Press-Room/Pre…