ch
511 posts

ch
@chybeta
open to bug bounty collaboration @HackenProof Security Researcher Just dm https://t.co/VVU1OV5yz6
Tham gia Ağustos 2017
4.7K Đang theo dõi14.3K Người theo dõi
Tweet ghim
ch đã retweet

New on the Anthropic Engineering Blog:
How we use a multi-agent harness to push Claude further in frontend design and long-running autonomous software engineering.
Read more: anthropic.com/engineering/ha…
English
ch đã retweet

I hacked Claude Code! It turns out "agentic" is just a fancy new way to get a shell. I achieved full RCE and hijacked organization API keys. CVE-2025-59536 | CVE-2026-21852
research.checkpoint.com/2026/rce-and-a…
#ai #Claude
English
ch đã retweet
“看看 etherscan都要收费”😂
Cos(余弦)😶🌫️@evilcos
万万没想到我们第一时间出手帮忙 Venus 大户 @KuanSun1990 跟进调查被盗事件,第一时间就给其指明了 Venus 风控必要性,风控后,然后我们协助他把被黑根本原因调查出来,他却在自己的群聊里全面诋毁我们“毫无作用,纯坑,看看 etherscan 都要收费,还有脸要赏金要致谢”。 现在的伦敦时间你 @KuanSun1990 可能还没醒,你醒了,来给个交代,否则我们会让大家知道什么是现实版的农夫与蛇,什么是两面三刀(你看看你和我私聊的嘴脸吧,你是如何诋毁其他帮你的角色的)。就你这样的人,以后谁还敢出手帮你。 本来我已经和你说了这次可以不要赏金,既然你如此踩我们(但这几天推文又都又在公开致谢我们…包括你历史上第一次被盗,你写的真的是声泪俱下,感动了很多人,包括我),这次的赏金我肯定要,你受益于我们,为什么我不能要赏金?我给谁做公益,也不可能给你这种人做公益。
中文

比较遗憾的是 $cards 没人赚到,昨晚发到2个群的时候120m,尴尬的是没什么人理我,就自己看了看报告研究了一下想着睡醒找位置买,没想到横了这么久睡醒就启动没给到上车机会。
说到底还是不相信自己,因为前段时间自己研究了nonos吃了rug亏了很多。不过 $cards 和 $nonos 不一样的是 $cards 是名牌创始人+名牌vc。
继续努力,我会慢慢变强。
0xNoNo🦇@0xNoNo_1
如果不是早上小橘老师 @maru_49940 发的 $cards 的投研,或许卖飞了 $huch 以后,我就算看到him喊单,也不会再买回来了,有人说我发早上的群聊截图装逼,我在评论him和群里研讨追高是同时,大概市值在5m左右,用手机太不方便了,我已经出本了,剩下的放着了。另外,如果真的想要装逼,其实我想说的是, $huch 我们群车300k🤣🤣🤣🤣
中文
ch đã retweet
ch đã retweet

1/4 dbugs LIVE
dbugs.ptsecurity.com — vulnerabilities’ home
See trends, discover more, read AI summaries, have all references at hand, and your profile with all your CVEs and CVSS score on a leaderboard.
⬇️ See thread: what’s live + what’s next ⬇️

English
ch đã retweet

After 9 months+ of cranking, cursing, and cursoring, and drawing on over 20 years experience running #HITB's Call for Papers, I bring you CFP Directory - a single system to make it easier for speakers to submit and organizers to connect and curate talks: cfp.directory
English


Hey hackers! We're running a beta for Hai for Hackers, our AI security agent. If you're interested, please reply with your HackerOne username (we will probably limit to ~100 hackers for now). After it's been enabled, you can start using it by clicking the Hai button in the top right corner of the app. It’s free to use (with a limited daily budget for now). It is like any other AI you’ve interacted with, with the added benefit that it has access to a whole bunch of HackerOne data, like reports and programs. We’re shipping improvements to Hai almost every day. Here are some neat use cases:
- “take all the learnings from STÖK, jhaddix, and nahamsec's recon strategy and build one for me!”
- “write a python script for a typical recon process”
- “i need an XSS payload that doesn’t use single or double quotes”
- “my XXE payload doesn't call back to my server, what could go wrong?”
- “write a response for report #133337”
The beta also comes with Hai Plays for you, which allows you to build your own security agents in HackerOne. You can create them at hackerone.com/settings/hai_p…. Some of the cool use cases we’ve seen so far are:
- write reports with minimal input from you (efficiency++!)
- convert reports into blogposts with a single prompt
- AI mentor to give feedback about your communication and increase the likelihood of a reward
In the background we’ve been working on agentic behavior, which we expect will soon come to Hai for Hackers as well. These AI agents can act like your hacking buddy and hack alongside you. We’ll keep you in the loop on our progress.

English
ch đã retweet
很好,这次我也是受害者了...被 @getAlby 偷走 0.00174788 BTC($191.96)。能偷是因为这是 Alby 的托管账号。我是很震惊的,因为这鬼协议我必然是不知情的...
我猜是不是会给我发邮件通知,果然 2025/5/1 给我发了个:
Updates to our Terms of Service – Please Review
我在邮件正文底部发现了这个“偷窃协议”:
An inactivity fee will apply to legacy Alby Accounts with a shared wallet created in 2023 or earlier, if there has been no account activity for 12 consecutive months.
然后我这笔 BTC 在 2025/5/26 被偷走了...
开眼界了...🤯😵💫😱



Cos(余弦)😶🌫️@evilcos
去中心化新定义:你的钱包不活跃,我就让钱离你而去了哦
中文
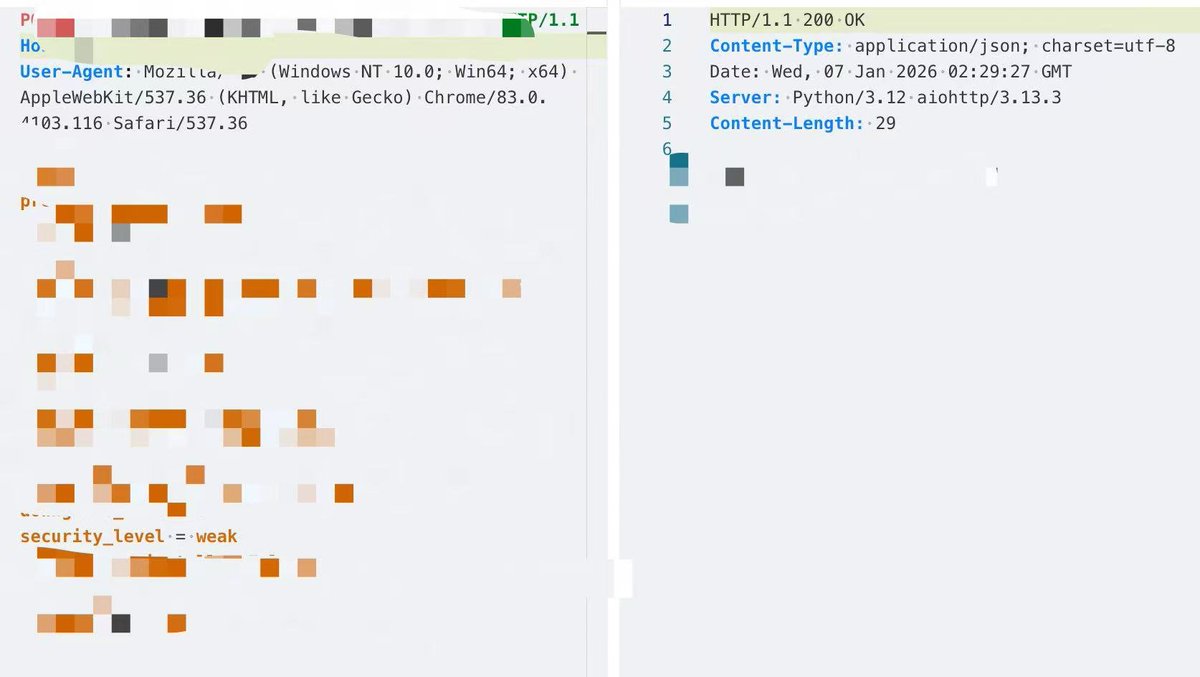
@ParamJani21 My case is just a special case
In most cases, it is difficult to chain the two
English

@chybeta Guide me please...I found SSRF but not know How to chain it to cache poisoning...! Please assist me...!
English