Rick
79 posts


Rick
@developerkavin
Existance is pain !!
Ghaziabad,Uttar Pradesh Tham gia Haziran 2024
130 Đang theo dõi8 Người theo dõi

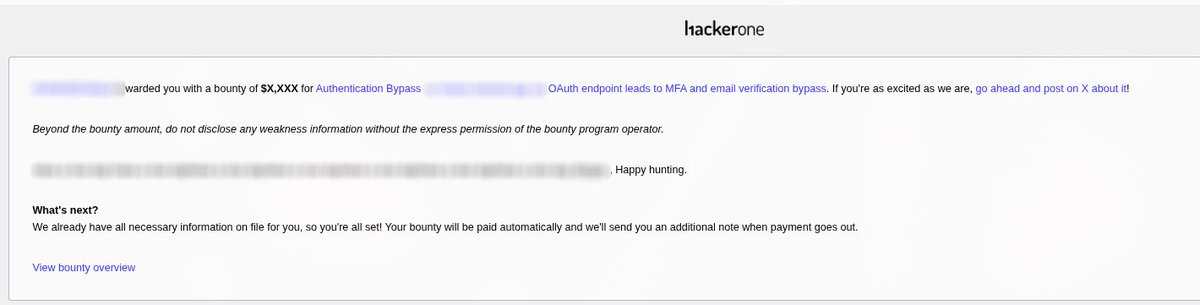
💰$X,XXX | 🐞2FA Bypass
Found an OAuth endpoint in an app where 2FA was not enforced under specific condition, resulting in a full auth bypass.
Sev : H
Like this post if you want a full write-up on this 📝
rgjny.me 👈
#HackerOne #BugBounty #TogetherWeHitHarder
English
Rick đã retweet
Rick đã retweet
Rick đã retweet

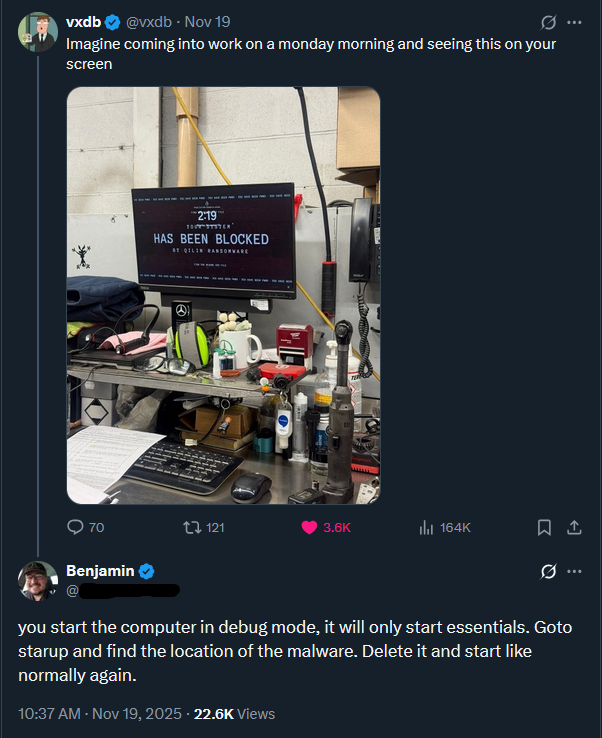
@vxunderground I once helped a friend wire $5000 in Bitcoin (>10 years ago) to a Ukrainian after one of his clients got fucked by BitLocker ransomware. Who would've thought all we had to do was reboot in safe mode to magically decrypt their files because the master key was obviously in Autorun

English

@vxunderground Never knew that one... thanks for increasing my knowledge ...
English
Rick đã retweet

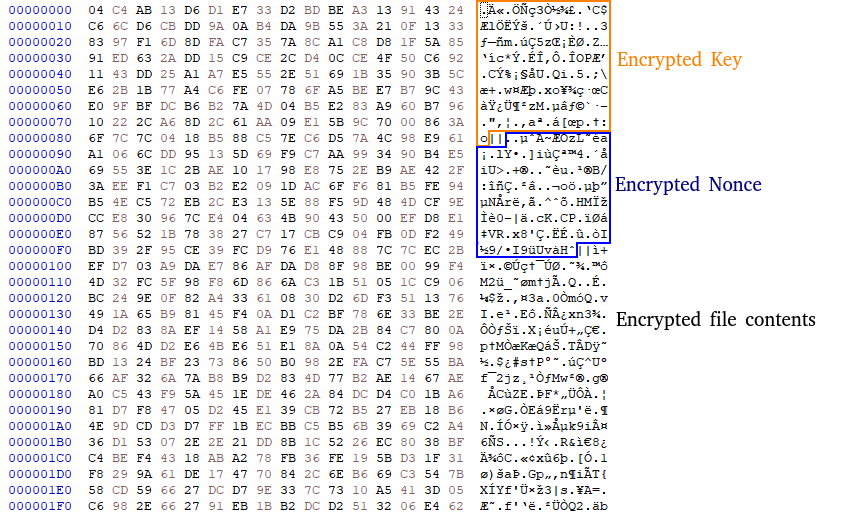
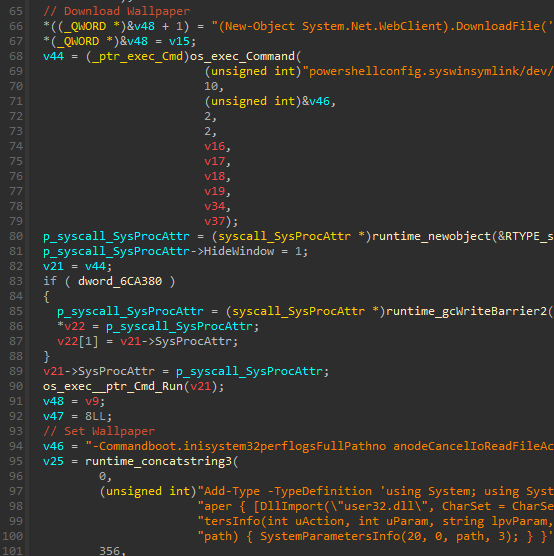
Using open source ransomware to target companies is illegal and for nerds....
Analysis of Yurei & The Ghost of Open Source Ransomware.
Research: #single-post" target="_blank" rel="nofollow noopener">research.checkpoint.com/2025/yurei-the…
OpenSource Ransomware [Prince]: github.com/oakkaya/Prince…
#analysis #malware
English

Lol, found a completely new RCE by accident while trying to find the RCE mentioned in the CVE 🤣. It was fun. Very fun!

Shreyas Chavhan@shreyas_chavhan
My first Auth Bypass to admin account takeover -- a chain of multiple vulns, reverse engineering an old CVE in a controlled environment obviously (for learning) with a complete blind approach so far. Hoping to see this helping me in real world too.
English

Feeling burned out and depressed. Bug bounty isn’t easy, especially in public programs where it’s all duplicates or informatives
Truth is, real bug bounty starts with private invites
Until then, it’s just pain.. or maybe it's a challenge!
Anyways, الحمدلله 🖤
#BugBounty #InfoSec

English
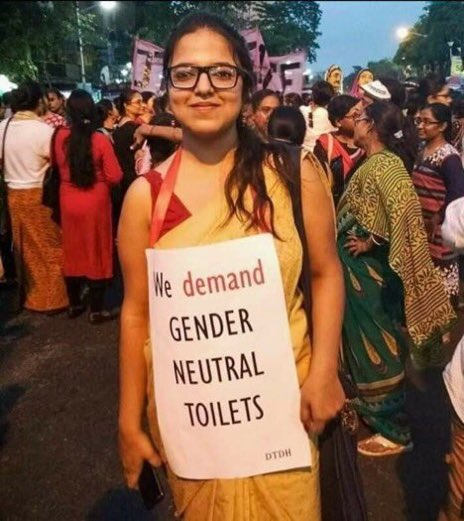
#Horrific In Sambhal, Uttar Pradesh, two Dalit youths who had gone to watch the Kanwar Yatra were tied to a pole and brutally beaten by a Hindu mob.
#DalitLivesMatter

English
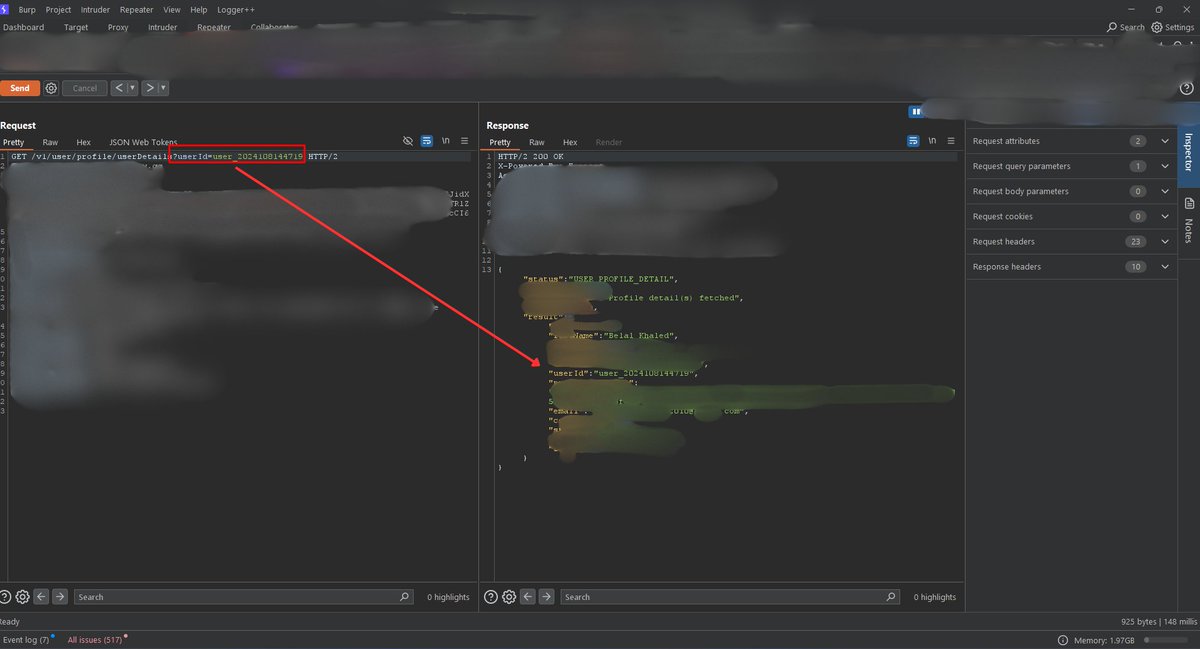
Session-Based Validation Bypass via Trusted Parameter Override
🔴GET /v1/user/profile/userDetails → Pulls my data based on my JWT session token.
🔴GET /v1/user/profile/userDetails?userId=victim-id
→ The app ignores the session and trusts the userId param which leads to exposing victim’s data
The logic prioritizes userId from the request over the authenticated session, leading to session confusion and broken access control.
#bugbountytips #websecurity

English


@KN0X55 And that’s why you have Webslinger to find the vulnerable URLs for you
English