🎩 Hats off to @eth_nik_dev for finding a low severity bug in the Hats vault
Nik has been an appreciated contributor in our community, constantly participating in the competitions we run.
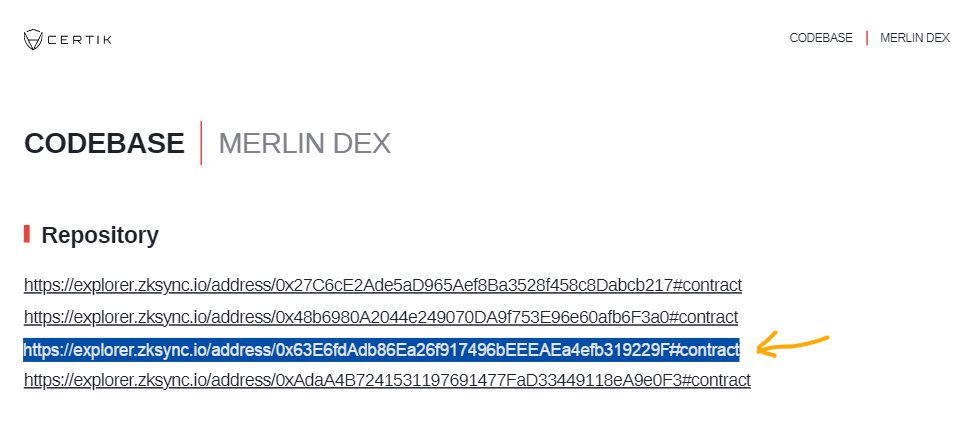
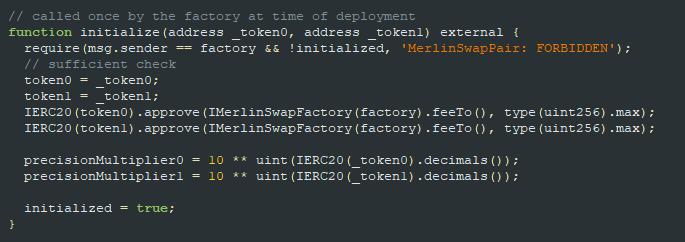
Check out our writeup 👇
hatsfinance.medium.com/frontrunning-i…
GIF
English