JEB Decompiler
400 posts


JEB Decompiler
@jebdec
JEB Decompiler & PNF Software news. Tweets by Nicolas Falliere.
SF Bay Area Tham gia Ekim 2011
457 Đang theo dõi2.3K Người theo dõi

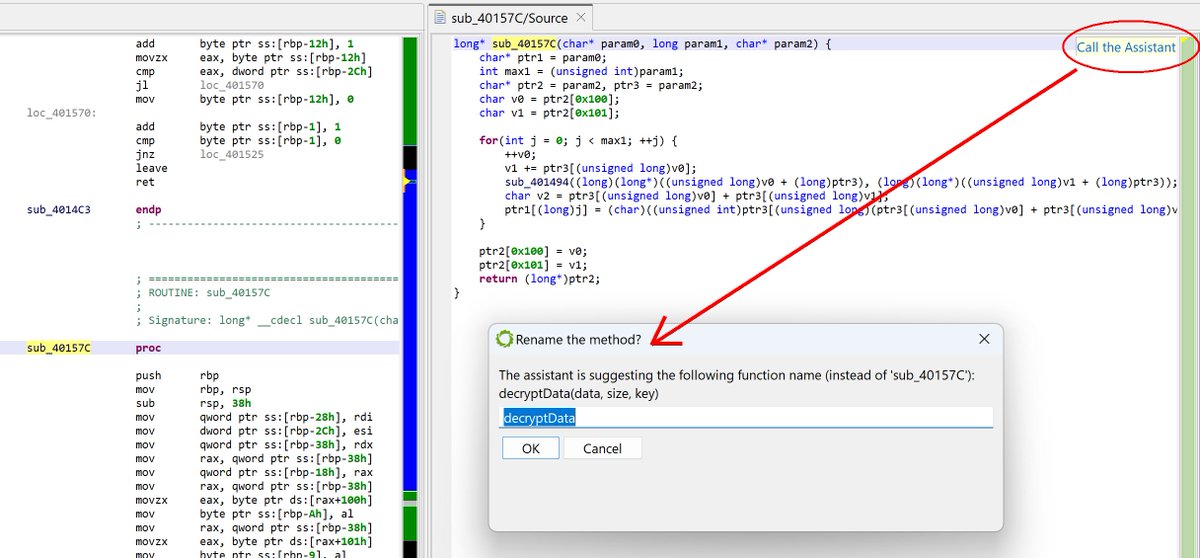
VIBRE is a conversational AI assistant that will help JEB users reverse-engineer your project files.
It is backed by the LLM of your choice (commercial/remote, local, or our own end-point for free) and by JEB's MCP server (which can be started separately and used by any AI tools, not just VIBRE).
Learn more about JEB 5.32 and VIBRE🤖 here: pnfsoftware.com/blog/vibe-reve…
#ReverseEngineering
English

JEB 5.31 ships with a generic SASS disassembler and experimental decompiler for GPU code compiled for Nvidia architectures Volta to Blackwell (compute capabilities sm_70 to sm_121) #ReverseEngineering
Learn more here: pnfsoftware.com/blog/reversing…
GIF
English

JEB 5.19 is available (pnfsoftware.com/jeb/changelist). An interesting new feature in this release is a mixed boolean-arithmetic (MBA) expression simplifier/breaker. It gives interesting results on obfuscated code.
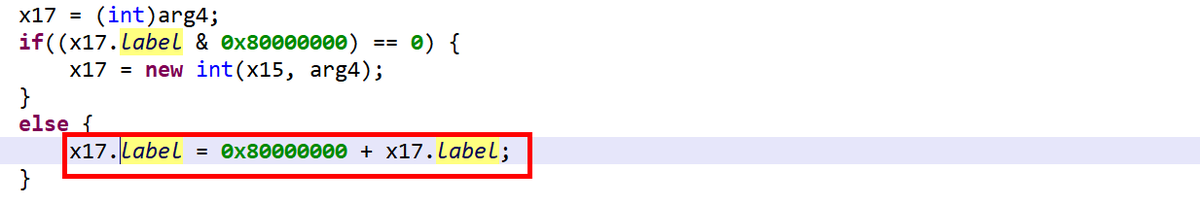
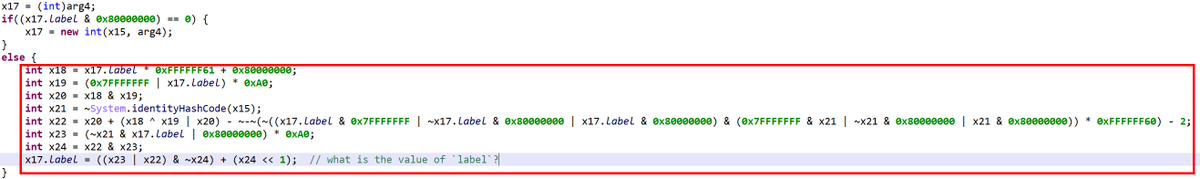
Have a look at the snippet in image 1, which is a decompilation with MBA as well as other bitwise simplifications disabled.
It is not easy to figure out that this code can be reduced to the MSB bit flip of its input, as seen in image 2. (The second input is pseudo-random and not used in the computation; its sole purpose is to obfuscate things further.)
This feature is enabled by default in JEB, but can be disabled by turning off the IR optimizers tagged as "DEOBFUSCATOR" (option: EnableDeobfuscatorOptimizers) #ReverseEngineering
English
JEB Decompiler đã retweet

🚀#Ph0wn2024 presents the Android Application Reversing workshop! Join Cedric Lucas to learn how Android apps are built, analyzed, and reverse-engineered using JEB(@jebdec ). Perfect for those diving into Android reverse engineering! 📱🔍
More info: #reverse-android-with-jeb" target="_blank" rel="nofollow noopener">ph0wn.org/workshops24/#r…

English

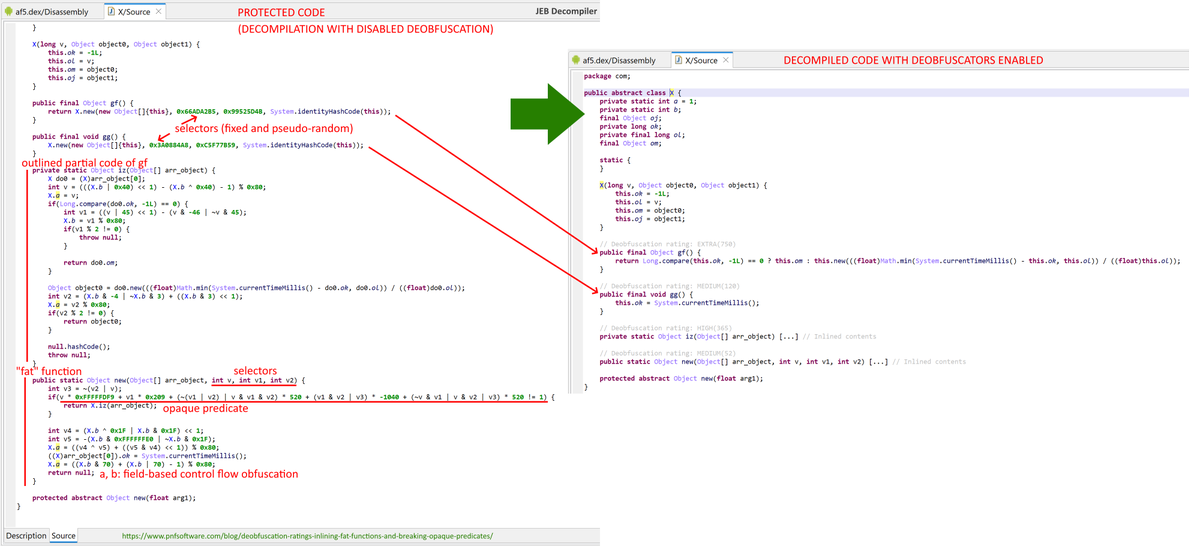
JEB 5.18 is available 🤖 Check out our latest blog post on inlining and deobfuscating "fat" functions: pnfsoftware.com/blog/deobfusca… #ReverseEngineering
English

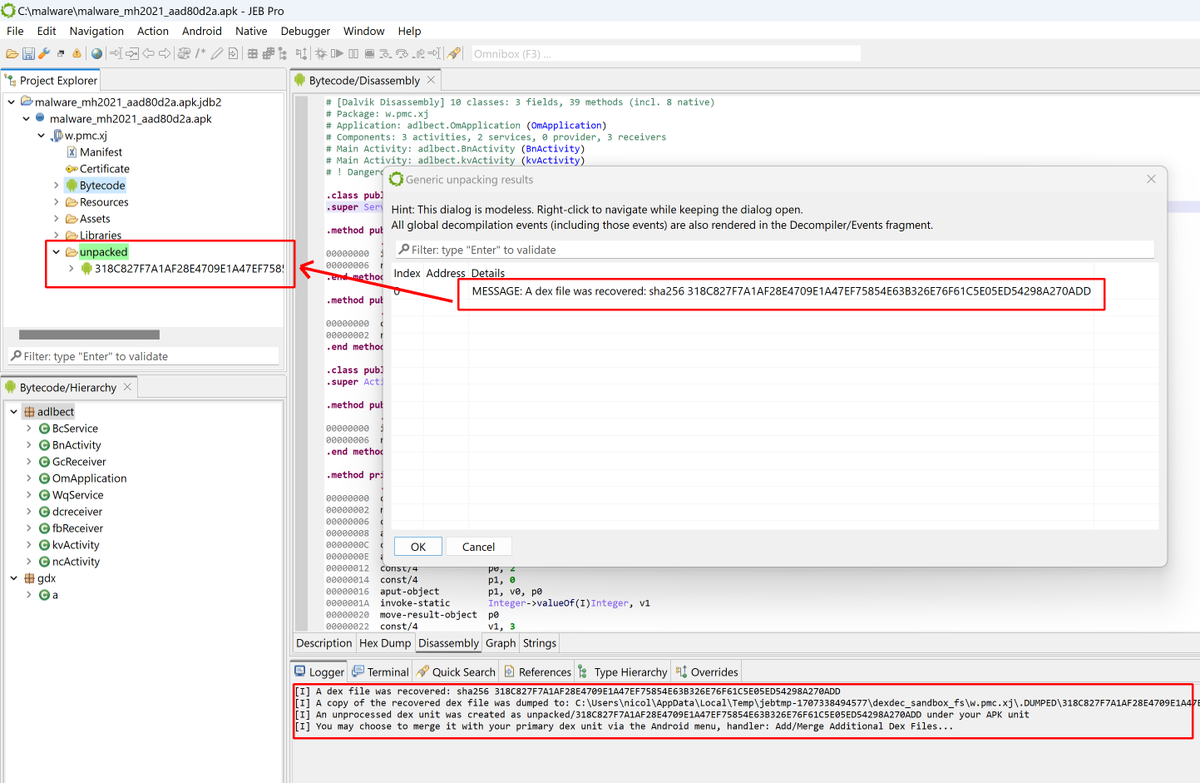
JEB 5.11 is available. More information about the generic unpacker here: pnfsoftware.com/blog/generic-u… #ReverseEngineering
English

JEB 5.9 is available! This release contains lots of important upgrades to both decompilers, and a new component for APK analysis, the "generic unpacker", which will attempt to unpack protected apps to recover dynamically-generated Android dex files. #ReverseEngineering
English

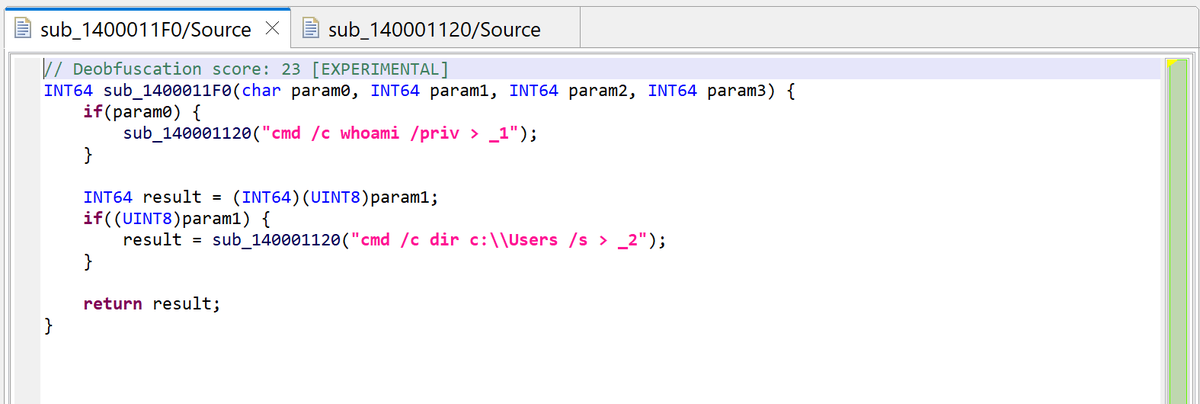
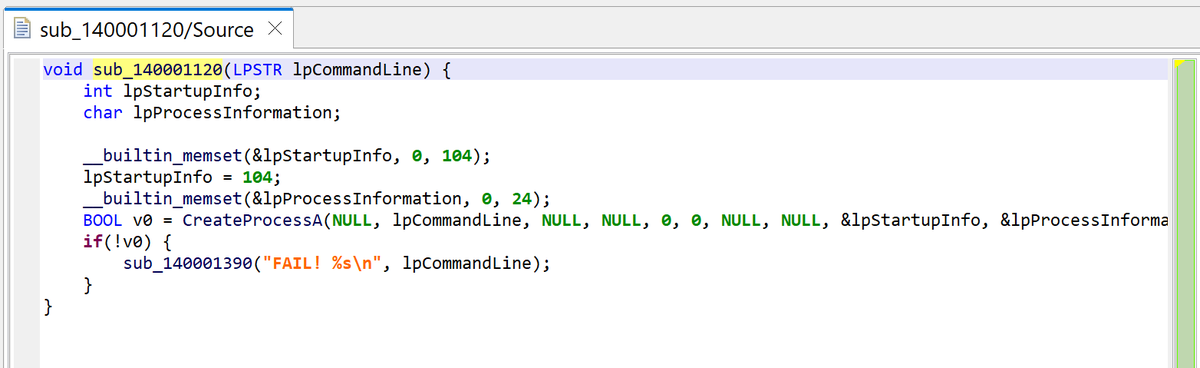
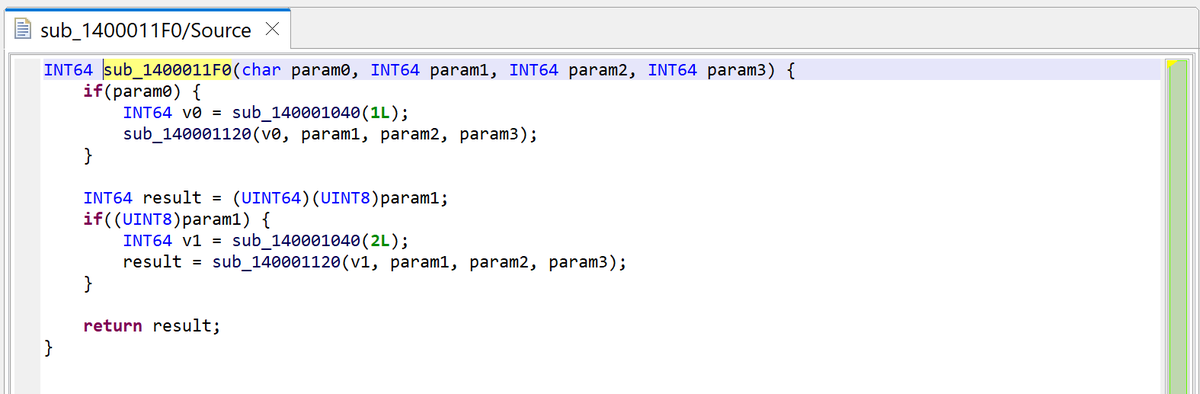
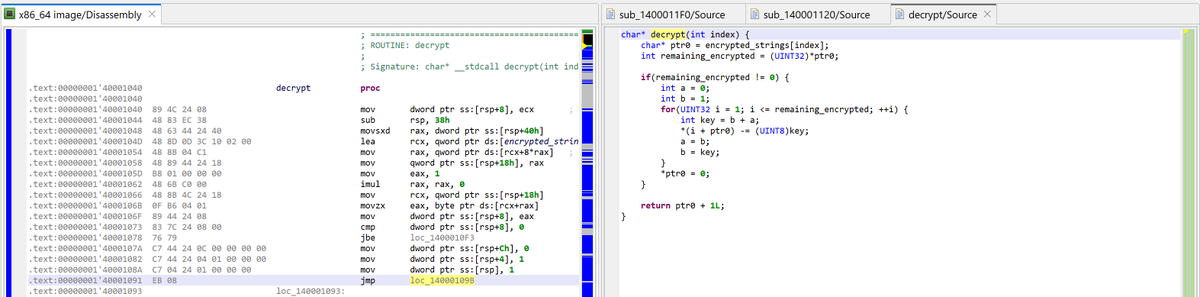
"How to use JEB to… auto-decrypt strings in protected binary code" - We are looking at a win64 malware, read more here: pnfsoftware.com/blog/how-to-us… #ReverseEngineering
English

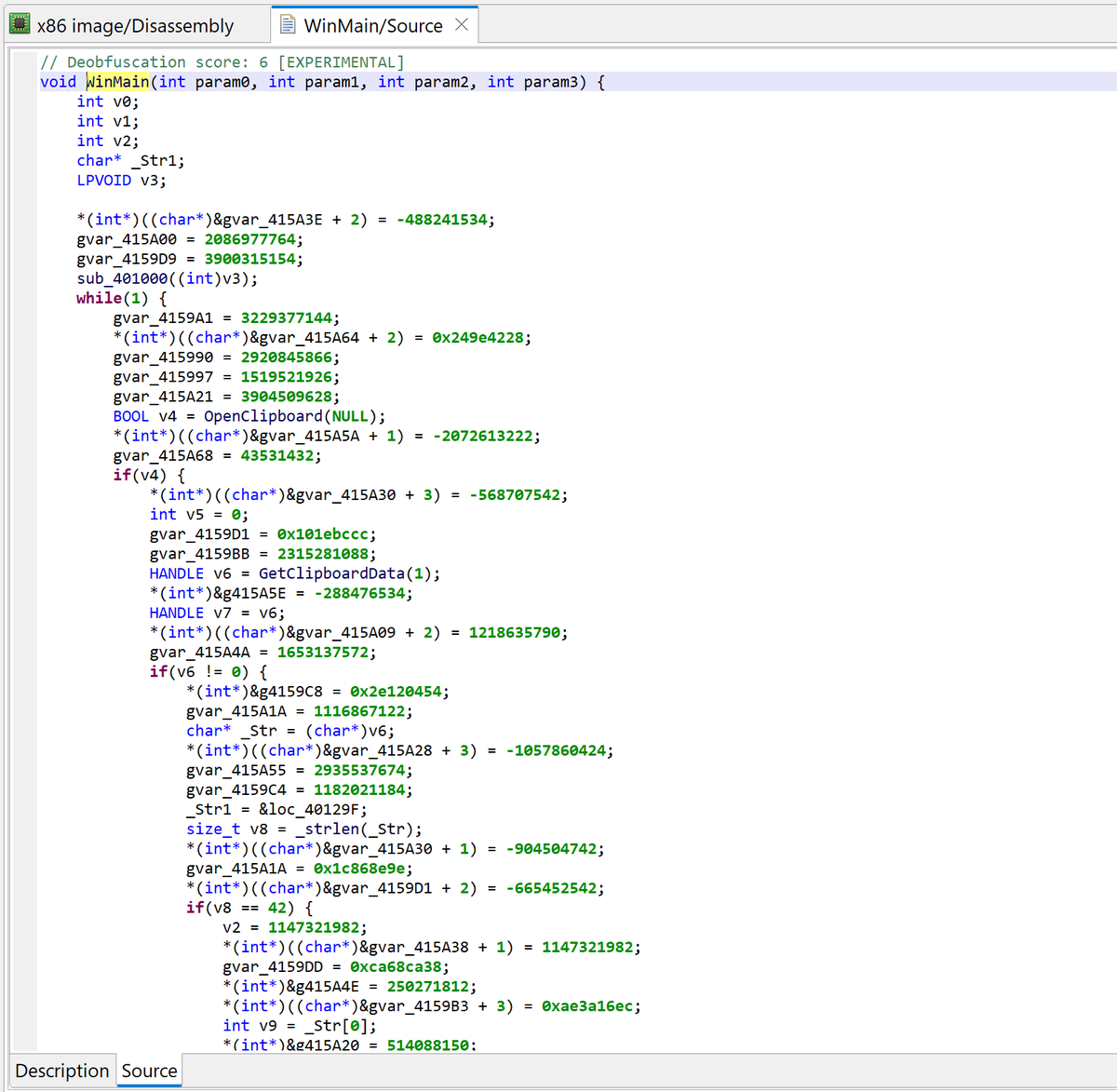
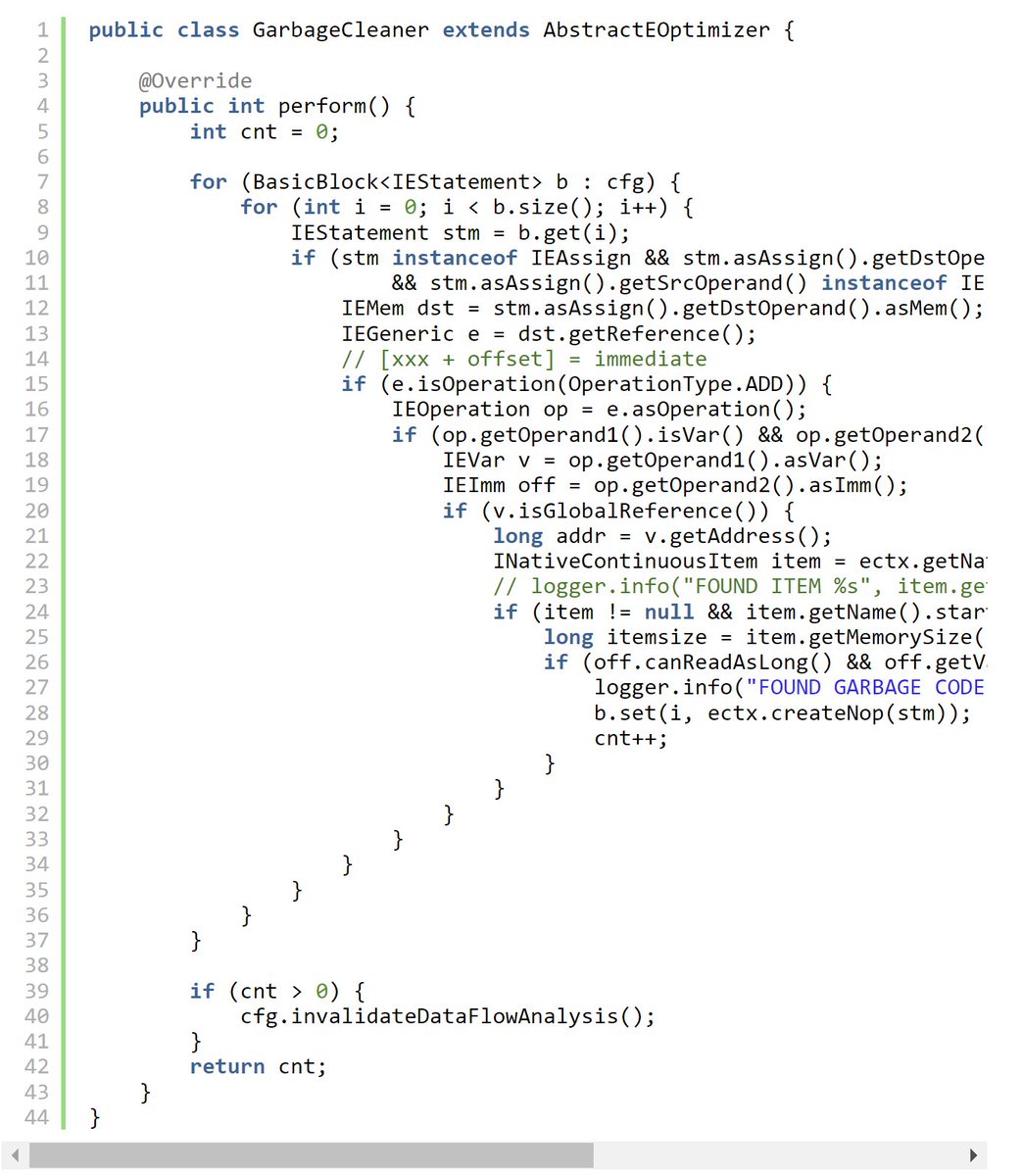
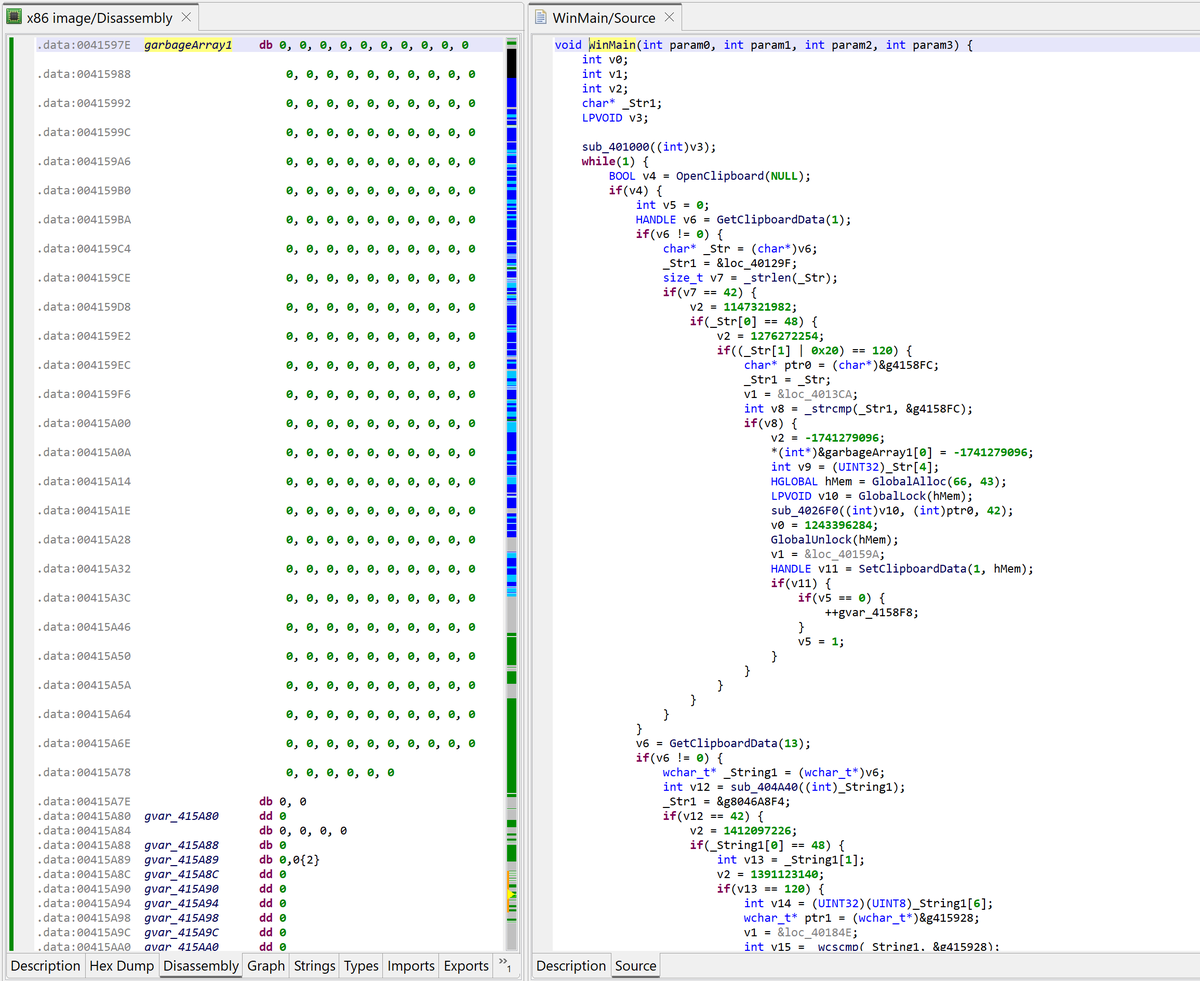
"How to use JEB to… analyze an obfuscated win32 crypto clipper" - Read our newest blog post here: pnfsoftware.com/blog/how-to-us… - Also, JEB 5.7 is being published today :) #ReverseEngineering
English

@wyq0001 If you can email support@pnfsoftware.com or message us on Slack (pnfsoftware.com/chat), with the sample file, we should be able to have a look. Thanks.
English

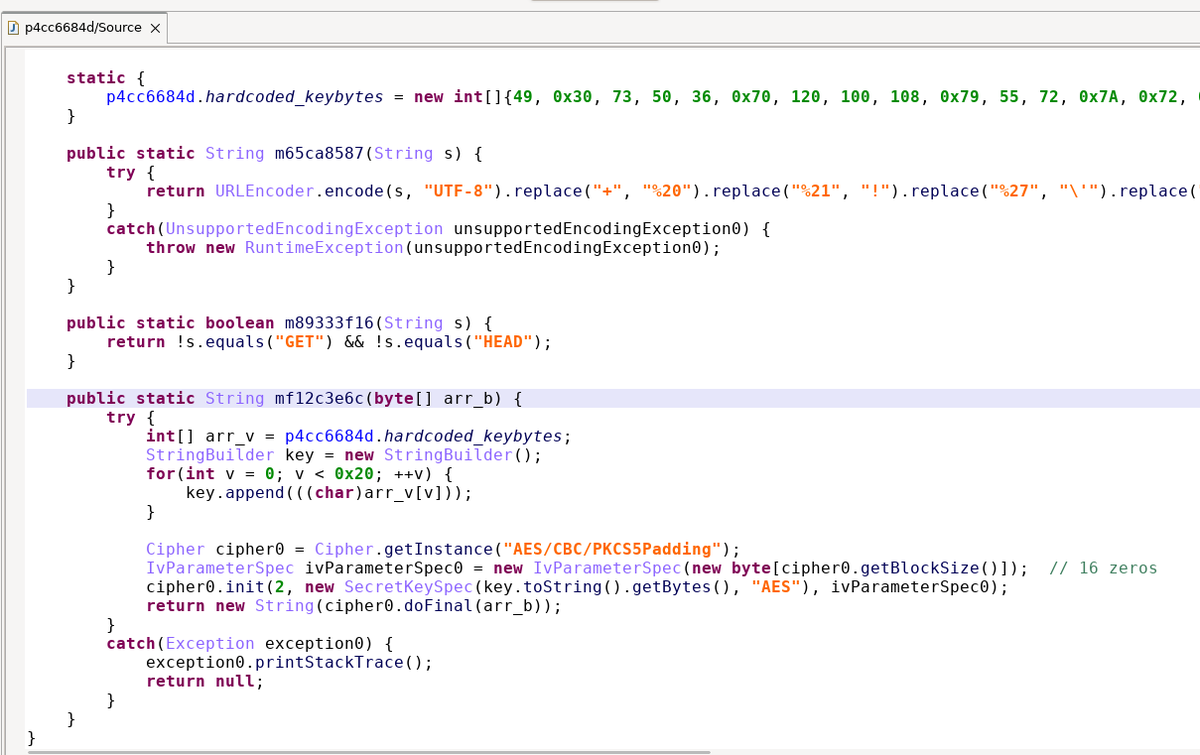
hi @jebdec you have [awesome] string decryption. Why can't you decrypt those AES-obfuscated strings in this case? It's not much more difficult than decrypting a hand-made algo...
You have the key, the IV and the ciphertext is provided as argument to the decryption function.
English

@VinayakBhujawa1 Sounds good, will look into that for the next updates. Thanks!
English


JEB 4.30 was released today!🤖The associated blog shows how to recover statically-registered JNI natives or how to retrieve string constants that were entirely removed from a Dex. Details here: pnfsoftware.com/blog/recoverin… #ReverseEngineering
English