置顶推文

Are you also interested in bug bounty?
Then you can learn more about one of my favorite bugs here: proviesec.medium.com/broken-link-hi…
#infosec #BugBounty #Hacking #brokenlink #bugbountytips
English
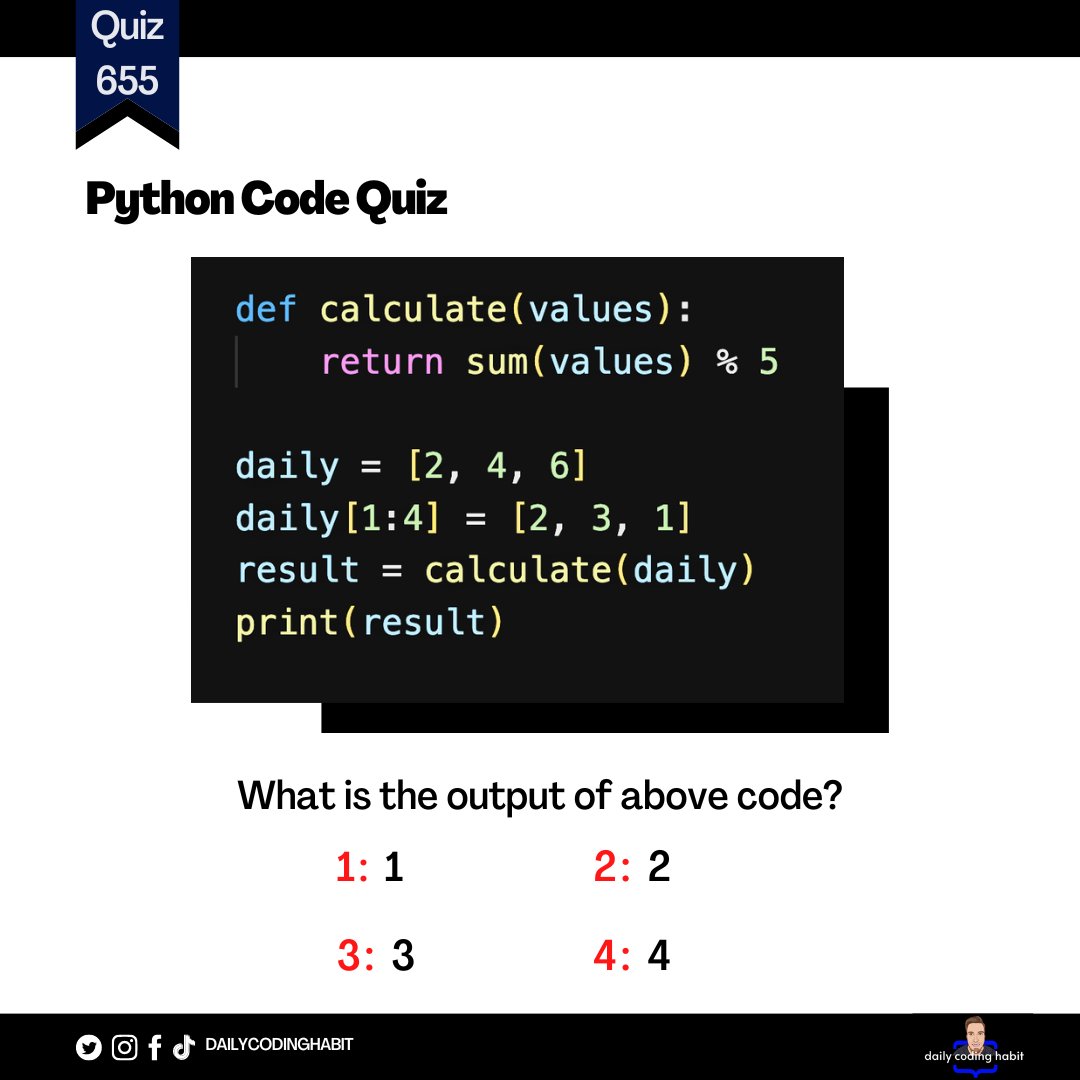
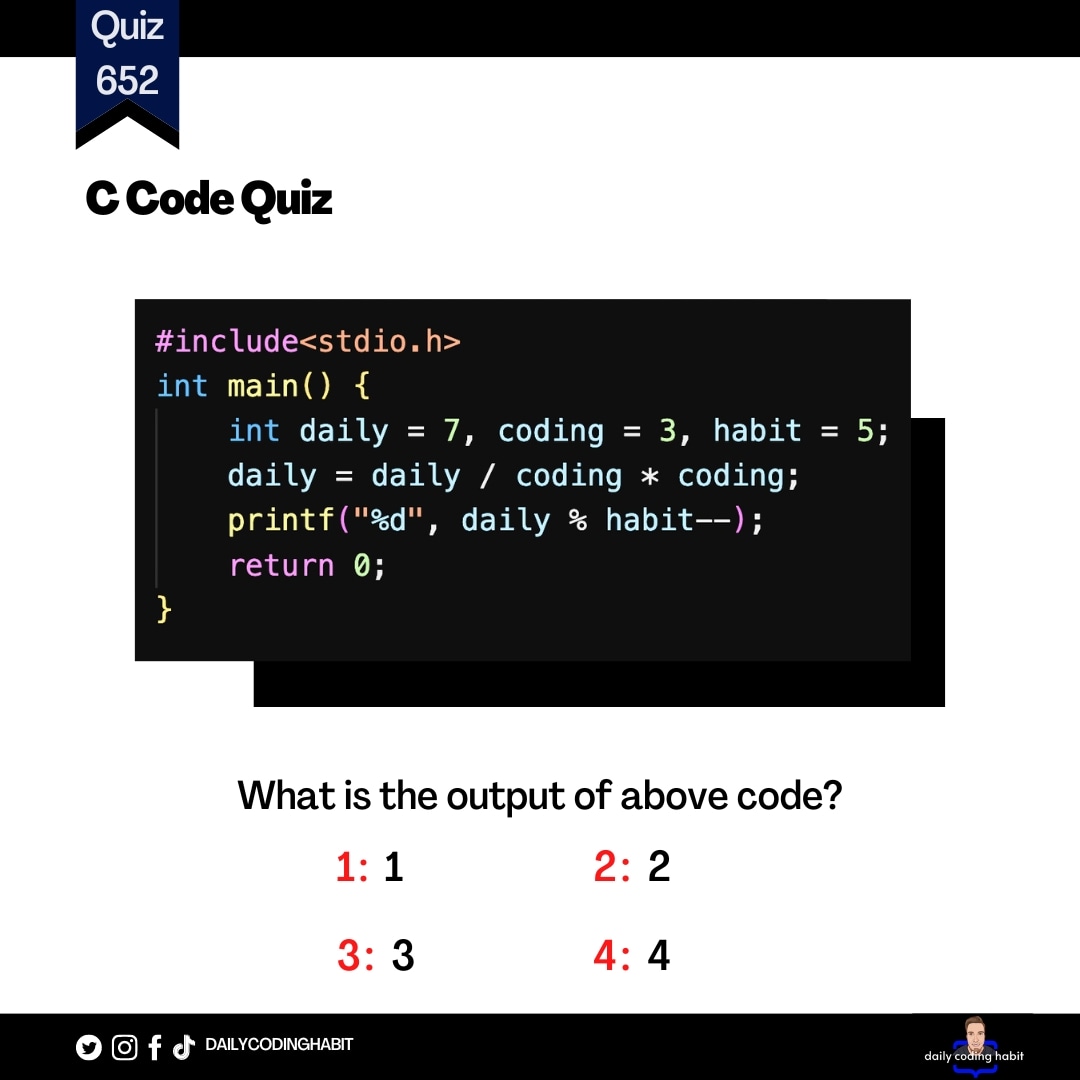
Dailycodinghabit
1.8K posts


@Dailycodinghab1
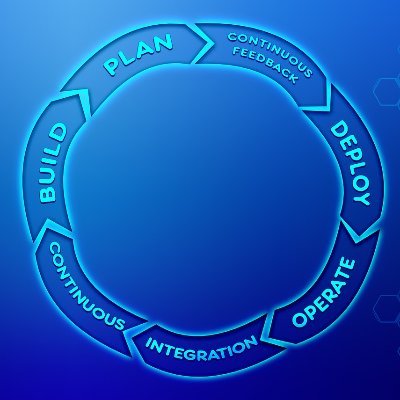
Oliver | Developer | 🇩🇪 #dailycodinghabit You daily coding lesson Python | C++ | PHP | Javascript | Swift | C | C# | Golang...