FAMASoon
4.2K posts

FAMASoon
@FAMASoon
Security research blog: https://t.co/iTsZ04qDQ8 GitHub: https://t.co/nfFPKkjf5O






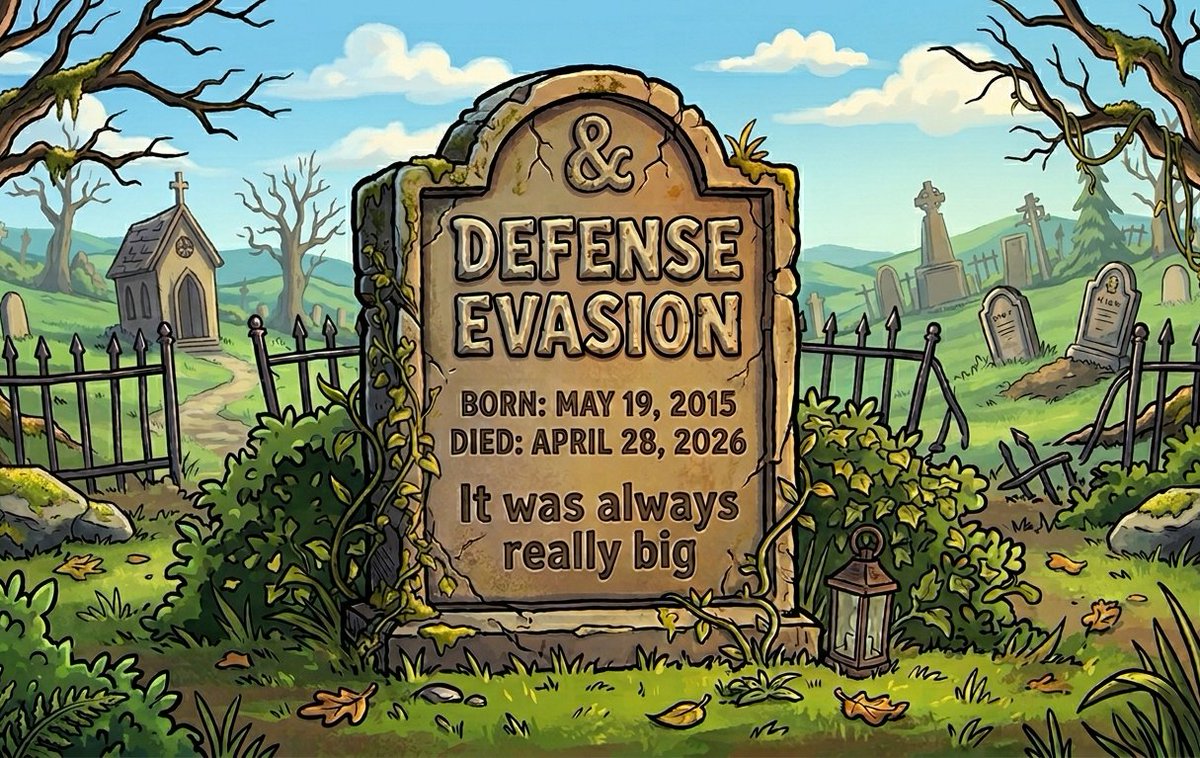




#Microsoft is finally pulling the plug on cross-signed driver trust 🔒 Starting April 2026 (Win11 24H2/25H2/26H1 + Server 2025), the kernel will only load WHCP-certified drivers by default. Cross-signed certs were deprecated back in 2021 — but trust persisted until now. Key points: 🔹 Only WHCP-signed drivers trusted by default 🔹 Small allow-list for widely-used reputable cross-signed drivers 🔹 Rolls out in evaluation mode first (100h uptime + 3 reboots before enforcement kicks in) 🔹 Confidential/internal drivers can still run via App Control (WDAC) policy anchored to UEFI Secure Boot PK/KEK 🛡️ BYOVD impact — this is a big deal The majority of classic #BYOVD drivers used to kill #EDRs (e.g., gdrv.sys, rtcore64.sys, DBUtil_2_3.sys…) are cross-signed. If their signatures are now untrusted by default, weaponizing them gets significantly harder. Combined with the vulnerable driver blocklist, the attack surface shrinks meaningfully. Not a silver bullet — WHCP-signed drivers can still be vulnerable — but closing the cross-signed weapons cache that threat actors have been raiding for years is a real, concrete win. Should've happened in 2021 when the certs actually expired, but better late than never. 🫠 📄 Blog: techcommunity.microsoft.com/blog/windows-i… 📄 Cert deprecation: learn.microsoft.com/en-us/windows-… #ReverseEngineering #BYOVD #EDR #MalwareAnalysis #WindowsSecurity







