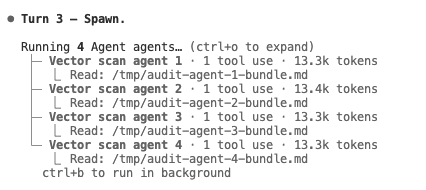
JaCoderX@JaCoderX
You’re describing security as closing the gap between what the user means and what the system does, and treating “good security” as *redundant specifications* that all have to line up before the system acts. That’s exactly how we built Bloxchain.
**Same idea, in practice**
We don’t assume one click or one key can fully encode intent. So the protocol only does something when *several* specifications agree:
- **What** (the action and its parameters)
- **Who** (which keys are allowed to request, approve, or execute)
- **When** (for sensitive actions, a mandatory delay and a second step)
- **Where** (which targets and which functions are even allowed to be called)
If any of these don’t align, the system doesn’t proceed. No single “vote” is enough.
**Two ways we get redundancy**
1. **Time and a second step (for high‑risk actions)**
For the most sensitive operations (e.g. changing who controls the wallet), you first *request* the change. Only after a waiting period can you *approve* it. So the same (or authorized) party has to confirm the same intent at two different times. That’s two separate specifications of “yes, this is what I want.”
2. **Split between “who decides” and “who executes”**
One key *signs* what should happen (the intent is in the signed message). A different key *executes* (submits the transaction and pays gas). So “what I want” and “what actually runs” are two different steps. The system only runs when both align: the right signer signed and the right executor submitted.
**Risk‑sensitive friction**
We don’t add extra steps everywhere. We add them where the downside of a mistake is large:
- **High‑risk** (e.g. ownership transfer, changing recovery): full flow — request → wait → approve (and, where used, signer vs executor separation).
- **Lower‑risk** (e.g. a routine transfer to a whitelisted contract): one flow that still uses signer + executor, or other lighter checks, so normal use stays simple.
So: *easy for low‑risk, harder for high‑risk*, without “more clicks for everything.”
**Guards on *what* can be called**
Besides “who” and “when,” we also bound *what* the wallet is allowed to do:
- Only certain *functions* (e.g. “transfer”) are registered as allowed.
- Only certain *target* addresses (e.g. a specific token contract) are whitelisted per function.
So intent is constrained along another dimension: even with the right keys and timing, the system will only execute calls that match these rules. That’s another overlapping specification that has to match.
**Roles and recovery**
Control is split across roles (e.g. owner, broadcaster, recovery). No single key has full control; recovery is a separate path. So “who I am” and “what I’m allowed to do” are specified in more than one way - again, redundancy.
**In short**
We treat security the same way you do: minimize the gap between user intent and system behavior by requiring *multiple, overlapping specifications* to agree. Bloxchain is built so that:
- Intent is expressed in more than one way (request vs approve, sign vs execute, roles, whitelists).
- High‑risk actions need more of these to align (including time and a second step).
- Low‑risk actions stay relatively smooth.
No perfection — only risk reduction through redundancy, and different angles (action, consequences, who can do it, what’s allowed, and when) all having to line up before the system acts.
---
*Bloxchain Protocol — [GitHub](github.com/PracticalParti…)