Arris Huijgen 已转推

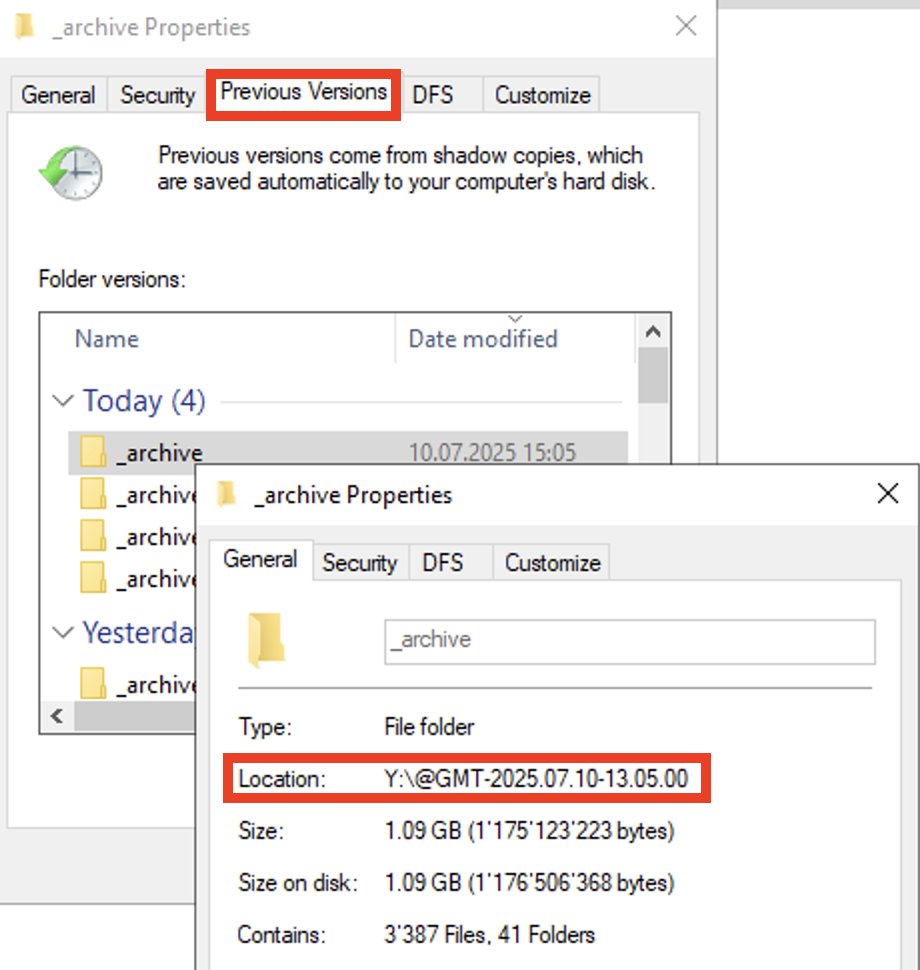
Small updated to DRSAT just pushed that will also allow Group Policy Editor and Certificate Authority / Templates MMC snap-ins work over a TCP only SOCKS connection.
github.com/CCob/DRSAT
English
Arris Huijgen
237 posts


@bitsadmin
Windows Offensive Security Enthusiast 🤠 Blog: https://t.co/CAwdjs2rKS GitHub: https://t.co/YG2YOxfosm









Look at those cute little blobs in your internal network. They look harmless, but how about the one carrying SOCKS? It's ProxyBlob, a reverse proxy over Azure. Check out @_atsika's article on how it came to exist after an assumed breach mission ⤵️ 👉 blog.quarkslab.com/proxyblobing-i…

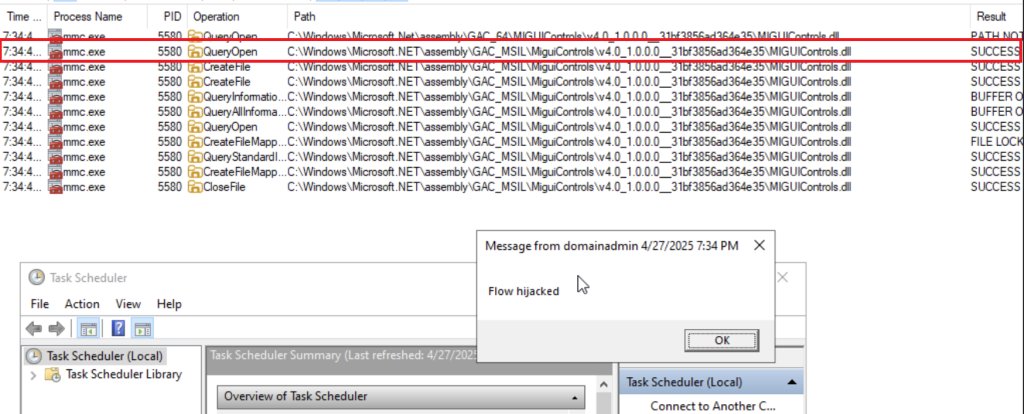
.NET GAC and NIC hijacking for lateral movement: williamknowles.io/net-gac-and-ni…





