Jayesh Madnani
977 posts


Jayesh Madnani
@Jayesh25
Researcher in charge @ Ethical InfoSec Services | HackerOne Top 10 | https://t.co/JSX03Wv1vl
http://hackerone.com/jayesh25 加入时间 Şubat 2016
499 关注14.3K 粉丝

We just shipped the biggest monitor upgrade in ArgosDNS history. 🎉
Per-monitor item limits are up 10x to 600x across every plan. Starter now covers targets that used to need Business.
Full write-up: argosdns.io/blog/monitors-…
English

Tomcat JMX Proxy exposed without auth?
Wrote a blog about how I got shell on a production Tomcat behind Cloudflare despite the deploy API being locked down, WAF blocking payloads, and CDN filtering template syntax.
8 dead ends. Then AccessLogValve + docBase + relaxedQueryChars + EL injection. 14 requests to RCE.
Tool + nuclei template included!
hackt.us/from-tomcat-jm…
#bugbountytips #bugbounty
English
Jayesh Madnani 已转推
Jayesh Madnani 已转推

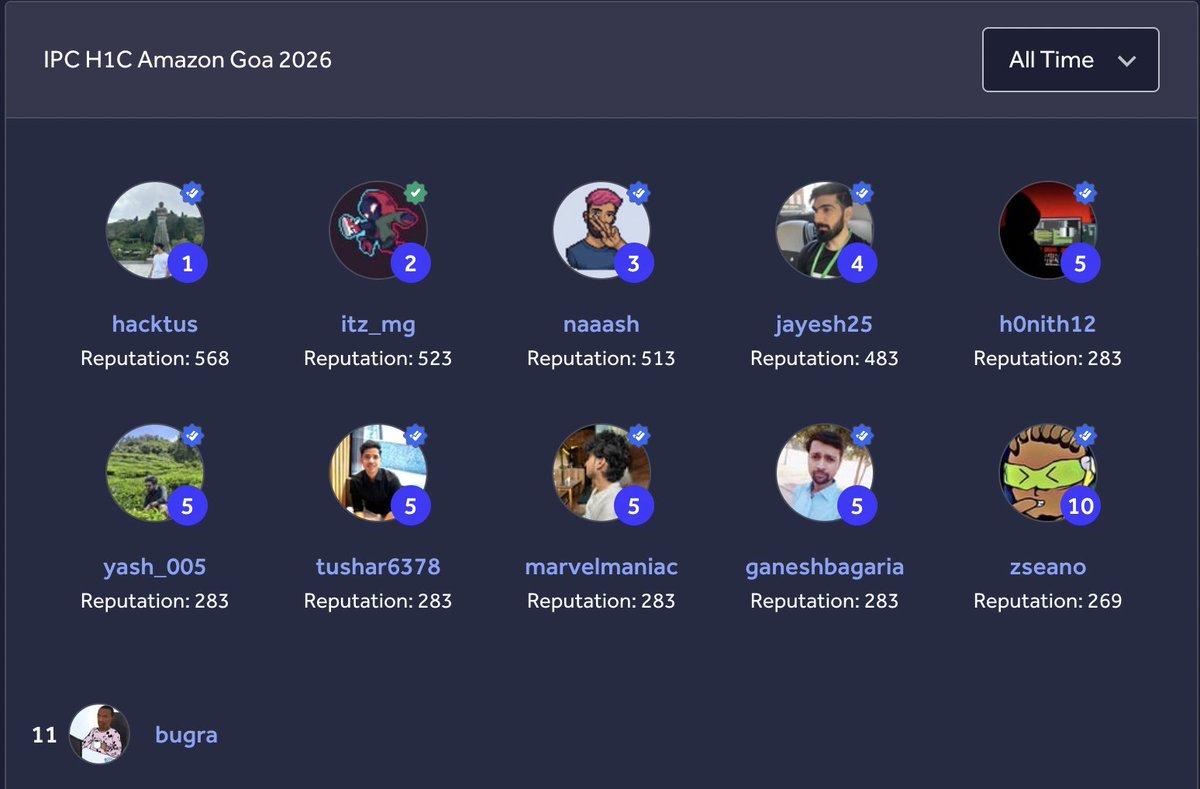
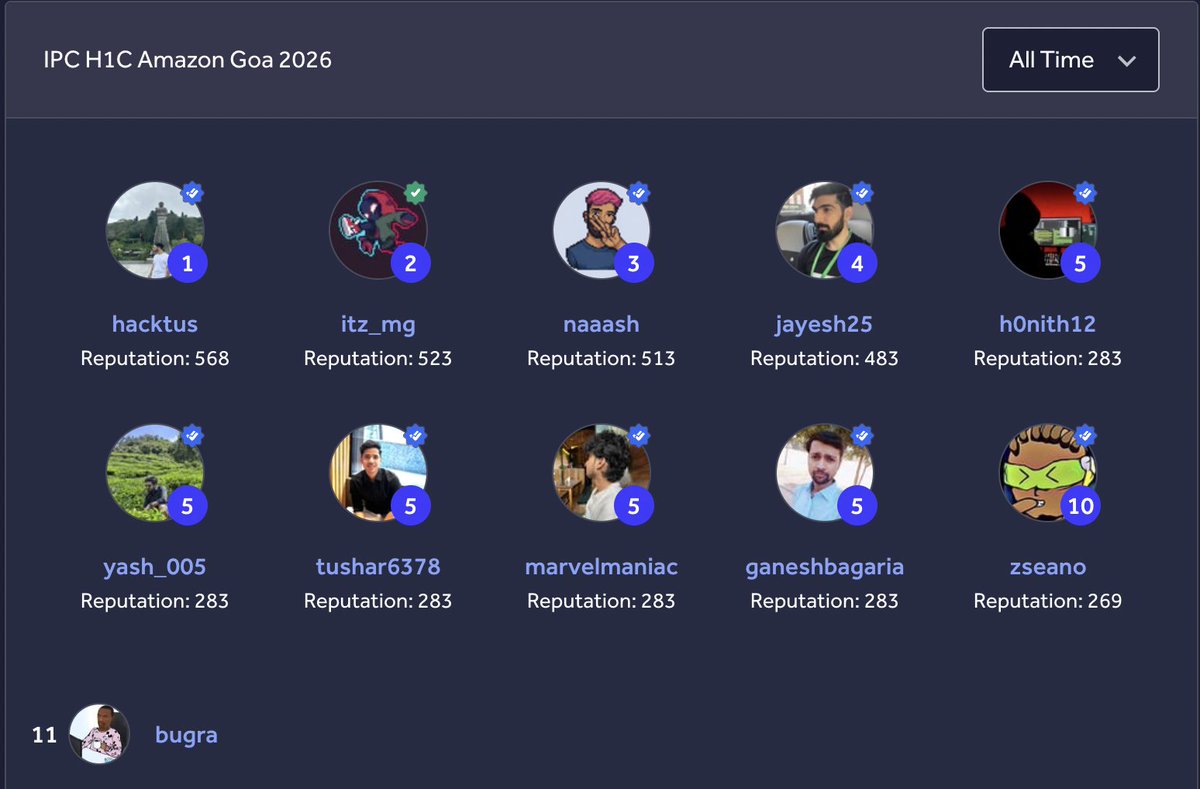
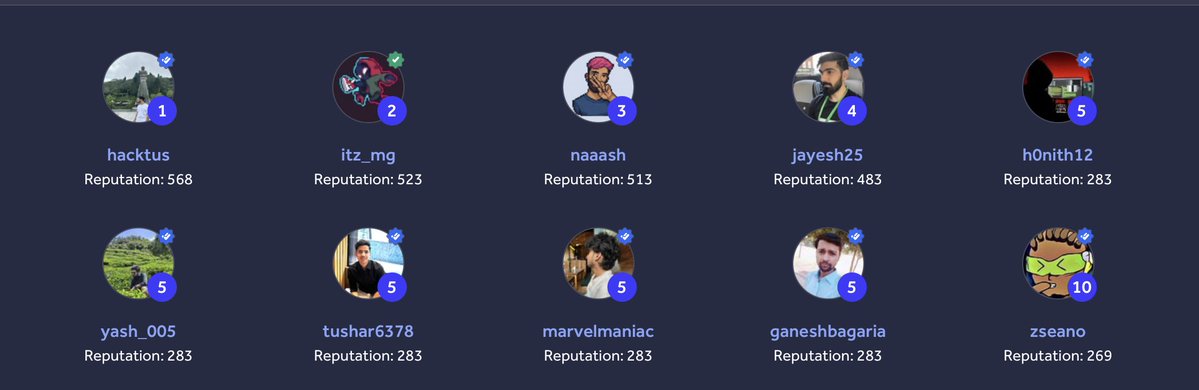
Just wrapped up an unreal week hacking @amazon in Goa 🇮🇳🌴 Teamed up with @Jayesh25, @itz_mg_ and @_naaash_ and somehow walked away with 1st place on the leaderboard 🏆
Picked up a stack of bonuses along the way:
- Pwnership: Eventwide Most Impactful Report
- Dive Deep: Most Creative Bug
- Most Impactful Issue on a specific asset
- Most # of Critical Issues on a specific asset
- Learn and Be Curious: Show and Tell (x2)
Got to meet so many talented hackers I'd only ever spoken to online, and honestly that was the best part of the whole trip. Such a good crew, so many good conversations, left with a bunch of new friends 🤝
Saw some genuinely wild techniques I'd never come across before, and for some reason 90% of the craziest bugs got popped between 3-6 AM 😅 something about that hour just hits different.
Huge thanks to @amazon and @Hacker0x01 for putting this together. Unique location, unique challenge, unforgettable crew.



English
Jayesh Madnani 已转推

Had a really fun time hacking @amazon in Goa 🌴
Teamed up with @H4cktus, @Jayesh25 and @itz_mg_ and we ended up 1st on the leaderboard 😅
Picked up a bunch of bonuses too:
🏆 Pwnership: Eventwide Most Impactful Report
🧠 Dive Deep: Most Creative Bug
💥 Most Impactful Issue on a Specific Asset
🔥 Most # of Critical Issues on a Specific Asset
🎤 Show & Tell
Big thanks to @Hacker0x01 for organizing this 🙌
Photo dump from the chaos 👇

English

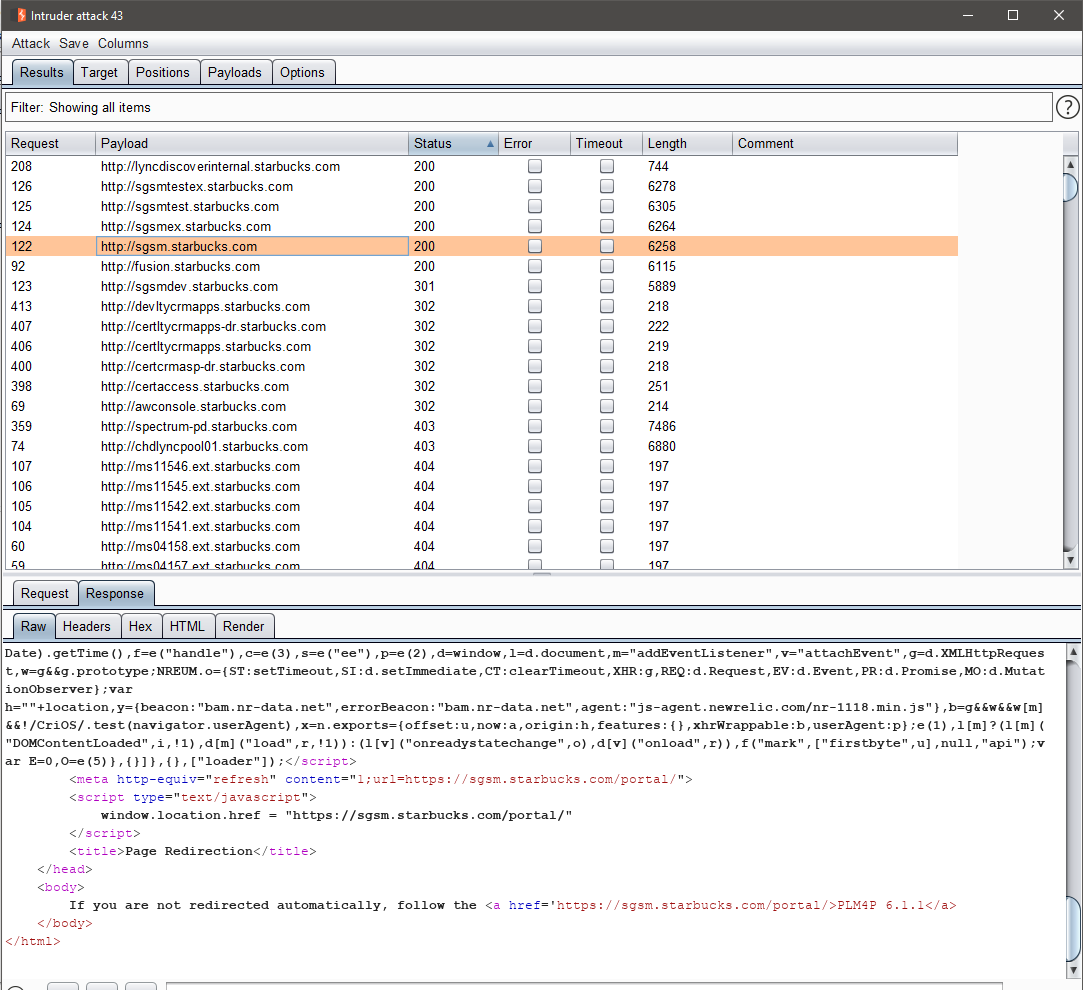
Small bug bounty writeup from one of my findings from the past - even back then having a carefully crafted list of non resolving starbucks hostnames was essential (shameless ad: argosdns.io). Writeup:
argosdns.io/blog/how-i-got…
Background of hackerone.com/reports/500468
English

IMO opus and sonnet models are enough to make everything else redundant at this point. It’s just lack of awareness with the partners but it’s only a matter of time. Most likely scenario is if they’ve got an edge or good enough contracts they will be acquired but under the hood they’re using the same AI tech… the only difference is how they’re distributing or were efficiently managing their workflow with a low cost basis, which is a problem that imho is already solved with the subscriptions we have available today.
English

@damian_89_ @ITSecurityguard @Th3G3nt3lman @GodfatherOrwa Awesome. This is going to be really valuable specifically on those large scopes :P
English
Jayesh Madnani 已转推

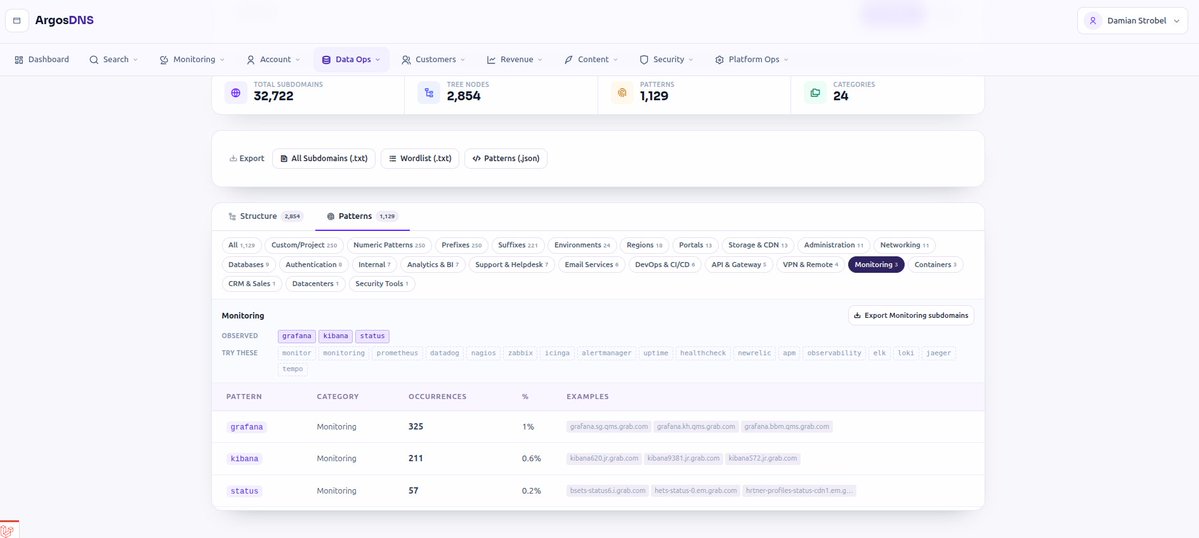
An there it is - "Domain Intelligence": argosdns.io/domains (for public access)
Feel free to explore. Trial users can explore preset limited data, growth plans+ can search their own stuff!
@Jayesh25 @ITSecurityguard @Th3G3nt3lman @GodfatherOrwa


English

@damian_89_ @Th3G3nt3lman @GodfatherOrwa That would be super nice.. would make it so much easier to shortlist interesting stuff 🙌🏻
English

Someone interested in this type of data within argosdns.io? Thinking of allowing regular users to access it. @Jayesh25 @Th3G3nt3lman @GodfatherOrwa
English
Jayesh Madnani 已转推

Why can the ArgosDNS.io database look smaller in some cases?
Because bigger subdomain counts can just mean more wildcard noise.
This article explains why:
argosdns.io/blog/wildcard-…
English

I’d say each has its own strengths but personally I’ve already replaced SecurityTrails with ArgosDNS. In my testing I’ve seen better quality results probably because the data seems to refresh more frequently and the product seems to be very focused on this niche. Another big factor for me was the price point it’s realistic enough that I can actually run it every few days via the API. With SecurityTrails that gets pretty expensive very quickly. That said, the free version is a good starting point if you want to compare the results and data freshness yourself before deciding. Most people will probably end up seeing similar differences once they try both :)
English

I've had firsthand access to ArgosDNS and can say it’s produced quite a few solid results that I didn’t even have in my own database. Unlike many tools, the data actually feels meaningful rather than just raw volume.
I've known @damian_89_ a while and have been chasing him for ages for his recon secret sauce 😄 From what I’ve seen so far, ArgosDNS is doing a lot of smart permutations, picking up real-world naming patterns, scanning cloud certs, and doing a ton of crawling behind the scenes to get this data. It’s also nice that the dataset is already deduped so you’re not dealing with garbage.
Feel free to give it a shot at argosdns.io
Damian Strobel@damian_89_
Hey guys, I just launched argosdns.io - if you are into IT security, bug bounty hunting, red teaming, ... this is interesting for you! argosdns.io
English

@Omkumar_13 Not quite what I meant but during live hacking events programs have a higher bounty scale than usual and of course these are high-paying programs that one would usually shy away from unless they were specifically in an LHE and learned about their true potential.
English

Here’s a quick insight into how a single opportunity can dramatically change your earning potential in bug bounties.
Ever wondered what kind of difference a Live Hacking Event (LHE) can make?
Picture this:
You report 10 XSS vulnerabilities on a newly launched public program and walk away with around $5k in total bounties.
Now compare that to someone invited to a Live Hacking Event reporting those same 10 XSS bugs - they could easily walk away with $75k–$100k. Same bugs. Completely different outcome. That’s the power of getting invited to an LHE. It unlocks new scope, direct access to top programs, face-to-face interactions with HackerOne triage and security teams, networking with elite hackers, and opportunities you won’t get anywhere else.
HackerOne has outlined the eligibility criteria for invites here: hackerone.com/blog/earning-h…
My advice? Focus your efforts on aligning with these criteria. One invite can really shift your entire growth curve, skills, learning, recognition, and bounties.
PS: Drop a comment if you feel you should’ve been invited to an LHE but haven’t yet. I’d love to hear your experience and it may help surface visibility for @Hacker0x01.
English

PS – Shoutout to @H4cktus for the Idea to give this a try :)
English

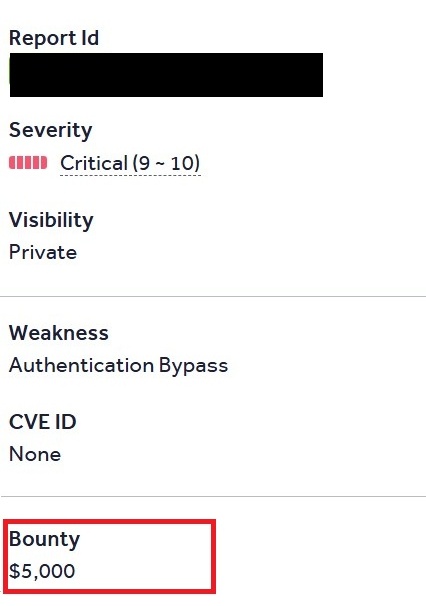
Scored a $5,000 bounty today. I’ve only started messing around with AI in my workflow THIS week. Normally I’d spend hours trying to escalate certain bugs - the kind that takes a lot of digging and escalation and I'd usually end up moving away from it considering the ROI. But this time I let AI handle some of the painful parts of the manual escalation process and it actually helped me efficiently escalate the bug. Ended up turning what would’ve been a tiny payout into a $5000 bounty.
Now I’ve basically got Burp Suite on one screen, AI on the other, and it feels like cheating (in a good way).
This might actually change how I hunt moving forward with respect to escalating stuff to avoid manual work whereever possible. 🚀
English