Archie أُعيد تغريده
Archie
69 posts

Archie
@Archie_1997
A teen with an aspiration for computers, likes to code in C / C++ every once in a while.
انضم Ekim 2021
94 يتبع437 المتابعون
Archie أُعيد تغريده

The reason why I am even posting this right now is because I directly copied this theme from
@Archie_1997
! I was reading many of the recent posts from https[:]//Archie-os[.]github[.]io and really liked the theme and obviously it seems works for technical posts (thanks Archie)!
English
Archie أُعيد تغريده


@sixtyvividtails The threads actually aren't valid objects either! The !object command fails when given the address of an idle thread. Windows Internals also confirms this should be the case.
English

@Archie_1997 Hah, very cool find!
Note while KiInitialProcess (Idle) is indeed just block in ntoskrnl, I think IDLE threads are actually valid kernel objects (valid _OBJECT_HEADER; just 0 id, no CID entries). So they ought to be openable via ObOpen*. Not that it'll help detect in any way 😺.
English

Getting code execution in a process that cannot be located using traditional kernel APIs and is untouchable from usermode? All while staying PatchGuard-friendly?
Sign me up: archie-osu.github.io/2025/04/13/pow…
English

@panchoszczcur @RiotVanguard Oh, great catch. I'll edit the article to properly list the authors. While the thread you posted is a great resource, I couldn't find any post discussing the actual hooked methods. I'm not part of any cheating circles, therefore if the info is shared on Discord, I wouldn't know.
English

@Archie_1997 @RiotVanguard The article you mentioned in there was not written by Nick Peterson, it was written by the authors listed as youd expect.. the authors are listed there and the first paragraph states it.. i think it should be appropriately noted
English

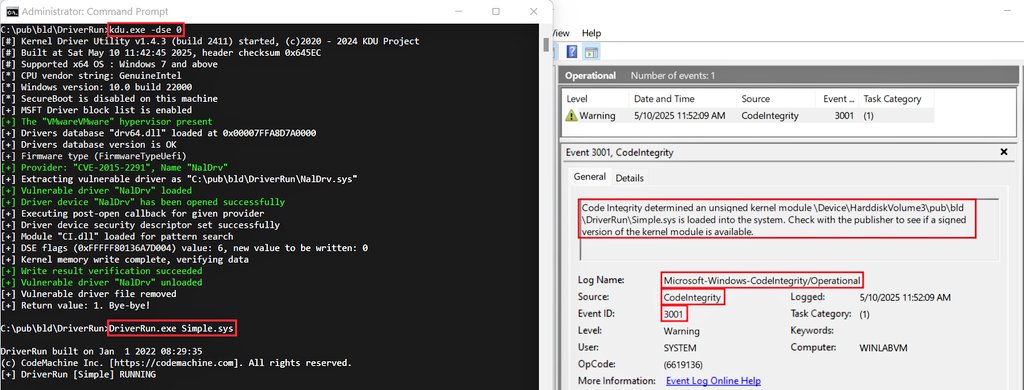
Dug into @RiotVanguard's kernel driver's dispatch table hooks.
The article took an unexpected turn half way through, as I found some not yet documented stuff, such as the complete list of system calls hooked by the driver.
Article link:
archie-osu.github.io/2025/04/11/van…
English

@panchoszczcur You make great points. Hooking ETW is certainly not a new technique, and there is multiple ways of hijacking CF via it. You sadly didn't save the rewrite in time, as I started looking Vanguard's hook right after publishing this article.
I'm sorry you didn't learn anything new.
English

@Archie_1997 i’ll save you the rewrite for riot vanguard from the horses mouth.. revers.engineering/fun-with-pg-co…
this community needs to stop enabling lazy researchers to gain visibility on recycled (plagiarized) info.. write about something you did on your own.. not piggyback for clout.
English

ETW is an incredibly powerful tool in the wrong hands.
Just finished writing about how it allows drivers to hook context switches on Windows 11 24H2 while remaining PatchGuard and HVCI compatible: archie-osu.github.io/etw/hooking/20…
English

@sixtyvividtails @Denis_Skvortcov That's incredibly helpful! Thank you for pointing it out, it's really a godsend 🤩
English

@Archie_1997 That's very nice!
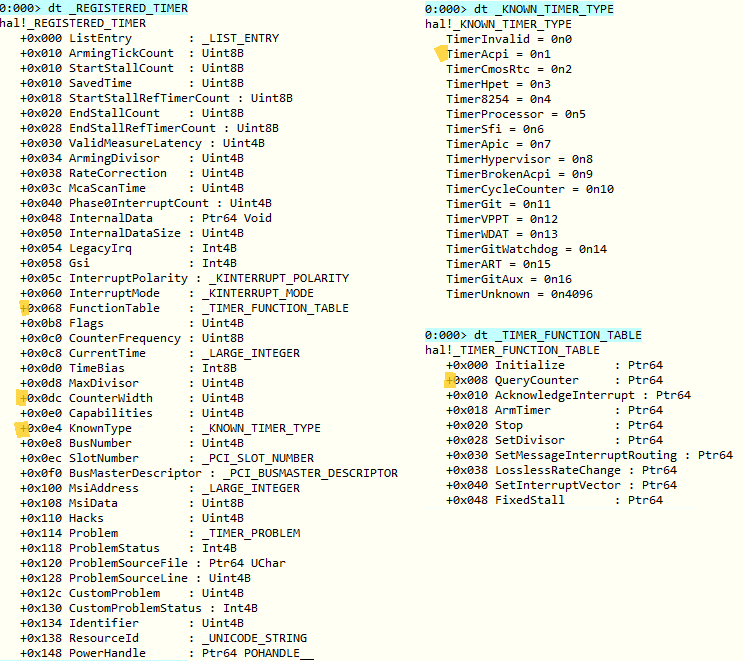
Note HalpPerformanceCounter ref'd in nt!KeQueryPerformanceCounter is ptr to _REGISTERED_TIMER structure.
// cc @Denis_Skvortcov
English

@tulachsam RWEverything delivering as always - got a clue as to why the mapping fails on Windows 11?
English

Super cool project, if you haven't yet, check it out.
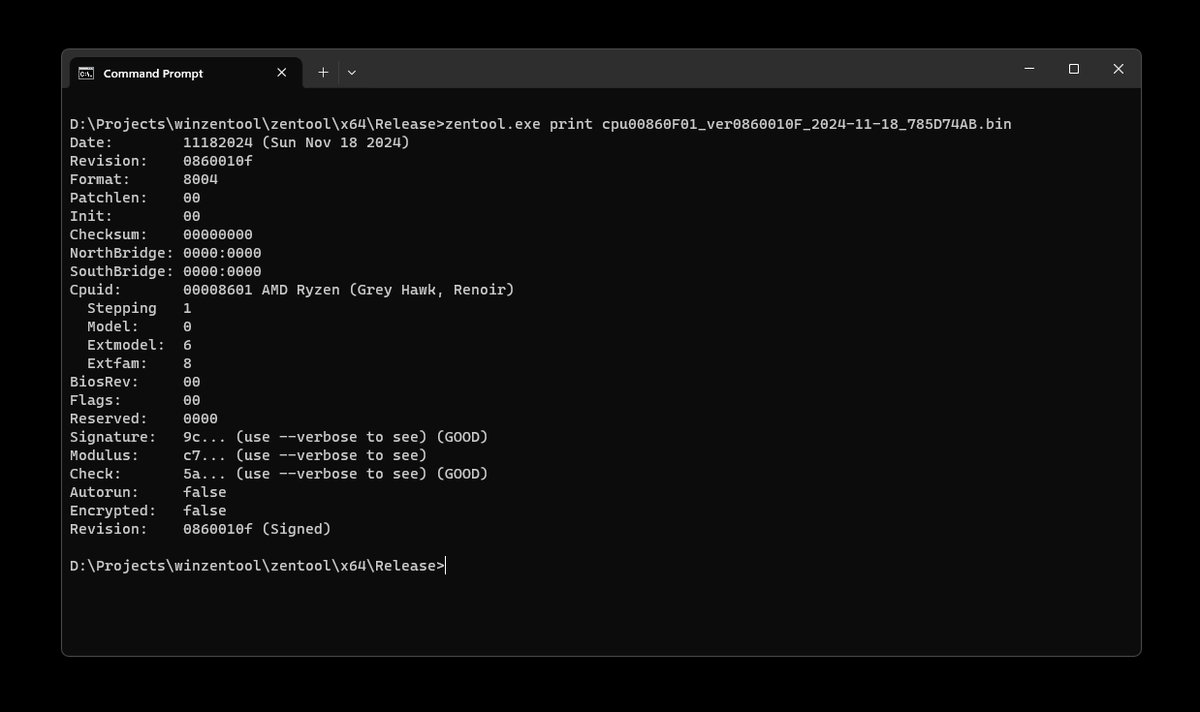
I have started porting it over to Windows. After fighting with hacky macros and different handling of packed structures in MSVC, I've got everything working except the loading part (need to work on kmode component).
Tavis Ormandy@taviso
You can now jailbreak your AMD CPU! 🔥We've just released a full microcode toolchain, with source code and tutorials. bughunters.google.com/blog/542484235…
English
Archie أُعيد تغريده

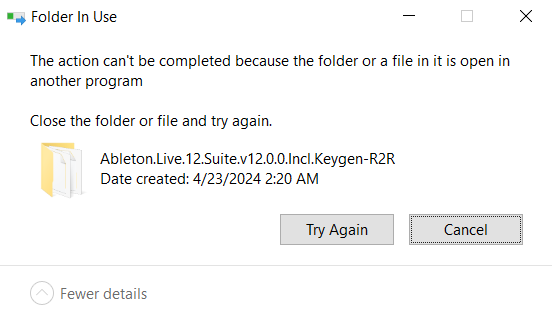
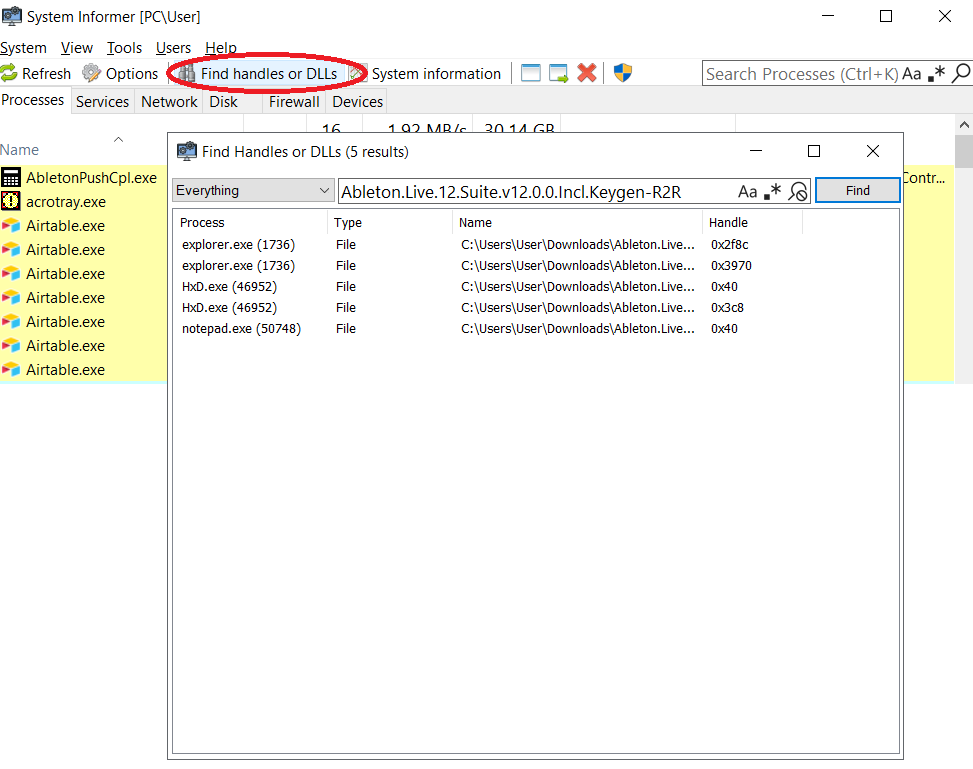
@wisdomicz @gf_256 System Informer can't do that because of Microsoft threatening to no longer sign their drivers. Look around and find the last build of Process Hacker (v3.0.4953), it doesn't yet have these restrictions.
English
Archie أُعيد تغريده

@SturdyStubs @ruostu @Throat_YT Having to restart your computer has nothing to do with it being (or not being) a kernel-level anticheat. EAC and BE are both kernel-level anticheats but don't require a reboot.
The reason VGK does is due to it being a boot driver.
English

@ruostu @Throat_YT EAC is not kernel level. A kernel level anticheat is loaded before anything else on your system which is why anticheats like vanguard require a restart to launch and run at all times. Not because they want to know every little thing you do but because it has to.
English