pwrflcat
750 posts


pwrflcat
@Darkwebcomputer
🇺🇸 occasionally knowing Microsoft security stack


started learning chinese, just in case




can someone sue them for this, please?



Kim calls out a detail in the attack on Stryker attack that will get lost in medical/national security headlines. Executives had personal phones wiped because corporate MDM was installed on their private devices!! Without proper personal backups, personal assets are potentially irrevocable. As an executive, I'd be pretty sour about this 'occupational hazard.' From the company perspective, during a major incident, their key decision makers lost: • their phone • their contacts • their communications • access to company systems With a stock price diving, this is operational blackout. Feel so bad for the security team...



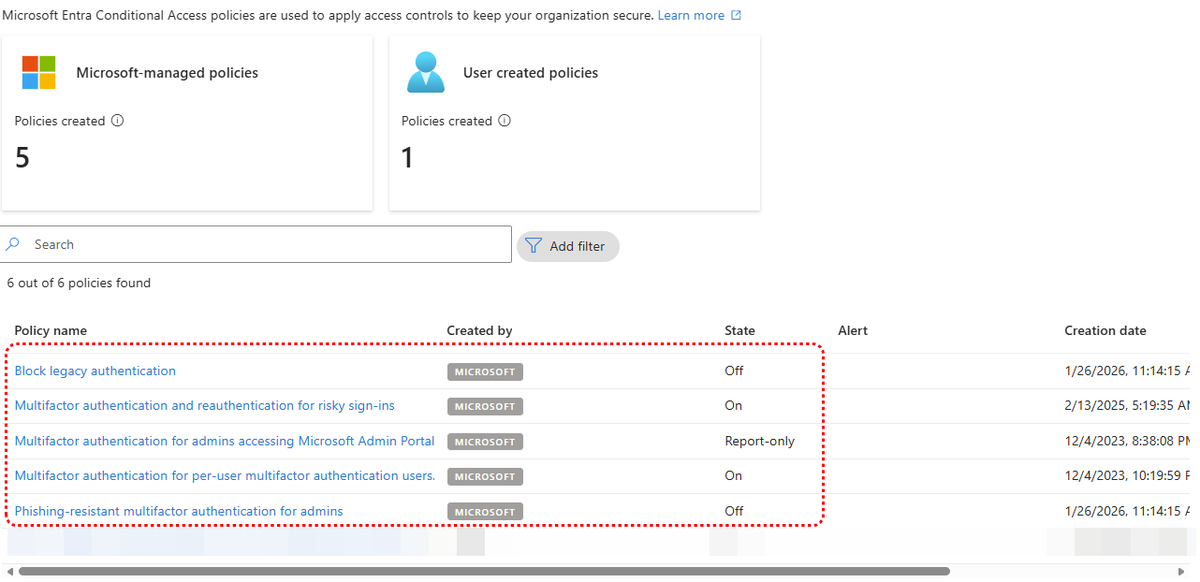
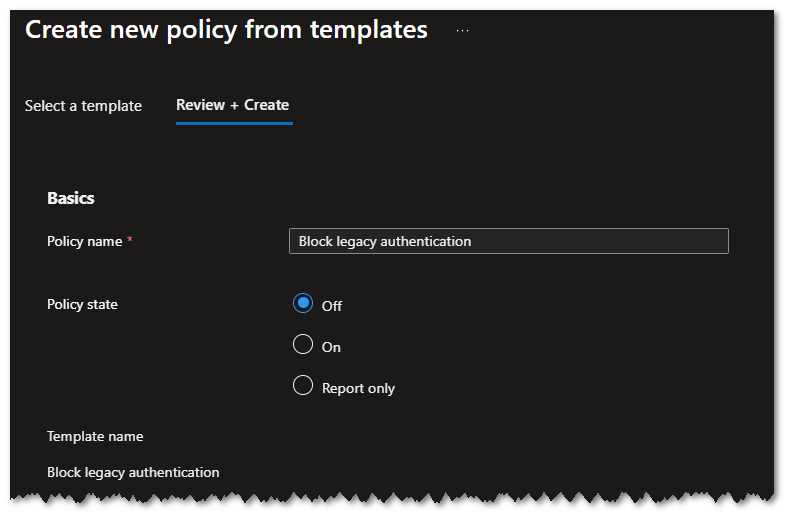
Saturday @MSIntune lab work. Setting up dedicated physical PAW device, admin account & dual admin approval. PAWS will be striped of everything and locked down. $30 @Yubico arrived overnight.


@ZackKorman The thing holding back most of the AI infosec startups is that they're often staffed and driven by people who were outside enterprise InfoSec and closer to start up/college culture (which is awesome), but those things don't carry over directly.





@AzureSupport You just got it fixed. 15 minute outage whole region no communication. Not the best look.