تغريدة مثبتة
Mickey Jin
296 posts


Mickey Jin
@patch1t
Exploring the world with my sword of debugger : )
انضم Ağustos 2013
251 يتبع5.3K المتابعون
Mickey Jin أُعيد تغريده

Today, Project Zero released a 0-click exploit chain for the Pixel 9. While it targets the Pixel, the 0-click bug and exploit techniques we used apply to most other Android devices.
projectzero.google/2026/01/pixel-…
English
Mickey Jin أُعيد تغريده

Holiday Project 👨🏻💻🎄
Interested in macOS malware? Have a read!
Objective-See Foundation@objective_see
🎉 A decade of Mac malware research 🎉 Just published our 10th annual “The Mac Malware of <year>” report ...2025 edition! For each new sample of 2025, covers: 🔎 IoCs 💉 Infection 💾 Persistence 📡 Capabilities ☣️ Samples for download Dive in 👇 objective-see.org/blog/blog_0x84…
English
Mickey Jin أُعيد تغريده

@patch1t For clarification, none of this was a collaboration. It's just the result of both of our independently (and almost coincidentally) researching the same targets.
English
Mickey Jin أُعيد تغريده

Introducing DirtyDict. A series of vulnerabilities found by me and @patch1t.
Most of this is my perspective, but Mickey did give me permission to share some details about one of his bugs.
Enjoy!
wts.dev/posts/dirtydic…
English
Mickey Jin أُعيد تغريده

🎉 My new blog post is about a PackageKit vulnerability I learned from @p1tsist1p 's blog posts.
🍎🐛macOS LPE via the .localized directory
I tried convincing Apple to universally fix it with no luck.
Go hunt for vulnerable pkg installers! There is a ton :-( Happy Friday!
theevilbit.github.io/posts/localize…
English
Mickey Jin أُعيد تغريده
A really thorough overview of the research: github.com/trailofbits/ex…
English
Mickey Jin أُعيد تغريده

The slidedeck to our talk, Crash One: A Starbucks Story - CVE-2025-24277, with @gergely_kalman from @hexacon_fr and @objective_see #OBTS is available from the link below.
It was a macOS vulnerability impacting the crash reporting process where we could achieve LPE and sandbox escape.
theevilbit.github.io/talks_workshop…
English
Mickey Jin أُعيد تغريده
Excited to share our research on ChillyHell, a modular macOS backdoor targeting officials in Ukraine. Check out our write-up for more details.
jamf.com/blog/chillyhel…
English

@logiruse The vulnerable API implementation also affects iOS, but it is more difficult to exploit because the mount trick doesn’t work on iOS.
English

For those missing the talk,
Blog: jhftss.github.io/Exploiting-the…
Slides: github.com/jhftss/jhftss.…
Mickey Jin@patch1t
Will share one of them at the Nullcon Berlin @nullcon
English

It's time to disclose this vulnerability. What happens if gcore has …apple.security.system-task-ports.read entitlement? That exactly is the root cause of CVE-2025-24204.
tsunekoh@tsunek0h
My submission for #NullconBerlin2025 has been accepted! I will talk about the details of CVE-2025-24204, which breaks process isolation on macOS.
English
Mickey Jin أُعيد تغريده

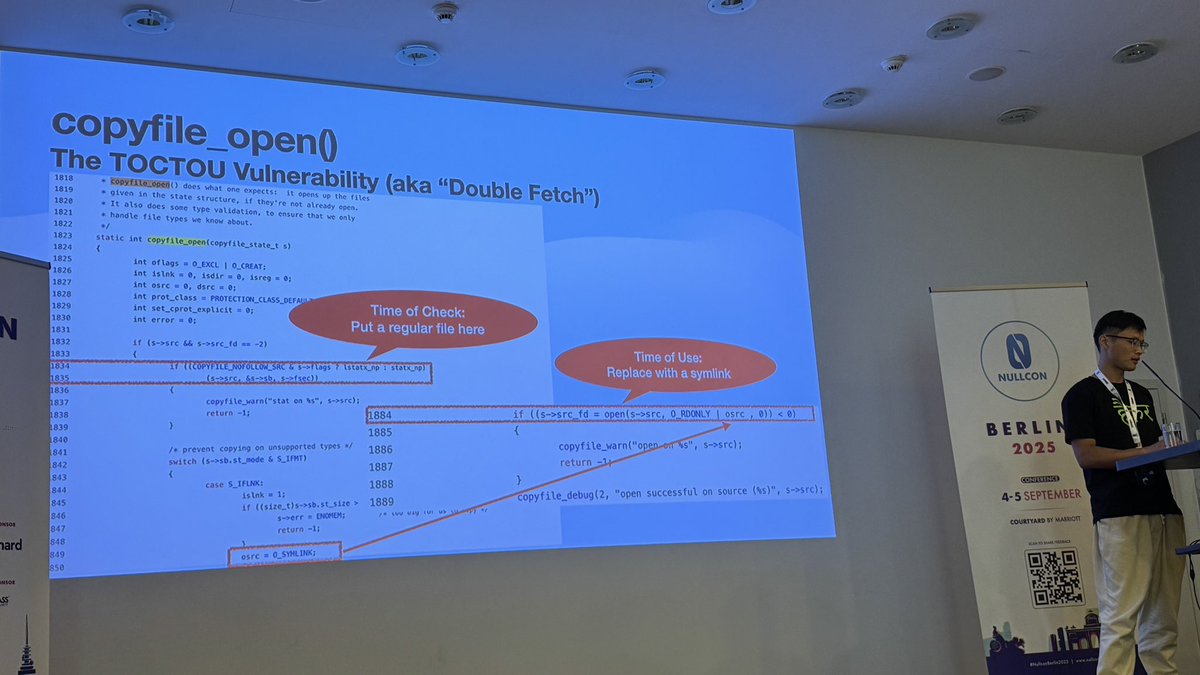
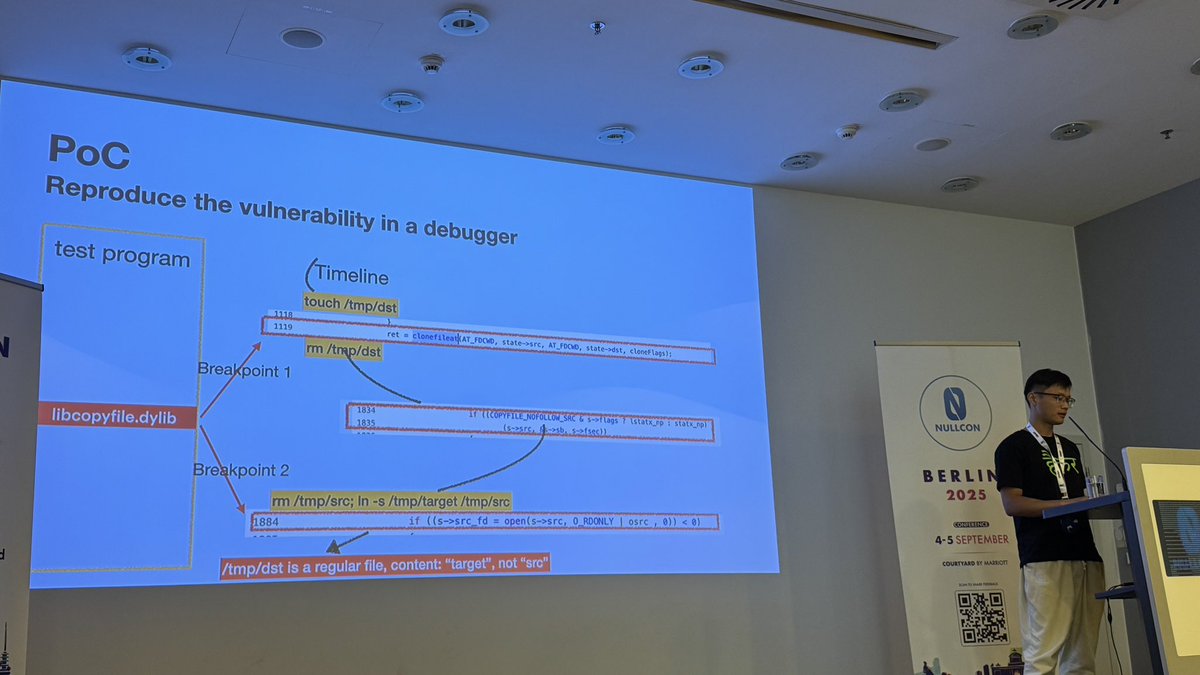
A tiny timing flaw in Apple’s core file-copy APIs can put millions of devices at risk 📂🍏
Despite warnings, Apple thought it was “too hard to exploit”—until Mickey Jin developed an exploit that steals secrets in privileged services
👉nullcon.net/berlin-2025/sp…
#NullconBerlin2025

English
Mickey Jin أُعيد تغريده

Thank you @helpnetsecurity to mention us 👍 awesome research by @tsunek0h
#macOS #applesecurity #NullconBerlin2025
helpnetsecurity.com/2025/09/04/mac…
English

@nullcon Apple: I’ve already warned you copyfile API has a vulnerability, can you catch it?
English

Super cool research by @patch1t . Exploiting the impossible , #Apple Deems Unexploitable … #NullconBerlin2025


English
Mickey Jin أُعيد تغريده
🚨 New blog post: ELEGANTBOUNCER - Catch iOS 0-click exploits without having the samples.
Features iOS backup forensics & messaging app scanning for iMessage, WhatsApp, Signal, Telegram & Viber attachments.
🔗 Link -> msuiche.com/posts/elegantb…
English
Mickey Jin أُعيد تغريده

🍏 #AppleDevelopers use NSFileManager thinking it’s safe — but @patch1t found a race condition once thought “impossible to exploit.”
At #NullconBerlin2025, he’ll show how it works, why CVE-2024-54566 failed, and Apple’s final fix.
👉 nullcon.net/berlin-2025/sp…
#iOS #applesecurity

English





