Watch This Space
1.6K posts

Watch This Space
@wtsdev
Watch This Space: A security research blog.


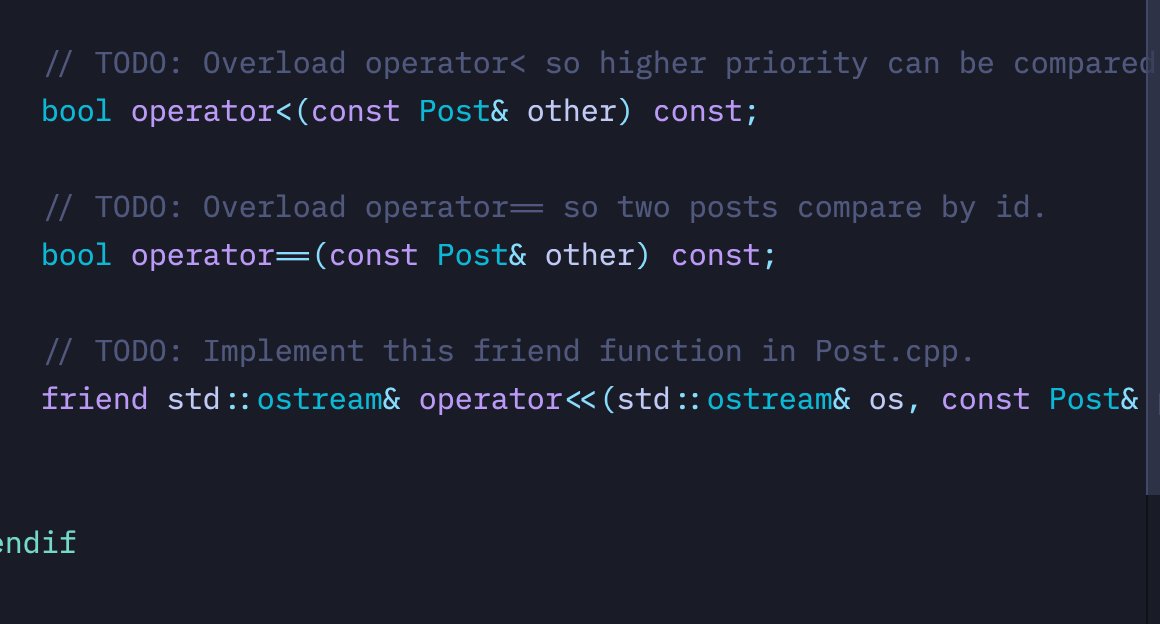
Claude helped me with this bug too but in a different way... Tried to gaslight me saying it wasn’t ~exploitable in practice~ and I got obsessed with proving it wrong 😩



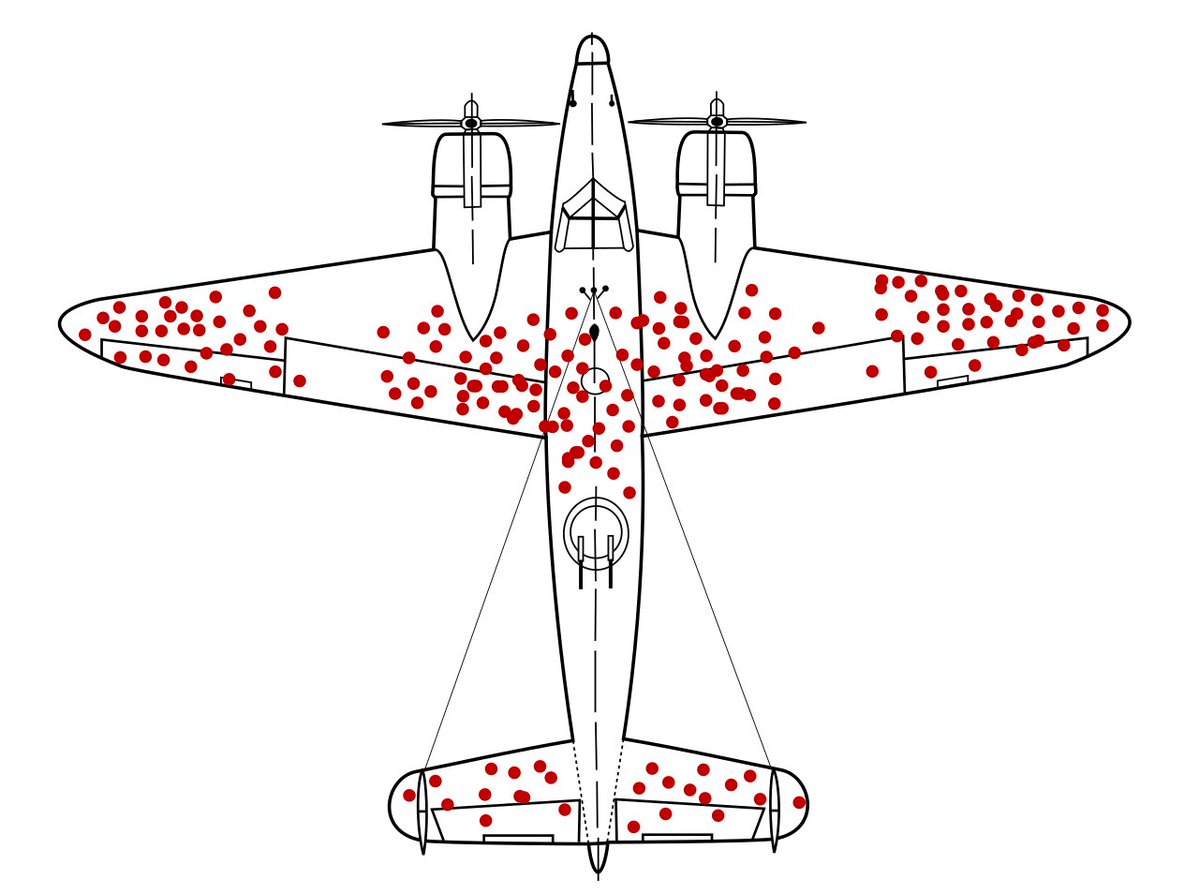
Early this week, we had a meeting at Apple Park in Cupertino. While there, we also shared with Apple our latest vulnerability research report: the first public macOS kernel memory corruption exploit on M5 silicon, surviving MIE. It was laser printed, in honor of our hacker friends. Full story: open.substack.com/pub/calif/p/fi…




apple just updated their human interface guidelines and double downed on the top left close button for an iphone 17 pro max crazy stuff. the folks that decide these things must be giants









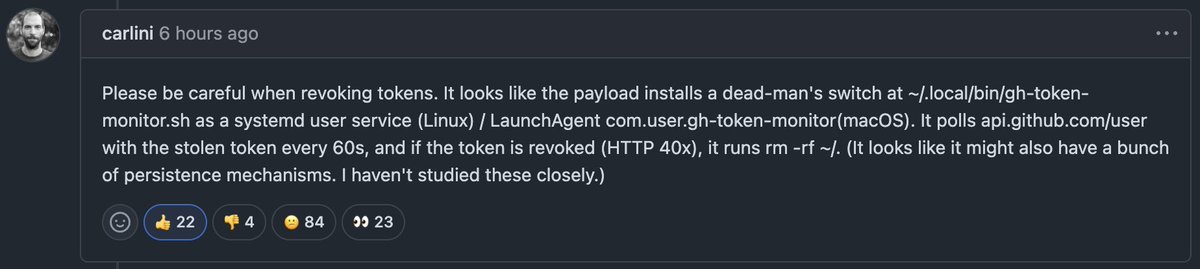
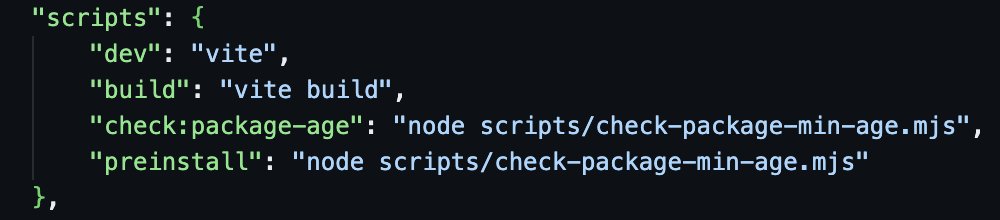
SECURITY ADVISORY — TanStack npm packages A supply-chain compromise affecting 42 @tanstack/* packages (84 versions total) was published to npm earlier today at approximately 19:20 and 19:26 UTC. Two malicious versions per package. Status: ACTIVE — packages are deprecated, npm security engaged, publish path being shut down. Severity: HIGH — payload exfiltrates AWS, GCP, Kubernetes, and Vault credentials, GitHub tokens, .npmrc contents, and SSH keys. If you installed any @tanstack/* package between 19:20 and 19:30 UTC today, treat the host as potentially compromised: • Rotate cloud, GitHub, and SSH credentials immediately • Audit cloud audit logs for the last several hours • Pin to a prior known-good version and reinstall from a clean lockfile Detection — the malicious manifest contains: "optionalDependencies": { "@tanstack/setup": "github:tanstack/router#79ac49ee..." } Any version with this entry is compromised. The payload is delivered via a git-resolved optionalDependency whose prepare script runs router_init.js (~2.3 MB, smuggled into each tarball at the package root). Unpublish is blocked by npm policy for most affected packages due to existing third-party dependents. All 84 versions are being deprecated with a SECURITY warning, and npm security has been engaged to pull tarballs at the registry level. Full technical breakdown, complete package and version list, and rolling status updates: github.com/TanStack/route… Credit to the security researcher for responsible disclosure.

npm config set min-release-age=2d



🚨 How the TanStack npm attack actually happened: 1. Attacker opened a normal-looking pull request (#7378) on the TanStack repo. 2. GitHub automatically ran CI tests on that PR. 3. Code inside the PR stole the workflow's GitHub Actions Cache write token during the test run. 4. The attacker used that token to plant poisoned files in the shared build cache. The PR could be closed afterwards. The poisoned cache stays. 5. The official release workflow later pulled from the cache, baked the malicious files into the build, and signed and published 84 malicious package versions to npm.



nah im just not gonna run npm install anymore