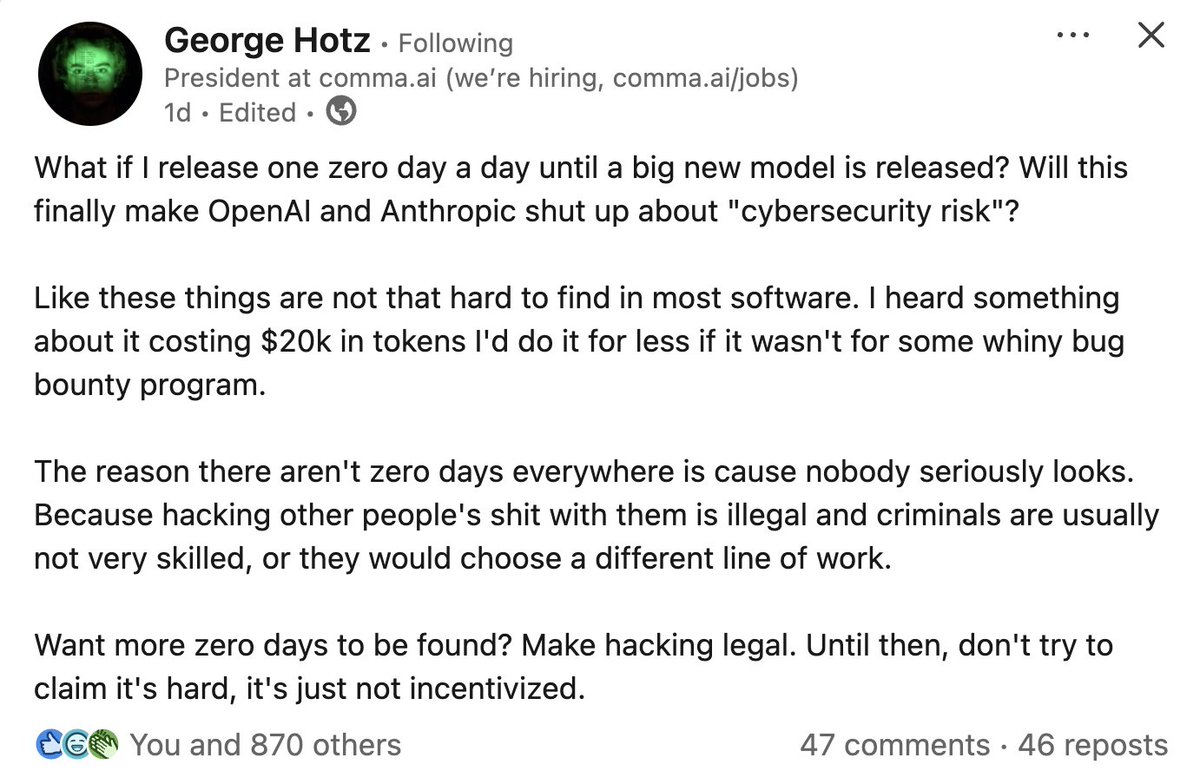
thirk 🐦⬛
4.4K posts

thirk 🐦⬛
@thirk
shitposting, programming, hacking, arguing. building privacy infra w/zk. tee skeptic. decentralization maxi. descriptive, not prescriptive. fuck vcs, fund pgs.
انضم Eylül 2021
698 يتبع285 المتابعون

@jtriley2p No version of this could work even in theory, right? At best we get TEE-like guarantees on locked hardware?
English

app's closed sauce + ios only :(
sdk's oss + has hole :3
steps:
---
1. img captured
2. img written to disk
3. c2pa manifest gen'd
4. img + c2pa signed
5. (optional) send to succinct's prover net
hole:
---
there's a gap between capturing the img & signing, an impl'r can ai-gen an img, forge c2pa manifest, sign it, & gen an sp1 proof about it
other stuff to know:
---
apple attests to signer's p256 pub key from secure enclave
sp1 proof exposes only img hash, app id, & apple root cert; BUT succinct prover sees device id, sig bytes, raw img bytes, & metadata (sus)
Succinct@SuccinctLabs
Today, we're launching ZCAM, an iPhone camera app to Prove What’s Real. ZCAM cryptographically signs photos and videos at the moment of capture. Anyone can independently verify the content came from a real device and hasn't been altered or AI-generated.
English

@pcaversaccio The people who have the power to change things are obviously not interested if it affects their bottom line.
English
thirk 🐦⬛ أُعيد تغريده

the negative and positive things that have happened since saturday are the result of _centralised_ points of building. everything that has happened (the bad and good things) would not have happened if we built in a truly decentralised way. overall, dprk would have far fewer "gains" if we stuck to cypherpunk principles. like, dprk does _not_ focus on smart contract hacks, they almost exclusively target centralised attack vectors. if we want to win against dprk (and any other state actor, which all focus on web2-based attack vectors), we need to go full cypherpunk mode. if this is not a wake up call, i do not think we will get a second chance.
English

@cialoneCodes @christroutner @rstormsf @UmbraCash @THORChain No reason to drop public crumbs regardless.
English

💯— and thinking a DM on x is private and wouldn’t be used by ‘the Feds’ if they felt like utilizing it is an absurdity
As an ecosystem, community of networks and likeminded developers and individuals, we need to come together at this critical point in time and move as one
We can compete after
English
As has been reported, Umbra was used to move funds associated with recent, high profile hacks. In total, we are aware of 349 ETH (~$800K) of stolen funds moving through the protocol. Reports of much higher amounts are inaccurate. A few notes:
First, as a stealth address system, Umbra is primarily useful for protecting the identity of the receiver, not the sender. Since hackers want to erase the association of funds with the hack-tainted sending address, it is not particularly helpful to hackers to move the funds through Umbra. All the stolen funds moved through the protocol can be identified, and we have been in touch with security researchers who are involved.
Second, Umbra is a permissionless protocol powered by autonomous smart contracts. There is nothing we can do to stop anyone from using these contracts, nor is there anything we can do to stop anyone from using a local or self hosted version of the Umbra frontend, which is fully open source.
We did, however, make the decision to move our hosted version of the frontend into maintenance mode. We did so this morning at 6:45 AM ET.
Please note that all funds in stealth addresses are completely safe and were never at risk. The Umbra protocol continues to operate normally, we've simply turned off our instance of the frontend.
We will restore access to the hosted frontend as soon as we are assured that doing so won't create obstacles to the current recovery efforts.
Updates will be posted here.
English

@naruto11eth You are the enemy, and we will not let you co opt our movement any longer. Goodbye :)
English

@rstormsf @UmbraCash If you believe any of this to be a detriment to umbra, this probably should have been a DM instead of a public message feds can reference later...
English

Prosecutors in my case called me a liar when I said that I can’t control Tornado Cash. If you can make changes to the user interface, including further updates through new builds on IPFS, then you are in full control. Therefore, you can do something like what their expert witness described as a “User Registry.” SDNY really loves pretending that changing a front end is the same thing as controlling an entire protocol. I used to think we lived in a sane world.
English

@senamakel @tayvano_ @lex_node @KelpDAO @LayerZero_Core bro couldn't even read and is now reply-guying for a (YOU). shameless.
English

@lex_node @KelpDAO @LayerZero_Core docs.layerzero.network/v2/workers/off…
"DVNs are independent entities that validate the authenticity and integrity of messages sent across blockchains within the LayerZero ecosystem"
so looks more of a validator to me...
English

@senamakel @KelpDAO @LayerZero_Core "trust on LZ & Aave will deteriorate"
This is the best thing that could happen for the industry
English

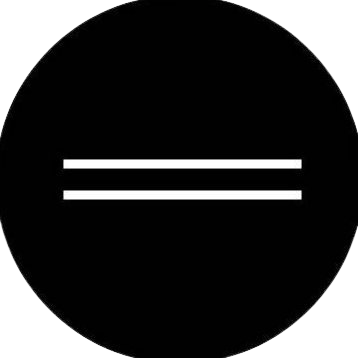
the issue with the @KelpDAO 280m$ hack was that it was just secured by just 1/1 validator set (DVN) on @LayerZero_Core . Which means one faulty transaction from a validator is all that's needed.
my belief is that the root cause was possibly that the LZ validator on Unichain was compromised.
the contagion effects are going to be quite bad. I don't think many people have realized it yet.
- kelp was looping on aave with stETH for a few percentage here and there. Aave is going through a bank run so that means they'll need to unwind their positions
- multiple protocols and chains are now going to be bad debt because their rsETH will get depegged.
- aave's bad debt is more than what they can cover rn so almost anyone who has deposited into their safety net (60mn$) is 100% rekt. all for just staking for a few % in extra yeild.
- trust on LZ & Aave will deteriorate. this is bad for the industry.
- the kelp team (amazing founders) will go through debt
i'd say i feel sorry for everyone who is going to go through the next few hours but unfortunately this is the industry we live in.

English
thirk 🐦⬛ أُعيد تغريده

i keep reading all of these messages/tweets etc. where people really think having "2 required DVNs" is better. what is wrong with all of you fucking morons? you fucking build trusted centralised clownshows and think adding an additional signer is the way to go, lmfaoooo, i enjoy watching the full retardedness of this space ngl. in fact, all what happens now is the result of our own fucking nonsense making. like i have zero fucking mercy.
English
thirk 🐦⬛ أُعيد تغريده

Would you let a computer hijack your muscle movements if it increased your performance 35%?
I totally would.
Came across a really interesting ACM paper today (SplitBody), where subjects were given difficult multitasking challenges.
Their mental load was “reduced” by having a computer electrically stimulate their arm instead. Bodily autonomy wise, it might feel a bit freaky, because you have the proprioception of your arm moving, but without the mental load of you moving it.
I think it’s actually less creepy than it sounds, and I wish more research was poured in this area.
Let me give an example. As a dancer myself, early on, aerials have a difficult initial mental barrier. The common way to learn is to essentially let your teacher control your muscle movements, repeating the overall motions, over and over again.
By sort of “proving” the movement is possible (giving up autonomy!) the concept suddenly clicks, and you’ll “just get it”.
I feel like there’s probably a lot of interesting biological barriers that could be overcome if you trained yourself to go past traditional limits by electrical stimulation first. Take a look at the Bannister effect!

English

@gabriberton However smart or not smart Mythos may be, the issue of having the manpower to do those kind of audits is what makes it so interesting.
English

@gabriberton I discovered this was true when I decided to "just look" into places I assumed were audited.
English
Bitcoin’s founder, Satoshi Nakamoto, has remained hidden for 17 years. A trail of clues — and a year of digging by our reporter, John Carreyrou — led us to a 55-year-old computer scientist in El Salvador named Adam Back. nyti.ms/4bXWC3V
English
thirk 🐦⬛ أُعيد تغريده

🚨 TODAY, THE FUTURE OF FREE SOFTWARE WILL BE DECIDED.
AT 10am THURGOOD MARSHALL COURTHOUSE, A JUDGE WILL DECIDE WHETHER ROMAN STORM'S CONVICTION WILL STAND.
If so, "the Government would criminalize the publication of decentralized software in violation of the first amendment."
Read all about Roman Storm's motion for acquittal at the link below.
Code is speech.
Privacy is not a crime.
FREE ROMAN STORM
therage.co/roman-storm-ac…

English
thirk 🐦⬛ أُعيد تغريده

@plantsci_guy @FFmpeg @AnthropicAI Yeah but only ffmpeg said we could search their patches for the exploits
English
@thirk @FFmpeg @AnthropicAI they identified major vulnerabilities in all common OS and bowsers, so might wanna unplug all ur devices for a while
English

Thank you to @AnthropicAI for sending FFmpeg patches
Anthropic@AnthropicAI
Introducing Project Glasswing: an urgent initiative to help secure the world’s most critical software. It’s powered by our newest frontier model, Claude Mythos Preview, which can find software vulnerabilities better than all but the most skilled humans. anthropic.com/glasswing
English